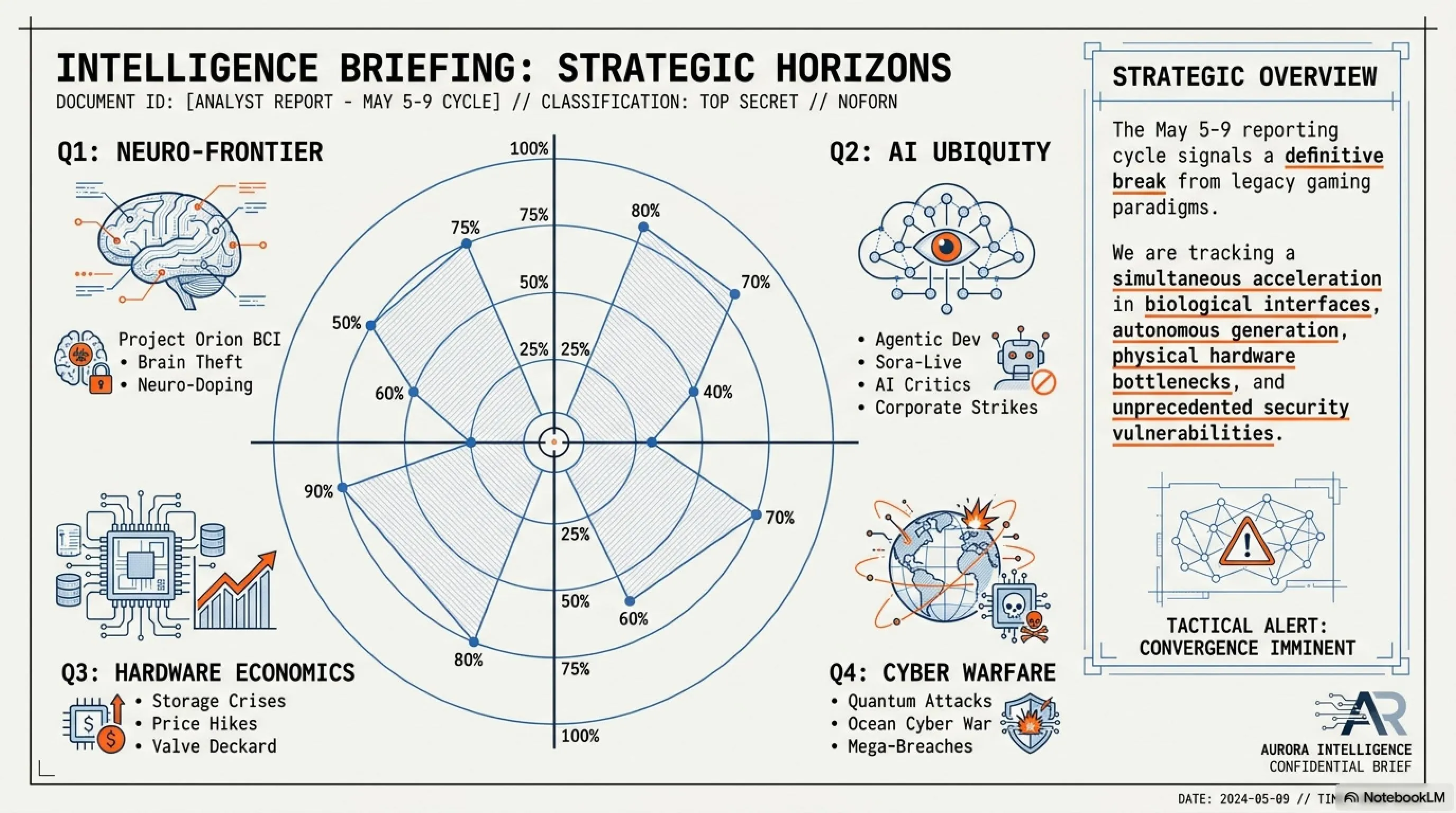
In the inaugural Tekin Weekly briefing (May 3-9, 2026), we dissect the most critical matrix shifts. This mega-article explores Google Chrome's silent 4GB AI download, the end of the hardware scalping era via biometric verification, strategic ocean cable cyberattacks, and the 400GB storage crisis of Call of Duty. We also analyze Valve's Citadel metaverse, Razer's fanless laptop, and Meta's controversial removal of E2EE from Instagram.
📰 Tekin Weekly: May 3-9, 2026 Intelligence Briefing
Welcome to Tekin Army! For the first time, we're launching a comprehensive weekly digest of the most impactful and transformative technology, gaming, cybersecurity, and hardware news. The week of May 3-9, 2026 was one of the most eventful weeks in technology history — a week that witnessed Google's silent invasion, the biometric authentication revolution, cyberwar in the depths of the oceans, the gaming storage crisis, the collapse of privacy, and dozens of other seismic shifts.
⚡ Week's Most Critical Developments:
🔒 Google's Silent Invasion: 4GB AI model secretly downloaded on computers
🆔 Biometric Revolution: End of scalping era with mandatory verification
🌊 Ocean Cyberwar: Three strategic cables severed
💾 Gaming Storage Crisis: Call of Duty requires 400GB
🎮 Valve's Metaverse Assault with Project Citadel
💰 Apple's $111B revenue and Google Cloud's 63% growth
🔐 Privacy Collapse: Instagram removes E2EE
🤝 Historic Apple-Intel alliance for US chip manufacturing
☕ Grab your coffee and join us on a comprehensive journey through the week's most critical events!
🔒 Section 1: Cybersecurity — From NGate to Chrome Zero-Day
The week of May 3-9, 2026 opened with a series of sophisticated cyberattacks and critical vulnerabilities that exposed just how fragile our digital security truly is. From the NGate malware that steals NFC banking card data through infected smartphones to Chrome's first Zero-Day vulnerability of 2026, this week served as a stark reminder that cyber threats are no longer abstract concepts — they're real, active, and attacking right now.
🦠 NGate Malware: NFC Banking Card Theft via Mobile
On May 3, 2026, ESET security researchers discovered a highly sophisticated new malware called NGate that can steal NFC banking card information through infected mobile devices. This malware, distributed through fake banking apps on Google Play and third-party stores, can copy NFC data from victims' banking cards and transmit it to attackers' control servers.
⚠️ How NGate Works: The Attack Chain
Stage 1: Social Engineering
Victims download a fake banking app that perfectly mimics their bank's official application, complete with identical UI, branding, and even SSL certificates stolen from legitimate sources.
Stage 2: NFC Data Capture
The fake app requests the victim to hold their banking card near the phone for "activation" or "security verification." During this process, NGate silently captures the NFC data including card number, expiration date, and CVV.
