🌙 Welcome to Tekin Night April 18, 2026
Good evening, tech enthusiasts! Tonight we bring you 6 hot and critical stories from the technology world. From sophisticated DDoS attacks on Bluesky to the discovery of a 13-year-old vulnerability in Apache ActiveMQ, from hackers' new techniques to evade Windows security to ransomware threats against major brands - it's all here.
⚡ Tonight's Headlines:
🔵 Sophisticated DDoS Attack on Bluesky: Social Network Under Pressure
🚨 13-Year-Old Apache ActiveMQ Vulnerability on CISA List
💻 Hackers Evading Windows Security with QEMU
💰 ShinyHunters Threatens Three Major Brands
😰 Teenagers Worried About AI Impact on Mental Health
🇪🇺 EU Forces Google to Share Search Data
🌃 Grab your evening beverage and get ready for an exciting news journey through the tech world!
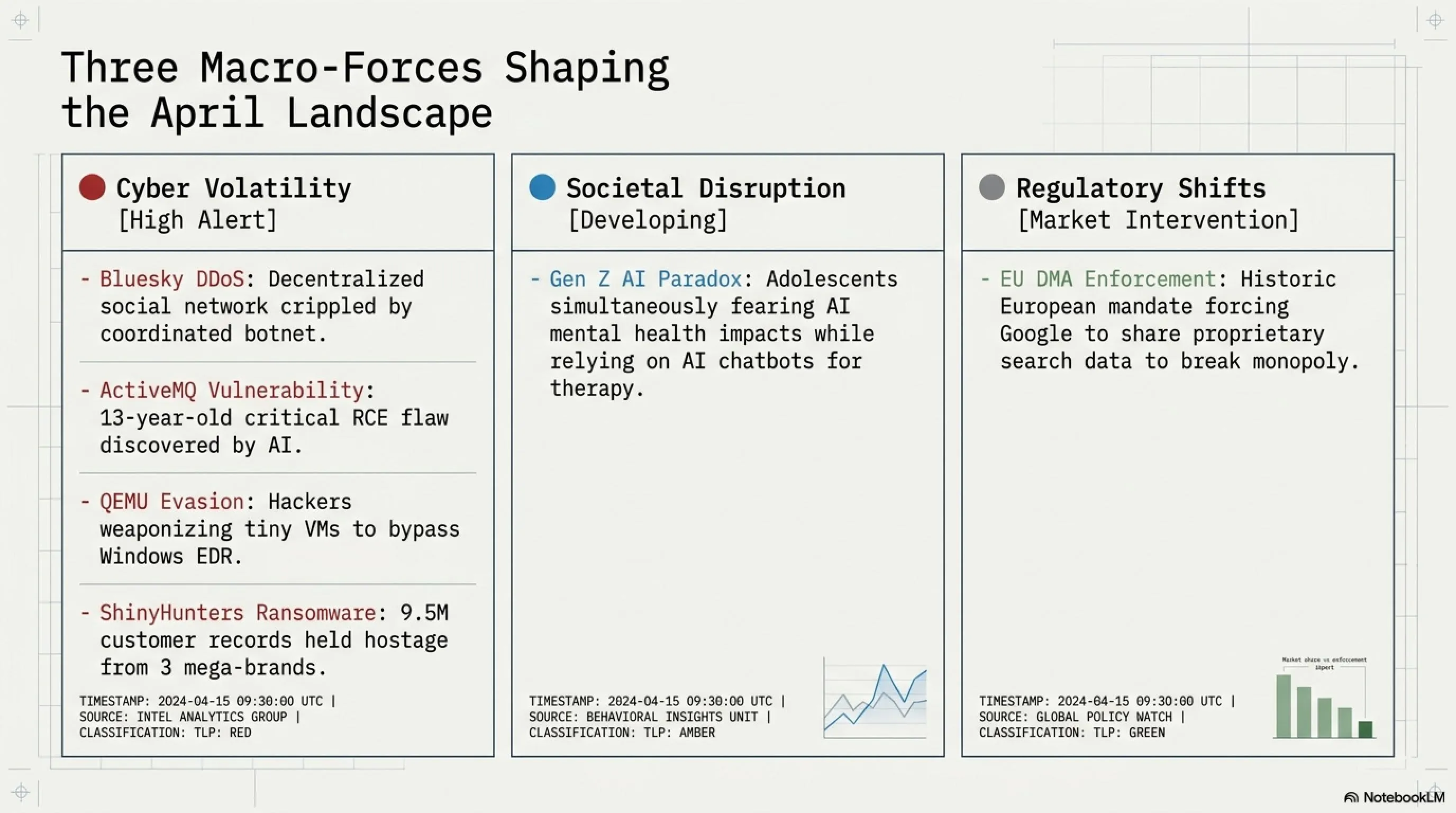
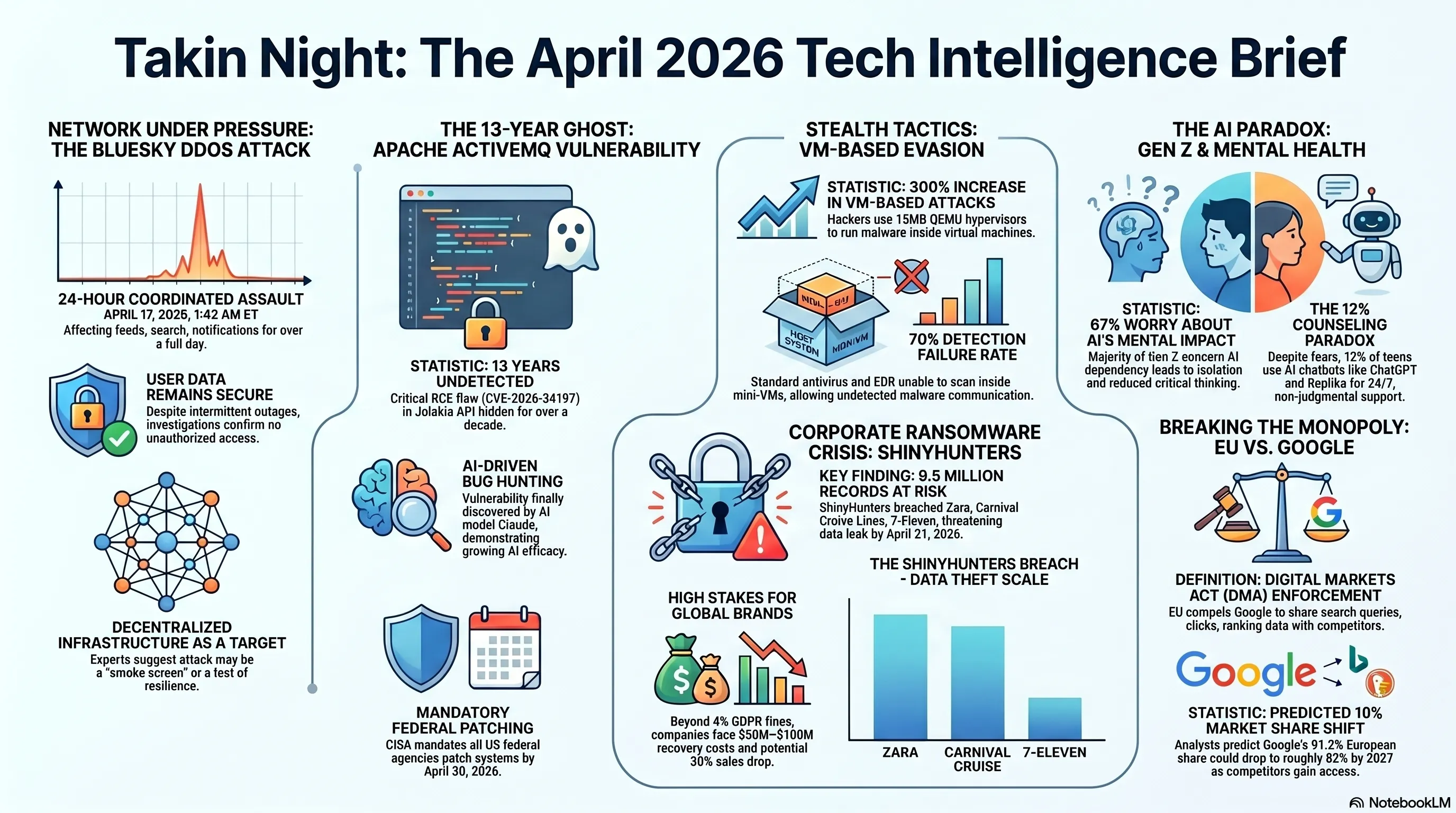
🔵 Bluesky Under Sophisticated DDoS Attack: Social Network Under Pressure
Bluesky, the decentralized social network known as an alternative to Twitter (X), has been under a severe and sophisticated DDoS (Distributed Denial of Service) attack since Thursday, April 17. According to the Bluesky team, this "sophisticated" and "coordinated" attack has caused intermittent outages across various platform services.
📊 Attack Details
| Start Time | Thursday, April 17, 1:42 AM ET |
| Duration | Over 24 hours (ongoing at time of writing) |
| Affected Services | Feed, Notifications, Threads, Search |
| Attack Type | Sophisticated and Coordinated DDoS |
| User Data Status | ✅ No evidence of unauthorized access to private data |
DDoS attacks typically flood target servers with massive amounts of fake traffic, overwhelming them and disrupting access for legitimate users. In these types of attacks, hackers usually use botnets - thousands of infected devices that send coordinated requests to the target server.
