Tonight's tech landscape is dominated by security concerns and breakthrough innovations. From an AI model so powerful it can't be publicly released, to state-sponsored hackers targeting home routers, to revolutionary battery technology that defies physics - this Tekin Night covers the stories shaping our digital future. Grab your evening coffee and let's dive deep into today's most critical developments. 🌌☕
📋 Tonight's Stories
- Anthropic's Claude Mythos: The AI Too Dangerous to Release Publicly
- Russian APT28 Router Hijacking: Your Home Network Under Attack
- Meta's Muse Spark: First Model from Superintelligence Labs
- Quantum Battery Breakthrough: Charges Faster as It Gets Bigger
- Drift's $285M Hack: Inside the 6-Month North Korean Operation
- Q1 2026 Funding Record: $297 Billion Poured Into Startups
🤖 1. Anthropic's Claude Mythos: The AI Too Dangerous to Release Publicly
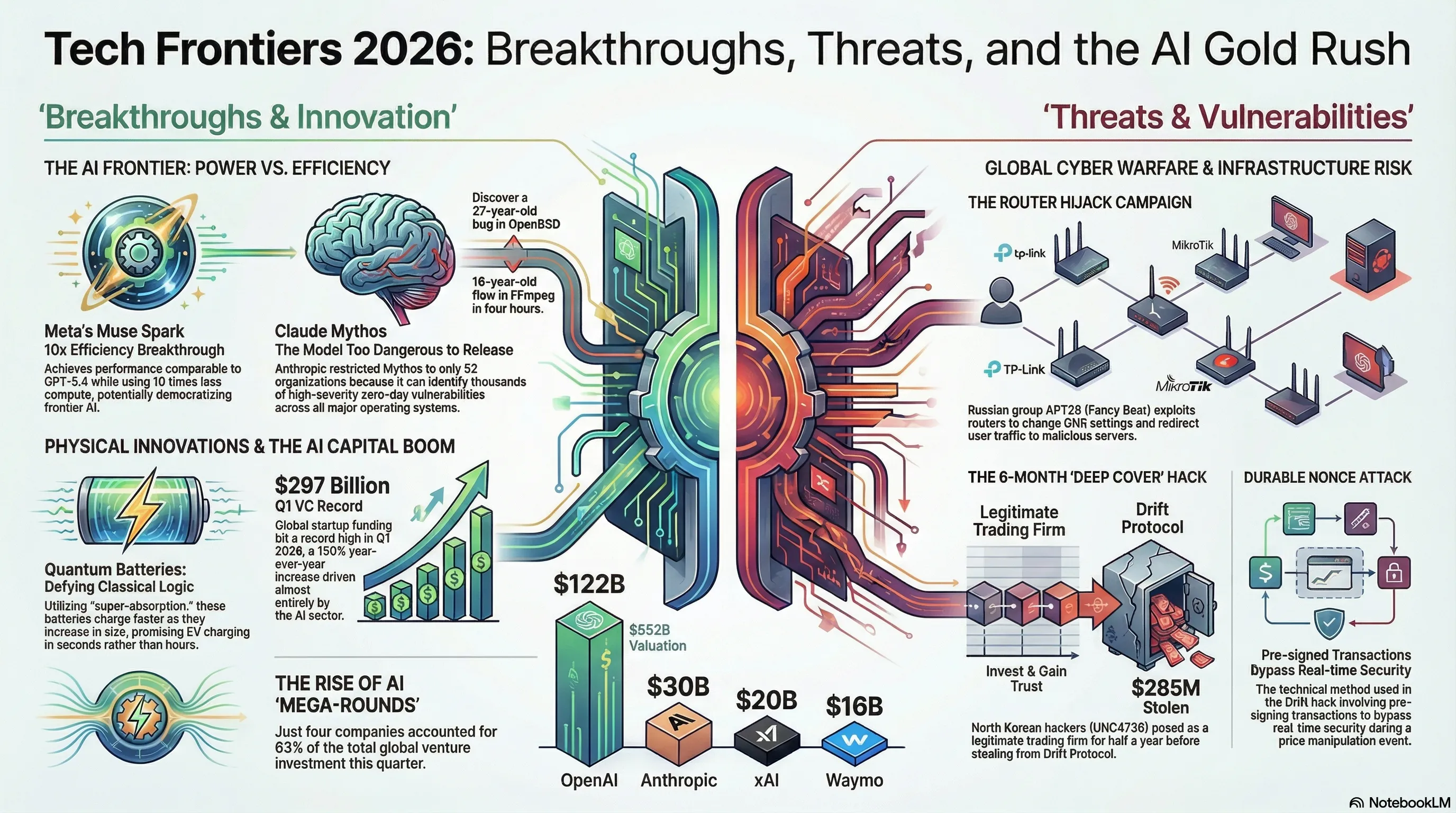
In one of the most significant AI security announcements of 2026, Anthropic today unveiled Claude Mythos Preview - a frontier AI model so powerful at discovering cybersecurity vulnerabilities that the company has decided to restrict access to just 52 carefully selected organizations worldwide. This marks the first time a major AI lab has withheld a model from public release specifically due to its offensive capabilities.
