In this deep-dive Tekin Garage cyber-analysis, we dissect one of the most critical and enduring Achilles' heels in the global telecommunications infrastructure: Signaling System No. 7 (SS7). Taking both an offensive and defensive approach, we investigate how threat actors and cyber syndicates—without deploying any malware to your device—can bypass bank Two-Factor Authentication (2FA), wiretap live cellular conversations, and extract your precise geolocation at the cellular level using nothing but your phone number. This comprehensive guide debu
🚨 Tekin Security: The Global SS7 Vulnerability Autopsy
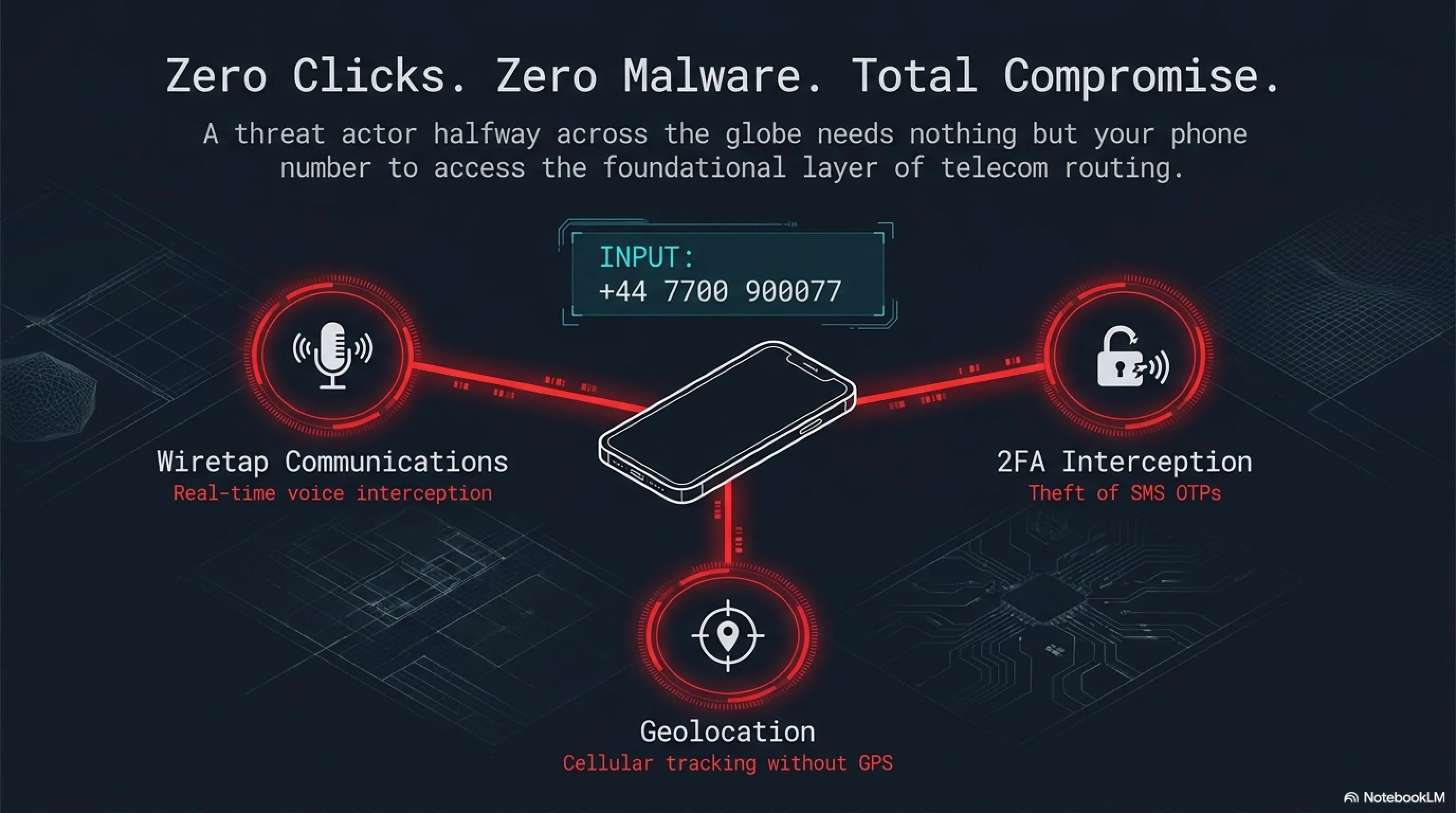
Welcome to Tekin Garage. Today, we are putting one of the telecom industry's most terrifying and heavily guarded secrets on the autopsy table. Imagine a threat actor sitting in a basement halfway across the globe. Without sending you a malicious link, without installing malware on your smartphone, and using nothing but your phone number, they can wiretap your calls, intercept your bank's 2FA SMS codes, and track your physical location on a map in real-time. This isn't a dystopian cyberpunk novel—this is the fundamental reality of the archaic SS7 signaling protocol.
⚡ What to Expect in This Strategic Analysis:
🔍 The historical roots of the trust-based SS7 protocol established in 1975.
🔓 A deep-level debug of how SMS Two-Factor Authentication (2FA) is bypassed.
📡 The mechanics behind call interception across 3G and 4G networks.
🛡️ Tekin Garage's strict digital hardening guidelines for protecting your identity.
☕ Grab a hot coffee and throw out your classic assumptions about mobile network security. We are entering the cyber red zone!
1. Into the Telecom Dark Room: What is SS7 and Why Does It Still Exist?
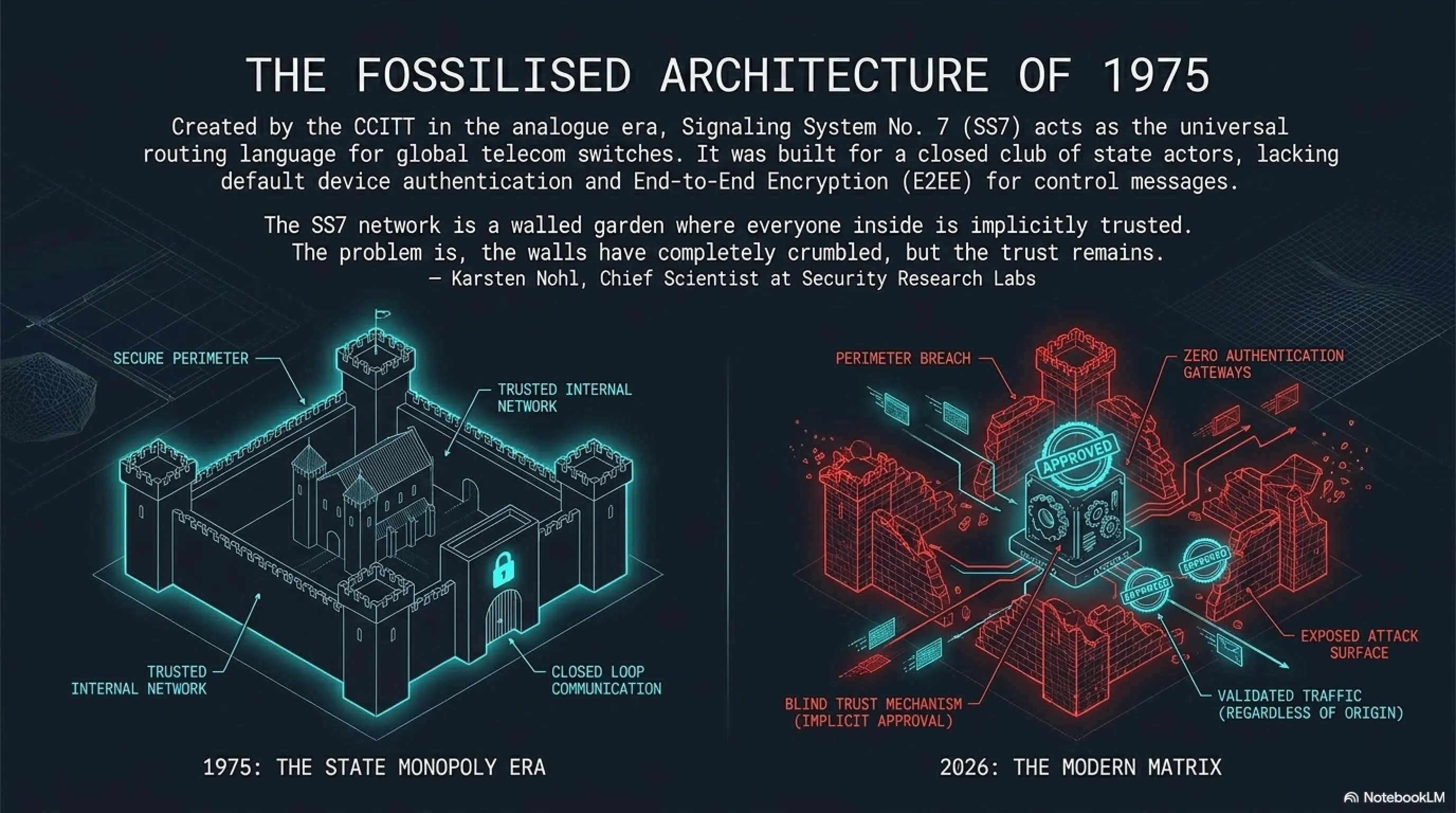
To comprehend the magnitude of the cybersecurity crisis we face today, we must power up the Garage's time machine and travel back to 1975. This was an era before the internet as we know it existed; telecommunications networks were essentially a massive web of copper wires connecting landlines. During this golden age of analogue communication, a standard called Signaling System No. 7 (SS7) was birthed by the CCITT (now ITU-T) to serve as the universal language for telecom switches globally. The core duty of SS7 was—and astonishingly, still is—to instruct disparate networks on how to route phone calls, deliver SMS messages, and manage cross-border billing systems seamlessly.
"The SS7 network is a walled garden where everyone inside is implicitly trusted. The problem is, the walls have completely crumbled, but the trust remains."
— Karsten Nohl, Chief Scientist at Security Research Labs (SRLabs)