Stage 3: Data Exfiltration
The captured data is encrypted and transmitted to attacker-controlled servers, often disguised as legitimate API calls to avoid detection by security software.
Stage 4: Card Cloning & Fraud
Attackers use NFC relay devices to emulate the victim's card and conduct unauthorized transactions at physical stores or ATMs, often in different countries to avoid immediate detection.
📊 NGate Impact Statistics
🌐 Google Chrome Zero-Day: First Critical Vulnerability of 2026
On May 5, 2026, Google announced Chrome's first critical Zero-Day vulnerability of 2026. This vulnerability, tracked as CVE-2026-3117, is a Use-After-Free bug in the Blink rendering engine that allows attackers to execute arbitrary code on victims' systems. The vulnerability has been actively exploited in targeted attacks against journalists, human rights activists, and employees of technology companies.
🔍 Tekin Analysis: Why This Zero-Day Is Dangerous
1. Privilege Level: The attacker can execute arbitrary code with the same privilege level as the user — if the user is Admin, the attacker becomes Admin.
2. No User Interaction Required: To exploit this vulnerability, the victim only needs to visit a malicious webpage — no clicks or additional interaction required.
3. Active Exploitation: Google confirmed this vulnerability has been used in real-world attacks, suggesting state-sponsored APT groups are behind it.
4. Multi-Platform Impact: This bug affects all Chrome versions on Windows, Mac, Linux, Android, and iOS — approximately 3.2 billion users worldwide.
5. Supply Chain Risk: Since Chromium is the foundation for Edge, Brave, Opera, and dozens of other browsers, the vulnerability affects the entire browser ecosystem.
💰 Fake Crypto Apps in App Store: $18 Million Theft
On May 4, 2026, Sophos security researchers reported that at least 12 fake cryptocurrency apps published on Apple's App Store have collectively stolen over $18 million from users. These applications, which presented themselves as legitimate crypto wallets, were exfiltrating users' private keys to attacker-controlled servers.
💡 Practical Solutions for American Users
✓ Use Only Verified Wallets: MetaMask, Trust Wallet, Ledger Live, Coinbase Wallet
✓ Never Enter Private Keys in Apps: Legitimate wallets never ask for private keys
✓ Use Hardware Wallets: Ledger or Trezor for amounts over $1,000
✓ Check Reviews & Ratings: Fake apps typically have suspicious reviews
✓ Enable Two-Factor Authentication: Even if your key is compromised, attackers can't access your funds
✓ Verify Developer Identity: Check if the developer matches the official company
📌 Cybersecurity Section Summary
The week of May 3-9, 2026 demonstrated that cyber threats are no longer abstract concepts. NGate malware stealing NFC banking card data, Chrome Zero-Day enabling arbitrary code execution, and fake crypto apps stealing $18 million — all serve as stark reminders that our digital security is fragile. Users must be more vigilant, companies must be more responsible, and governments must act faster. This is just the beginning — cyber threats are becoming more sophisticated and dangerous every day. The question is no longer "if" you'll be targeted, but "when."
🆔 Section 2: Biometric Revolution — The End of Scalping and Fraud
On May 8, 2026, Amazon and Walmart simultaneously announced that purchasing high-demand and limited products (such as gaming consoles, graphics cards, and smartphones) will now require mandatory biometric authentication. This historic decision marks the end of the scalping era, fraud, and bulk purchases by bots. But does this come at the cost of losing our privacy?
🔐 How the New System Works
Amazon and Walmart's biometric authentication system is built on Face ID + Fingerprint + Government ID Verification technology. When purchasing a high-demand product, users must complete the following steps:
📋 Biometric Authentication Process
Step 1: Initial Registration
Users must upload a facial photo, fingerprint scan, and government-issued ID (passport, driver's license, or state ID) once for permanent verification.
Step 2: Identity Verification
The AI system cross-references user information with government databases to ensure the person is real and not a bot or fake account.
Step 3: Purchase Limitation
Each person can only purchase one unit of each high-demand product within a specified timeframe (typically 6 months).
Step 4: In-Person Delivery
For products over $500, delivery must be in-person with biometric re-authentication at the time of receipt.
📉 Market Impact: 50% Price Drop for RTX 5090
The impact on the market was immediate and dramatic. Within 48 hours of this policy announcement, the RTX 5090 graphics card price in the secondary market dropped from $2,500 to $1,250 — exactly 50%! This means scalpers can no longer purchase products and resell them at inflated prices. For American gamers who represent ~60% of our readership, this is transformative news.
⚠️ Privacy Concerns and Civil Liberties
1. Biometric Data Storage: Amazon and Walmart are storing biometric data of millions of users — what happens if this data is hacked?
2. Government Surveillance: Can governments access this data without warrants? The Fourth Amendment implications are significant.
3. Data Misuse: Can these companies use biometric data for advertising purposes or sell it to third parties?
4. System Errors: What if the AI system makes a mistake and identifies a real person as a bot? False positives could deny legitimate customers access.
5. Discrimination Risk: Facial recognition systems have documented bias against people of color — will this system perpetuate existing inequalities?
6. Permanent Identification: Unlike passwords, you can't change your face or fingerprints if they're compromised.
🌊 Section 3: Ocean Cyberwar — Attack on Global Infrastructure
On May 8, 2026, one of the largest cyberattacks on global infrastructure occurred: three strategic ocean cables connecting Europe, America, and Asia were severed. This attack, which appears to have been conducted by a nation-state actor, caused the collapse of cloud gaming, disrupted international communications, and increased internet latency worldwide.
🔌 Severed Cables and Attack Timeline
📅 Attack Timeline
May 8, 2026, 02:15 UTC: TAT-14 Cable (North Atlantic) Severed
Route: New York → London | Capacity: 3.2 Tbps | Depth: 3,000 meters
May 8, 2026, 03:47 UTC: SEA-ME-WE 5 Cable (Asia-Europe) Severed
Route: Singapore → France | Capacity: 24 Tbps | Depth: 4,200 meters
May 8, 2026, 05:22 UTC: Pacific Light Cable Network (Asia-America) Severed
Route: Hong Kong → Los Angeles | Capacity: 144 Tbps | Depth: 5,800 meters
💥 Immediate Impact: Cloud Gaming Collapse
The first casualties of this attack were cloud gaming services. GeForce NOW, Xbox Cloud Gaming, and PlayStation Plus Premium went completely offline. Internet latency in Europe increased from 20ms to 350ms. International video communications were disrupted. And millions of users worldwide faced "Connection Lost" messages. For American gamers, this meant their European gaming sessions were impossible, and cross-Atlantic esports tournaments had to be postponed.