What makes Claude Mythos so special? According to Anthropic's announcement, this model has already identified thousands of high-severity zero-day vulnerabilities across every major operating system and web browser. Zero-day vulnerabilities are security flaws that are unknown to software vendors and have no patches available - making them extremely valuable to both defenders and attackers. The model discovered a 27-year-old bug in OpenBSD, a 16-year-old flaw in FFmpeg, and a memory-corrupting vulnerability in a memory-safe virtual machine monitor.
The decision to limit access comes through Project Glasswing, Anthropic's new partnership program that provides early access to select technology and infrastructure organizations for defensive security tasks only. The 52 organizations include tech giants like NVIDIA, Amazon, Apple, Google, and Microsoft, as well as critical infrastructure providers and government cybersecurity agencies. These partners can use Mythos to scan their systems for vulnerabilities before attackers find them.
Why is Anthropic so cautious? In a previously leaked internal memo, the company called Mythos "currently far ahead of any other AI model in cyber capabilities" and warned it "presages an upcoming wave of models that can exploit vulnerabilities in ways that far outpace the efforts of defenders." The concern is that if Mythos were publicly available, malicious actors could use it to discover and exploit vulnerabilities faster than defenders could patch them - creating a catastrophic security imbalance.
The model's capabilities extend beyond simple vulnerability scanning. Mythos can perform autonomous penetration testing, analyze complex code bases for subtle security flaws, and even suggest exploitation techniques. In one demonstration, it autonomously hacked a secure operating system in just four hours - a task that would typically take human security researchers days or weeks.
🔍 Tekin's Analysis:
This is a watershed moment in AI development. Anthropic's decision to restrict Mythos access acknowledges what many security experts have warned about: AI models are becoming powerful enough to fundamentally shift the balance between attackers and defenders. The fact that a single AI model can find thousands of zero-days across all major systems shows we're entering a new era of cybersecurity where AI-powered offense may temporarily outpace AI-powered defense. Expect other AI labs to face similar dilemmas as their models become more capable. The question isn't whether to restrict powerful AI - it's how to do so while still advancing beneficial applications.
🔴 2. Russian APT28 Router Hijacking: Your Home Network Under Attack
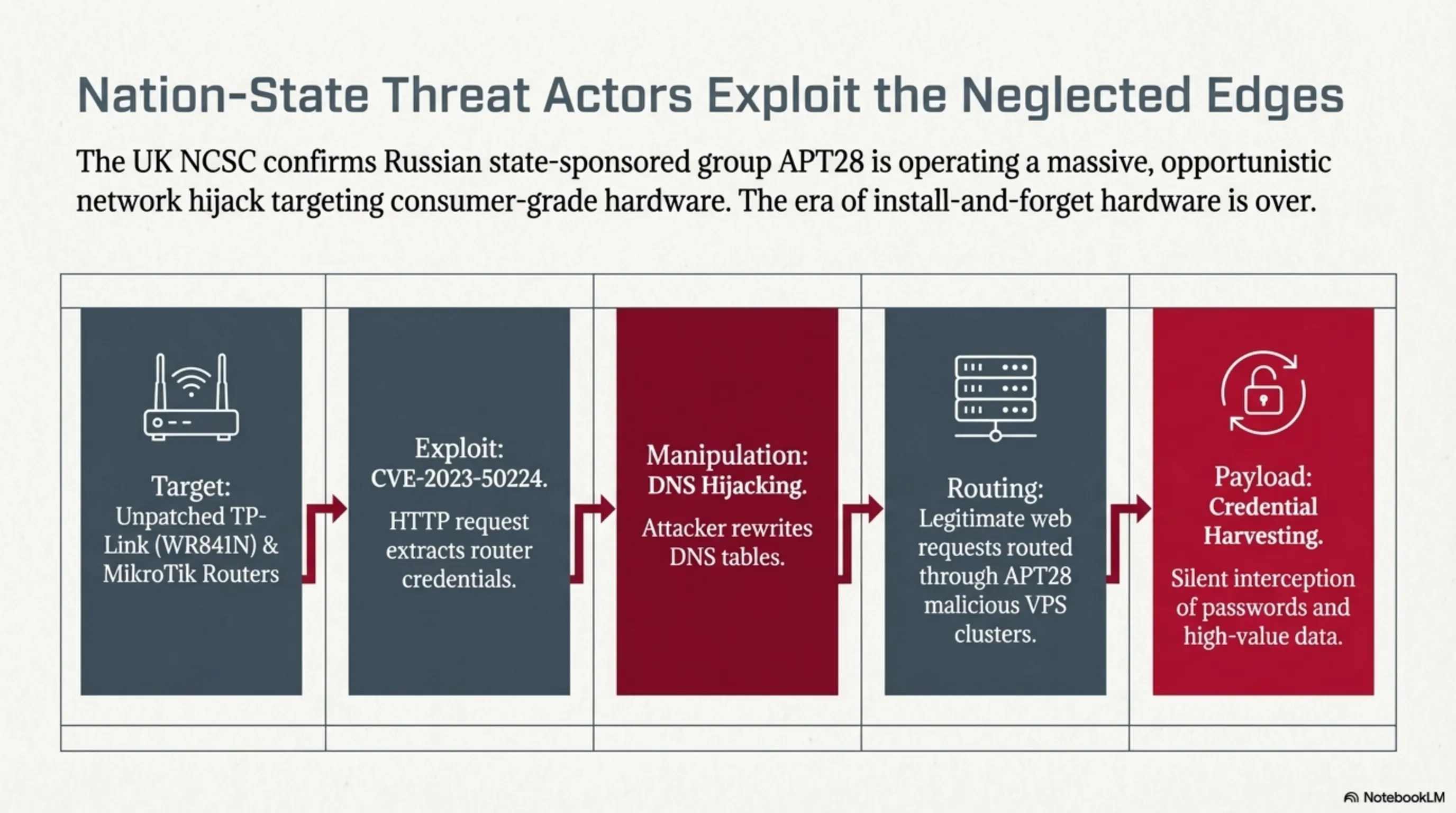
The UK's National Cyber Security Centre (NCSC) issued an urgent warning today: Russian state-sponsored hackers from the APT28 group (also known as Fancy Bear) are conducting a widespread campaign to hijack home and small office routers, redirecting internet traffic through attacker-controlled servers to steal credentials and sensitive information. This isn't a theoretical threat - it's happening right now, and your router might already be compromised.
How does the attack work? APT28 hackers are exploiting known vulnerabilities in popular router models, particularly TP-Link and MikroTik devices. The NCSC specifically identified the TP-Link WR841N as a heavily targeted model, with attackers leveraging CVE-2023-50224 - a flaw that allows unauthenticated attackers to extract router credentials via a crafted HTTP request. Once inside, hackers modify the router's DNS (Domain Name System) settings to redirect all internet traffic through servers they control.
What makes this attack particularly insidious is its invisibility. When you type a website address like "gmail.com" into your browser, your router's DNS settings determine which server translates that name into an IP address. By controlling the DNS server, attackers can redirect you to fake websites that look identical to the real ones - capturing your passwords, emails, and other sensitive data without you ever knowing. The NCSC describes this as "opportunistic in nature," meaning attackers cast a wide net and then filter for high-value targets.
The campaign has been active since at least 2024, with investigators identifying two distinct clusters of malicious activity, each involving multiple Virtual Private Servers (VPSs) configured to operate as malicious DNS infrastructure. These servers have received large volumes of requests from compromised routers worldwide, suggesting the scale of the operation is massive. Over 20 TP-Link models and numerous MikroTik routers appear on the compromised devices list.
Who's at risk? The NCSC warns that while the attacks are "believed to be opportunistic," they're likely targeting individuals and organizations of potential intelligence value. This includes government employees, defense contractors, journalists, activists, and anyone working in sensitive industries. However, the broad nature of the campaign means even ordinary users could be caught in the dragnet and have their credentials stolen for later use or sale on dark web markets.
⚠️ Tekin's Warning:
This attack highlights a critical weak point in home cybersecurity: routers are often the most neglected devices on your network. Most people never change default passwords, never update firmware, and never check DNS settings. APT28 knows this and is exploiting it at scale. If you own a TP-Link or MikroTik router, check for firmware updates immediately, change default credentials, and verify your DNS settings haven't been tampered with. Better yet, consider replacing older models with newer devices that receive regular security updates. The era of "set it and forget it" routers is over - your home network is now a frontline in state-sponsored cyber warfare.
🧠 3. Meta's Muse Spark: First Model from Superintelligence Labs
Meta today unveiled Muse Spark, the debut model from its newly formed Meta Superintelligence Labs - and it's making waves for both its capabilities and its efficiency. This is the first major AI release since Meta acquired Scale AI for $14.3 billion in June 2025, bringing CEO Alexandr Wang on board to lead the company's AI efforts. Muse Spark represents a fundamental rethinking of how Meta approaches AI development.
The headline feature? Muse Spark achieves performance comparable to competitors' top models while running on 10 times less compute. In independent testing by Artificial Analysis, the model scored 52 points on the Intelligence Index, landing in the top 5 alongside Gemini 3.1 Pro, GPT-5.4, and Claude Opus 4.6. This efficiency breakthrough could dramatically reduce the cost of running AI services and make advanced AI more accessible.
What can Muse Spark do? It's a native multimodal reasoning model with tool use capabilities, visual chain-of-thought reasoning, and multi-agent orchestration. In practical terms, this means it can analyze images, use external tools like calculators or search engines, show its reasoning process visually, and coordinate multiple AI agents to complete complex tasks. Meta describes it as a step toward "personal superintelligence" that understands your world and can act on your behalf.
The model is currently powering the Meta AI app and website, with rollouts to WhatsApp, Instagram, Facebook, Messenger, and Ray-Ban Meta smart glasses coming in the next few weeks. Meta is also offering private preview API access to select partners. Notably, Muse Spark will integrate with content from Meta's platforms - similar to how xAI's Grok uses X (Twitter) data - allowing it to reference public posts, trending topics, and location-based information.
What's different about Meta's approach? According to the company, Meta Superintelligence Labs "rebuilt our AI stack from the ground up" over the past nine months, moving faster than any previous development cycle. The focus was on creating a model that's "small and fast by design, yet capable enough to reason through complex questions in science, math, and health." This contrasts with the industry trend of building ever-larger models that require massive computational resources.
💡 Tekin's Take:
Muse Spark's 10x efficiency advantage could be a game-changer for the AI industry. If Meta can deliver frontier-model performance at a fraction of the computational cost, it fundamentally changes the economics of AI deployment. This could pressure OpenAI, Google, and Anthropic to focus more on efficiency rather than just raw capability. The $14.3 billion Scale AI acquisition is already paying dividends - Alexandr Wang's expertise in data quality and model training is clearly visible in Muse Spark's design. Watch for Meta to release an open-source version, which could democratize access to efficient frontier AI and accelerate innovation across the industry.
⚡ 4. Quantum Battery Breakthrough: Charges Faster as It Gets Bigger
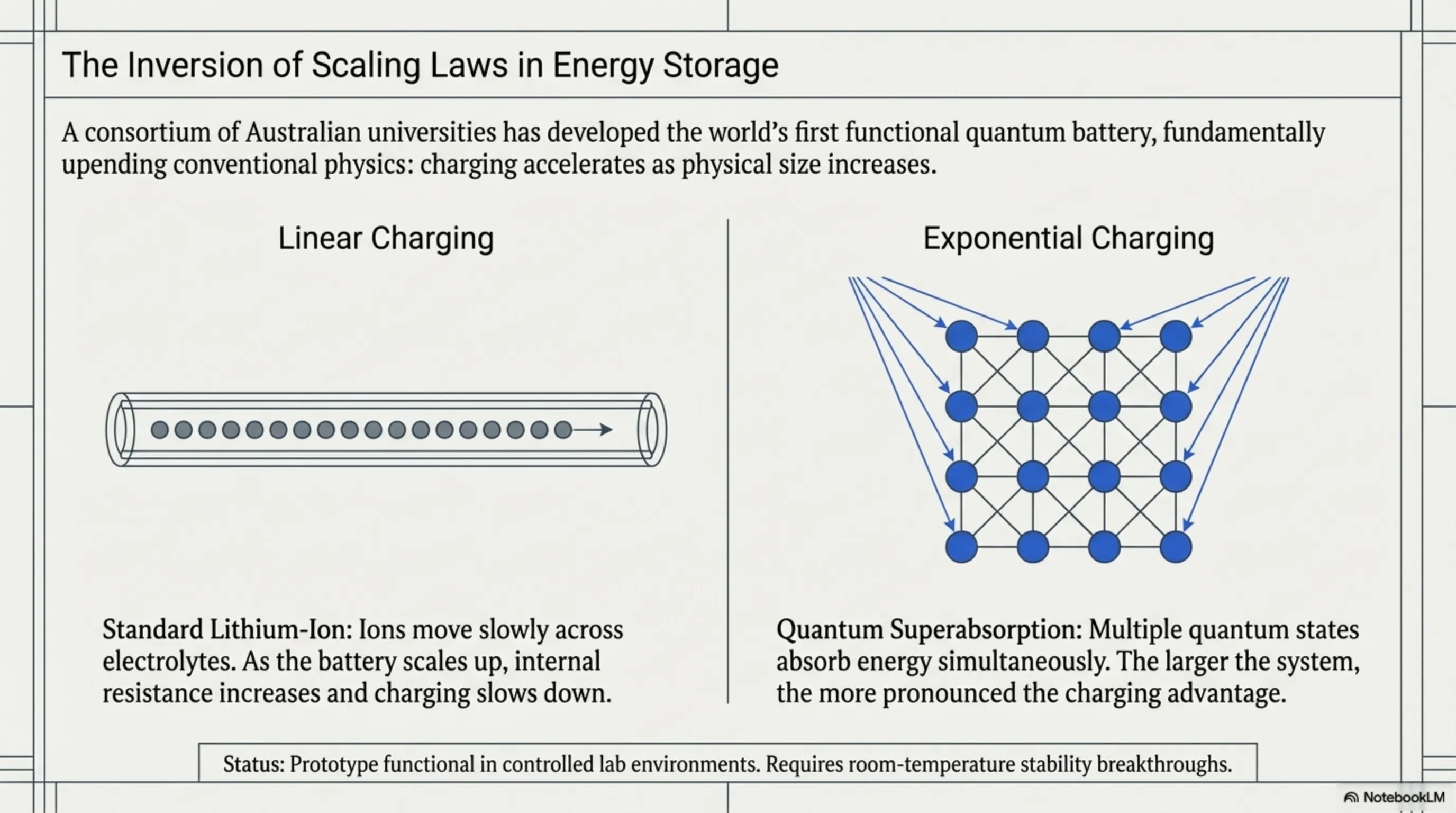
Australian scientists from CSIRO, RMIT University, and the University of Melbourne have achieved what many thought impossible: they've built the world's first working quantum battery prototype. But here's the mind-bending part - unlike conventional batteries that charge slower as they get bigger, quantum batteries charge faster as they scale up. This defies our everyday understanding of energy storage and could revolutionize everything from smartphones to electric vehicles.
What is a quantum battery? While the concept has existed in theoretical physics since 2013, this is the first time researchers have demonstrated a complete charge-store-discharge cycle in a single device. The prototype uses multi-layered organic microcavity structures charged via laser systems - a radical departure from lithium-ion technology, which relies on ion movement between electrodes through electrolyte solutions.
The key innovation is something called "super absorption" - a quantum effect where multiple quantum states can absorb energy simultaneously. Imagine if you could charge your phone by having every atom in the battery absorb energy at the same time, rather than waiting for ions to slowly move from one side to the other. That's essentially what's happening here, and the effect becomes more pronounced as the battery gets larger.
How much faster are we talking? The researchers demonstrated that charging time decreases as the number of quantum cells increases - a phenomenon they call "quantum advantage in charging." While the current prototype is small and charges wirelessly with a laser, the principles could scale to much larger batteries. Theoretical calculations suggest that a quantum battery the size of a car battery could charge in seconds rather than hours.
What are the challenges? The current prototype operates under carefully controlled laboratory conditions and requires laser charging, which isn't practical for everyday use. The quantum effects that enable super absorption are fragile and can be disrupted by heat, vibration, and electromagnetic interference. Researchers need to develop room-temperature quantum batteries that can be charged with conventional electrical connections before this technology becomes commercially viable.
🔬 Tekin's Analysis:
This quantum battery breakthrough is one of those rare moments when laboratory physics crosses into practical technology. The fact that charging speed increases with size could solve one of the biggest obstacles to electric vehicle adoption - charging time. Imagine pulling into a charging station and fully charging your EV in 30 seconds instead of 30 minutes. That's the promise of quantum batteries. However, we're still years away from commercial products. The path from lab prototype to consumer device is long and filled with engineering challenges. But the fundamental physics has been proven, and that's the hardest part. Expect major investment in quantum battery research over the next decade.
💸 5. Drift's $285M Hack: Inside the 6-Month North Korean Operation
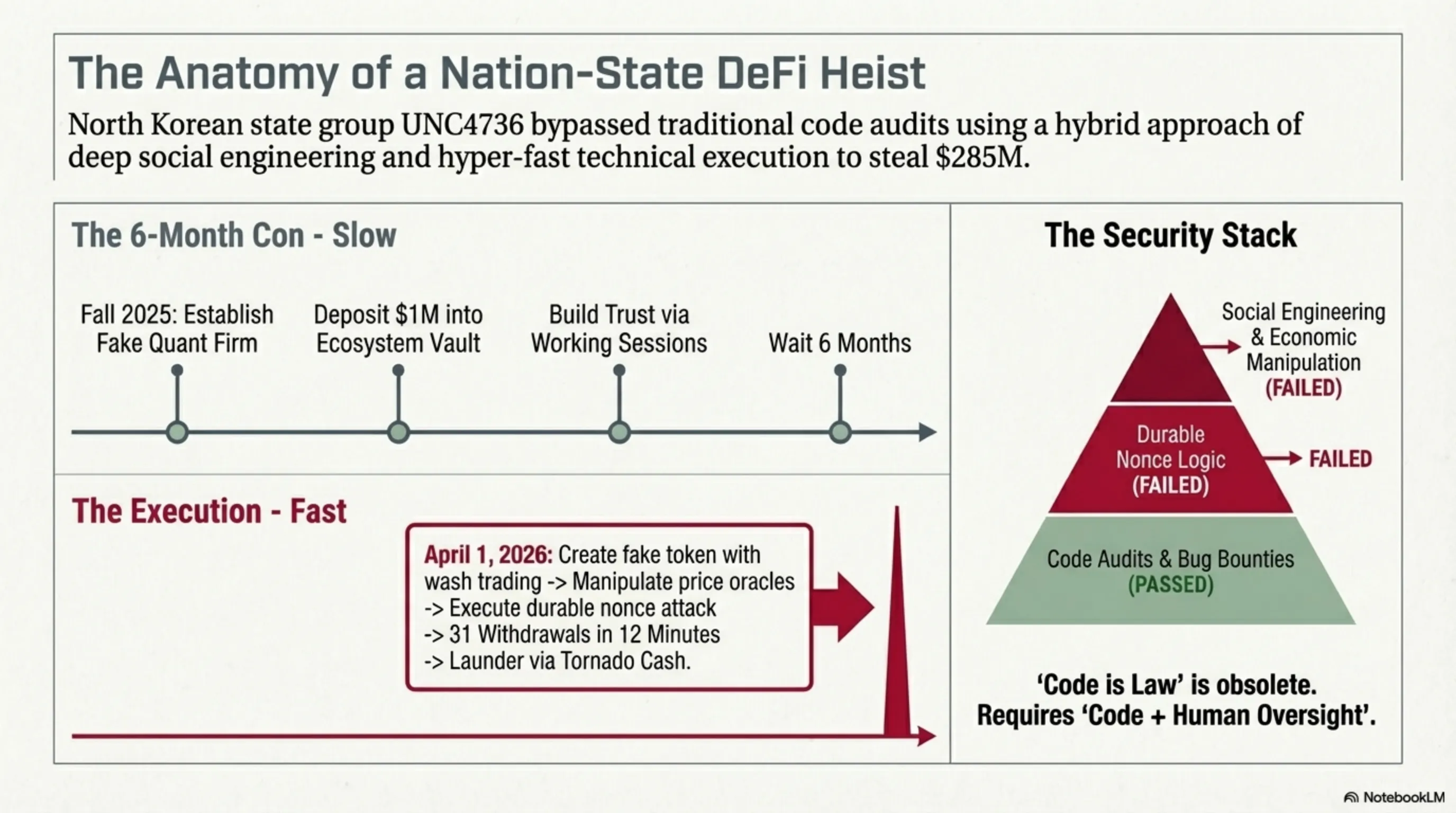
Drift Protocol today released a detailed post-mortem of the April 1st attack that resulted in $285 million in stolen cryptocurrency - and the details are chilling. This wasn't a quick smash-and-grab hack. It was a meticulously planned, six-month intelligence operation that began in fall 2025, involving fake identities, real capital investment, and months of trust-building before the attackers struck.
How did it unfold? According to Drift's investigation, the attackers - identified as North Korean hacking group UNC4736 (also known as AppleJeus, Citrine Sleet, and Gleaming Pisces) - posed as a legitimate quantitative trading firm. They deposited more than $1 million of their own capital into Drift's Ecosystem Vault, held working sessions with contributors across multiple countries, and waited nearly half a year before executing their attack. This level of patience and operational security is characteristic of state-sponsored actors with unlimited resources and time.
The technical attack was sophisticated. Rather than exploiting a traditional software vulnerability, the hackers used a "durable nonce attack" - a method that involves pre-signing transactions with special account settings that allow them to be executed later. They manufactured an entirely fictitious token with a small amount of seeded liquidity and wash trading, manipulated Drift's price oracles into treating it as legitimate collateral, and then used their pre-signed transactions to drain the protocol's vaults across 31 withdrawals in approximately 12 minutes.
What happened to the money? The attackers immediately moved the stolen funds through Tornado Cash, a cryptocurrency mixing service that obscures transaction trails by pooling funds from multiple sources. This is a standard money laundering technique used by North Korean hackers, who have stolen billions of dollars from cryptocurrency exchanges and DeFi protocols over the past several years. The funds are typically used to finance North Korea's missile and nuclear programs, as the regime faces international sanctions that limit traditional funding sources.
Why did Drift's security fail? The protocol had standard security measures in place, including code audits and monitoring systems. However, the attack exploited a combination of social engineering (building trust over months), economic manipulation (creating fake collateral), and technical sophistication (durable nonce transactions) that no single security measure could prevent. This highlights a fundamental challenge in DeFi: protocols must be open and permissionless to function, but this openness creates attack surfaces that determined adversaries can exploit.
⚠️ Tekin's Warning:
This attack should terrify anyone involved in DeFi. The fact that state-sponsored hackers are willing to invest $1 million and wait six months to steal $285 million shows the level of sophistication and patience we're dealing with. Traditional security measures - code audits, bug bounties, monitoring systems - are necessary but not sufficient against adversaries with this level of resources and determination. DeFi protocols need to implement multi-layered security that includes social verification of major participants, time-locked withdrawals for large amounts, and circuit breakers that can halt suspicious activity. The era of "code is law" is over - we need "code plus human oversight" to survive in a world where nation-states are actively attacking DeFi infrastructure.
💰 6. Q1 2026 Funding Record: $297 Billion Poured Into Startups
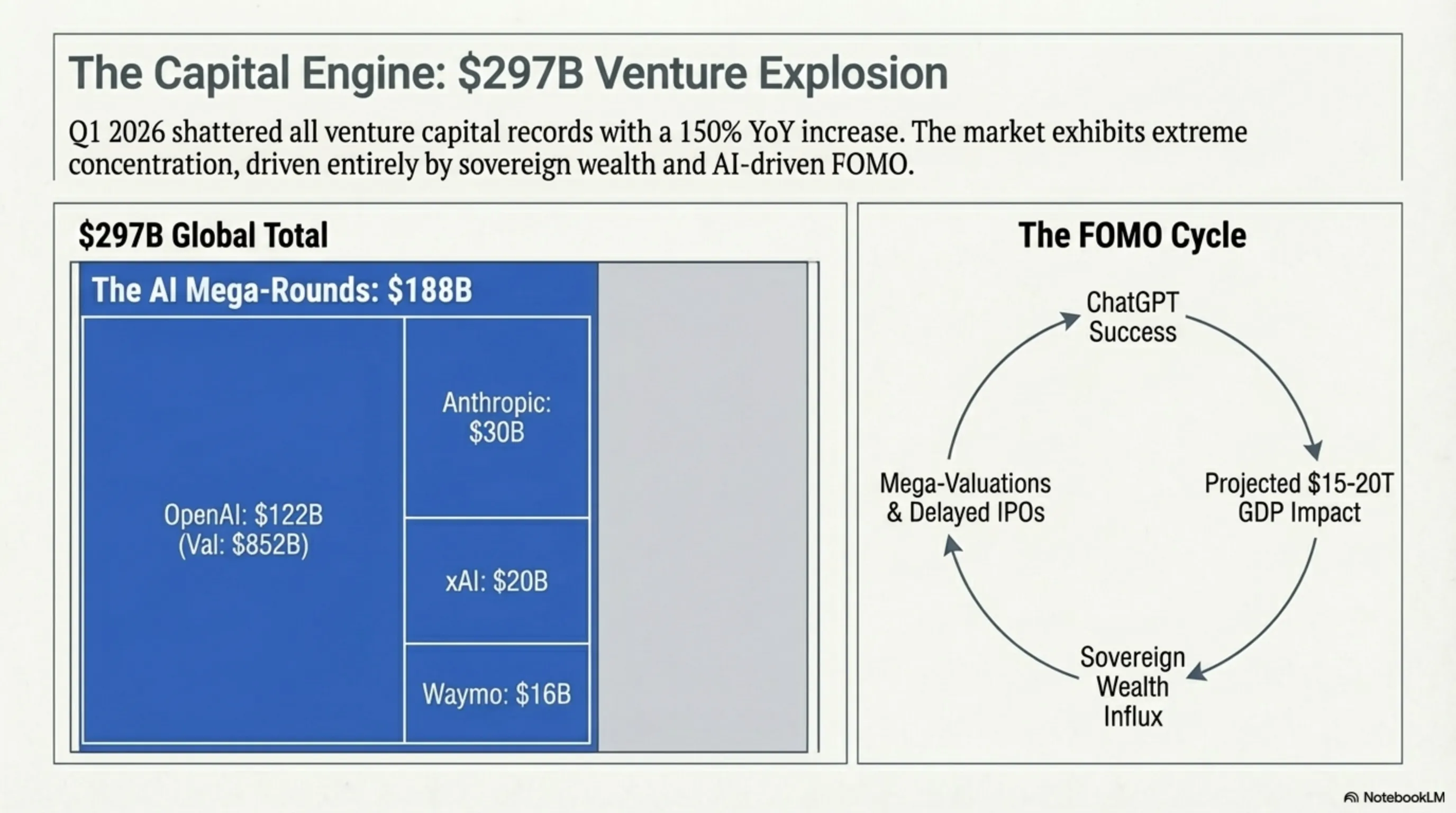
Crunchbase released its Q1 2026 venture capital report today, and the numbers are staggering: global startup funding hit $297 billion in the first quarter, shattering all previous records and representing a 150% increase both quarter-over-quarter and year-over-year. This isn't just a recovery from the 2023-2024 funding winter - it's a complete transformation of the venture capital landscape, driven almost entirely by massive investments in artificial intelligence companies.
Where did the money go? The top four deals alone accounted for $188 billion - more than 63% of total funding. OpenAI led with its record-breaking $122 billion round at an $852 billion valuation. Anthropic raised $30 billion, xAI (Elon Musk's AI company) secured $20 billion, and Waymo (Google's self-driving car unit) brought in $16 billion. These mega-rounds are unprecedented in venture capital history and reflect investor belief that AI will be the defining technology of the next decade.
What sectors are attracting capital? Beyond the headline AI deals, investors are concentrating on AI infrastructure (semiconductors, data centers, cloud services), robotics and automation, biotechnology platforms with AI integration, and fintech tools that leverage AI for productivity. Traditional consumer apps and e-commerce startups - once the darlings of venture capital - are struggling to raise funding unless they have a compelling AI angle.
Why the sudden surge? Several factors are converging. First, the success of ChatGPT and other AI applications has proven there's massive consumer and enterprise demand for AI products. Second, the potential market size is enormous - analysts estimate AI could add $15-20 trillion to global GDP by 2030. Third, there's a fear of missing out (FOMO) among investors who don't want to be left behind in what many see as a once-in-a-generation technology shift. Finally, sovereign wealth funds and pension funds are allocating unprecedented amounts to venture capital, providing massive pools of capital seeking deployment.
What does this mean for the IPO market? Interestingly, while private funding has exploded, the IPO market remains selective. Companies like SpaceX, OpenAI, and Anthropic could reopen the IPO window with successful public offerings, or they could drain private market capital by staying private longer. The massive valuations being achieved in private markets reduce the urgency to go public, as companies can raise billions without the regulatory burden and public scrutiny of being a public company.
📊 Tekin's Analysis:
This funding surge is both exciting and concerning. On one hand, massive capital investment will accelerate AI development and could lead to breakthrough applications that benefit humanity. On the other hand, we're seeing classic bubble behavior - huge valuations based on future potential rather than current revenue, fear of missing out driving investment decisions, and capital concentrating in a handful of companies. History suggests that when everyone is rushing into the same sector, corrections are inevitable. Not all of these AI companies will succeed, and some will fail spectacularly. However, the winners could become the most valuable companies in history. For entrepreneurs, this is the best funding environment in years. For investors, it's time to be selective and focus on companies with real technology moats, not just AI buzzwords.
🌙 Tekin Night Conclusion
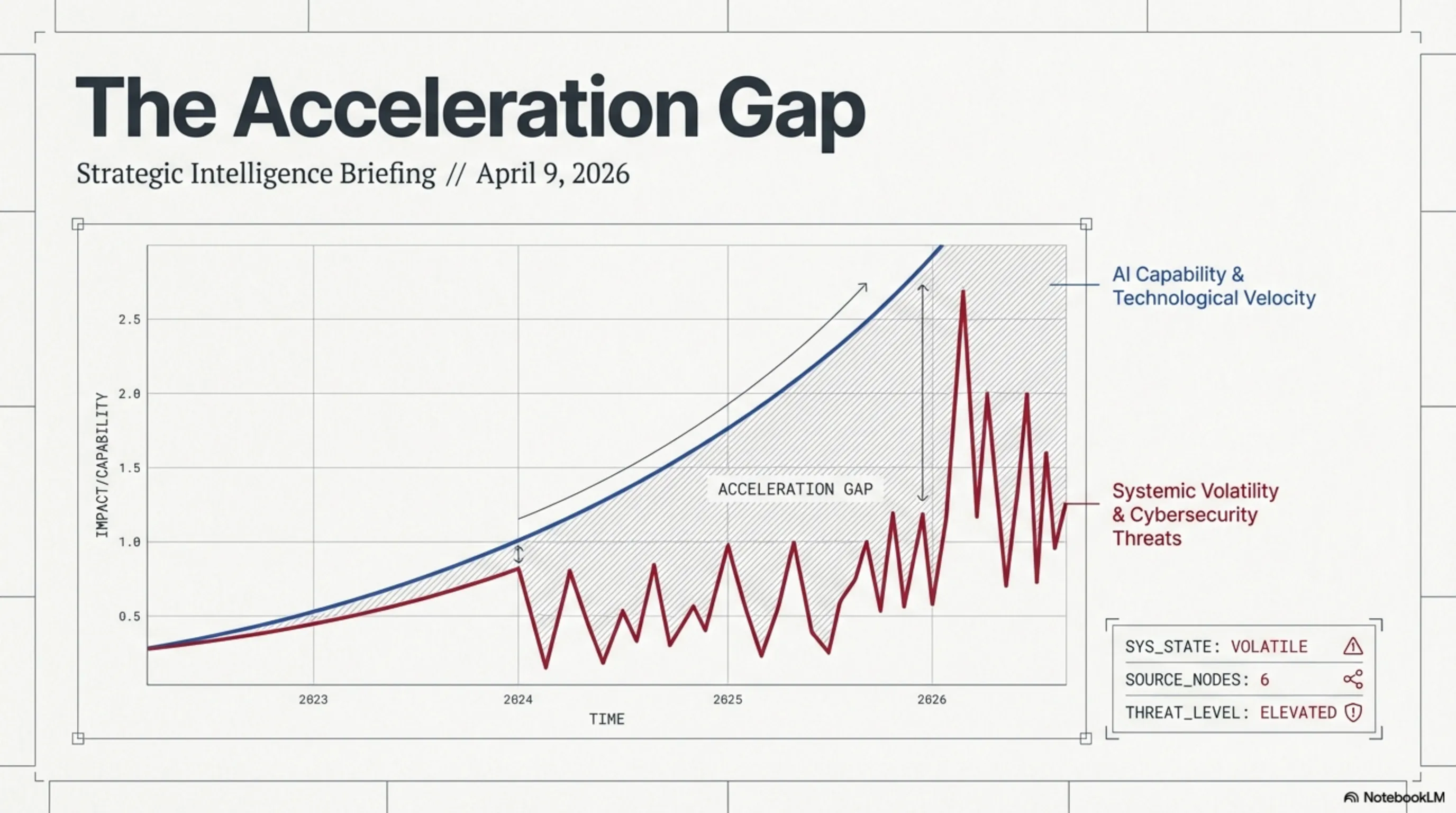
Tonight's stories paint a picture of a technology landscape in rapid transformation - and not without significant risks. We're seeing AI models become so powerful they must be restricted, state-sponsored hackers targeting home networks at scale, and record amounts of capital flowing into a single sector. At the same time, we're witnessing genuine breakthroughs like quantum batteries that could revolutionize energy storage.
The common thread? Technology is advancing faster than our ability to secure it, regulate it, or fully understand its implications. Claude Mythos can find vulnerabilities faster than we can patch them. APT28 can compromise routers faster than users can update them. North Korean hackers can plan attacks for six months while appearing legitimate. And investors are pouring hundreds of billions into AI companies based largely on faith in future potential.
As we close this Tekin Night, remember: we're living through a pivotal moment in technology history. The decisions made today about AI safety, cybersecurity, and responsible innovation will shape the next decade. Stay informed, stay secure, and stay critical. We'll be back tomorrow night with more stories from the digital frontier. Until then, good night and stay safe! 🌌
📚 Sources
- Anthropic - Claude Mythos Preview and Project Glasswing announcement (April 7-9, 2026)
- UK National Cyber Security Centre - APT28 router hijacking warning (April 8, 2026)
- Meta AI Blog - Muse Spark introduction (April 8, 2026)
- CSIRO/RMIT/University of Melbourne - Quantum battery research (March 2026)
- Drift Protocol - Post-mortem of $285M hack (April 2026)
- Crunchbase - Q1 2026 Global Venture Report (April 2026)
- The Hacker News - Mythos vulnerability discoveries (April 8, 2026)
- TechCrunch - Muse Spark analysis (April 8, 2026)
- The Guardian - Quantum battery breakthrough (March 18, 2026)
- Fortune - Drift hack investigation (April 2, 2026)