But where lies the fundamental, architectural flaw? In the 1970s and 80s, telecom networks were an exclusive, closed club. Only a handful of massive, state-owned telecom monopolies had physical access to the infrastructure. Consequently, the original architects built SS7 on a foundation of "Absolute Trust." The protocol features zero default mechanisms for authenticating connecting devices and completely lacks End-to-End Encryption (E2EE) for its control messages. The system operates on the naive assumption that anyone sending a signaling command is inherently a legitimate operator. If a switch in Eastern Europe or Africa tells your local carrier in New York: "Subscriber 555-0199 is currently roaming on my network, please forward all their calls and texts to me," the home network complies without challenging the request or asking for cryptographic verification!
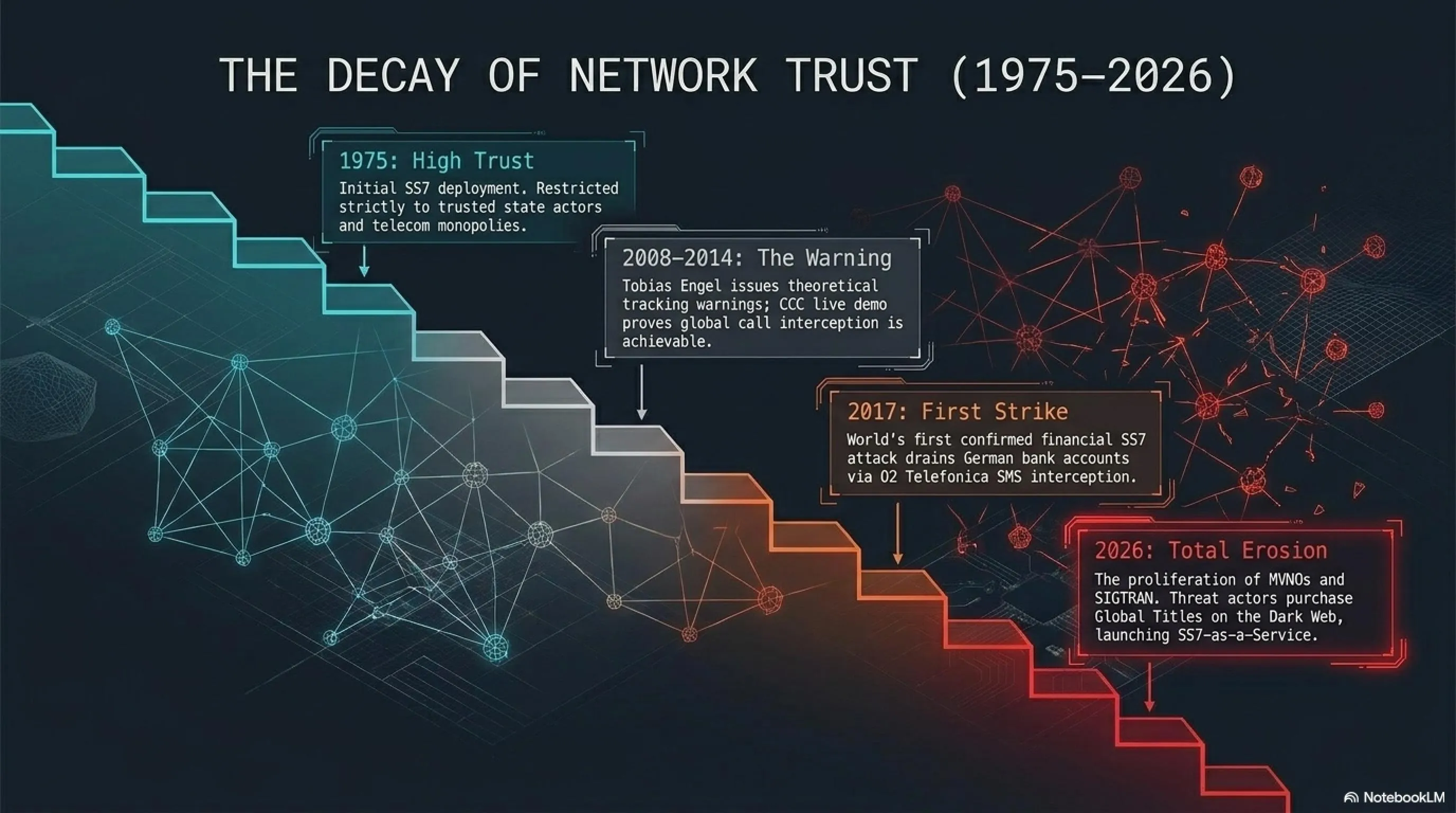
⏱️ Historical Dossier: The Evolution of SS7 Vulnerabilities
| Year | Cybernetic Milestone in Signaling Networks |
|---|---|
| 1975 | Initial development of SS7, heavily reliant on mutual trust between state actors and telecom monopolies. |
| 2008 | Security researcher Tobias Engel issues the first theoretical warnings at the CCC in Germany regarding location tracking via signaling protocols. |
| 2014 | A terrifying live demonstration at the Chaos Communication Congress (CCC) proves that global call interception is practically achievable. |
| 2017 | The world's first confirmed financial SS7 attack. Hackers drain German bank accounts by intercepting SMS 2FA codes sent via O2 Telefonica. |
| 2026 | The rise of "SS7-as-a-Service" on the Dark Web, granting amateur threat actors state-level access to the global telecom matrix for a monthly fee. |
Today, with the explosive proliferation of Mobile Virtual Network Operators (MVNOs) and third-party bulk SMS gateways, the walls of this closed club have been obliterated. The network is now accessible to thousands of big and small entities globally. Threat actors can easily purchase, rent, or hack into an SS7 node on the Dark Web, acquiring a "Global Title"—the master key to the global telecom grid. Utilizing modern adaptation protocols like SIGTRAN (which packages legacy SS7 commands over IP networks), they masquerade as legitimate operators, initiating a cascade of cyber devastation.
2. Autopsy of an Exploit: How Hackers Manipulate the Network Matrix
Let's debug this vulnerability on the Tekin Garage workbench in an isolated environment. Exploiting the SS7 infrastructure isn't black magic; it is simply the clever manipulation of the network's own standardized commands. These attacks rely on a subset of messages called the Mobile Application Part (MAP). Under normal circumstances, MAP protocols are responsible for updating user status, locating devices for incoming calls, and managing roaming handoffs.
🔧 Tekin Analysis: Executing the Routing Exploit
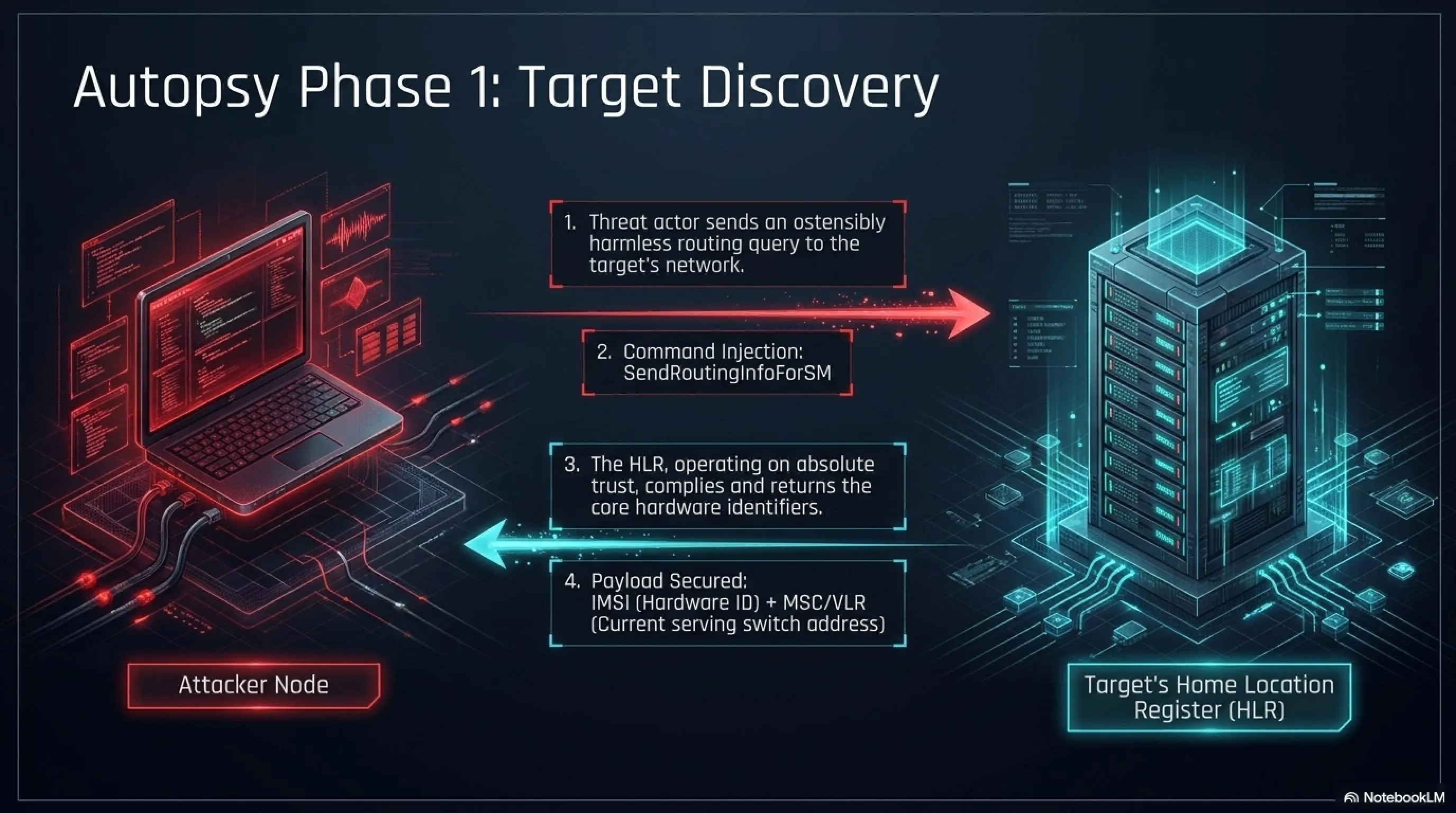
Phase 1 (Target Discovery): The hacker must first identify which telecom switch the target is currently connected to. They send an ostensibly harmless query called SendRoutingInfoForSM to the target's Home Location Register (HLR). The network obliges, handing over the SIM card's unique hardware identifier (IMSI) and the address of the current serving switch (MSC/VLR).
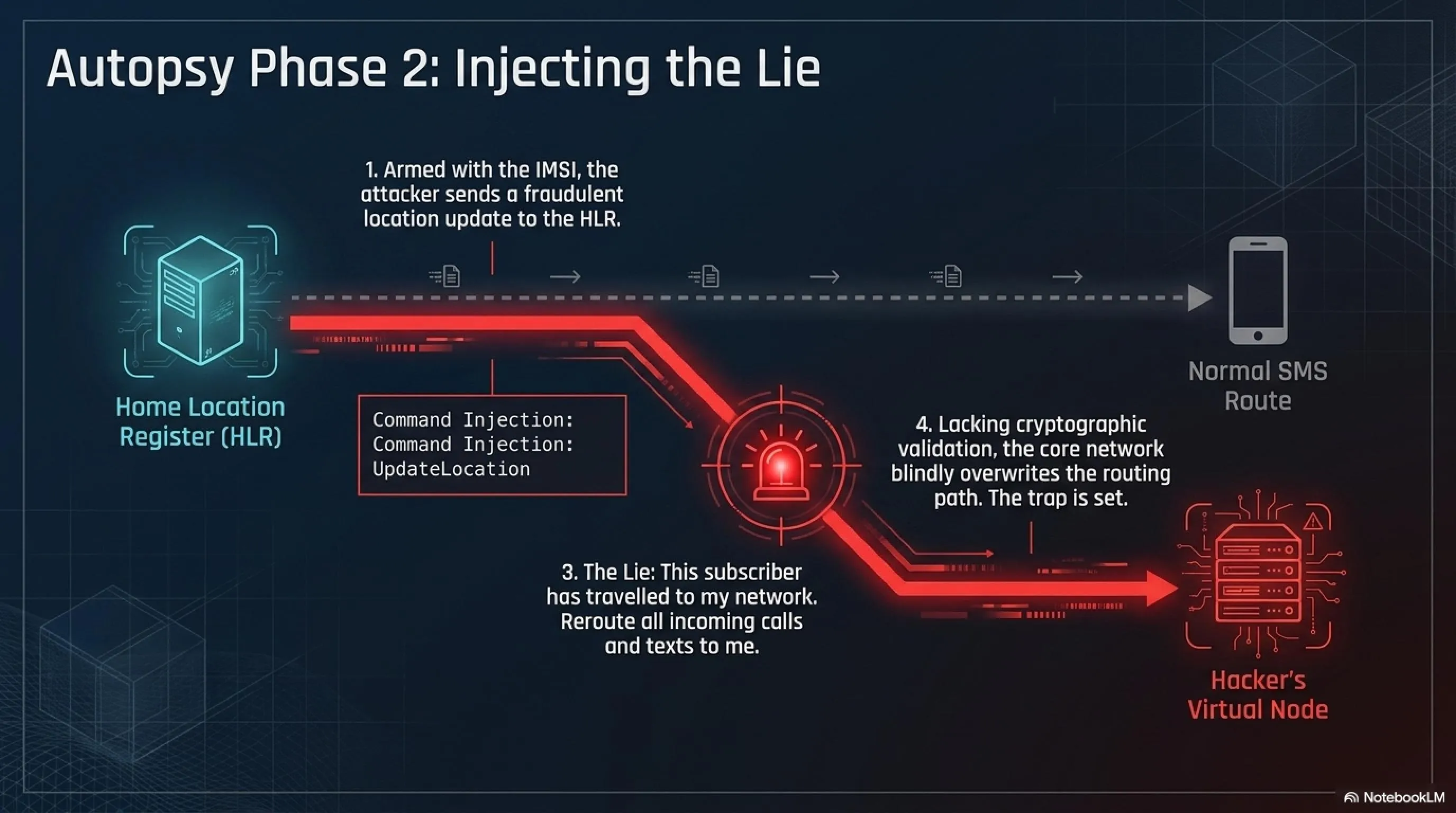
Phase 2 (Injecting the Lie): Armed with this golden data, the hacker launches the lethal blow: sending an UpdateLocation message to the target's HLR. This message falsely declares: "Your subscriber with this IMSI has just traveled to my network. Please update their routing path for all incoming calls and texts!" Lacking cryptographic validation, the core network blindly accepts the update.
3. The 2FA SMS Interception: When Your Airwaves Are Hijacked
One of the most devastating and highly weaponized applications of the SS7 exploit in today's digital economy is the outright theft of digital identities via SMS Two-Factor Authentication (2FA) interception. Banks, cryptocurrency exchanges, and secure messengers like Telegram and WhatsApp all heavily rely on a simple text message to verify your identity. However, as we observed in the previous phase on the debugging workbench, the threat actor has already successfully instructed the network matrix (HLR) that you are supposedly roaming on their rogue network.
When you (or the hacker) trigger a login request to a crypto exchange, the platform's server dispatches an SMS containing the One-Time Password (OTP) to your phone number. This message enters the originating telecom network. The telecom switch checks the HLR database and discovers that the routing path for your SMS has been updated to the hacker's virtual network node. Consequently, the text message—referred to in network architecture as an SMS-MT (Mobile Terminated)—never lights up your smartphone screen. Instead, it is routed directly into the hacker's Dark Web dashboard. They input the code and, in a fraction of a second, seize total control of your assets or accounts.
⚔️ Security Battlefield: SMS 2FA vs. Authenticator Apps
❌ Legacy SMS System (SMS 2FA)
- Absolutely vulnerable to SS7 routing exploits and network-level interception.
- Extremely high risk of SIM Swapping via social engineering attacks.
- Dependent on cellular coverage and telecom uptime.
- Data is transmitted as unencrypted plaintext between cell towers.
✅ Authenticator Apps (TOTP)
- Operates completely offline, functionally isolated from the SS7 network.
- Generates Time-based One-Time Passwords (TOTP) that expire every 30 seconds.
- Protected locally by the device's biometric sensors (FaceID/Fingerprint).
- Uninterceptable at the network layer because algorithms process locally on the device.
The most terrifying aspect noted during Tekin Garage's case studies is that in advanced financial fraud, hackers employ hybrid attacks. They initially harvest your online banking username and password via sophisticated Phishing campaigns or mobile malware. Then, to bypass the dynamic OTP, they leverage the SS7 infrastructure. You remain completely oblivious to the intrusion until you receive a withdrawal notification—assuming the hacker hasn't already routed that notification to their own server as well.
4. Cellular Geolocation Tracking: The Shadow That Follows You
Do you believe that disabling your smartphone's GPS (Location Services) makes you untrackable? In the dark realm of SS7, your GPS toggle is utterly irrelevant. As long as your device is powered on and communicating with a Cell Tower, the network matrix knows exactly which geographical radius you occupy. And if the network knows, a hacker connected to an SS7 node knows.
The technique of Geolocation Tracking within this protocol is executed by dispatching an inquiry named ProvideSubscriberInfo (PSI) or AnyTimeInterrogation (ATI). The threat actor sends this query to your home network's HLR, essentially asking: "Where is the subscriber with this number right now?" The network, maintaining its blind trust, responds with the Cell Global Identity (CGI). This identifier is the precise, unique code of the cellular tower your phone is currently pinging.
📊 Tekin Analysis: Cell ID Triangulation Accuracy
Major Urban Centers
Under 50 - 200mExtremely high precision due to dense tower infrastructure.
Suburbs & Residential Areas
500m to 1.5kmModerate accuracy, sufficient for pinpointing specific neighborhoods.
Rural Highways & Countryside
3km to 10kmLow accuracy due to massive distances between macro-cells.
Once the hacker secures the Cell ID code, they seamlessly cross-reference it against open-source databases (such as OpenCelliD) or commercial geolocation APIs to extract the exact longitude and latitude coordinates of the tower on a map. Because this operation occurs entirely at the infrastructure level (Layer 3 of the OSI model), no warning icons or notifications will ever appear on your smartphone screen. You are being monitored in absolute silence.
Intelligence agencies, state-sponsored APT groups, and organized criminal syndicates globally utilize this methodology for real-time target tracking. This technique does not require the deployment of complex, multi-million-dollar spyware like NSO Group's Pegasus; SS7 natively offers this capability to anyone holding the keys to the signaling network.
5. Tekin Garage Defensive Protocol: Hardening Your Communications
Now that we have exposed the gaping wounds within the SS7 infrastructure and witnessed how a seemingly simple routing exploit can shatter our identity matrix, the ultimate question arises: Should we throw our smartphones into the ocean? At Tekin Garage, we advocate for cyber hardening (Armor Plating) rather than surrender. Because you, as an end-user, have zero administrative control over telecom core servers (Layer 3 signaling), your only viable survival strategy is to migrate your security to the application layer via End-to-End Encryption (E2EE).
🛡️ Cyber Hardening Guidelines Against SS7 Exploits
- Eradicate SMS 2FA Completely: Access the security settings of your banking apps, crypto exchanges, Telegram, Twitter, and Gmail immediately. Disable SMS-based Two-Factor Authentication and bind your accounts to TOTP Authenticator apps (like Google Authenticator, Authy) or physical hardware keys (like YubiKey).
- Migrate from Cellular Calls to VoIP: For sensitive, confidential, and corporate communications, absolutely refuse to use standard cellular voice routing (GSM/VoLTE). Exclusively utilize messengers that enforce strict End-to-End Encryption (like Signal or WhatsApp). In this scenario, even if a threat actor intercepts your traffic, they capture nothing but unreadable, encrypted data packets.
- Audit and Disable Call Forwarding: Dial the MMI codes
*#21#or*#62#on your device to verify if your calls are being stealthily diverted to an unknown number. To neutralize and erase all active diversions, execute the command##002#. - Compartmentalize with Burner SIMs: If forced to use SMS for legacy banking systems, acquire a dedicated, highly compartmentalized SIM card. This number must remain a strict secret between you and your bank. Never link this Burner SIM to public social media profiles or online directories.
The global telecommunications industry is actively transitioning towards 5G Standalone (SA) architectures, which aim to entirely replace SS7 with more secure, IP-based protocols like HTTP/2 with TLS encryption and Diameter. However, as long as legacy 2G and 3G networks remain operational for backward compatibility, and telecom operators continue to rely on interconnected SS7 bridges, this ominous shadow will persist over global communications grids.
🏷️ The Full Dossier: Telecom Vulnerabilities & Cyber Forgery
To fully map the modern threat matrix, review our previous Tekin Garage deep-dives:

❓ User Debug: Frequently Asked Questions (FAQ)
1. Will using a VPN prevent me from being tracked via SS7?
No. A VPN only encrypts your internet traffic (the data layer). SS7 attacks occur at the telecom infrastructure level (the signaling layer between cell towers). Therefore, a VPN provides zero protection against Cell ID tracking or SMS interception.
2. Can mobile operators completely block these routing attacks?
Operators can significantly mitigate the risk by deploying advanced SS7 Firewalls to filter out suspicious control messages (such as an 'UpdateLocation' originating from an illogical foreign network). However, due to the open, interoperable nature of the global protocol, achieving 100% security at the network layer remains practically impossible.
3. What should I do if my Telegram is hacked via SMS interception?
If you notice unauthorized access, immediately navigate to Settings > Devices and 'Terminate' all unrecognized active sessions. Immediately afterward, enable Two-Step Verification (Cloud Password). This ensures that even if a hacker intercepts your SMS code again, they cannot bypass the dedicated cloud password.
2. Academic vulnerability research on MAP and SIGTRAN protocols
3. Official ITU-T documentation on Signaling System No. 7 architecture
4. NCSC (National Cyber Security Centre) advisories regarding SMS 2FA risks
5. Recent Citizen Lab reports detailing signaling protocol abuse by state actors
6. Tekin Garage Cyber Research & Analysis Team (2026)