🔍 Tekin Analysis: Why Was Bluesky Targeted?
Bluesky has experienced significant growth in recent months, with many users migrating from X (formerly Twitter) to this platform. This rapid growth could have various reasons for being targeted:
- Competition with larger platforms and potential attacks from rivals
- Testing Bluesky's decentralized infrastructure by hackers
- Using DDoS as a smokescreen for more sophisticated attacks
- Demonstration of power by hacker groups or hidden extortion
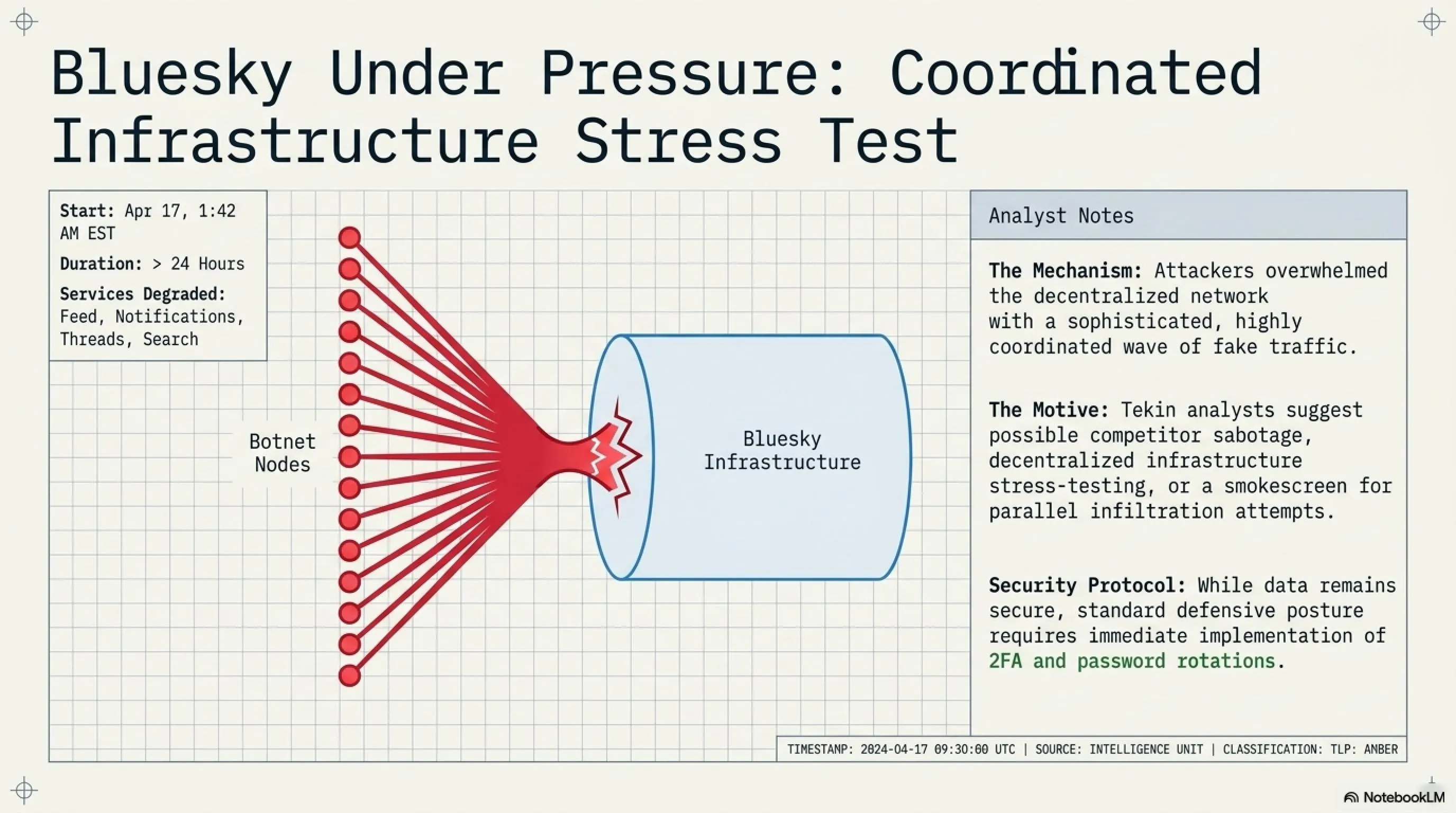
The Bluesky team has emphasized in their statements that there is no evidence of unauthorized access to users' private data. This is an important point because DDoS attacks are sometimes used as a "smokescreen" to hide actual intrusions. However, Bluesky's security team has stated they are monitoring all systems and have observed no signs of breach.