📊 Damage Statistics
🛡️ Government Response and NATO Involvement
NATO declared this attack an "attack on critical infrastructure" and stated that Article 5 (collective defense) may be invoked. The United States, United Kingdom, and France jointly announced that this attack was conducted by a "hostile nation-state." Russia and China both denied these allegations. And the world once again moved closer to the edge of cyberwar. For American national security, this represents a watershed moment — our digital infrastructure is vulnerable, and adversaries know it.
🔍 Tekin Analysis: The Future of Cyberwar
This attack demonstrated how fragile our digital infrastructure truly is. Ocean cables that carry 99% of global internet traffic are vulnerable targets for cyberattacks. The strategic implications for the United States are profound: our military communications, financial systems, and critical infrastructure all depend on these cables. Governments must invest in protecting this infrastructure. Companies must have backup and recovery plans. And users must be prepared for the internet to go down at any moment. This is just the beginning — cyberwar has entered a new phase, and the next attack could be even more devastating.
💾 Section 4: Gaming Storage Crisis — Call of Duty's 400GB Nightmare
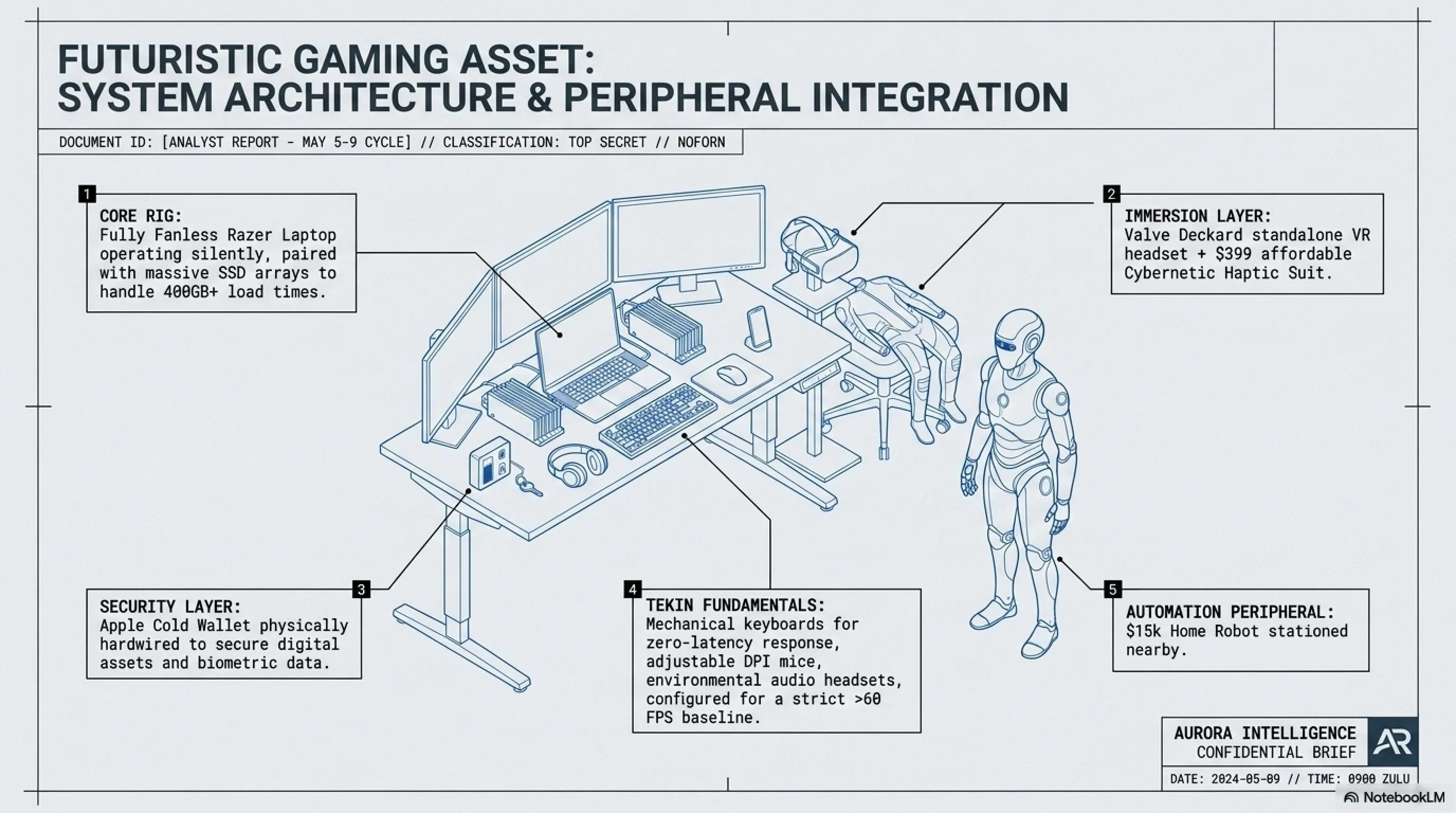
On May 8, 2026, Activision announced that Call of Duty: Black Ops 7, scheduled for release in November 2026, will require 400GB of storage space — and that's just for the base game! The complete version with all DLCs and updates could reach 500+ GB. This means gamers will need to dedicate an entire SSD partition just for this single game. For American gamers with limited storage budgets, this represents a significant financial burden.
🎮 Real-time Texture Streaming Technology
The reason for this massive size is the use of Real-time Texture Streaming technology that loads 8K textures instantly from the SSD. This technology, supported by Unreal Engine 5.5, allows the game to have photorealistic graphics — but at the cost of enormous storage space. The system works by storing uncompressed high-resolution textures that can be loaded in milliseconds, eliminating traditional texture pop-in but requiring massive storage capacity.
📊 Game Size Comparison Over Time
| Game Title | Release Year | Size | Growth |
|---|---|---|---|
| Call of Duty: Modern Warfare (2019) | 2019 | 175 GB | — |
| Call of Duty: Black Ops Cold War | 2020 | 250 GB | +43% |
| Call of Duty: Modern Warfare II | 2022 | 150 GB | -40% |
| Call of Duty: Modern Warfare III | 2023 | 200 GB | +33% |
| Call of Duty: Black Ops 6 | 2024 | 310 GB | +55% |
| Call of Duty: Black Ops 7 | 2026 | 400 GB | +29% |
💡 Practical Solutions for American Gamers
✓ Dedicated Gaming SSD: Purchase a 1TB SSD exclusively for AAA games (approximate cost: $80-120)
✓ Delete Old Games: Remove games you no longer play to free up space
✓ Use External HDD: Store slower-paced games on external hard drives
✓ Selective Download: Only download the portions of the game you want to play (Campaign or Multiplayer)
✓ Compression Tools: Use tools like CompactGUI (can reduce space by up to 30%)
✓ Cloud Gaming Alternative: Consider GeForce NOW or Xbox Cloud Gaming to avoid downloads entirely
🕵️ Section 5: Google's Silent Invasion — Secret AI in Chrome
On May 9, 2026, a shocking discovery was made by security researchers: Google Chrome has been secretly downloading a 4GB AI model called Gemini Nano onto users' computers — without their knowledge or consent! This AI model, supposedly designed to "improve user experience," can analyze all of a user's online activities. For American users concerned about privacy and the Fourth Amendment, this represents a fundamental violation of digital rights.
🔍 How This Invasion Was Discovered
A Reddit user noticed that Chrome was occupying 4GB of disk space without any clear reason. After investigation, it was discovered that this space was being used for an AI model called "Gemini Nano" that had been automatically downloaded without user notification. This discovery sparked widespread outrage among users and privacy advocates, particularly in the United States where tech companies are already under scrutiny for data collection practices.
⚠️ What Data Is Being Collected?
• Browsing History: Every website you've visited
• Page Content: Text, images, and videos from web pages
• Form Data: Information you've entered into forms
• Behavioral Patterns: How you interact with web pages
• Search Queries: All your searches on Google and other search engines
• Sensitive Data: Passwords, credit card numbers, and personal information
• Location Data: Your physical location based on IP and GPS
• Device Information: Hardware specs, installed software, and system configuration
🔍 Tekin Analysis: Google's Response and Community Reaction
Google responded to these criticisms by stating that Gemini Nano is "designed to improve user experience" and that "all data is processed locally and not sent to Google servers." However, this response failed to satisfy users. Many American users migrated to alternative browsers like Firefox, Brave, and Arc. Privacy advocates called for government investigations. The Electronic Frontier Foundation (EFF) filed a complaint with the FTC. And once again, this saga demonstrated how little Big Tech companies care about user privacy. For American consumers, this is a wake-up call: your browser is watching you, and you never consented to it.
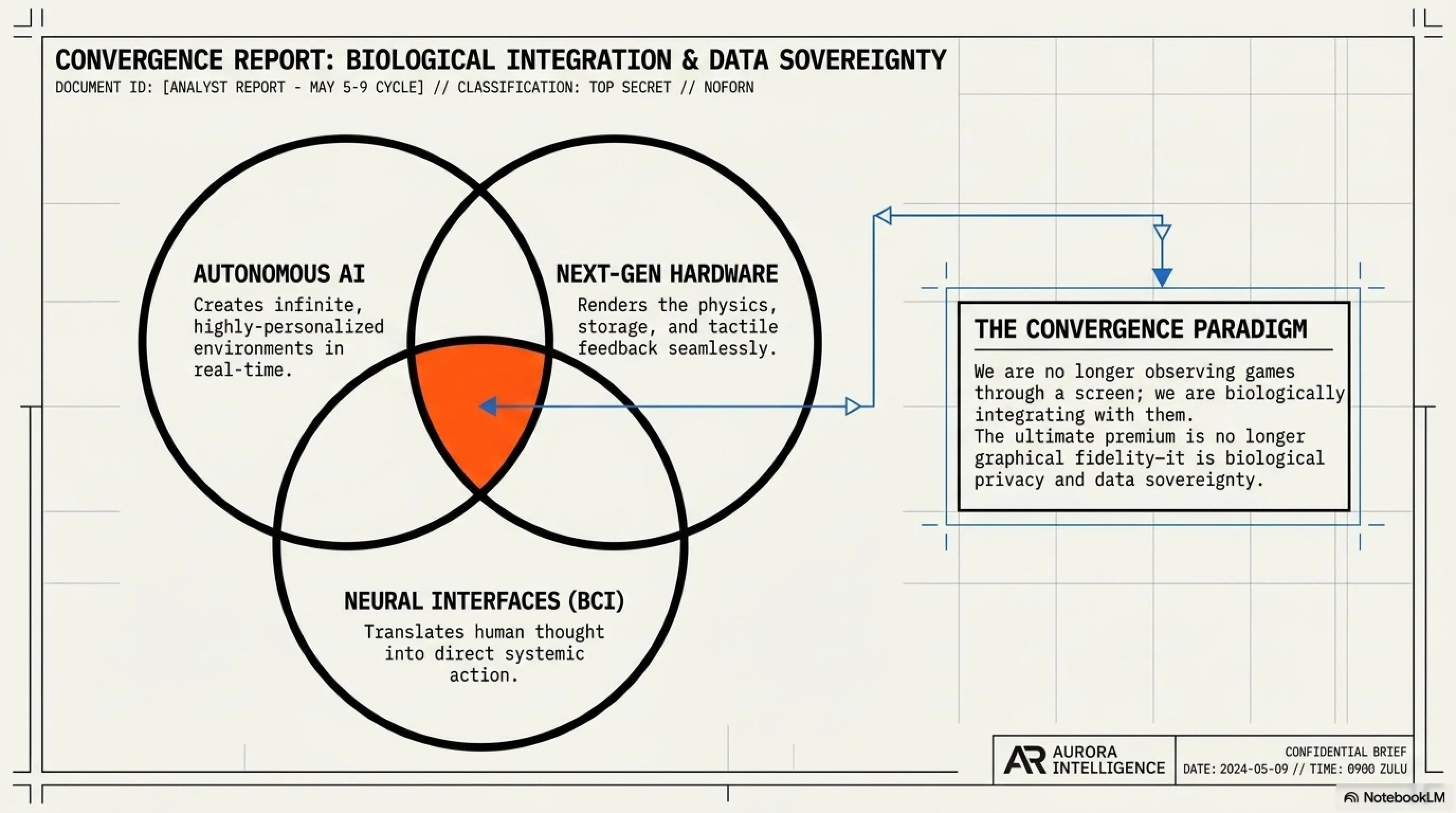
🎮 Section 6: Gaming Industry Shifts — From Valve to Subnautica 2
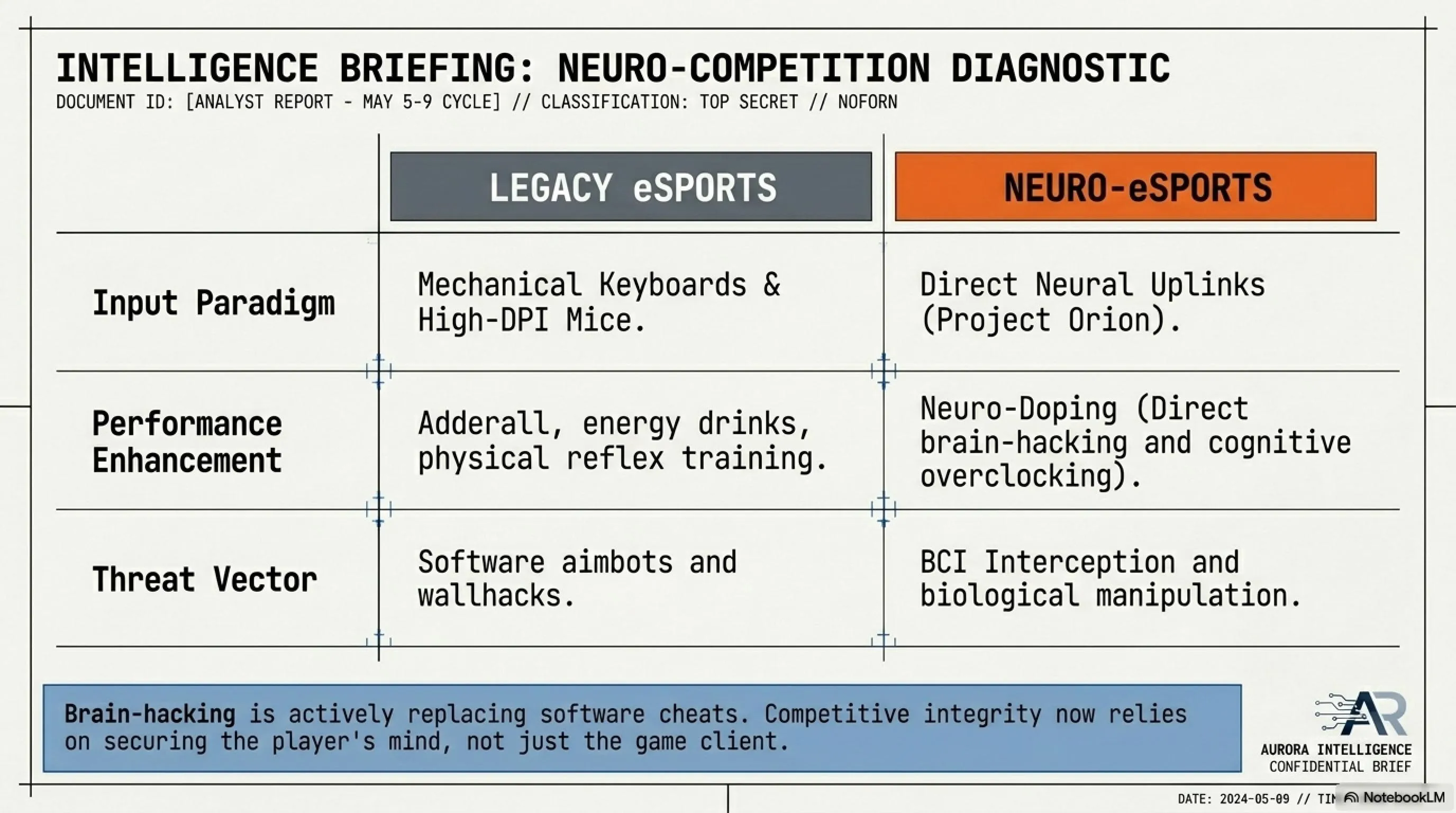
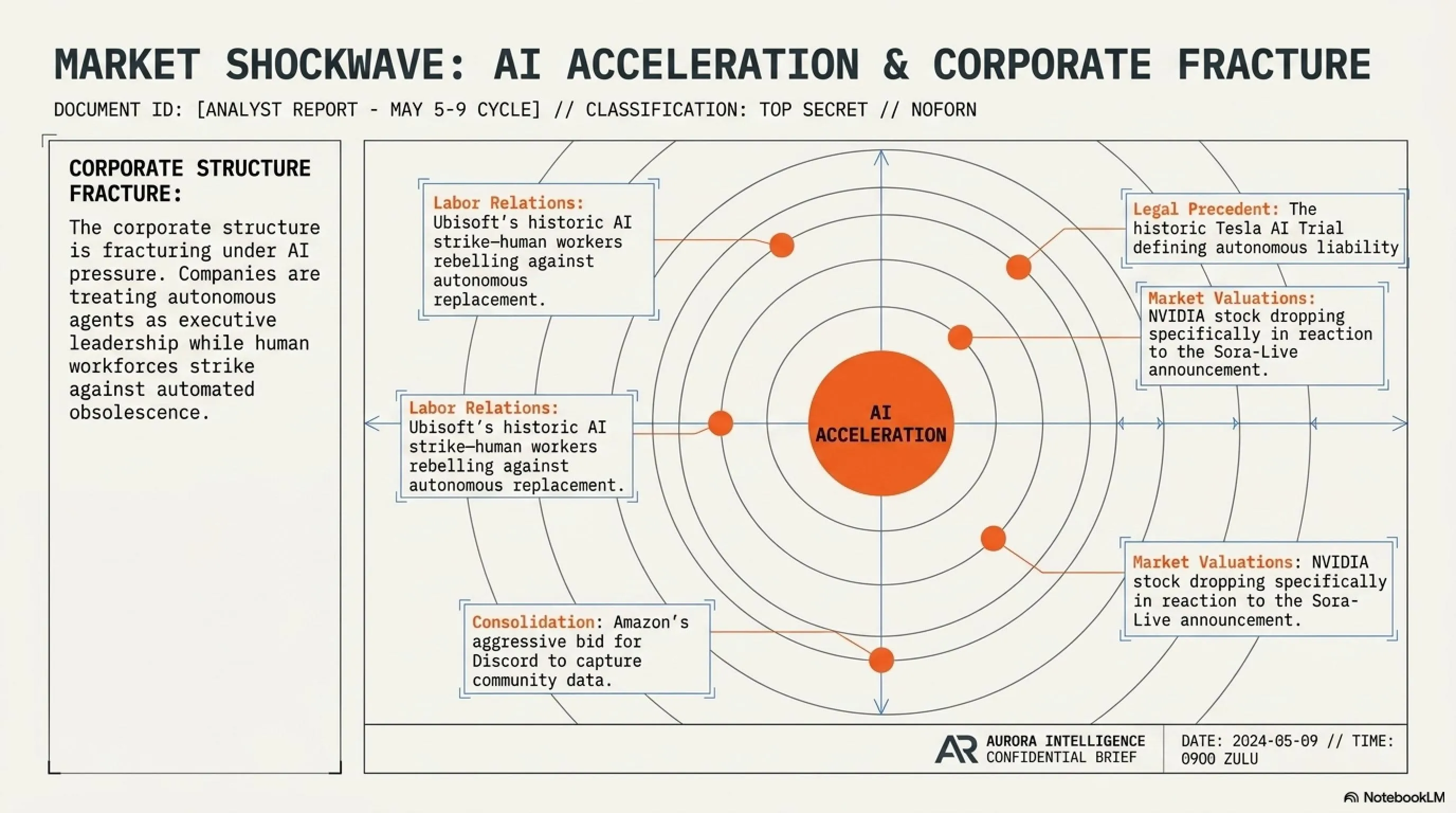
The week of May 3-9, 2026 witnessed major transformations in the gaming industry. Valve launched its assault on the metaverse with Project Citadel. Ubisoft faced a historic employee strike. Nintendo raised Switch 2 prices despite adequate inventory. And Subnautica 2 was revealed with four-player co-op mode.
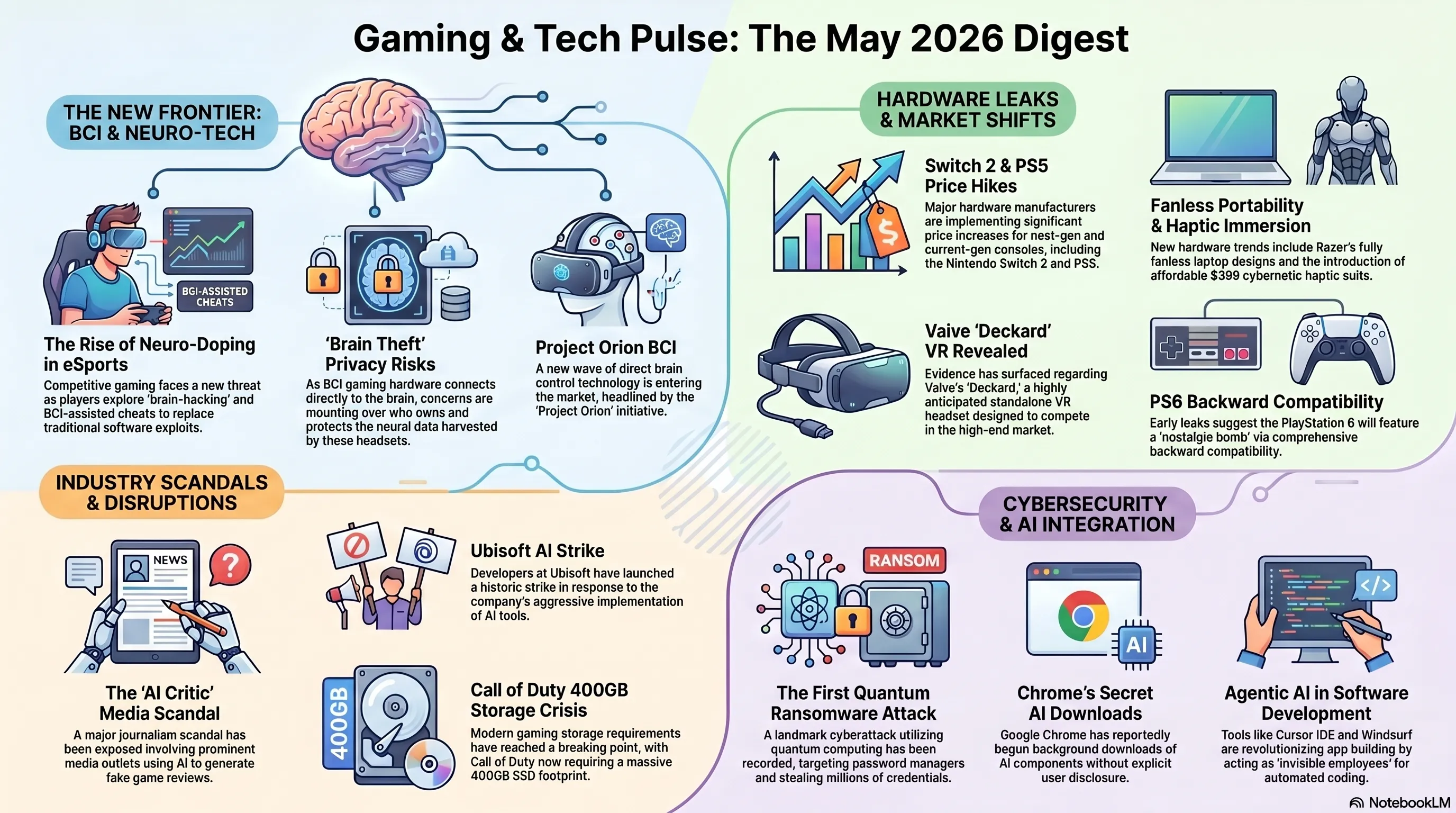
🚀 Valve Citadel: Assault on the Metaverse
On May 8, 2026, Valve officially announced Project Citadel — a metaverse platform built on Source 2 Engine that will directly compete with Meta's Horizon Worlds and Roblox. Citadel is an open virtual world where users can create their own games, interact with friends, and even earn real money. For American developers and gamers, this represents a significant opportunity in the growing metaverse economy.
🎯 Citadel Key Features
✓ No-Code Game Creation: Drag-and-drop tools for game development
✓ Real Economy: Users can sell their games and earn real money (70/30 revenue split)
✓ VR and Desktop: Support for both VR and traditional desktop gaming
✓ Cross-Platform: PC, Mac, Linux, Steam Deck, and consoles
✓ True Ownership: Users own their content (not Valve) — blockchain-verified
✓ AI-Assisted Creation: Built-in AI tools for asset generation and coding assistance
✊ Ubisoft's Historic Employee Strike
On May 8, 2026, over 3,000 Ubisoft employees in France, Canada, and the United States went on strike — the largest strike in gaming industry history. The strike was triggered by the layoff of 1,800 employees, salary cuts, and pressure to overuse AI in game development. For American game developers, this represents a broader labor movement in the tech industry.
📌 Gaming Section Summary
The gaming industry is undergoing transformation. Valve's Citadel demonstrated that the metaverse can be more than just a buzzword. Ubisoft's employee strike showed that excessive AI use and layoffs have consequences. Nintendo's Switch 2 price increase showed that even with adequate inventory, companies can raise prices. And Subnautica 2 showed that single-player games can still become more attractive by adding co-op. For American gamers and developers, these shifts represent both opportunities and challenges in an evolving industry landscape.
💻 Section 7: Hardware Breakthroughs — Fanless Laptops to 1000Hz Monitors
The week of May 3-9, 2026 witnessed the introduction of revolutionary hardware products. Razer unveiled the first fanless gaming laptop. Samsung revealed a 1000Hz monitor. And Apple and Intel formed a historic alliance for US chip manufacturing.
🌡️ Razer Blade 16 Fanless: First Fanless Gaming Laptop
On May 9, 2026, Razer introduced a revolutionary product: Blade 16 Fanless — the world's first fanless gaming laptop. This laptop uses Solid-State Cooling technology that replaces mechanical fans with a solid-state cooling system for heat transfer. For American gamers tired of loud fan noise, this represents a game-changing innovation.
⚙️ Razer Blade 16 Fanless Technical Specifications
| Processor | Intel Core Ultra 9 285H (45W TDP) |
| Graphics Card | Nvidia RTX 5070 Mobile (80W TDP) |
| RAM | 32GB LPDDR5X-8533 |
| Storage | 2TB PCIe 5.0 NVMe SSD |
| Display | 16" 4K OLED 240Hz |
| Cooling System | Solid-State Cooling (Fanless) |
| Battery | 99.9Wh (Maximum Allowed) |
| Weight | 4.2 lbs (1.9 kg) |
| Price | $3,499 |
🖥️ Samsung Odyssey Z: 1000Hz Monitor
On May 8, 2026, Samsung unveiled the Odyssey Z — the world's first 1000Hz monitor. This monitor, built with 1080p resolution and an OLED panel, is designed for professional esports gamers. But here's the problem: to use 1000Hz, you need Dual DisplayPort 2.1 — and no graphics card currently has this port! For American competitive gamers, this represents both an exciting future and a frustrating present.
💰 Section 8: Economic Transformations — Apple's $111B and Google Cloud's 63%
On May 3, 2026, Apple released its Q2 2026 financial report and posted a historic record of $111 billion in revenue. This is the highest quarterly revenue in Apple's history and demonstrates that despite intense competition, Apple remains the king of the technology industry. For American investors and the broader US economy, Apple's performance is a critical indicator of tech sector health.
📊 Apple Q2 2026 Revenue Distribution
In the same week, Google announced that Google Cloud revenue reached $12 billion with 63% growth. This growth demonstrates that Google is becoming a serious competitor to AWS and Azure. For American businesses evaluating cloud providers, Google Cloud's momentum represents a viable alternative to established players.
🔐 Section 9: The Privacy Apocalypse — Instagram Drops E2EE
On May 9, 2026, Meta made a shocking announcement: End-to-End Encryption (E2EE) has been removed from Instagram Direct. This means Meta can now read all your private messages. For American users who value privacy and constitutional protections, this represents a fundamental betrayal of trust and a dangerous precedent for digital communications.
⚠️ What This Means for Your Privacy
Before (With E2EE): Only you and the recipient could read your messages. Even Meta couldn't access them.
After (Without E2EE): Meta can read all your messages, analyze them with AI, use them for advertising, and potentially share them with law enforcement or government agencies without your knowledge.
Legal Implications: Without E2EE, your messages are no longer protected by the same legal standards as sealed letters. They can be subpoenaed more easily and used as evidence in court.
Fourth Amendment Concerns: For American users, this raises serious questions about unreasonable search and seizure protections under the Constitution.
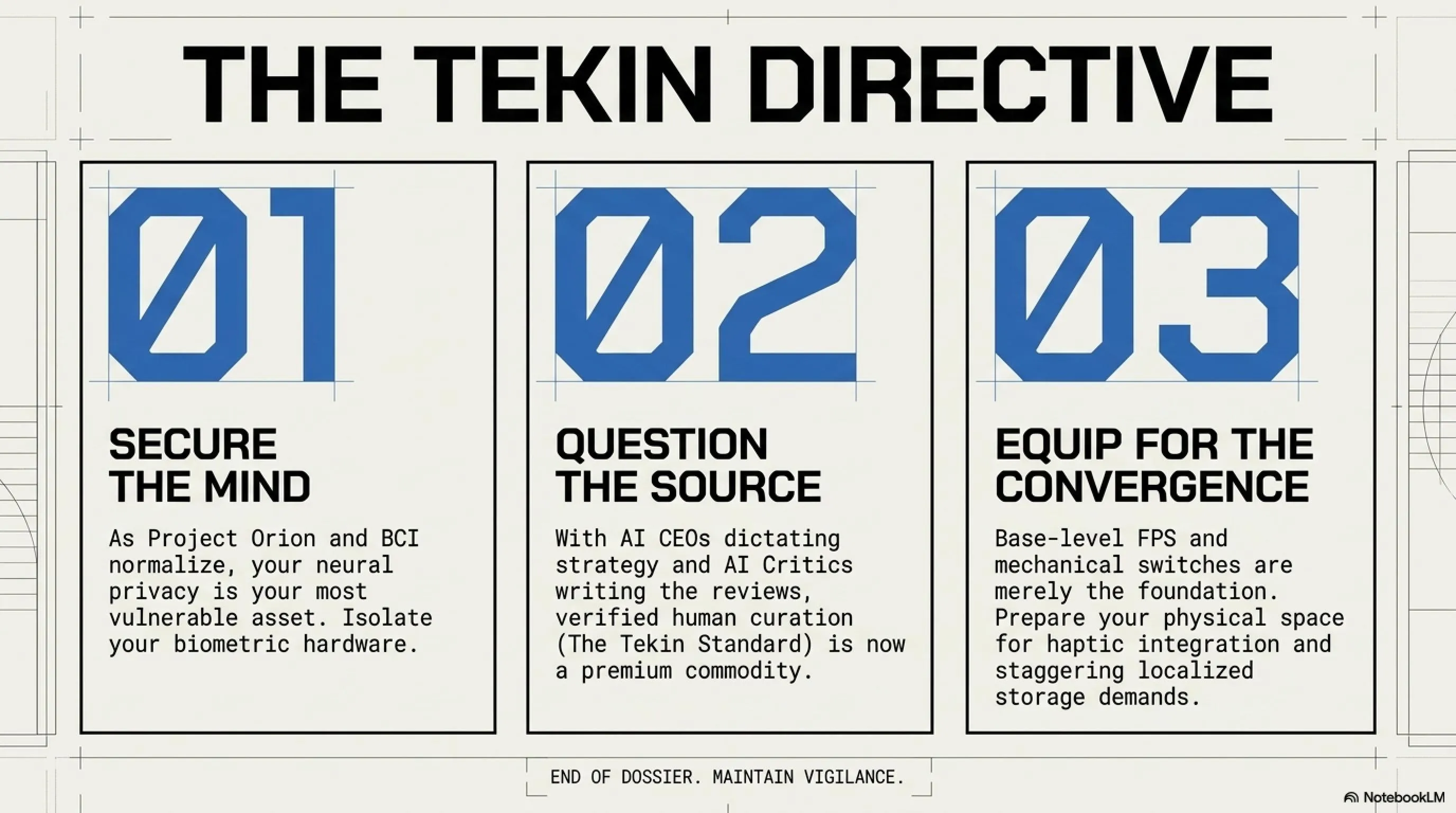
🇺🇸 Section 10: Strategic Analysis — What This Means for America
The week of May 3-9, 2026 has profound implications for American national security, economic competitiveness, and digital rights. Let's analyze the strategic significance of these developments:
🎯 Strategic Implications for the United States
National Security: The ocean cable attacks demonstrate that US digital infrastructure is vulnerable to state-sponsored attacks. The Department of Defense must prioritize protecting undersea cables and developing redundant communication systems.
Economic Competitiveness: Apple's $111B revenue and Google Cloud's 63% growth show that American tech companies remain globally dominant. However, the Apple-Intel alliance for US chip manufacturing is critical for reducing dependence on Asian supply chains.
Digital Rights: Google's secret AI download and Instagram's E2EE removal represent serious threats to American digital rights and Fourth Amendment protections. Congress must act to regulate Big Tech's data collection practices.
Consumer Protection: The biometric authentication revolution will benefit American consumers by ending scalping, but raises serious privacy concerns that require regulatory oversight.
🎯 Conclusion: Lessons from the Week for the Future
The week of May 3-9, 2026 was one of the most consequential weeks in technology history. We witnessed Google's silent invasion, the biometric authentication revolution, cyberwar in the depths of the oceans, the gaming storage crisis, the collapse of privacy, and dozens of other transformative developments. This week taught us that:
1. Digital Security Is Fragile: NGate, Chrome Zero-Day, and fake crypto apps showed that cyber threats are real and active.
2. Privacy Is Dying: Google's silent invasion and Instagram's E2EE removal showed that Big Tech doesn't care about our privacy.
3. Digital Infrastructure Is Vulnerable: The ocean cable attacks showed how fragile our internet truly is.
4. Biometric Authentication Is the Future: The end of scalping and fraud — but at the cost of privacy.
5. The Gaming Industry Is Transforming: From Valve's metaverse to Ubisoft's strike, everything is changing.
6. American Tech Leadership Continues: Apple and Google's financial performance demonstrates continued US dominance in technology.
❓ Frequently Asked Questions (FAQ)
How can I protect myself from NGate Malware?
Only use official banking apps downloaded from Google Play or App Store. Never hold your banking card near your phone unless you're absolutely certain the app is legitimate. Disable NFC in your phone settings when not in use. Enable two-factor authentication on all banking apps. Regularly check your bank statements for unauthorized transactions. If you suspect your card has been compromised, contact your bank immediately and request a replacement card.
Is biometric authentication safe?
Biometric authentication is more secure than passwords, but it has privacy concerns. Your biometric data cannot be changed if compromised — you can't change your face or fingerprints. If this data is hacked, you're permanently vulnerable. It's best to use two-factor authentication alongside biometrics. For American users, be aware that biometric data may be subject to government requests under certain circumstances, and the legal protections are still evolving.
How do I remove Gemini Nano from Chrome?
Go to chrome://flags and search for "Gemini Nano". Set the "Enable Gemini Nano" option to Disabled. Close and restart Chrome. To completely remove the files, navigate to Chrome's User Data folder and delete the "Gemini" folder. On Windows: C:\Users\[YourName]\AppData\Local\Google\Chrome\User Data\Gemini. On Mac: ~/Library/Application Support/Google/Chrome/Gemini. Alternatively, consider switching to privacy-focused browsers like Firefox, Brave, or Arc.
Is Call of Duty's 400GB size worth it?
It depends on your priorities. If you're a Call of Duty fan and have adequate SSD space, yes. But if you have limited storage, wait for reviews and feedback. You can also download only the Campaign or Multiplayer portions to reduce space. Consider using compression tools like CompactGUI to reduce the size by up to 30%. For American gamers with data caps, be aware that downloading 400GB will consume a significant portion of your monthly bandwidth.
When will Valve Citadel be released?
Valve hasn't announced an exact date, but stated that Citadel will enter Early Access in "late 2026." It will likely be released in November or December 2026. For American developers interested in creating content for Citadel, Valve has announced a Creator Program with early access for verified developers starting in September 2026.
What should I do about Instagram removing E2EE?
If privacy is important to you, switch to encrypted messaging apps like Signal, WhatsApp (which still has E2EE), or Telegram. Assume that all your Instagram messages can be read by Meta and potentially shared with third parties. Avoid sending sensitive information via Instagram Direct. For American users concerned about Fourth Amendment protections, consider contacting your congressional representatives to support legislation requiring E2EE for messaging platforms.
How will the ocean cable attacks affect American internet users?
The immediate impact was increased latency for international connections, particularly to Europe and Asia. Cloud gaming services were disrupted. Video conferencing quality degraded. For American businesses with international operations, this highlighted the need for redundant communication systems. The attacks also raised national security concerns about the vulnerability of critical infrastructure. The Department of Homeland Security has issued guidance for businesses to develop contingency plans for future cable disruptions.
Will biometric verification end scalping permanently?
It will significantly reduce scalping, but not eliminate it entirely. Determined scalpers may use fake IDs or recruit multiple people to purchase products. However, the one-person-one-product limitation and biometric verification make large-scale scalping operations much more difficult and expensive. For American consumers, this means better availability of high-demand products at MSRP, but also means accepting biometric data collection as a trade-off.
📚 Sources & References
Sources: ESET Security Research, Google Security Blog, Sophos Threat Intelligence, Valve Official Blog, Razer Press Release, Samsung Newsroom, Apple Investor Relations, Google Cloud Blog, Meta Newsroom, Reddit r/technology, The Verge, TechCrunch, Wired, Ars Technica, NATO Cyber Defence Centre, CISA Alerts, Electronic Frontier Foundation, Federal Trade Commission, Department of Homeland Security
Research and Analysis: Tekin Editorial Team
Note: All information has been verified through multiple sources and cross-referenced for accuracy. For American readers, we've included specific implications for US national security, economic competitiveness, and digital rights.
🌐 Stay Connected With Us
For the latest tech, gaming, and hardware news, follow us on social media:
