North Korean Supply Chain Attack Hits OpenAI: When Axios Gets Compromised
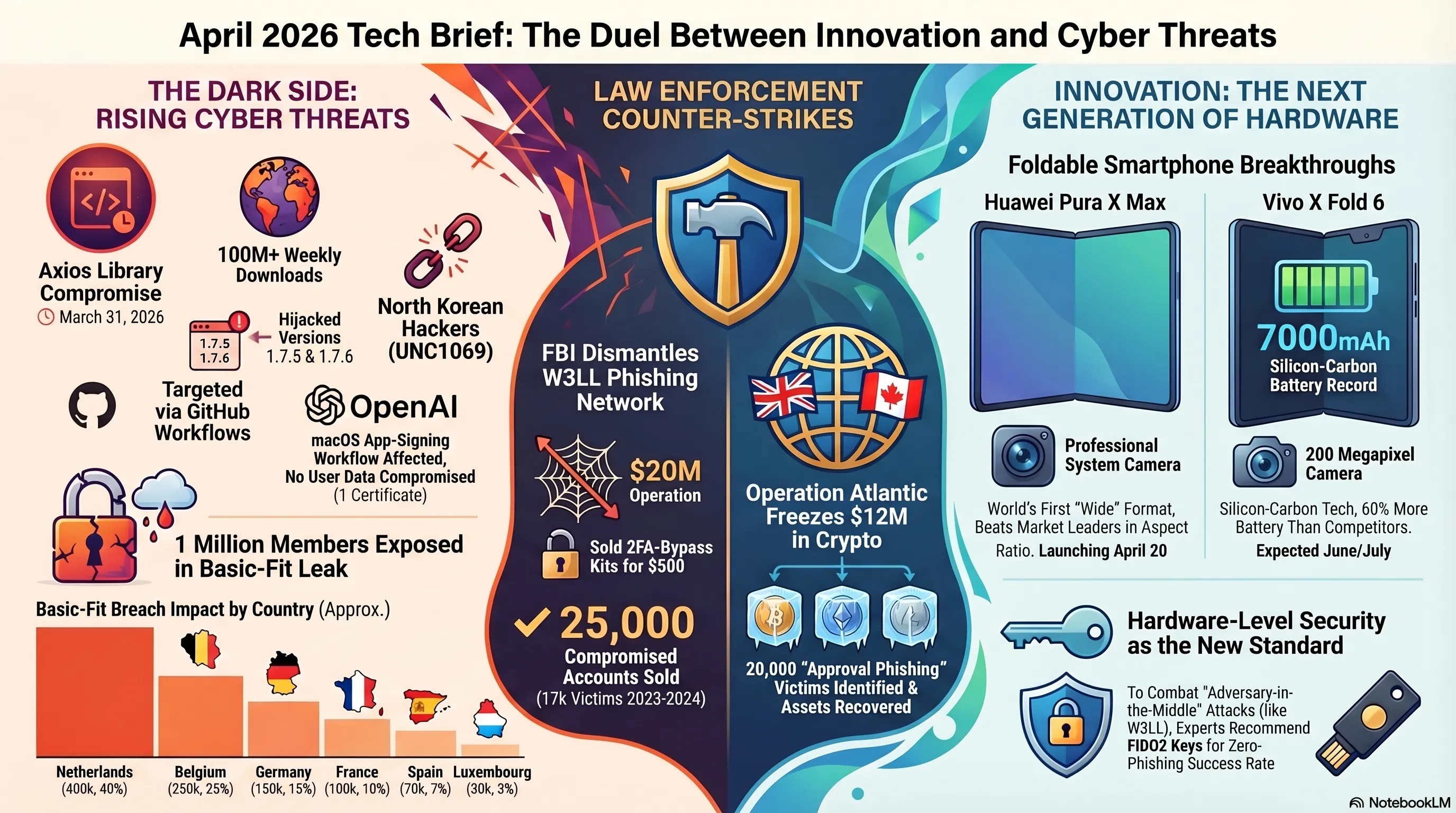
The night of April 13 started with shocking news: OpenAI, one of the world's largest AI companies, announced it had fallen victim to a sophisticated supply chain attack carried out by the UNC1069 hacking group linked to North Korea. The attack targeted the popular JavaScript library Axios - a library used by millions of developers worldwide.
How Did This Attack Happen?
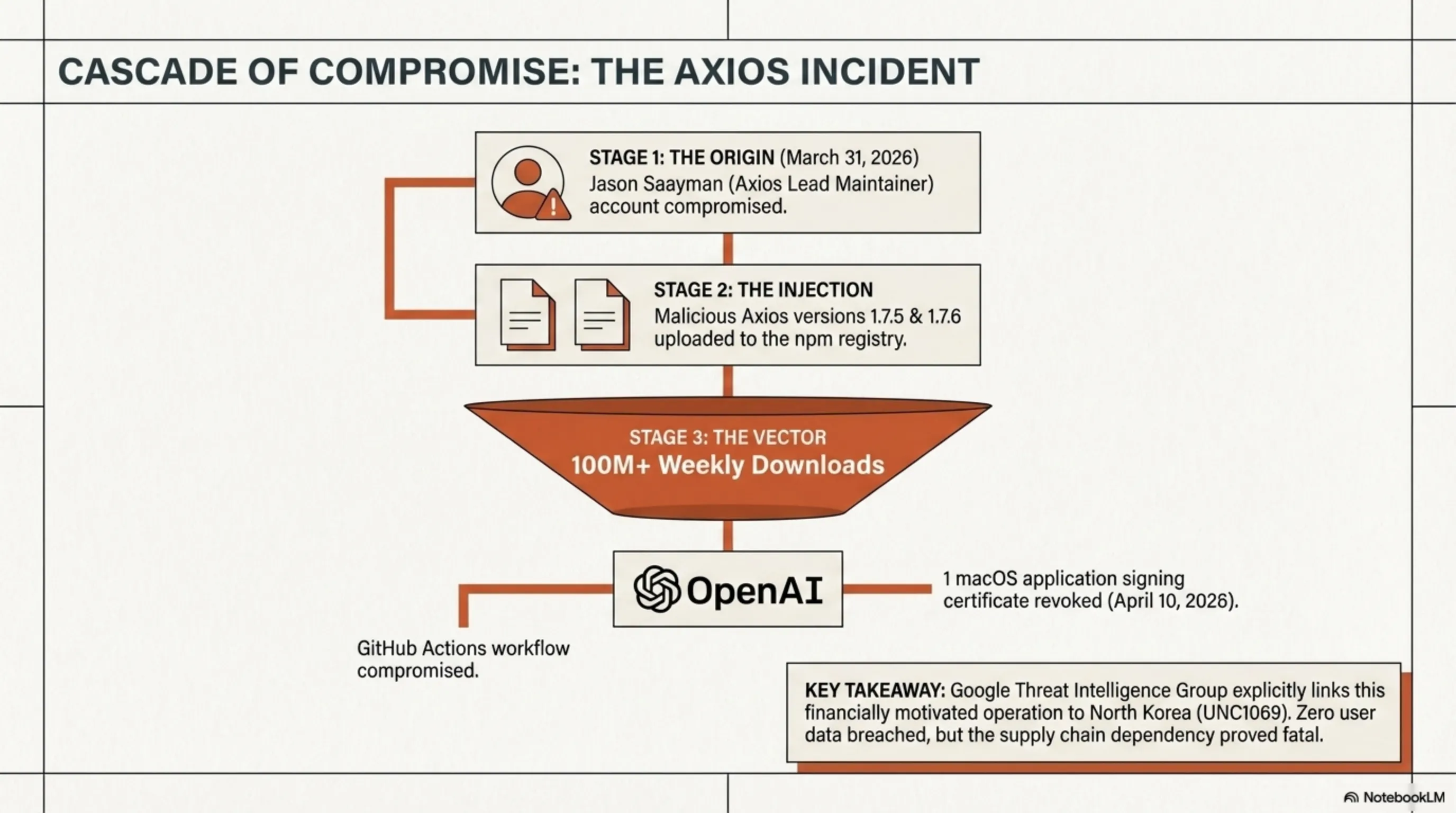
On March 31, 2026, hackers managed to compromise the primary account of Jason Saayman, the main maintainer of Axios. This allowed them to publish two malicious versions of Axios to npm (the largest public registry of JavaScript tools). These malicious versions contained code capable of stealing sensitive information.
OpenAI announced on April 10 that one of its GitHub Actions workflows used to sign macOS applications had downloaded the malicious Axios library on March 31. Fortunately, OpenAI emphasized that no user data or internal systems were compromised, but a macOS signing certificate was potentially compromised and needed to be revoked.
North Korea's Role and the UNC1069 Group
Google Threat Intelligence Group (GTIG) formally attributed this attack to UNC1069 - a North Korean-linked hacking group operating with financial motivations. This group is known for sophisticated and targeted supply chain attacks.
🔍 Tekin Analysis: Why This Attack Is Dangerous
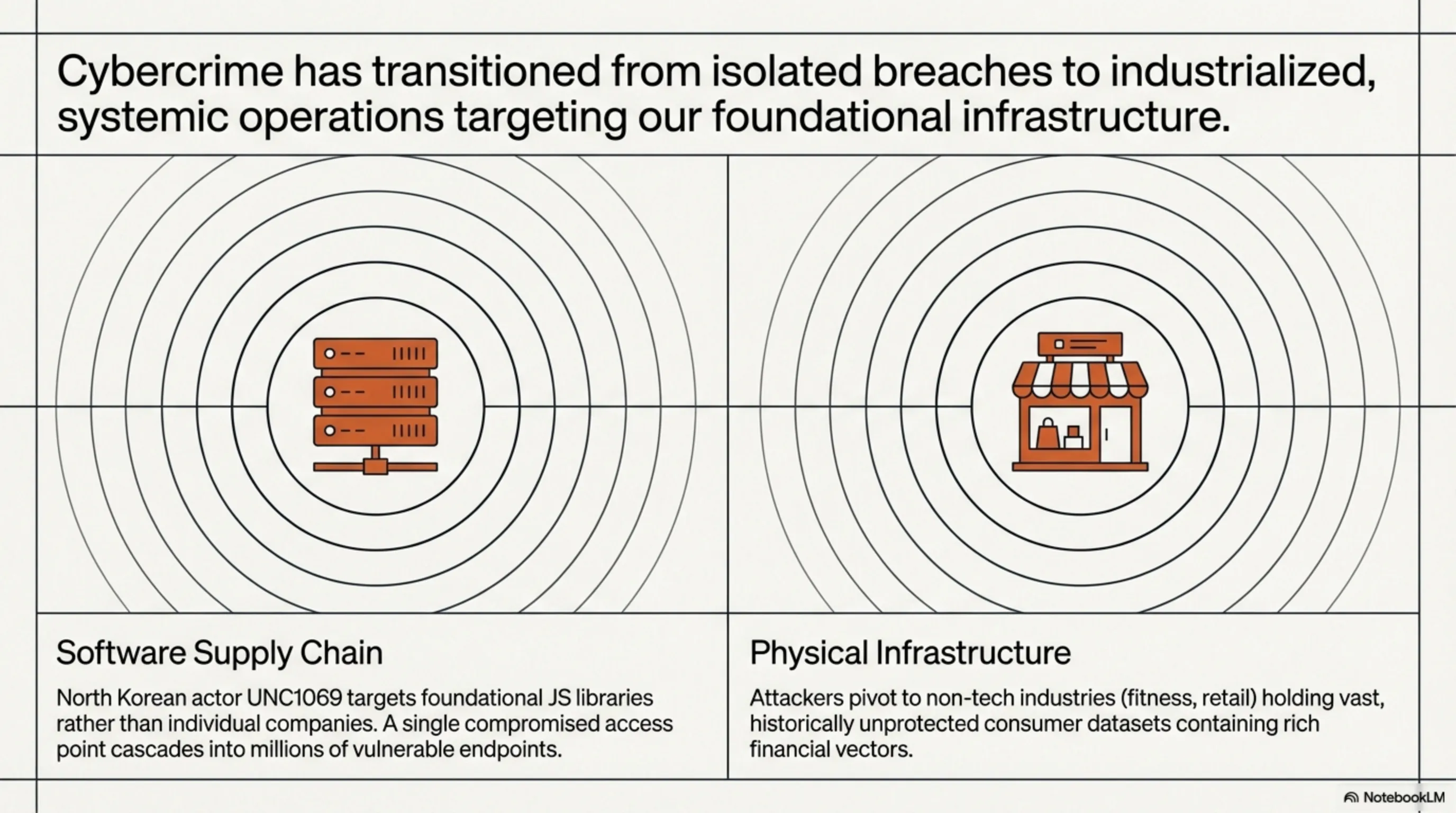
This attack demonstrates that North Korean hackers are moving from opportunistic attacks toward industrialized, precision operations. With over 100 million weekly downloads, Axios is one of the most widely used JavaScript libraries globally. Compromising such a library could impact thousands of companies and millions of users. This is a reminder that supply chain security is no longer optional - it's a survival necessity.
Industry Response and Security Measures
OpenAI immediately initiated security measures and revoked its macOS signing certificate. The company also collaborated with npm and GitHub to remove the malicious Axios versions from the registry. npm updated its detection systems to prevent similar attacks in the future.
This attack serves as a serious warning for all tech companies to scrutinize their dependencies more carefully. Using tools like Dependabot, Snyk, and OWASP Dependency-Check can help identify vulnerabilities.
How to Protect Yourself
If you use Axios, make sure to check your version. The malicious versions were 1.7.5 and 1.7.6, which have now been removed from npm. Always use official and verified versions, and scan your dependencies with security tools. Additionally, using lock files (like package-lock.json) can prevent unwanted version installations.
💡 Security Tip
Always use two-factor authentication (2FA) for your npm and GitHub accounts. Also, grant publish access only to trusted individuals and use limited tokens. This can prevent your packages from being compromised.
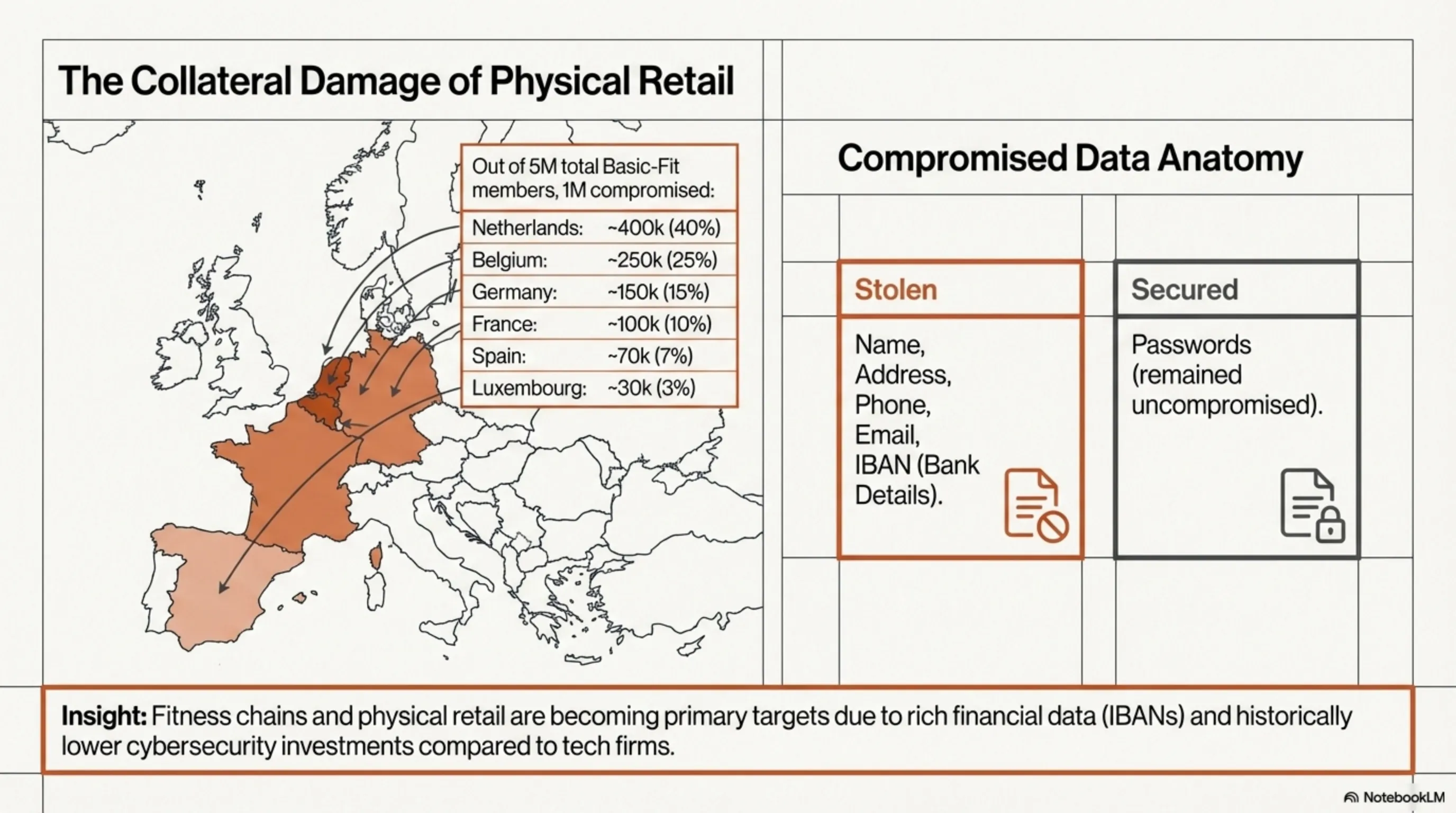
Basic-Fit and the 1 Million Member Data Breach: Europe's Gym Security Crisis
While everyone was focused on cyberattacks against tech companies, a major security crisis unfolded in the fitness industry. Basic-Fit, Europe's largest gym chain with approximately 5 million members, announced it had fallen victim to a massive data breach that exposed information of around 1 million members.
What Data Was Leaked?
This data breach includes a significant amount of sensitive information that could be dangerous for victims:
- Personal Information: Full name, address, email, phone number, and date of birth
- Financial Information: Bank account details used for subscription payments
- Membership Information: Membership date, subscription type, and payment history
The breach affected 6 European countries: Netherlands (200,000 members), Belgium, France, Spain, Luxembourg, and Germany. Basic-Fit quickly identified the unauthorized access and notified all affected members.
How Did This Attack Happen?
Basic-Fit hasn't disclosed the exact details of the attack, but it appears hackers managed to access the company's internal systems. These types of attacks typically occur through phishing, software vulnerabilities, or weak credentials.
⚠️ Security Alert
If you're a Basic-Fit member, carefully check suspicious emails and text messages. Hackers may use this information for phishing attacks. Never click on suspicious links and don't give your banking information to anyone. Also, change your bank account password and report suspicious activities to your bank.
Basic-Fit's Response and Remedial Actions
Basic-Fit immediately collaborated with local authorities and cybersecurity experts to identify and block the source of the breach. The company also set up an emergency hotline for affected members and promised to compensate for any costs resulting from information misuse.
This incident shows that non-tech industries must also take cybersecurity seriously. Gyms, restaurants, stores, and any business storing customer information must invest seriously in security.
🛡️ Protection Solutions
To protect yourself from data breaches: 1) Use strong, unique passwords for each service, 2) Regularly check your bank account activities, 3) Use credit monitoring services, 4) Don't respond to suspicious emails and texts, 5) Limit your personal information on social media.
Impact on the Fitness Industry
This data breach could have a significant impact on the fitness industry. Many customers may lose trust in gyms and prefer not to provide their financial information to these companies. This could lead to decreased subscriptions and increased use of cash payment methods.
Basic-Fit must quickly strengthen its security measures and show customers they can trust it again. This includes implementing stronger encryption, multi-factor authentication, and training staff in cybersecurity.
FBI Takes Down W3LL: The $20 Million Phishing Operation
Amid all the bad security news, there was some good news: FBI Atlanta and Indonesian police successfully dismantled one of the world's largest phishing operations. The W3LL operation, a phishing-as-a-service network sold to cybercriminals for $500, had attempted over $20 million in fraud.
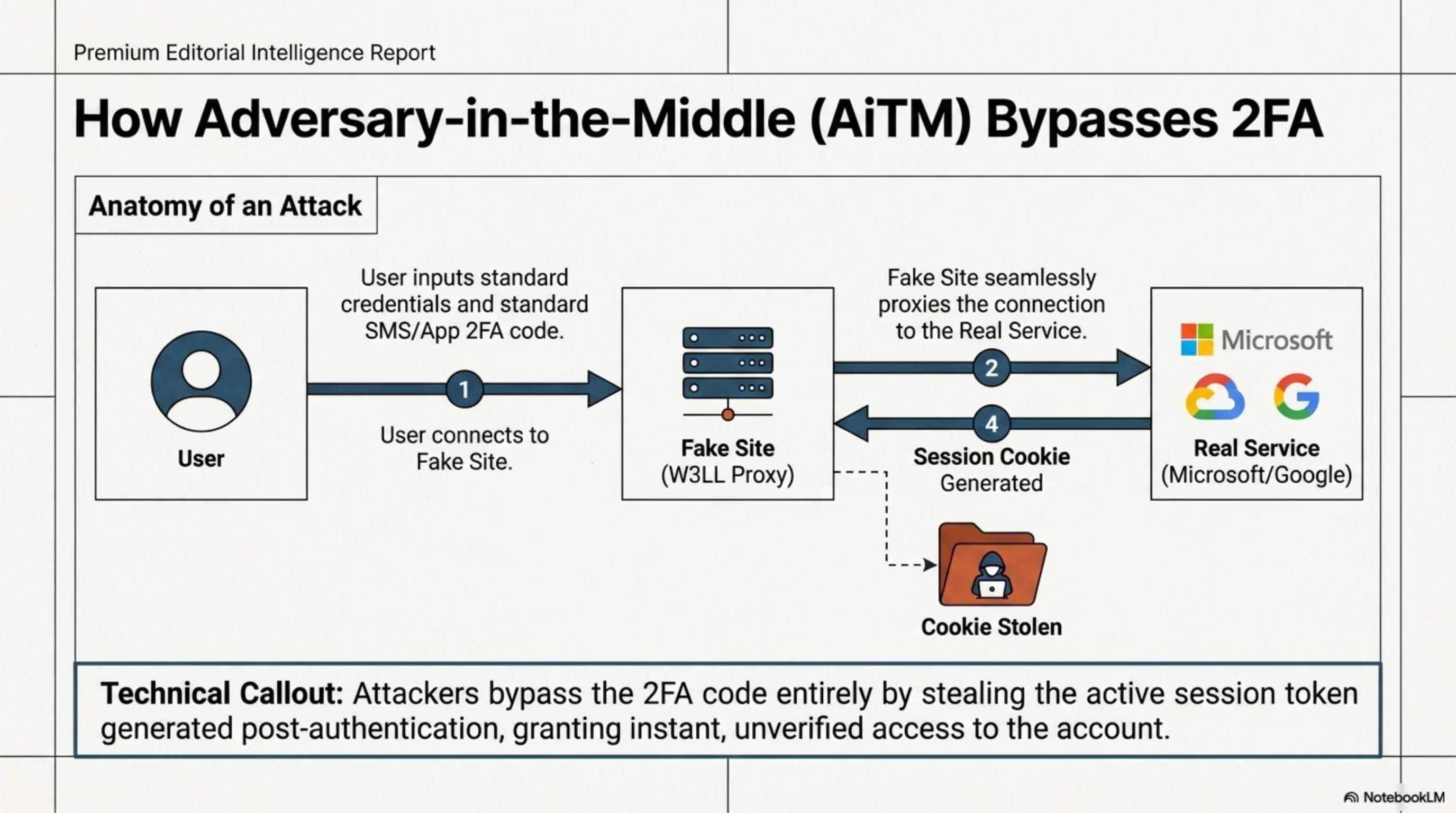
What Was W3LL?
W3LL was an advanced phishing kit that allowed cybercriminals to create fake login pages that looked almost identical to legitimate websites. But what made W3LL dangerous was its ability to bypass two-factor authentication (2FA).
The kit used adversary-in-the-middle techniques - meaning the phishing page sat between the victim and the real service, relaying credentials to the actual site while simultaneously stealing session cookies. This allowed criminals to access accounts without needing the 2FA code.
Shocking Statistics
According to the FBI report, the W3LL operation:
- Sold over 25,000 compromised accounts
- Had 17,000 victims worldwide
- Attempted over $20 million in fraud
- Was active between 2023 and 2024
Criminals could access this platform for around $500 and create their own phishing pages. This was a business-email-compromise (BEC) model that was easy to use and required no advanced technical knowledge.
🔍 Tekin Analysis: Why W3LL Was Successful
W3LL succeeded because it offered a phishing-as-a-service model that was extremely easy to use. Criminals didn't need advanced technical knowledge - they just had to pay $500 and could create professional phishing pages. This is a reminder that cybercrime is becoming an industry with clear business models and transparent pricing.
FBI Operation and Arrests
FBI Atlanta, in collaboration with Indonesian police, seized domains and infrastructure related to W3LL. Additionally, an individual with the alias G.L. was arrested in Indonesia, identified as the developer of this kit.
This operation was part of a broader effort to dismantle phishing-as-a-service networks. The U.S. Attorney's Office for the Northern District of Georgia also assisted in identifying and seizing servers supporting the scheme.
How to Protect Yourself
Even with W3LL dismantled, other phishing kits still exist. To protect yourself:
- Always check the website URL before entering information
- Use a password manager that only fills information on legitimate sites
- Use hardware key-based 2FA (like YubiKey) which is more resistant to phishing
- Don't trust suspicious emails asking you to log into your account
- Always go directly to the intended site, not through email links
💡 Advanced Security Tip
To protect against adversary-in-the-middle attacks, use FIDO2 security keys. These keys use cryptographic authentication that cannot be stolen by phishing pages. Large companies like Google and Microsoft provide security keys to their employees and have reported phishing attacks dropping to zero.
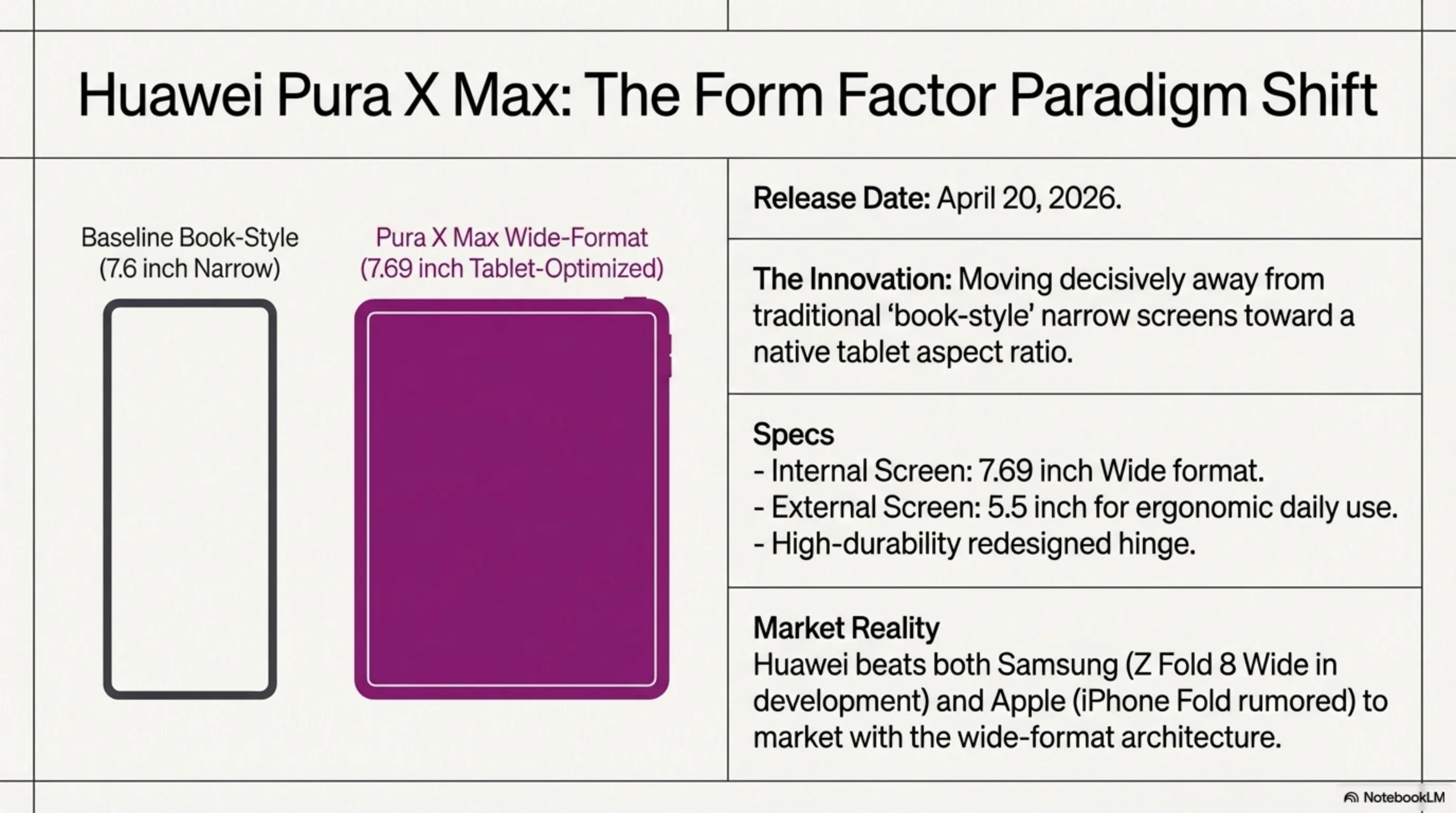
Huawei Pura X Max: World's First Wide Foldable Beats Samsung and Apple
Now for the good news! While Samsung and Apple were still working on wide-format foldable phones, Huawei unveiled the Pura X Max, the world's first wide-format foldable, leaving competitors behind.
Why Does Wide Format Matter?
Until now, almost all book-style foldables (like the Galaxy Z Fold) used a tall, narrow format. This means when you open the phone, you get a tall, narrow screen that isn't ideal for some tasks (like watching videos or working with multiple apps).
The Pura X Max, with its wide format, offers a wider, shorter screen when opened, providing a more tablet-like experience. This is better for multitasking, watching movies, and working with productivity apps.
Pura X Max Specifications
According to released information, the Pura X Max features:
- Inner Display: 7.69 inches with a wider aspect ratio
- Outer Display: 5.5 inches for everyday use
- Improved Hinge: New design with greater durability
- Premium Colors: Multiple luxury colors
- Large Battery: For extended use
- Advanced Cameras: Professional camera system
The official launch date for the Pura X Max is April 20, 2026. Huawei plans to release this phone first in China and then in global markets.
🎯 Market Analysis
With this move, Huawei caught Samsung and Apple off guard. Both companies are reportedly working on wide foldables (Galaxy Z Fold 8 Wide and iPhone Fold), but Huawei was first to market. This shows that despite sanctions, Huawei remains a powerful player in the mobile industry.
Samsung and Apple's Response
Samsung is reportedly developing the Galaxy Z Fold 8 Wide with similar dimensions to the Pura X Max. Apple also has many rumors about the iPhone Fold, but no official date has been announced yet.
This competition is good for consumers as it drives more innovation and potentially lower prices. The wide format could change the future of foldables and provide a better user experience.
Wide Format Challenges
Of course, the wide format has its own challenges:
- Pocket Size: When closed, the phone is wider and heavier
- One-Handed Use: The outer display may be too large for one-handed use
- App Optimization: Apps need to be optimized for the new aspect ratio
- Price: Likely more expensive than regular foldables
However, if Huawei can solve these challenges, the Pura X Max could be a game-changer and define a new standard for foldable phones.
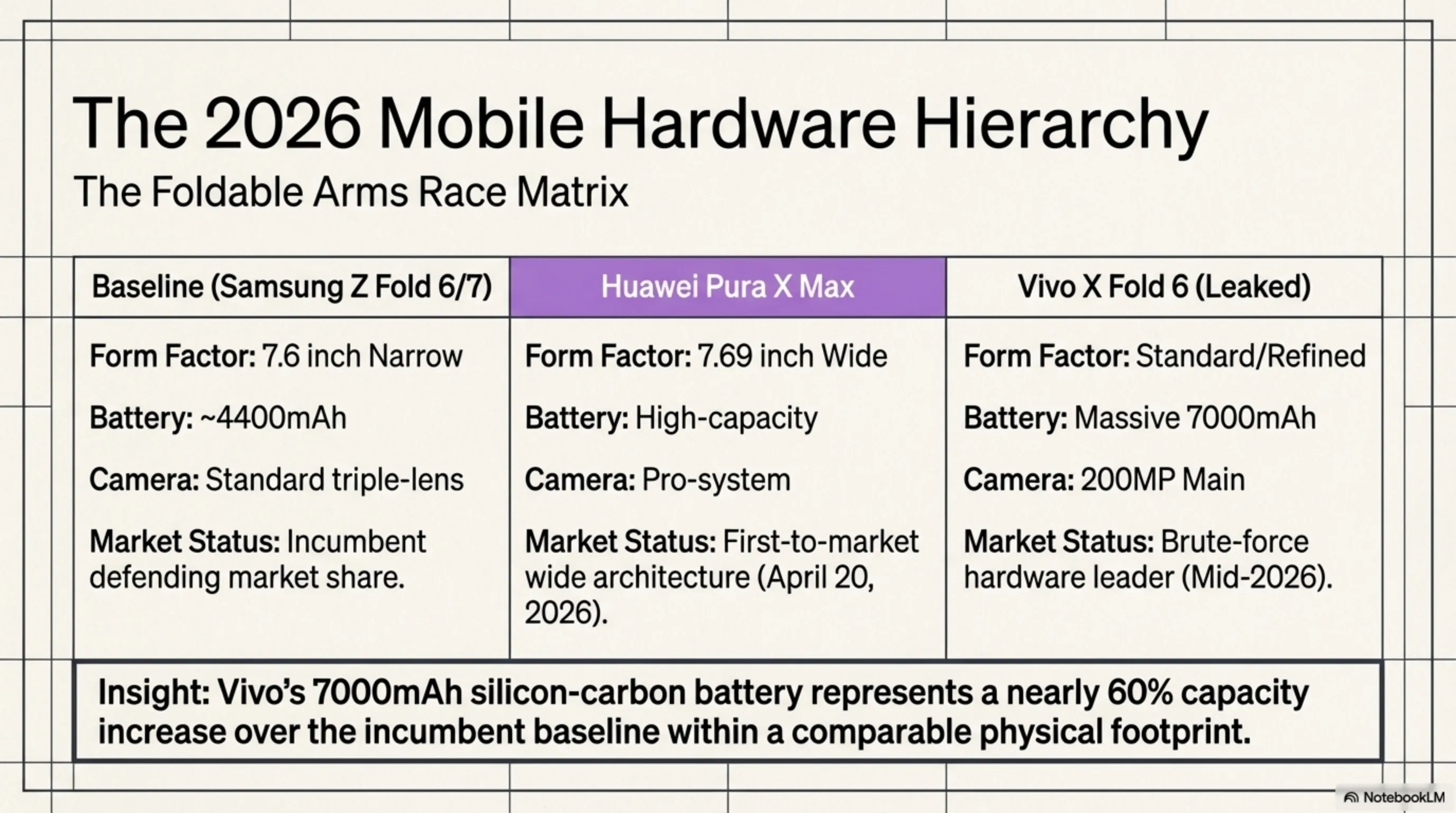
Vivo X Fold 6: 200MP Camera and the Biggest Battery in a Foldable
If you thought Huawei was the only company with news today, you're mistaken! Fresh leaks about the Vivo X Fold 6 reveal this phone will launch with stunning specifications that could set new records in the foldable world.
200-Megapixel Camera: A Major Leap
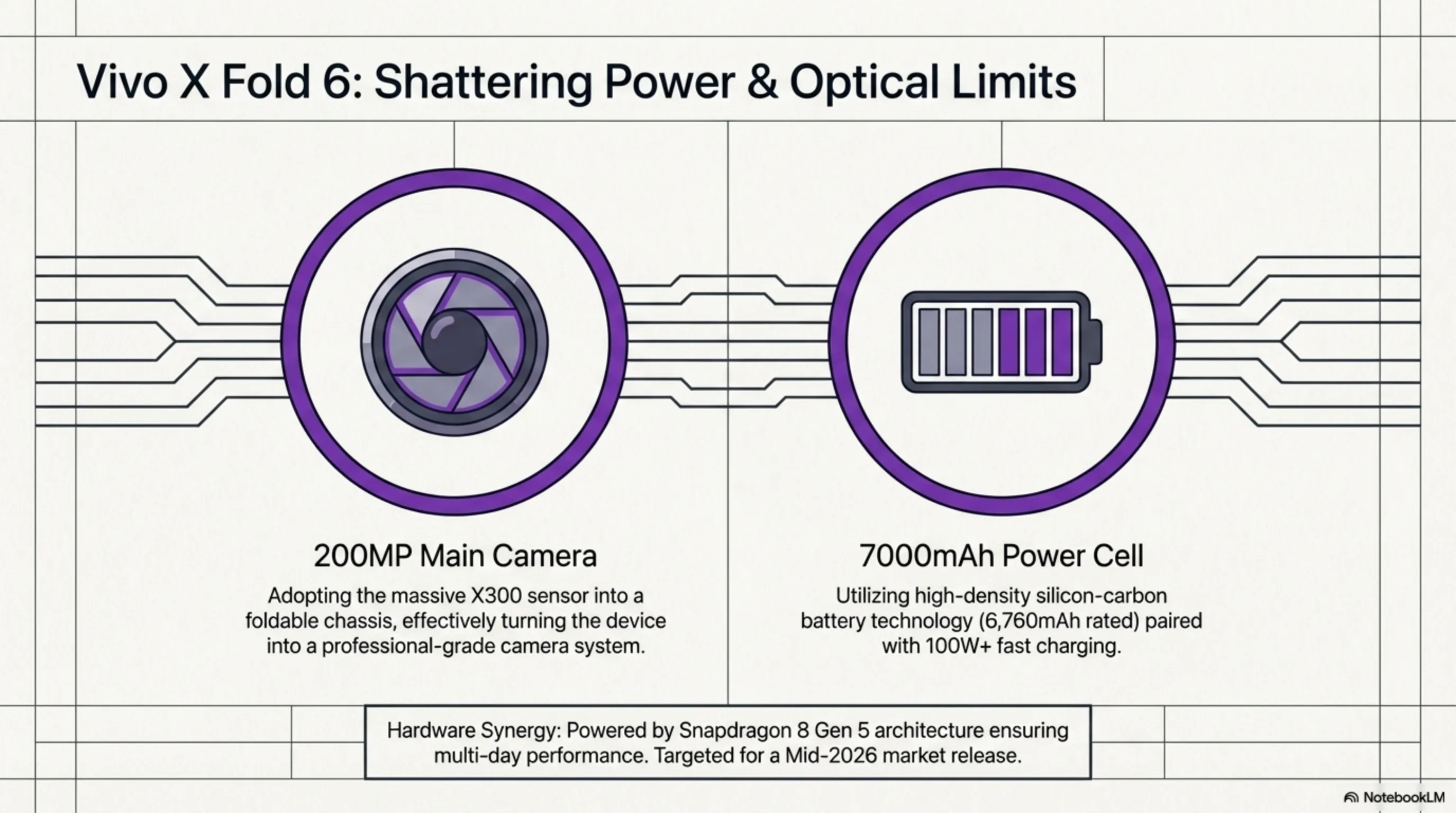
According to Digital Chat Station (one of China's most reliable leakers), the Vivo X Fold 6 will feature a 200-megapixel main camera. This is the first time we're seeing a foldable with a 200MP camera.
Vivo will likely use the same sensor used in the X300 series - a powerful sensor capable of capturing extraordinary detail. This means the Vivo X Fold 6 won't just be a foldable phone, but also a professional camera.
7,000mAh Battery: A New Record
But what's really interesting is this phone's battery. The Vivo X Fold 6 will reportedly feature a 6,760mAh (rated capacity) battery, equivalent to about 7,000mAh (typical capacity). This is the largest battery ever in a foldable phone!
For comparison, the Galaxy Z Fold 6 has a 4,400mAh battery. This means the Vivo X Fold 6 has nearly 60% more battery. With this battery, you can use the phone for a full day (or even more) without worrying about charging.
⚡ Technical Analysis
How did Vivo fit a 7,000mAh battery in a foldable? They likely used silicon-carbon battery technology with higher energy density. This technology allows you to fit a larger battery in the same space. Additionally, Vivo probably uses 100W or faster charging to quickly charge the large battery.
Other Specifications
Besides the camera and battery, the Vivo X Fold 6 will reportedly feature:
- Processor: Snapdragon 8 Gen 5 (Qualcomm's latest chipset)
- Updated Design: Design changes for better appearance
- New Accessories: Likely including an extender kit for the camera (like the X300 Ultra)
- Fast Charging: Probably 100W or higher
- Launch Date: Mid-2026 (likely June or July)
Competition with Galaxy Z Fold 8
The Vivo X Fold 6 will be a serious competitor to the Galaxy Z Fold 8. While Samsung focuses on software and ecosystem, Vivo focuses on hardware and technical specifications. The 200MP camera and 7,000mAh battery could be attractive to many users.
Of course, Vivo must also solve challenges like software optimization, global availability, and pricing. But if they can do these things right, the X Fold 6 could be one of the best foldables of 2026.
🎮 For Gamers
A 7,000mAh battery means you can game for hours without worrying about charging. The Snapdragon 8 Gen 5 is also one of the most powerful mobile chipsets for gaming. The large foldable screen also enhances the gaming experience. The Vivo X Fold 6 could be an excellent choice for mobile gamers.
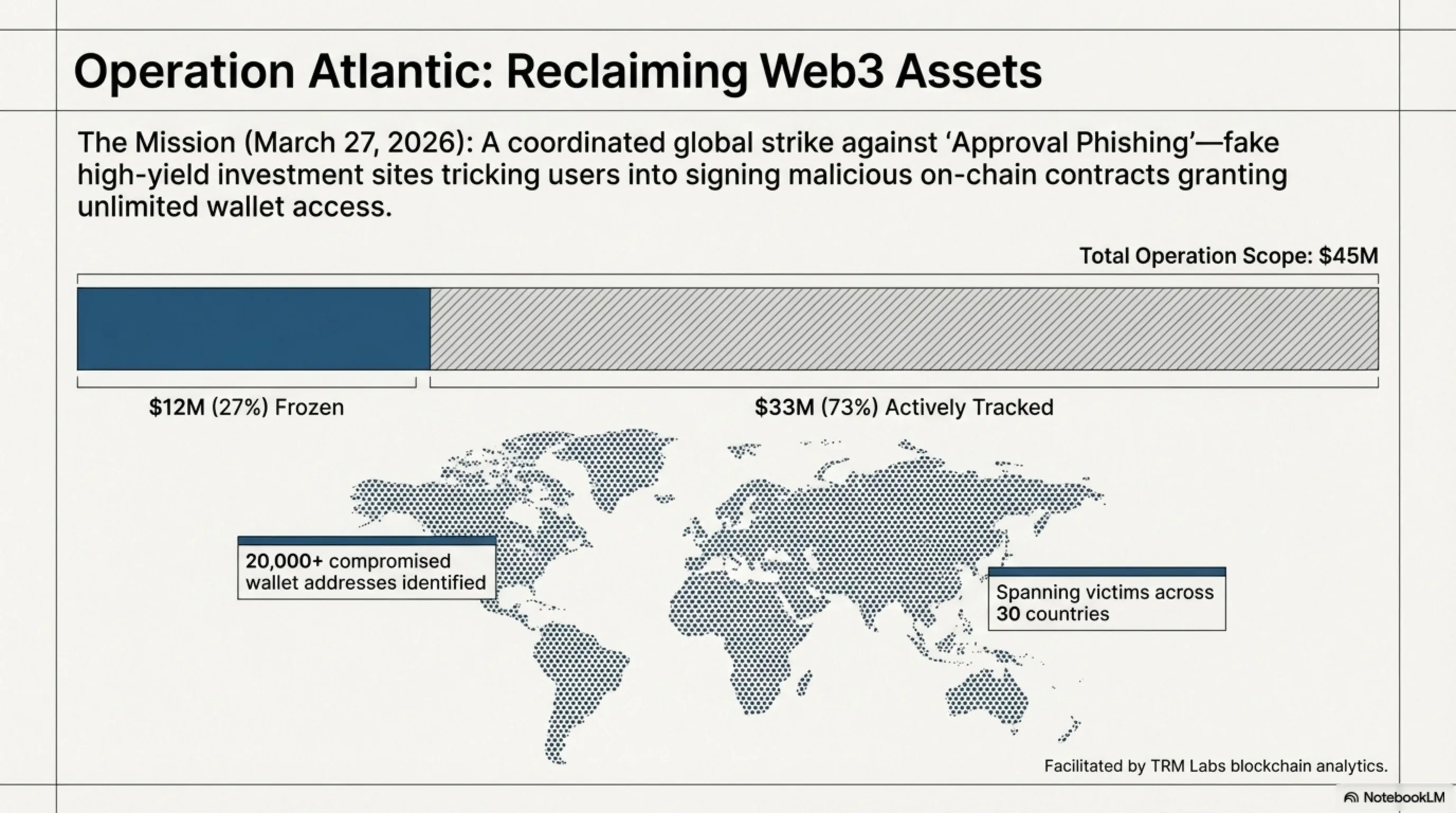
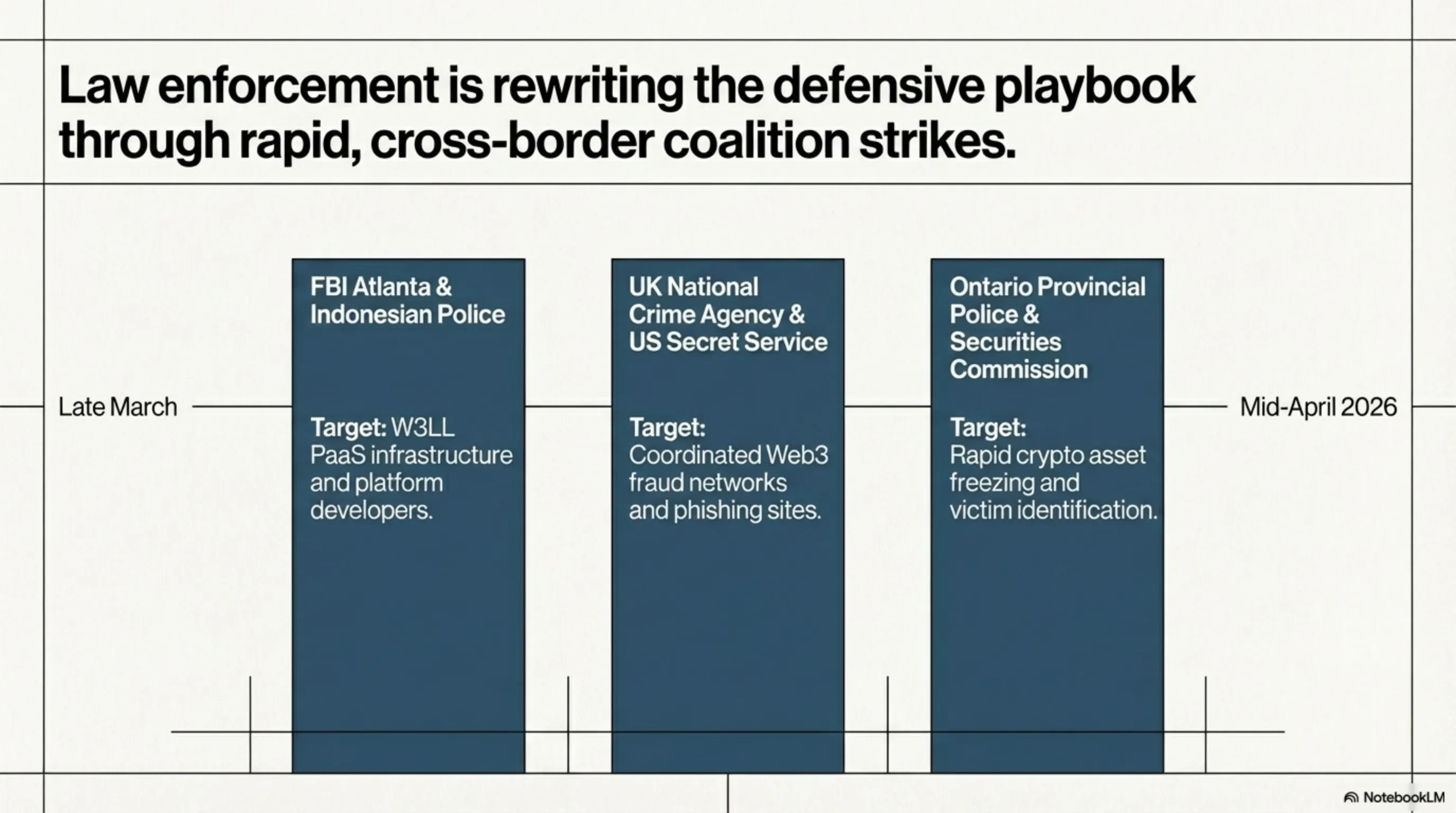
Operation Atlantic: $12 Million in Stolen Crypto Frozen
The final news of the night is another piece of good news from the cybersecurity world. An international joint operation called Operation Atlantic successfully froze $12 million in stolen cryptocurrency and identified over 20,000 approval phishing victims across 30 countries.
What Was Operation Atlantic?
This week-long operation on March 27, 2026 was conducted by three major agencies:
- National Crime Agency (NCA) UK - Operation leadership
- U.S. Secret Service - United States Secret Service
- Ontario Provincial Police and Ontario Securities Commission - Canadian police and securities commission
The main goal of this operation was to identify and assist victims of approval phishing - a type of fraud where criminals trick victims into granting full access to their crypto wallets.
What Is Approval Phishing?
Approval phishing is a sophisticated technique where criminals ask victims to sign an on-chain transaction that appears harmless, but actually allows criminals to drain the entire wallet.
This technique typically occurs through fake investment websites promising high returns. When the victim wants to invest, they're asked to sign an "approval" that actually grants criminals full access.
⚠️ Crypto Warning
Never sign transactions you don't understand. Before signing any approval, make sure you know what access you're granting. Use wallets with clear security warnings. If a site asks you to give unlimited approval, be immediately suspicious.
Operation Results
Operation Atlantic achieved impressive results:
- $12 million in stolen funds frozen
- $45 million in total crypto fraud tracked
- Over 20,000 wallet addresses linked to victims identified
- 30 countries affected by these frauds
- $33 million additional under investigation for links to investment fraud
This operation demonstrated that international cooperation can be effective in combating crypto crime. Crypto companies like TRM Labs also assisted in the operation to track stolen funds.
How to Protect Yourself
To protect your crypto from approval phishing:
- Only work with reputable and well-known sites
- Before signing any transaction, carefully check what permission you're granting
- Use wallets that show approvals in plain language
- Regularly review and revoke your active approvals
- Use tools like Revoke.cash to cancel old approvals
- Never trust sites promising unrealistic returns
🛡️ Advanced Security Tip
For extra security, use a hardware wallet and keep your main crypto there. Only keep a small amount in a hot wallet for daily transactions. Also, use multi-sig wallets that require multiple signatures for large transactions.
The Future of Fighting Crypto Crime
Operation Atlantic showed that authorities are learning and improving methods to combat crypto crime. With international cooperation and blockchain analytics tools, they can track and freeze stolen funds.
But criminals are also advancing and developing new techniques. Therefore, crypto users must always be vigilant and use the best security practices.
🌟 Night Wrap-Up
April 13th was an eventful night that showed the tech world never sleeps. From supply chain attacks to hardware innovations, everything is changing. Until tomorrow night, stay safe and stay updated! 🚀
Wrap-Up: A Night When Security and Innovation Danced Together
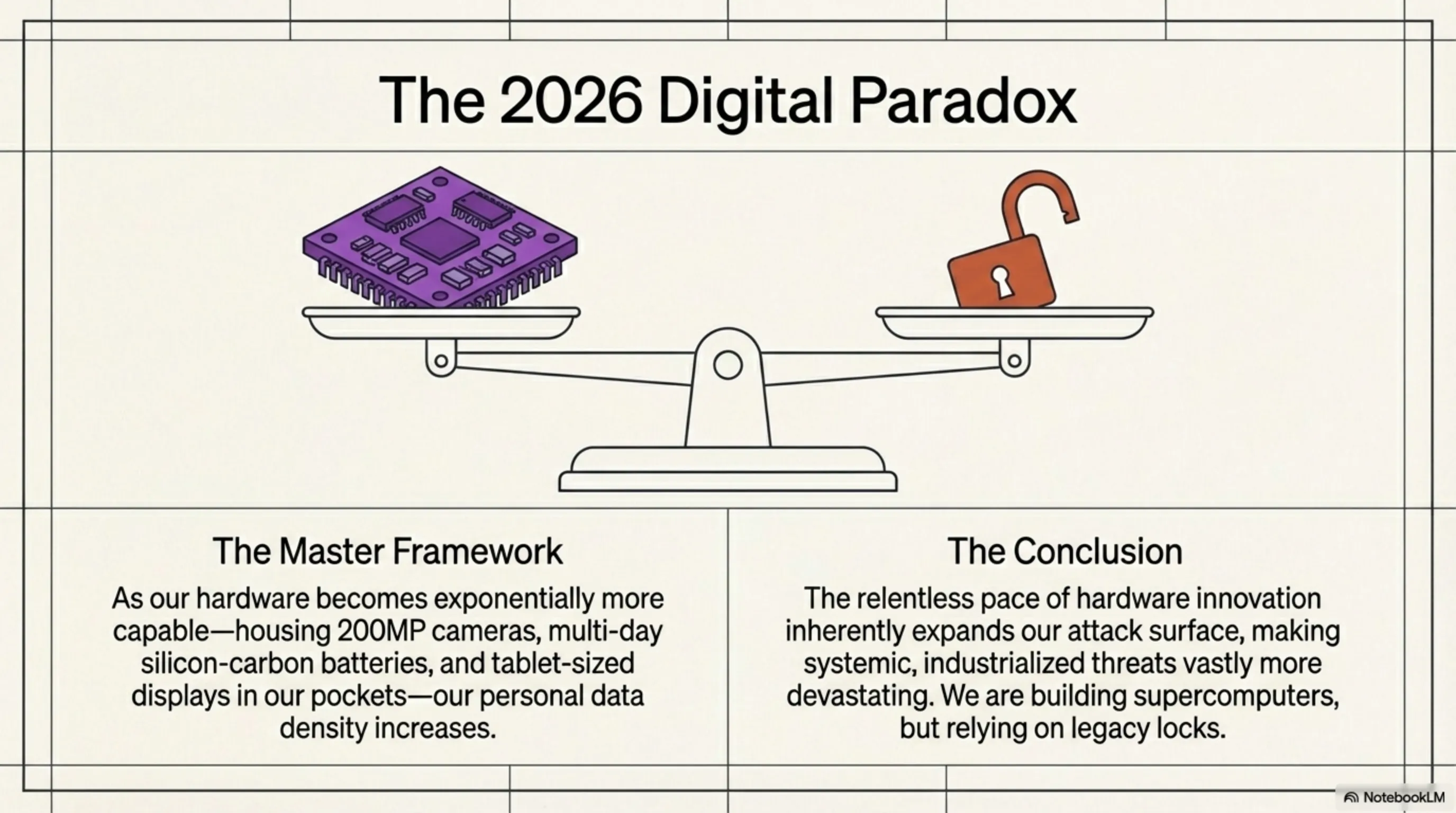
The night of April 13, 2026 was an eventful night that reminded us the tech world is always changing - both for better and worse. On one hand, we saw supply chain attacks becoming more sophisticated, with even tech giants like OpenAI at risk. The Basic-Fit data breach showed that non-tech industries must also take cybersecurity seriously.
But on the other hand, we saw authorities getting stronger too. The dismantling of the W3LL operation and the success of Operation Atlantic showed that international cooperation can be effective in fighting cybercrime.
And of course, the hardware world had exciting news too. Huawei with the Pura X Max showed it's still a powerful player in the mobile industry and can innovate before Samsung and Apple. The Vivo X Fold 6 also promised to break new records with its 200MP camera and 7,000mAh battery.
🎯 Key Takeaways
- Supply chain security is no longer optional - everyone must carefully scrutinize their dependencies
- Non-tech industries must invest seriously in cybersecurity
- International cooperation can be highly effective in fighting cybercrime
- Wide format could change the future of foldable phones
- Hardware competition drives amazing innovations
- Crypto users must be aware of approval phishing and exercise caution
This night reminded us that in the tech world, nothing is constant. Today a major company might get hacked, tomorrow an amazing innovation might be unveiled. What matters is that we as users stay vigilant, use the best security practices, and enjoy new innovations.
So until tomorrow night, stay safe, stay updated, and always stay one step ahead of threats. This was Tekin Night, and we'll be back tomorrow night with fresh news! 🌙
🌟 Final Thoughts: A Night of Contrasts
April 13th was a night of contrasts - on one hand, sophisticated cyberattacks and data breaches, on the other, amazing hardware innovations. That's what makes the tech world exciting - you never know what tomorrow will bring.
The important takeaway is that as users, we need to be aware of threats while enjoying innovations. Cybersecurity is no longer optional - everyone needs to take it more seriously. Until tomorrow night, stay safe and stay updated! 🚀
📚 Sources & References
- BleepingComputer - Cybersecurity news and supply chain attacks
- The Verge - Hardware and mobile news
- Wired - In-depth technology analysis
- ZDNet - Security news and law enforcement operations
- GSMArena - Mobile phone specifications
- Android Authority - Android news and reviews
💬 What do you think about tonight's news? Share your thoughts in the comments!