⚠️ Security Note
If you're a Bluesky user, don't worry - your data is safe. However, it's always recommended to have strong passwords and enable two-factor authentication (2FA). This DDoS attack only disrupted service access and did not access personal data.
🚨 13-Year-Old Apache ActiveMQ Vulnerability Added to CISA List
The US Cybersecurity and Infrastructure Security Agency (CISA) added a critical vulnerability in Apache ActiveMQ to its Known Exploited Vulnerabilities (KEV) catalog on April 16. The amazing thing is that this bug had been hidden in the code for 13 years and was only just discovered!
🔐 CVE-2026-34197 Vulnerability Specifications
| CVE ID | CVE-2026-34197 |
| Vulnerability Type | Improper Input Validation |
| Impact | Remote Code Execution (RCE) |
| Authentication Required | Yes (authenticated user) |
| Hidden Duration | 13 years! |
| Exploitation Status | 🔴 Actively being exploited |
| Patch Deadline | ⏰ April 30, 2026 |
Apache ActiveMQ is an open-source message broker used for transferring data between applications and services. This vulnerability is located in the Jolokia management API and allows an attacker to execute arbitrary code remotely - essentially turning a message broker into a remote command executor!
🎯 How Did This Bug Stay Hidden for 13 Years?
Interestingly, this vulnerability was discovered by Claude (an AI model from Anthropic) during a bug bounty hunt! Security researchers say this bug was "hiding in plain sight" but nobody noticed it. This shows that:
- Legacy code can contain hidden vulnerabilities
- AI can be effective in security bug hunting
- Regular security reviews are essential even for old code
CISA has ordered all US federal agencies to patch their systems by April 30. If you also use Apache ActiveMQ, immediately update to patched versions. This is a serious warning because the bug is being actively exploited.
✅ Immediate Actions
If you're a system administrator using Apache ActiveMQ: 1) Immediately install patched versions 2) Check system logs for suspicious activity 3) Restrict access to the Jolokia management API 4) Implement strong authentication and access control.
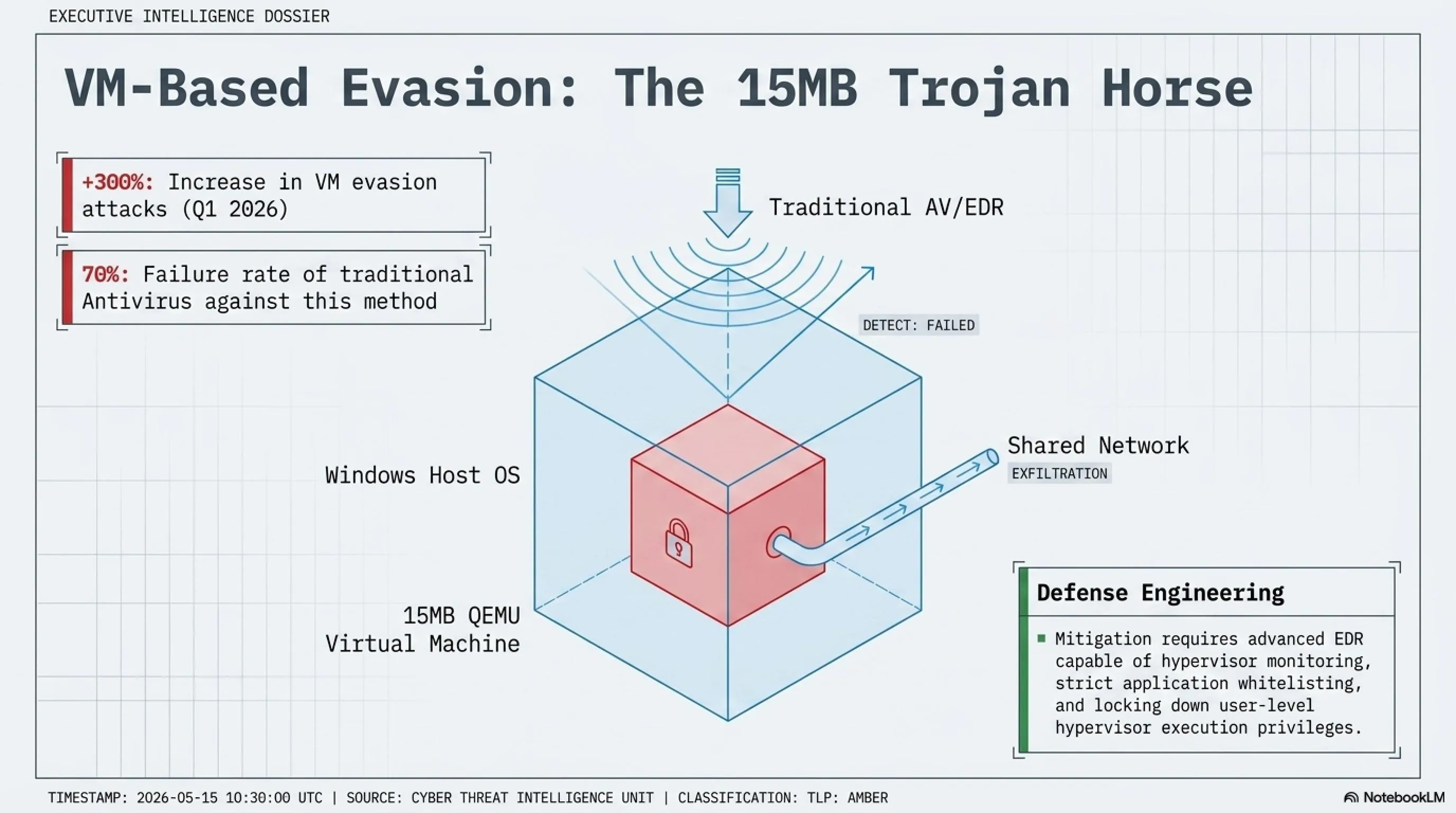
💻 Hackers Using QEMU to Evade Windows Security
Security researchers have discovered that hackers are using QEMU virtual machines to evade Windows security systems. This new technique allows attackers to hide their malware in a virtual environment and escape detection by antivirus and EDR (Endpoint Detection and Response) systems.
🔬 How Does This Attack Work?
| Step 1 | Install QEMU (an open-source hypervisor) on victim's system |
| Step 2 | Create a small virtual machine inside the system |
| Step 3 | Run malware inside the virtual machine |
| Step 4 | Communicate with host system via shared folders or network |
| Result | 🔴 Antivirus doesn't see malware because it's inside VM |
QEMU is an open-source software for creating virtual machines typically used by developers and IT professionals. But now hackers have realized they can use it to hide their malware. Since most antivirus software only scans the host system and doesn't check inside virtual machines.
📊 Alarming Statistics
This technique is known as "VM-based evasion" and is one of the most sophisticated detection evasion methods. Hackers can even send a stripped-down version of QEMU (about 15 megabytes) along with their malware, making installation and execution very fast.
🛡️ Protection Solutions
- Use advanced EDR that also monitors virtual machines
- Restrict hypervisor execution on user systems
- Monitor unusual network activity
- Use Application Whitelisting
- Train users to identify suspicious files
💰 ShinyHunters Threatens Three Major Brands
The notorious ransomware group ShinyHunters has announced they've stolen sensitive data from three major global brands - Zara, Carnival Cruise Lines, and 7-Eleven. The group threatens to release over 9 million customer records if ransom isn't paid by April 21.
🎯 Attack Details
| Victim | Record Count | Data Type |
| Zara | 4.2 million | Customer info, transactions |
| Carnival | 3.8 million | Passports, credit cards, bookings |
| 7-Eleven | 1.5 million | Loyalty program, payment info |
| Total | 9.5 million | 🔴 Critical |
⏰ Deadline: April 21, 2026 | Status: Under negotiation
ShinyHunters is one of the most active ransomware groups with a history of attacking major companies like Microsoft, AT&T, and Ticketmaster. The group typically exploits API and database vulnerabilities to gain access, then sells stolen data on the dark web or uses it for extortion.
💸 Economic Impact Analysis
This attack could cause severe financial damage to these brands:
- Recovery costs: $50-100 million per company
- GDPR fines: Up to 4% of annual revenue
- Loss of trust: 20-30% sales decline short-term
- Legal lawsuits: Millions in customer compensation
- Security costs: Infrastructure security upgrades
Interestingly, ShinyHunters typically releases stolen data samples as "proof" on hacker forums to show their claims are real. In this case, they've published samples from Zara and Carnival data including names, emails, phone numbers, and even portions of credit card information.
⚠️ If You're a Customer of These Brands
Immediately change your account passwords. If you use the same password on other sites, change those too. Monitor your bank cards and report any suspicious transactions to your bank immediately. Enable two-factor authentication on all important accounts.
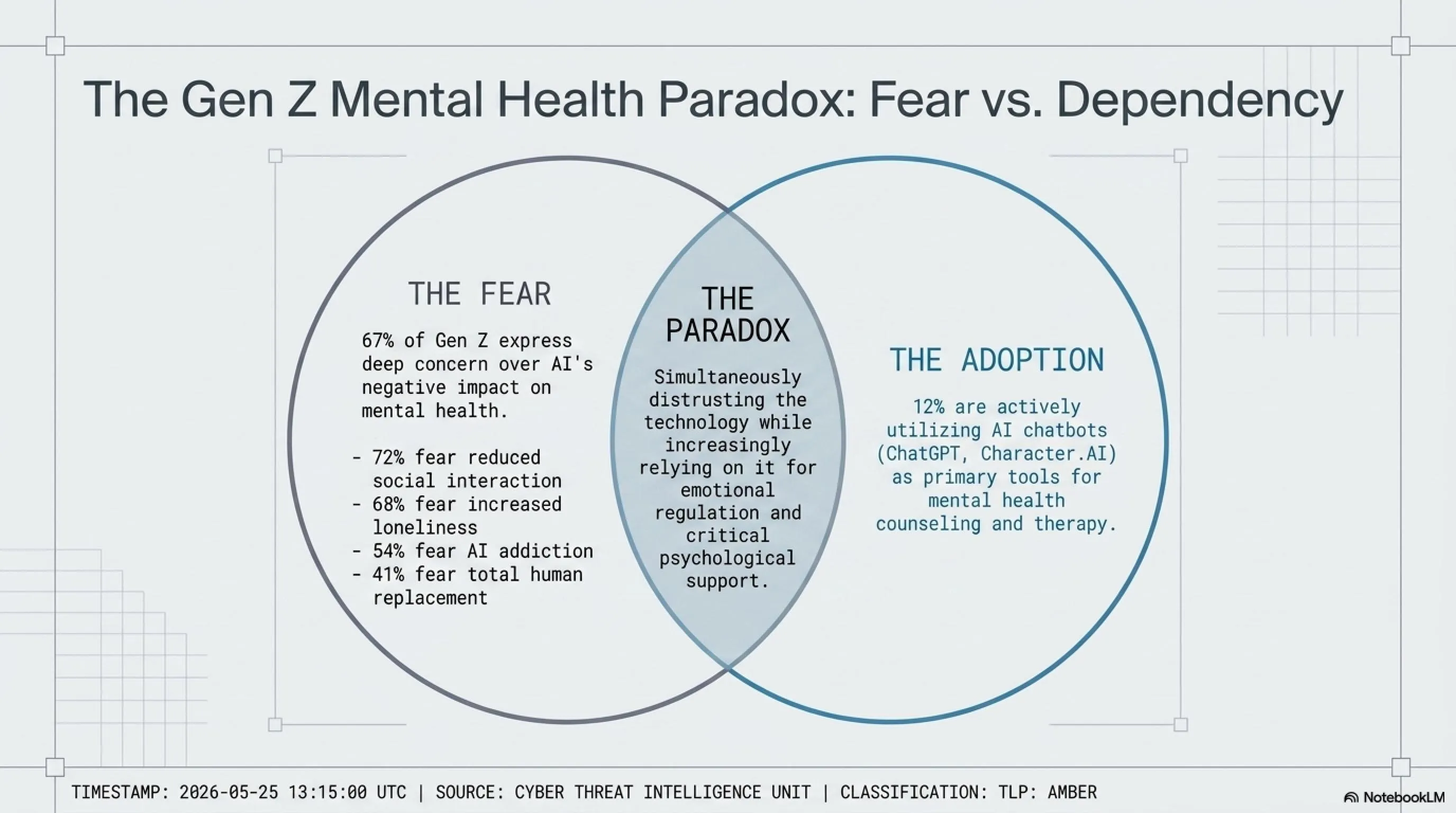
😰 Teenagers Concerned About AI Impact on Mental Health
A new survey shows that teenagers are increasingly concerned about AI's impact on their mental health. Interestingly, while 67% express concern, 12% are using AI tools for mental health counseling - a worrying paradox!
📊 Survey Statistics
This survey conducted by a reputable research institute shows that Gen Z teenagers (born 1997-2012) have deep concerns about AI's impact on their daily lives. They fear that over-reliance on AI will reduce social skills, increase loneliness, and cause mental health problems.
🧠 The AI and Mental Health Paradox
| Concern | Percentage |
| Reduced real social interactions | 72% |
| Increased feelings of loneliness | 68% |
| Dependency on AI for decision-making | 61% |
| Reduced creativity and critical thinking | 58% |
| Privacy violation concerns | 76% |
But here's the paradox: while teenagers are concerned about AI's negative impact, many use AI chatbots like ChatGPT, Character.AI, and Replika to talk about their mental health issues. Reasons include: easy 24/7 access, no judgment, free cost, and privacy protection.
✅ Pros and Cons of Using AI for Mental Health
✅ Pros
- Instant 24/7 access
- Free or affordable
- No judgment
- Privacy protection
- Easy to express problems
❌ Cons
- Lack of real empathy
- Risk of misdiagnosis
- No deep understanding
- Addiction risk
- No medical license
Mental health experts warn that while AI can be a useful support tool, it should never replace professional counseling. AI chatbots cannot recognize emergencies, show real empathy, or provide specialized treatments. Using AI for mental health should be done cautiously and as a complement - not a replacement - to human counseling.
💡 Tekin Recommendation
If you're a teenager using AI for mental health counseling, remember it's just a tool. In serious situations, always talk to a real psychologist or counselor. Discuss your concerns with parents or teachers. Maintain balance between technology use and real human interactions.
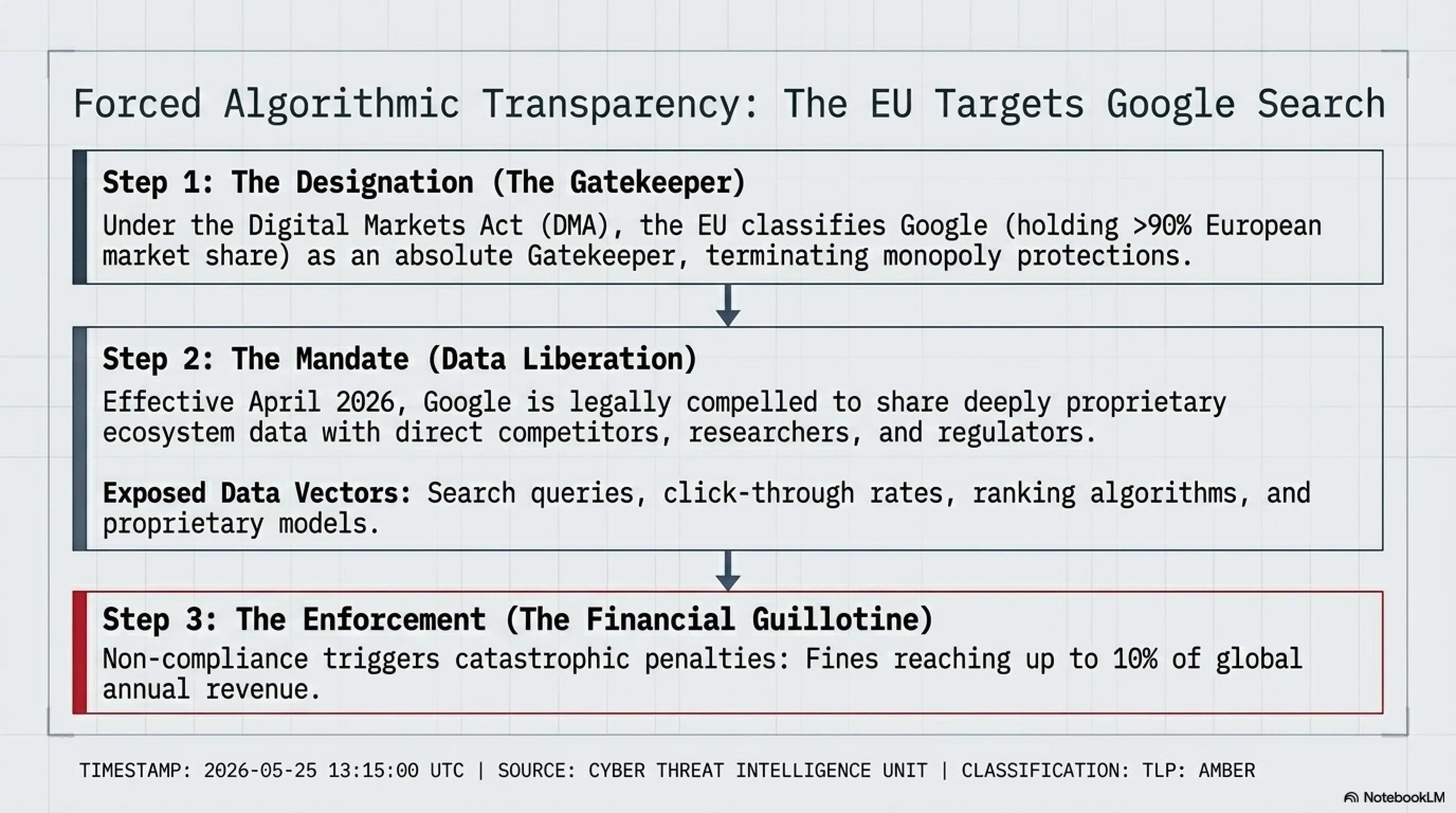
🇪🇺 EU Forces Google to Share Search Data with Competitors
The European Union, under the Digital Markets Act (DMA), has forced Google to share its search data with competitors. This historic decision could forever change the search engine landscape and break Google's monopoly.
⚖️ EU Decision Details
| Law | Digital Markets Act (DMA) |
| Effective Date | April 2026 |
| Covered Data | Queries, clicks, rankings, algorithms |
| Beneficiaries | Competing search engines, researchers, regulators |
| Non-Compliance Penalty | Up to 10% of global annual revenue |
The DMA, which came into effect in March 2024, forces large tech companies (called "Gatekeepers") to stop their monopolistic behaviors. Google, with over 90% search market share in Europe, is recognized as a Gatekeeper and must comply with these rules.
🌍 Impact on Search Industry
This decision could create massive changes in the search industry:
- More competition: Smaller search engines can use Google's data to improve their algorithms
- Transparency: Researchers can better understand how Google's algorithms work
- Innovation: New startups can build better products with access to data
- Reduced monopoly: Google's market share may decrease
- Privacy: Concerns about user data security exist
📊 Search Engine Market Share Comparison in Europe
| Search Engine | Current Share | 2027 Forecast |
| 91.2% | 82-85% ⬇️ | |
| Bing | 3.8% | 6-8% ⬆️ |
| DuckDuckGo | 1.5% | 3-4% ⬆️ |
| Yandex | 1.2% | 2-3% ⬆️ |
| Others | 2.3% | 4-6% ⬆️ |
Google is obviously unhappy with this decision, arguing that sharing search data could compromise user privacy and eliminate the company's competitive advantage. But the EU argues that Google's monopoly harms innovation and users deserve more choices.
💡 Tekin Opinion
This is a historic decision that could set a precedent for other countries. If successful, the US, Canada, and other nations may enact similar laws. For users, this means better search engines, more accurate results, and greater privacy. For Google, it's a major challenge they must adapt to.
🌙 Tekin Night April 18 Wrap-Up
Tonight we witnessed 6 important and impactful tech stories, each shaping our digital future in different ways:
- Bluesky under DDoS: Showed that even decentralized platforms are vulnerable to cyber attacks
- 13-year-old Apache ActiveMQ bug: Reminded us that security bugs can hide for years
- Hackers evading with QEMU: New attack techniques are always evolving
- ShinyHunters threats: Ransomware remains one of the biggest cyber threats
- Teenagers and AI: The new generation is concerned about AI's impact on their lives
- EU vs Google: Antitrust laws can transform the tech industry
These stories show that the tech world is rapidly changing - from cybersecurity to digital regulations and AI's social impacts. At Tekin, we always monitor these changes to keep you updated.
🌃 Good night and see you tomorrow morning at Tekin Morning!
📚 Sources and References
Sources: Bluesky Official Status Updates, CISA KEV Catalog, Apache ActiveMQ Security Advisories, Cybersecurity Research Reports, ShinyHunters Dark Web Posts, Teen Mental Health Surveys 2026, European Commission DMA Enforcement, TechCrunch, The Verge, Ars Technica, BleepingComputer, SecurityWeek
Analysis and Research: Tekin Editorial Team
Publication Date: April 18, 2026 - 5:00 AM Tehran Time
❓ Frequently Asked Questions
How can I protect against DDoS attacks?
To protect against DDoS attacks: 1) Use CDN services like Cloudflare 2) Implement rate limiting 3) Enable Layer 7 firewalls 4) Filter suspicious traffic 5) Use load balancers 6) Have an incident response plan 7) Monitor traffic patterns 8) Consider DDoS mitigation services.
Should I update Apache ActiveMQ immediately?
Yes, absolutely! CVE-2026-34197 is a critical vulnerability being actively exploited. CISA has set an April 30 deadline. Update to the latest patched version immediately, restrict access to Jolokia management API, review system logs for suspicious activity, and implement strong authentication and access controls.
How do I detect QEMU VM-based malware on my system?
Signs of QEMU VM infection: 1) qemu-system processes in Task Manager 2) Unusual CPU/RAM consumption 3) Suspicious network traffic from unknown processes 4) Suspicious .qcow2 or .img files 5) Unauthorized hypervisor execution. Use advanced EDR solutions that monitor virtual machines and implement application whitelisting.
What should I do if I'm a Zara, Carnival, or 7-Eleven customer?
Immediate actions: 1) Change your account password immediately 2) Change passwords on other sites if you reused them 3) Monitor your bank cards 4) Enable two-factor authentication (2FA) 5) Notify your bank 6) Wait for official company notification 7) Use credit monitoring services 8) Watch for phishing attempts.
Is it safe to use AI for mental health counseling?
AI can be a helpful supplementary tool but should never replace professional counseling. Limitations: lack of genuine empathy, risk of misdiagnosis, no deep understanding, no medical license. In serious situations, always consult a real psychologist. AI is only suitable for initial, non-professional support and should complement, not replace, human therapy.
What impact will the EU decision have on Google?
Under the DMA, Google must share search data (queries, clicks, rankings, algorithms) with competitors. Impacts: potential market share decrease from 91% to 82-85%, increased competition, greater transparency, innovation in search industry. Non-compliance could result in fines up to 10% of global annual revenue.
🌐 Stay Connected With Us
For the latest tech, gaming, and gadget news, follow us on social media:
🌐 Stay Connected With Us 🎮✨
For the latest tech, gaming, and gadget news, follow us on our official social media channels:
