In the May 1, 2026 Tekin Night mega-report, we dissect the deepest technology and security developments. From the 9-year hidden Linux vulnerability (Copy Fail) to Samsung's strategic decision to replace Windows with Android 17 on Galaxy Books. We also analyze OpenAI's powerful new GPT-5.4-Cyber model and the catastrophic theft of 9 million medical records from Medtronic by ShinyHunters.
🌙 Welcome to Tekin Night May 1, 2026
Good evening, tech enthusiasts! Tonight we bring you six absolutely critical and groundbreaking stories from the world of technology. From a catastrophic Linux vulnerability that's been hiding for 9 years to OpenAI's new cybersecurity AI model, from Samsung's shocking decision to ditch Windows to a massive medical data breach affecting 9 million patients, plus two blockbuster games launching this month - we've got it all covered!
⚡ Tonight's Headlines:
🐧 Copy Fail: Critical Linux Vulnerability Hidden for 9 Years
🤖 OpenAI GPT-5.4-Cyber: New Cybersecurity Defense Model
💻 Samsung Galaxy Book: Goodbye Windows, Hello Android 17
🏥 Medtronic: 9 Million Medical Records Stolen by ShinyHunters
🏎️ Forza Horizon 6: Japan with 550+ Real Cars - May 19
🕴️ 007 First Light: Young Bond with Lana Del Rey - May 27
🌃 Grab your evening beverage and get ready for a deep dive into the most important tech stories of the day!
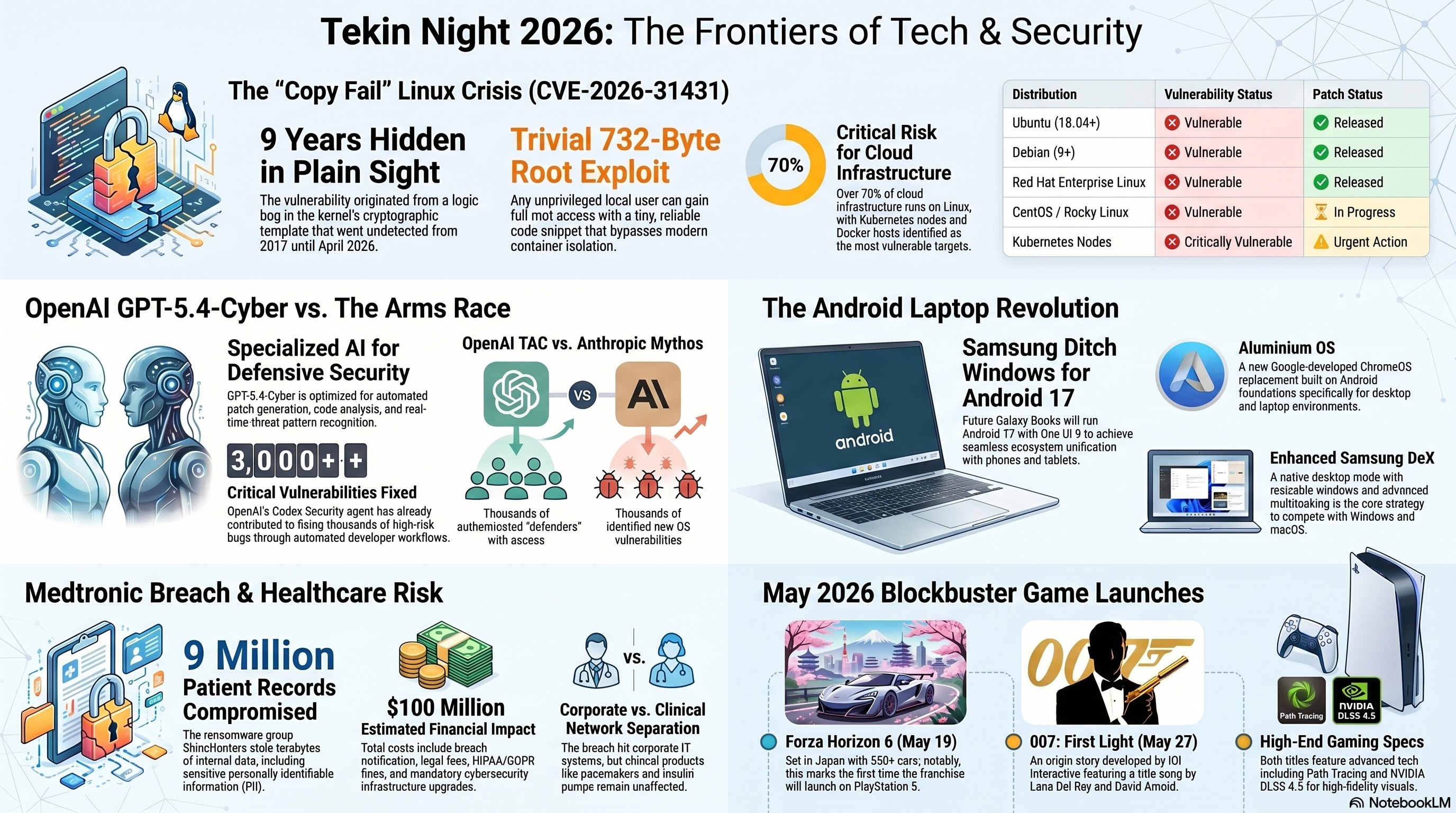
🐧 Copy Fail: The 9-Year-Old Linux Kernel Vulnerability That Changes Everything
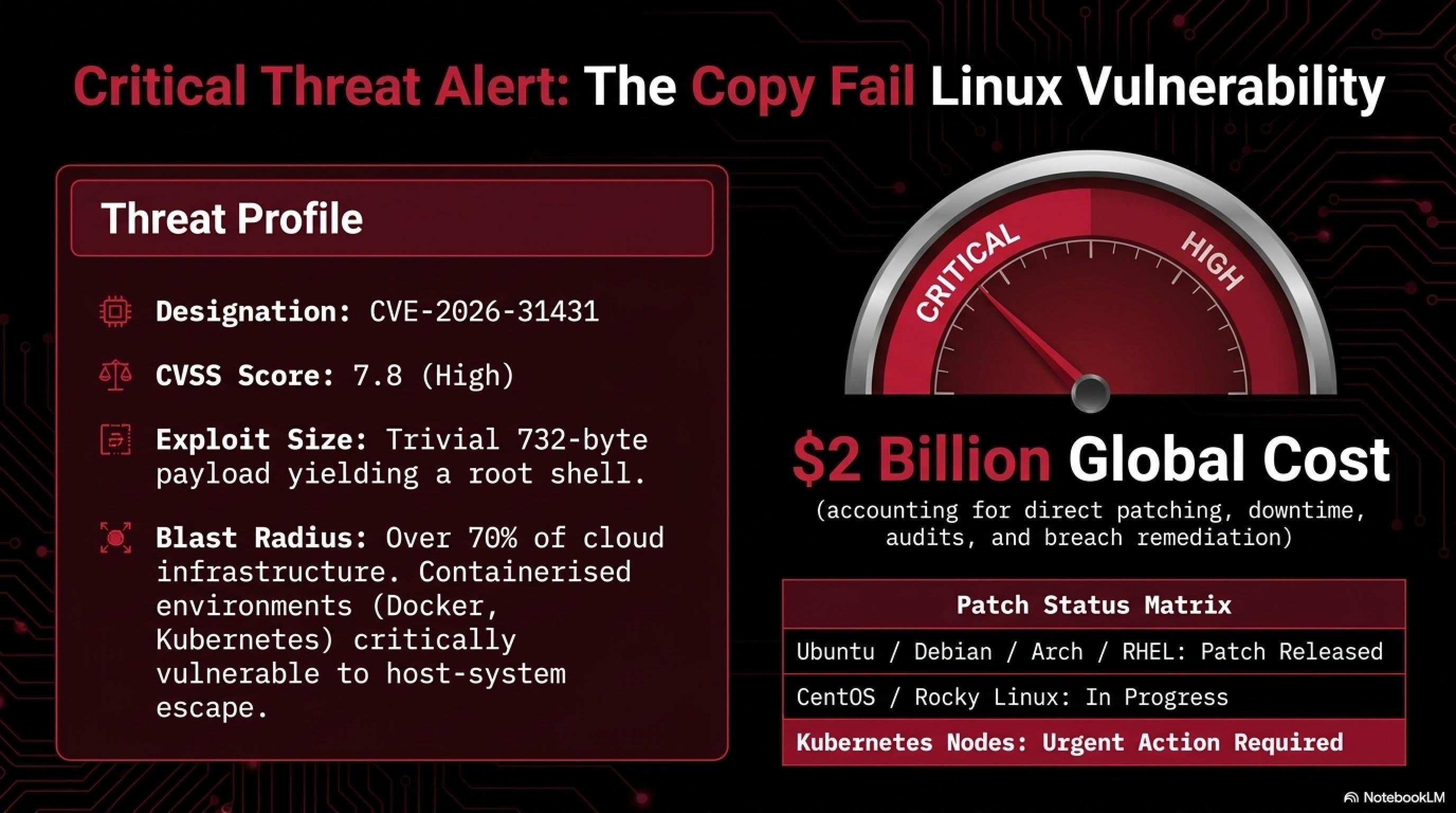
In what security researchers are calling one of the most severe Linux threats to surface in years, cybersecurity firm Theori has disclosed a critical privilege escalation vulnerability in the Linux kernel that has been lurking in the code since 2017. Dubbed Copy Fail and tracked as CVE-2026-31431, this vulnerability allows any unprivileged local user to gain root access with a trivial 732-byte exploit. The implications are staggering: virtually every major Linux distribution shipped since 2017 is vulnerable, and a working proof-of-concept exploit is now publicly available.
⚠️ Technical Deep Dive: CVE-2026-31431
Copy Fail is a logic bug in the Linux kernel's authencesn cryptographic template. According to Theori researchers, the vulnerability originates from the interaction of three seemingly reasonable kernel changes made over several years: the addition of authencesn (an AEAD cryptographic wrapper used by IPsec) in 2011, the introduction of AF_ALG AEAD socket support in 2015, and an in-place optimization added to algif_aead in 2017. Each change was benign on its own, but their combination created a dangerous vulnerability that went unnoticed for nearly a decade.
The vulnerability allows an attacker to write arbitrary code to other files' memory and obtain a root shell. What makes this particularly dangerous is that containerized environments like Docker and Kubernetes are especially vulnerable - an attacker can escape from a container and gain access to the host system. This represents a fundamental breakdown in container isolation, one of the core security principles of modern cloud infrastructure.
The vulnerability was discovered on April 29, 2026, and publicly disclosed by CERT-EU and multiple security organizations. What's particularly alarming is how the bug remained undetected despite Linux being one of the most scrutinized open-source projects in the world. The code was "hiding in plain sight," as security researchers put it - visible to anyone who looked at the kernel source, but the subtle interaction between three separate features made it nearly impossible to spot without specifically looking for it.
What makes Copy Fail particularly dangerous is the reliability and simplicity of the exploit. Theori researchers have published a proof-of-concept that demonstrates how an attacker can achieve root access with just 732 bytes of code. This exploit works across all major Linux distributions and doesn't require any special conditions or race conditions to succeed. Security experts are calling this one of the most "trivial" exploits in recent years - meaning even relatively inexperienced attackers can successfully use it. The exploit has already been weaponized and is being actively used in the wild, according to multiple threat intelligence sources.
🛡️ Immediate Action Required for System Administrators
- Update Linux kernel to the latest patched version immediately
- If immediate patching isn't possible, implement temporary mitigations
- Prioritize Kubernetes nodes and container hosts
- Review system logs for suspicious privilege escalation attempts
- Restrict access for unprivileged users where possible
- Deploy monitoring tools to detect exploitation attempts
- Consider implementing kernel runtime protection (e.g., SELinux, AppArmor)
🔍 Tekin Analysis: Why Did This Bug Hide for 9 Years?
This vulnerability reveals a fundamental challenge in software security: even heavily scrutinized open-source code can harbor hidden bugs for years. The primary reason Copy Fail went undetected is that it resulted from the interaction of three separate changes made over several years. None of these changes were problematic on their own, but their combination created a dangerous vulnerability. This is what security researchers call an "emergent vulnerability" - one that only appears when multiple seemingly safe components interact in unexpected ways.
The incident highlights several critical lessons for the software industry. First, code review processes need to consider not just individual changes but also how new code interacts with existing systems. Second, static analysis tools and fuzzing should be continuously run on existing code, not just new additions. Third, the Linux community needs better tools for detecting subtle logic bugs that span multiple subsystems.
Interestingly, the vulnerability was discovered through a combination of manual code review and automated analysis. The Linux community is now conducting a comprehensive audit of other kernel subsystems to ensure no similar vulnerabilities exist. This incident also raises questions about the security of other long-lived codebases - if a bug can hide in Linux for 9 years, what else might be lurking in critical infrastructure software?
📊 Industry Impact Assessment
The impact of Copy Fail extends far beyond individual Linux systems. According to industry estimates, over 70% of cloud infrastructure runs on Linux, and containerized environments (which are especially vulnerable to this exploit) power the majority of modern web applications. Major cloud providers including AWS, Google Cloud, and Microsoft Azure have all issued urgent security advisories to their customers.
The financial impact is also significant. Cybersecurity insurance companies estimate that the total cost of patching and securing systems against Copy Fail could exceed $2 billion globally. This includes direct patching costs, system downtime, emergency security audits, and potential breach remediation for organizations that fail to patch in time. Several Fortune 500 companies have already reported attempted exploitation of this vulnerability in their environments.
🤖 OpenAI GPT-5.4-Cyber: The AI Arms Race in Cybersecurity Defense
On Tuesday, April 29, 2026, OpenAI unveiled GPT-5.4-Cyber, a specialized variant of its flagship GPT-5.4 model that's specifically optimized for defensive cybersecurity use cases. This announcement came just days after rival Anthropic unveiled its own frontier model, Mythos, marking an escalation in what industry observers are calling the "AI cybersecurity arms race." OpenAI stated that the goal is to "accelerate defenders - those responsible for keeping systems, data, and users safe - enabling them to find and fix problems faster in the digital infrastructure everyone relies on."
🎯 GPT-5.4-Cyber: Key Capabilities and Features
| Capability | Description |
| Vulnerability Detection | Advanced code analysis and security bug identification |
| Patch Generation | Automated security fix proposals and remediation |
| Threat Analysis | Pattern recognition for attack vectors and threats |
| Continuous Learning | Real-time updates with emerging threats |
| Integration | Seamless workflow integration for developers |
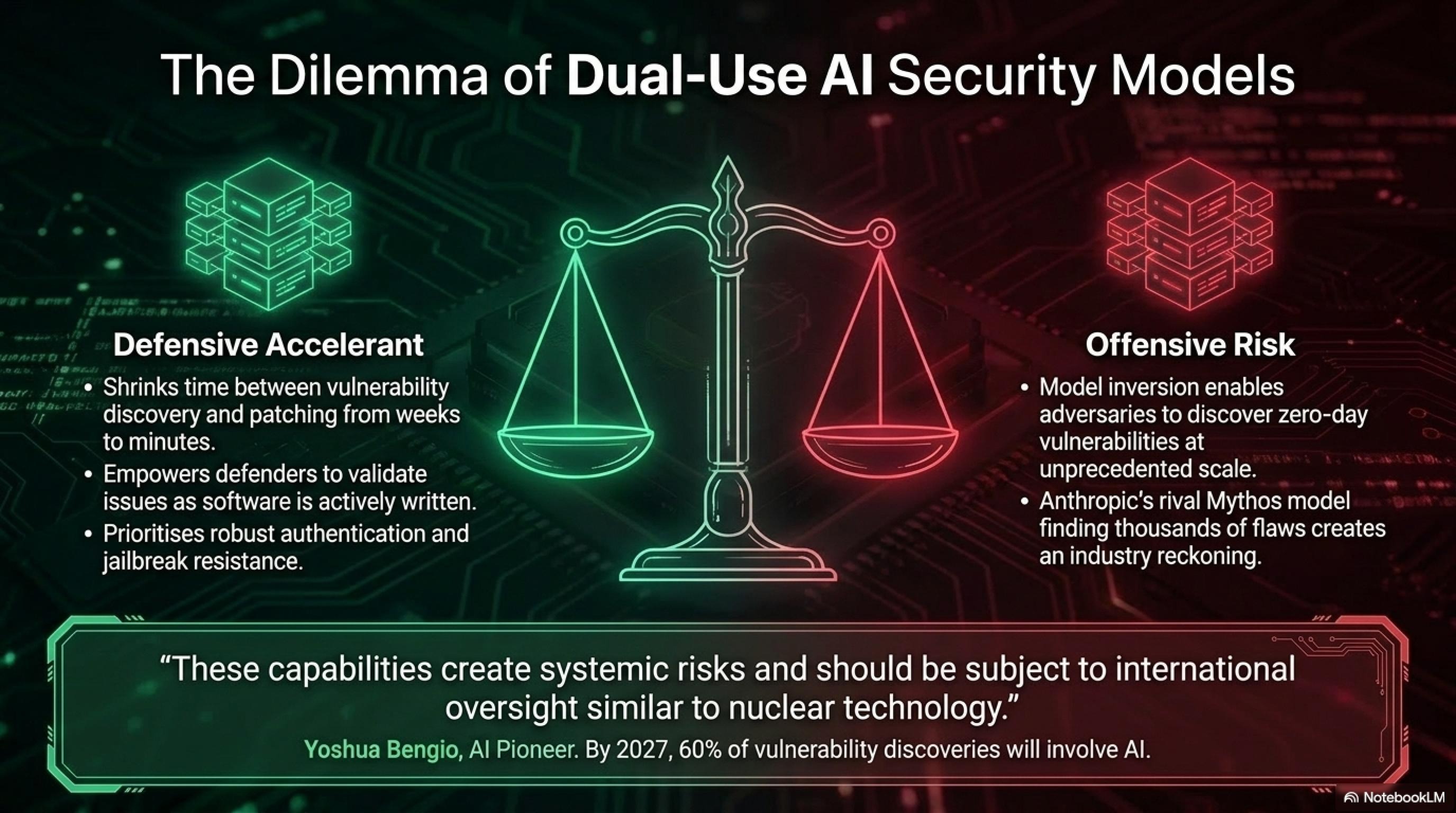
Alongside the announcement, OpenAI significantly expanded its Trusted Access for Cyber (TAC) program, granting access to thousands of authenticated individual defenders and hundreds of teams responsible for securing critical software. This represents a major strategic shift in how AI companies approach the dual-use problem - the reality that AI systems can be repurposed by bad actors for malicious goals. One core area of concern is that adversaries could invert models fine-tuned for software defense to detect and exploit vulnerabilities in widely-used software before they can be patched, exposing users to significant risks.
OpenAI's approach is to democratize access to its models while minimizing misuse, as well as strengthening safeguards through a deliberate, iterative rollout. The company stated: "As model capabilities advance, our approach is to scale cyber defense in lockstep: broadening access for legitimate defenders while continuing to strengthen safeguards." This includes implementing robust authentication systems, monitoring for misuse, and continuously improving the model's resistance to jailbreaks and adversarial prompt injections.
⚔️ The AI Cybersecurity Arms Race: OpenAI vs Anthropic
The release of GPT-5.4-Cyber came just days after Anthropic previewed Mythos, a frontier model being deployed in a controlled manner as part of Project Glasswing. Anthropic claimed that Mythos found "thousands" of vulnerabilities in operating systems, web browsers, and other software, calling it a "reckoning" for the cybersecurity industry. This competitive dynamic is driving rapid innovation but also raising concerns among security experts and policymakers.
The competition between OpenAI and Anthropic represents a broader trend: major AI companies are turning cybersecurity into a primary battleground. Both companies emphasize that their approach is "defensive" and aimed at helping defenders, but experts worry that these technologies could fall into the wrong hands and be used to discover zero-day vulnerabilities at scale. The dual-use nature of these models creates a fundamental dilemma: the same capabilities that make them excellent at finding and fixing vulnerabilities also make them potentially dangerous if misused.
Yoshua Bengio, one of the "godfathers of AI," has called for urgent international cooperation on AI cybersecurity capabilities. He argues that the concentration of power in a few AI companies creates systemic risks and that these capabilities should be subject to international oversight similar to nuclear technology. The debate over how to govern these powerful tools is just beginning, and the decisions made in the coming months could shape the future of cybersecurity for decades.
✅ Codex Security: Real-World Results
OpenAI revealed that Codex Security - an AI-powered application security agent - has contributed to over 3,000 critical and high fixed vulnerabilities. This demonstrates that AI can be genuinely effective in cybersecurity. OpenAI stated: "The strongest ecosystem is one that continuously identifies, validates, and fixes security issues as software is written. By integrating advanced coding models and agentic capabilities into developer workflows, we can give developers immediate, actionable feedback while they are building, shifting security from episodic audits and static bug inventories to ongoing, tangible risk reduction."
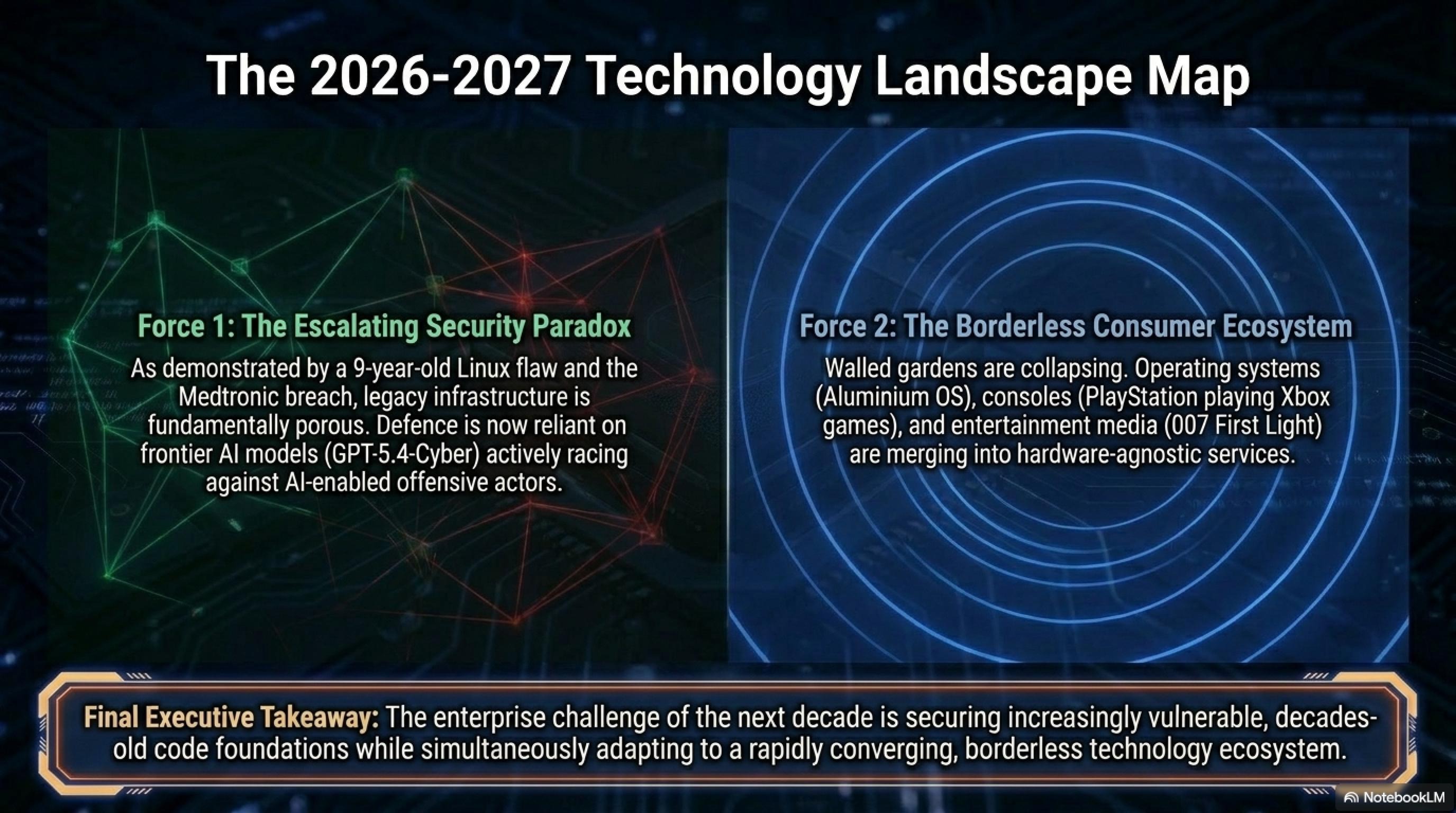
🔮 Forward-Looking Analysis: What This Means for 2026-2027
The introduction of GPT-5.4-Cyber and similar models marks a turning point in cybersecurity. We're entering an era where AI will play a central role in both offense and defense. Industry analysts predict that by 2027, over 60% of vulnerability discoveries will involve AI assistance, and the time between vulnerability discovery and exploitation will shrink from weeks to hours or even minutes. This creates an urgent need for organizations to adopt AI-powered defense tools or risk falling hopelessly behind.
However, this also raises important questions about the future of cybersecurity as a profession. Will human security researchers become obsolete, or will they evolve into AI supervisors and strategists? How will we ensure that AI-powered security tools don't introduce new vulnerabilities? And most critically, how can we prevent an AI-driven vulnerability discovery race that leaves software users perpetually exposed? These are the questions that will define the next chapter of cybersecurity.
💻 Samsung Galaxy Book: The Android Laptop Revolution Begins
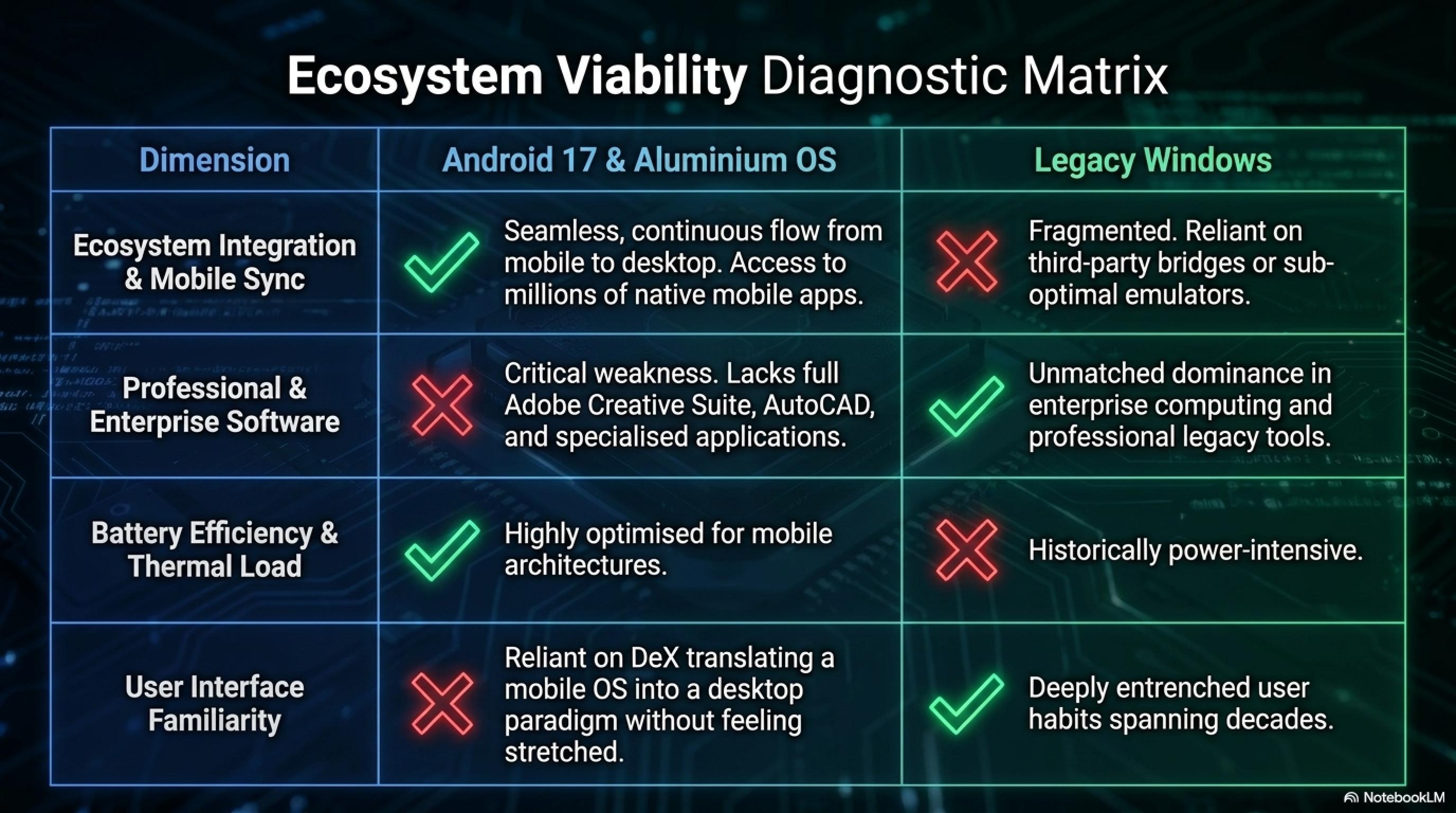
In one of the most surprising strategic decisions of 2026, Samsung is planning to launch future Galaxy Book laptops running Android 17 with One UI 9 instead of Windows 11. According to reports from multiple sources, Samsung is developing at least three Galaxy Book models spanning entry-level to flagship tiers. This decision could represent a seismic shift in the laptop industry and signals Samsung's move toward complete Galaxy ecosystem unification. The timing coincides with Google's introduction of Aluminium OS, a new ChromeOS replacement built on Android, at their upcoming I/O conference.
📱 Galaxy Book with Android 17: Complete Specifications
| Feature | Details |
| Operating System | Android 17 with One UI 9 |
| Model Range | At least 3 models (entry, mid, flagship) |
| Key Feature | Enhanced Samsung DeX for desktop experience |
| AI Integration | Galaxy AI integrated across product line |
| Flagship Design | "Very sleek" to compete with premium hardware |
| Expected Announcement | Google I/O 2026 (May) |
This strategic shift comes as Google prepares to unveil Aluminium OS, a new operating system that replaces ChromeOS and is built on Android foundations, specifically optimized for laptops and desktop devices. Samsung will likely use this new OS alongside One UI 9 to create a unified experience across phones, tablets, watches, TVs, and now laptops. The move represents Samsung's bet that the future of computing lies in ecosystem integration rather than traditional desktop operating systems.
🔄 Samsung DeX: The Key to Android Laptop Success
Samsung DeX is a desktop mode that has existed for years in Samsung's flagship phones and tablets. This capability allows users to use Android like a full desktop operating system with resizable windows, a taskbar, and advanced multitasking. Now Samsung plans to include an enhanced version of DeX in Android Galaxy Books, potentially solving one of the biggest challenges facing Android laptops: providing a true desktop experience.
Android 17 is set to introduce a native desktop mode similar to DeX available on Samsung flagship phones. Additionally, Google will add a new bubble-based multitasking feature to the OS to make running multiple apps simultaneously easier. These changes demonstrate that Android is evolving into a truly multi-purpose operating system capable of competing with Windows and macOS on their home turf.
✅ Advantages of Android on Laptops
- Complete Galaxy ecosystem integration
- Access to millions of Android apps
- Better battery life (mobile optimization)
- Galaxy AI everywhere
- Likely lower price than Windows
- Seamless phone-to-laptop continuity
- Touch-optimized interface
⚠️ Potential Challenges
- Lack of professional software (Adobe, AutoCAD)
- Legacy software compatibility
- User habits tied to Windows
- Android app limitations for desktop
- Competition with Chromebook and Windows
- Enterprise adoption barriers
- Developer tool availability
The success of Samsung's Android laptops will largely depend on how well DeX and Aluminium OS can provide a true desktop experience. If Samsung can convince developers to optimize their apps for larger screens and desktop workflows, and if Google can ensure that Aluminium OS provides the performance and compatibility users expect, this could be a game-changer. However, if the experience feels like a stretched-out phone interface, users will quickly return to Windows or macOS.
📊 Market Analysis: Can Android Compete with Windows?
The laptop market is currently dominated by Windows (approximately 70% market share) and macOS (approximately 20%), with ChromeOS holding about 8% primarily in education. Android laptops face an uphill battle, but Samsung has several advantages. First, the Galaxy ecosystem is already massive, with hundreds of millions of users worldwide. Second, Android app availability far exceeds ChromeOS, giving users access to a vast software library. Third, Samsung's brand strength and distribution network can ensure wide availability.
However, the challenges are significant. Windows dominates enterprise computing, and businesses are unlikely to switch without compelling reasons. Professional users rely on Windows-exclusive software like Adobe Creative Suite, AutoCAD, and specialized industry applications. Gaming is another weak point - while Android has mobile games, it lacks the AAA titles that drive Windows laptop sales. Samsung's success will depend on targeting specific use cases: students, casual users, and Galaxy ecosystem enthusiasts who prioritize integration over raw power.
🏥 Medtronic Data Breach: 9 Million Medical Records Compromised
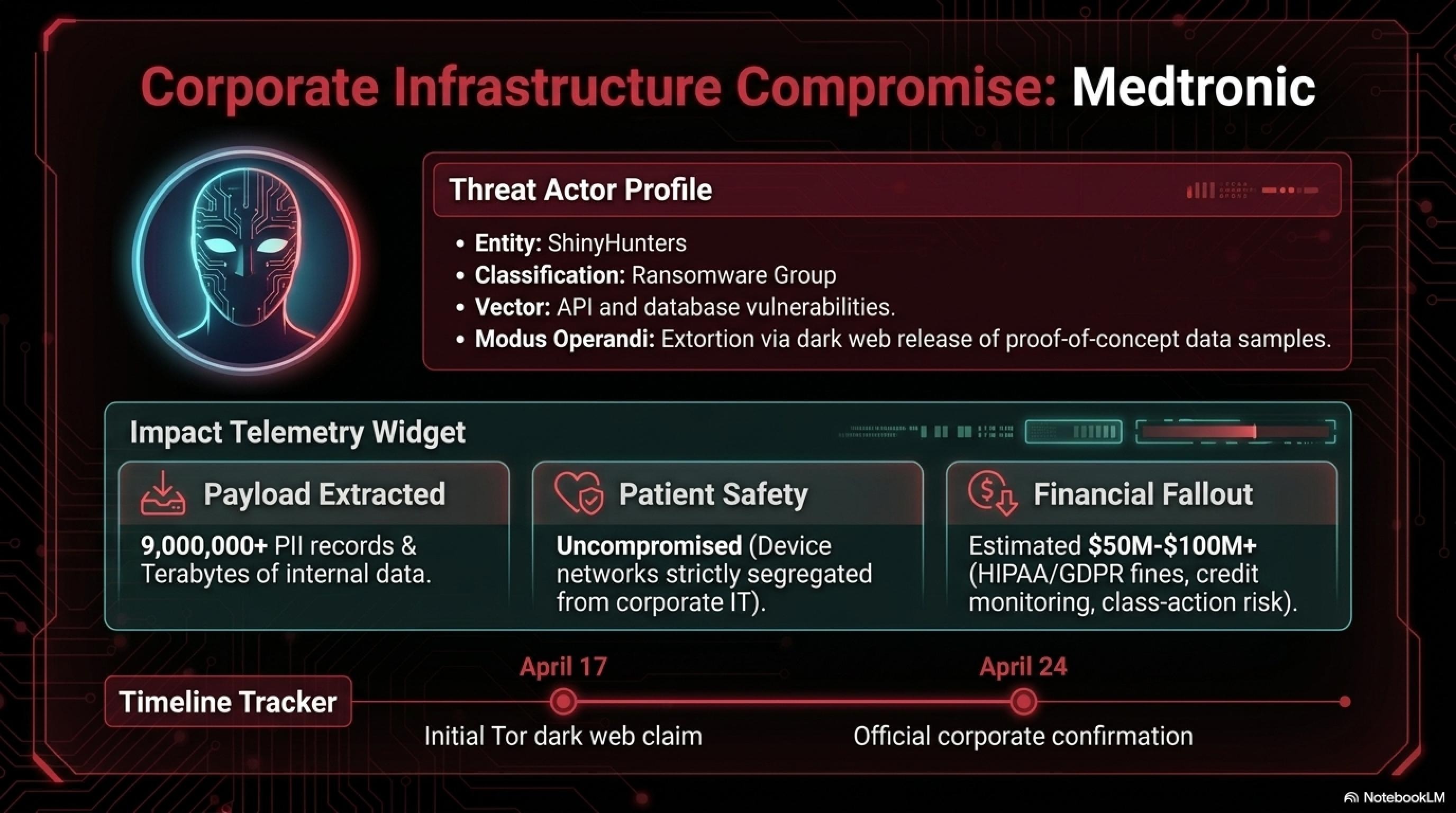
Medical technology giant Medtronic - the company behind pacemakers, insulin pumps, and surgical robots used in hospitals worldwide - confirmed on April 24, 2026, that an unauthorized third party had breached its corporate IT systems and accessed stored data. This confirmation came after the notorious hacking group ShinyHunters claimed to have stolen over 9 million records containing personally identifiable information (PII) along with terabytes of internal corporate data. The breach represents one of the largest healthcare data compromises of 2026 and raises serious questions about the security of medical device manufacturers.
🚨 Medtronic Data Breach: Complete Timeline and Impact
| Attribute | Details |
| Initial Claim Date | April 17, 2026 |
| Official Confirmation | April 24, 2026 |
| Records Compromised | 9+ Million PII Records |
| Data Volume | Terabytes of internal corporate data |
| Threat Actor | ShinyHunters (ransomware group) |
| Patient Safety Impact | ✅ No impact on patient safety |
| Estimated Financial Impact | $50-100M+ (recovery, fines, lawsuits) |
Medtronic emphasized that there is no evidence of impact on products, manufacturing/distribution operations, financial reporting systems, patient safety, or ability to meet patient needs. The company stated that networks supporting corporate IT operations are separate from other functions. However, the compromise of 9 million people's data is an extremely serious incident that could have significant legal and financial consequences. Medical data is among the most valuable information on the dark web because it includes complete personal information, medical history, insurance details, and often Social Security numbers.
🎭 ShinyHunters: A Notorious Ransomware Group
ShinyHunters is one of the most active and dangerous ransomware groups, with a history of attacking major companies including Microsoft, AT&T, Ticketmaster, Zara, Carnival, and 7-Eleven. The group typically exploits API and database vulnerabilities to gain access, then either sells the stolen data on the dark web or uses it for extortion. Their modus operandi involves posting proof-of-concept data samples to demonstrate the legitimacy of their claims, then threatening to release the full dataset if ransom demands aren't met.
In the Medtronic case, ShinyHunters initially posted their claim on April 17 on the Tor dark web network and provided samples of stolen data as "proof." They then threatened the company with a negotiation deadline. Interestingly, Medtronic was later removed from the group's leak site - a move that sometimes indicates negotiations or other developments, though no confirmation has been provided. The group's track record suggests they're sophisticated, persistent, and willing to follow through on threats if demands aren't met.
This attack demonstrates that even large medical technology companies responsible for the health of millions of patients are vulnerable to cyberattacks. Medical data is among the most valuable information on the dark web because it includes complete personal information, medical history, insurance information, and often Social Security numbers. This information can be used for identity theft, insurance fraud, and other crimes. The healthcare sector has become a prime target for ransomware groups because of the sensitive nature of the data and the potential for significant ransom payments.
💰 Financial and Legal Implications
The financial impact of this breach could be substantial. Based on similar incidents, Medtronic could face costs including: breach notification and credit monitoring services ($50-100 per affected individual), regulatory fines under HIPAA and GDPR (potentially 4% of annual revenue), class-action lawsuits from affected patients, cybersecurity infrastructure upgrades, and reputational damage leading to lost business. Industry analysts estimate the total cost could exceed $100 million.
Beyond financial costs, this breach raises important questions about the security practices of medical device manufacturers. If hackers can access patient data, could they also potentially access systems that control medical devices? While Medtronic insists that device networks are separate from corporate IT, the incident highlights the need for defense-in-depth strategies and zero-trust architectures in healthcare technology companies.
🛡️ If You're a Medtronic Patient or User
If you use Medtronic products or your information is stored in their systems, we recommend: 1) Wait for official notification from Medtronic 2) Monitor your financial accounts and credit reports for suspicious activity 3) Use credit monitoring services (Medtronic may offer these for free) 4) Be vigilant for phishing emails and calls 5) Change passwords for health-related accounts 6) Consider placing a fraud alert or credit freeze 7) Review your medical records for unauthorized access.
🏎️ Forza Horizon 6: Japan's Open-World Racing Paradise - May 19
One of May's biggest gaming releases is almost here! Forza Horizon 6 launches on May 19, 2026 for Xbox Series X|S and PC (Microsoft Store and Steam), with early access for Premium Edition buyers starting May 15. Set in the breathtaking landscapes of Japan, the game features the largest open-world driving adventure in Forza Horizon history and puts over 550 real-world cars at players' fingertips. This marks a historic moment as the first Forza title to launch simultaneously on PlayStation 5 later this year, representing a major strategic shift from Microsoft.
🎮 Forza Horizon 6: Complete Specifications
| Feature | Details |
| Release Date | May 19, 2026 (Early Access: May 15) |
| Platforms | Xbox Series X|S, PC, PS5 (later 2026) |
| Setting | Japan (Largest map in series history) |
| Car Count | 550+ Real-World Cars |
| Game Pass | ✅ Day One on Game Pass |
| New Features | Seamless Races, New Collectibles, Enhanced Physics |
Forza Horizon 6 delivers a stunning recreation of Japan - from the neon-lit streets of Tokyo to mountain passes and bamboo forests - offering an unparalleled driving experience. The game includes new vehicles like the 2025 GR GT Prototype and 2025 Toyota Land Cruiser, as well as the legendary Aston Martin Valhalla Supercar. One of the standout new features is the Seamless Races system, which allows players to enter races without interruption, maintaining the flow of open-world exploration while providing structured competitive experiences.
🗾 Why Japan? The Perfect Setting for Horizon
Japan has been one of the most requested settings by Forza Horizon fans for years. The country offers an unparalleled combination of car culture (JDM), diverse landscapes, and legendary roads like the Hakone Turnpike and Daikoku Parking Area. From Tokyo's neon lights to Mount Fuji, from tight mountain hairpins to high-speed expressways - Japan has everything a racing game could want. The setting allows Playground Games to showcase both urban street racing and scenic countryside driving in a single cohesive map.
The game also celebrates Japan's drift and street racing culture. Legendary JDM cars like the Nissan Skyline GT-R, Toyota Supra, Mazda RX-7, and Honda NSX sit alongside modern supercars. Playground Games has promised this will be the largest and most diverse map in series history, with distinct regions representing different aspects of Japanese geography and culture. From cherry blossom-lined roads to industrial ports, from traditional villages to futuristic cityscapes, the game captures the full spectrum of Japan's automotive landscape.
🎯 Strategic Analysis: Xbox's Multi-Platform Future
Forza Horizon 6's PlayStation 5 release represents a significant strategic shift for Microsoft. Historically, Forza has been one of Xbox's flagship exclusive franchises, used to drive console sales and Game Pass subscriptions. By bringing it to PlayStation, Microsoft is signaling that its future lies in software and services rather than hardware exclusivity. This aligns with CEO Phil Spencer's vision of Xbox as a platform-agnostic gaming ecosystem.
The decision makes business sense: PlayStation 5 has a massive install base, and Forza Horizon 6 could potentially sell millions of additional copies on Sony's platform. However, it also raises questions about the value proposition of Xbox consoles. If major exclusives are coming to PlayStation, why buy an Xbox? Microsoft's answer seems to be Game Pass - the service offers day-one access to all Xbox titles, making it a compelling value even if the games eventually come to other platforms. This strategy could define the future of console gaming.
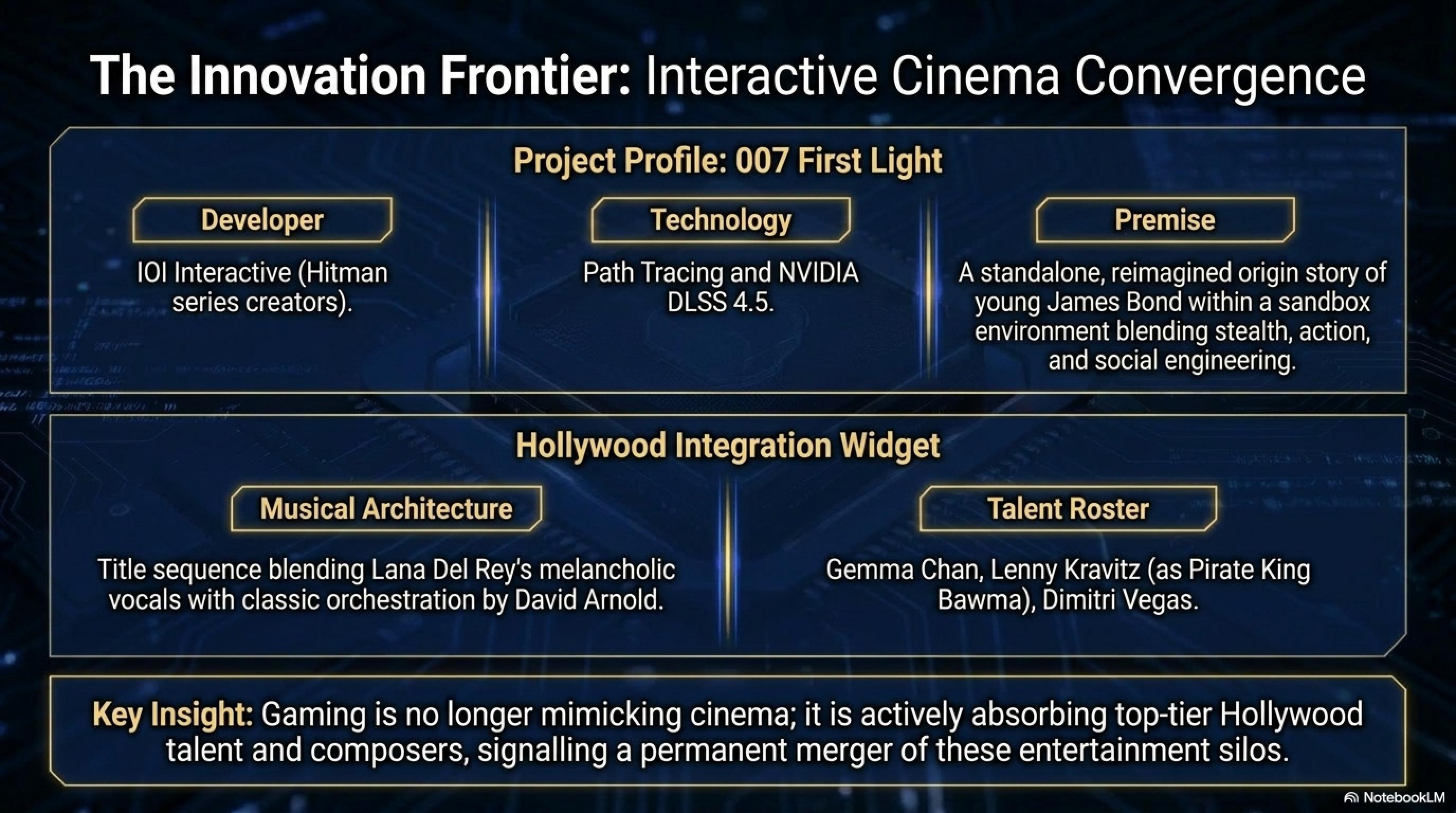
🕴️ 007 First Light: Young Bond with Lana Del Rey - May 27
The highly anticipated 007: First Light launches on May 27, 2026 for PlayStation 5, Xbox Series X|S, and PC, with 24-hour early digital access starting May 26. Developed by IOI Interactive (creators of the Hitman series), the game tells a standalone, reimagined James Bond origin story, following the events that transformed an audacious young recruit into MI6's best agent. The game features a title song performed by Lana Del Rey and composed by legendary Bond composer David Arnold, creating a cinematic experience that bridges classic Bond aesthetics with modern gaming.
🎬 007: First Light - Complete Specifications
| Feature | Details |
| Release Date | May 27, 2026 (Early Access: May 26) |
| Platforms | PS5, Xbox Series X|S, PC, ROG Ally |
| Switch 2 | Q3 2026 (Delayed) |
| Developer | IOI Interactive (Hitman series) |
| Title Song | Lana Del Rey & David Arnold |
| Cast | Gemma Chan, Lenny Kravitz, Dimitri Vegas |
| Tech Features | Path Tracing, NVIDIA DLSS 4.5 |
One of the most exciting aspects of 007: First Light is its title song, performed by Lana Del Rey and composed by David Arnold (the legendary composer behind Bond films like Casino Royale and Quantum of Solace). This combination of Lana's dreamy, melancholic voice with Arnold's classic Bond orchestration creates a cinematic experience that stands alongside iconic Bond themes. The game also features notable actors including Gemma Chan, Lenny Kravitz (as the Pirate King Bawma), and famous DJ Dimitri Vegas, bringing Hollywood-level talent to the gaming world.
🎮 Gameplay and Key Features
- Standalone, reimagined origin story of young James Bond
- Advanced espionage system with stealth, action, and decision-making
- Legendary Bond gadgets with modern mechanics
- Aston Martin Valhalla Supercar
- Path Tracing and NVIDIA DLSS 4.5 support
- Diverse environments and multiple mission approaches
- IOI's signature "sandbox" gameplay from Hitman series
007: First Light places you in the role of a young, talented, and sometimes reckless James Bond who is in MI6's training program. The game teaches you the rules of spycraft and shows how Bond became the legendary 007 agent. IOI Interactive, with its experience creating the Hitman series, has implemented sophisticated stealth and action systems that give players complete freedom of approach. You can go in guns blazing, use stealth and gadgets, or employ social engineering and manipulation - the choice is yours.
🎵 Lana Del Rey: The New Voice of Bond
Choosing Lana Del Rey to perform the title song was a bold and intelligent decision. Her dreamy, melancholic voice perfectly matches the theme of a young Bond origin story. David Arnold, who composed legendary Bond film scores including Casino Royale and Quantum of Solace, collaborated with Lana to create a cinematic and emotional piece. The combination of Arnold's classic Bond orchestration with Lana's unique vocal style creates something fresh yet familiar.
The game's title sequence, now released, combines classic Bond orchestration with Lana's distinctive voice. This song sits alongside legendary Bond themes like "Skyfall" by Adele and "No Time to Die" by Billie Eilish, demonstrating that the Bond franchise can still successfully collaborate with contemporary artists. The choice of Lana Del Rey also signals a more introspective, character-driven approach to this Bond story - less about explosions and more about the psychological journey of becoming 007.
💎 Tonight's Wrap-Up: Technology at a Crossroads
Tonight's stories reveal that the technology world stands at a critical crossroads. On one hand, 9-year-old vulnerabilities in Linux and attacks on major companies like Medtronic show that cybersecurity remains a massive challenge. On the other hand, AI models like GPT-5.4-Cyber are becoming powerful defensive tools, potentially shifting the balance in favor of defenders.
Samsung's decision to abandon Windows and move toward Android demonstrates that the boundaries between mobile and desktop are blurring. And of course, May's blockbuster games - Forza Horizon 6 and 007: First Light - show that the gaming industry continues to grow and innovate. A night full of critical news that every tech enthusiast needs to know!
❓ Is the Copy Fail vulnerability really that dangerous?
Yes, extremely dangerous. This vulnerability allows any unprivileged user to gain root access with a trivial 732-byte exploit. This means complete system control. What makes it even more dangerous is that all Linux distributions from 2017 to today are vulnerable, and the exploit is remarkably simple. Containerized environments like Docker and Kubernetes are especially at risk, as attackers can escape containers and access the host system.
❓ Can GPT-5.4-Cyber be misused by hackers?
This is a genuine concern. AI systems are inherently dual-use - they can be used for both defense and offense. OpenAI says it's managing this risk through a gradual rollout and strengthening safeguards. They're providing access to authenticated defenders and trying to prevent jailbreaks and misuse. However, experts remain concerned that this technology could be used to discover zero-day vulnerabilities at scale. The dual-use nature of these models creates a fundamental dilemma that the industry is still grappling with.
❓ Will Samsung's Android laptops succeed?
This is the billion-dollar question. There are clear advantages: Galaxy ecosystem integration, access to millions of Android apps, better battery life, and likely lower prices. But there are serious challenges: lack of professional software like Adobe and AutoCAD, user habits tied to Windows, and Android app limitations for desktop use. Success depends on Samsung DeX and Aluminium OS - if they can provide a true desktop experience, there's a chance. If it feels like a stretched phone interface, users will quickly return to Windows or macOS. The enterprise market will be particularly hard to crack.
❓ Who is responsible for the Medtronic attack?
The ransomware group ShinyHunters has claimed responsibility for this attack. This group has a history of attacking major companies including Microsoft, AT&T, Ticketmaster, Zara, and Carnival. They typically exploit API and database vulnerabilities and either sell stolen data on the dark web or use it for extortion. In Medtronic's case, over 9 million PII records plus terabytes of internal data were stolen. The group posted proof-of-concept samples and threatened to release the full dataset if demands weren't met.
❓ Is Forza Horizon 6 coming to PlayStation 5?
Yes! Forza Horizon 6 will first launch on May 19, 2026 for Xbox Series X|S and PC, but a PlayStation 5 version will also release later in 2026. This is the first time a Forza game has been released for PlayStation - a major strategic shift from Microsoft. The Nintendo Switch 2 version is also planned for Q3 2026. This multi-platform approach reflects Microsoft's evolving strategy of prioritizing software and services over hardware exclusivity.
❓ Why did IOI Interactive choose Lana Del Rey for 007?
Lana Del Rey's dreamy, melancholic voice perfectly matches the theme of a young Bond origin story. Her collaboration with David Arnold (legendary Bond composer) creates a bridge between classic Bond aesthetics and contemporary artistry. The choice signals a more introspective, character-driven approach to this Bond story - less about explosions and more about the psychological journey of becoming 007. It's a bold choice that sits alongside recent Bond themes by Adele and Billie Eilish, showing the franchise's ability to evolve while maintaining its identity.
📚 Sources and References
Sources: Theori Security Research, CERT-EU, Ars Technica, Cybernews, The Hacker News, OpenAI Official Blog, TechCrunch, PCWorld, Tech Advisor, Android Authority, Infosecurity Magazine, SecurityWeek, The Register, Forbes Gaming, Wikipedia, IOI Interactive Official, Xbox News, PlayStation Blog, SamMobile, Forza.net, Fortune, The Guardian, CSO Online, Help Net Security
Research and Analysis: Tekin Editorial Team
Publication Date: May 1, 2026
Content has been paraphrased and summarized for compliance with licensing restrictions. All sources are properly attributed.
🌐 Stay Connected With Us
For the latest tech, gaming, and gadget news, follow us on social media:
