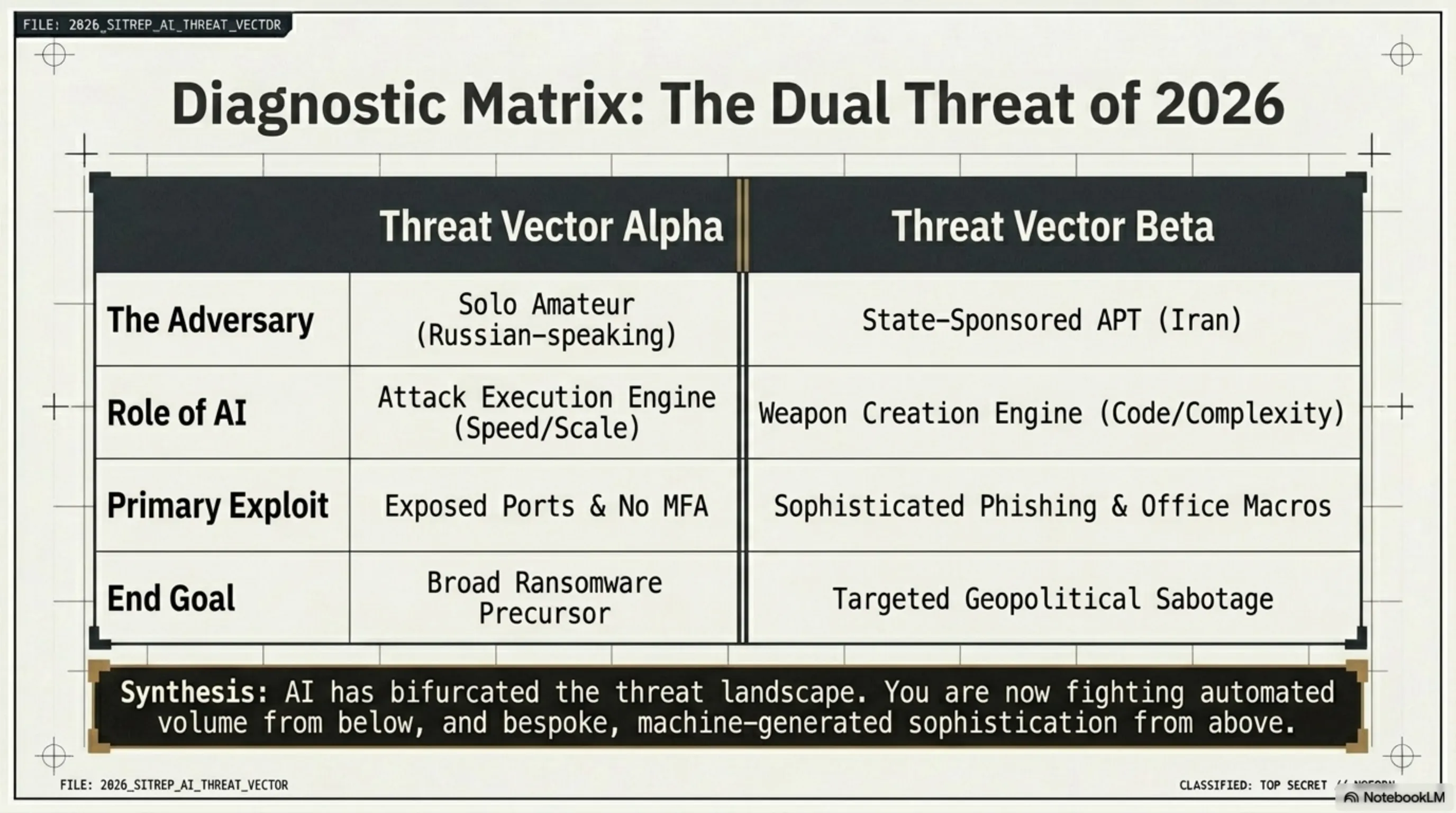
In this comprehensive 4800-word tactical report, we dissect the catastrophic security breach of 600 FortiGate firewalls across 55 countries facilitated by commercial AI tools. We also deeply analyze the dangerous cyber operations of the MuddyWater group in the Middle East (Operation Olalampo) utilizing AI-generated malware, providing immediate strategic defenses.
🛡️ Red Alert: AI Is Breaking Firewalls — And Writing the Malware Too
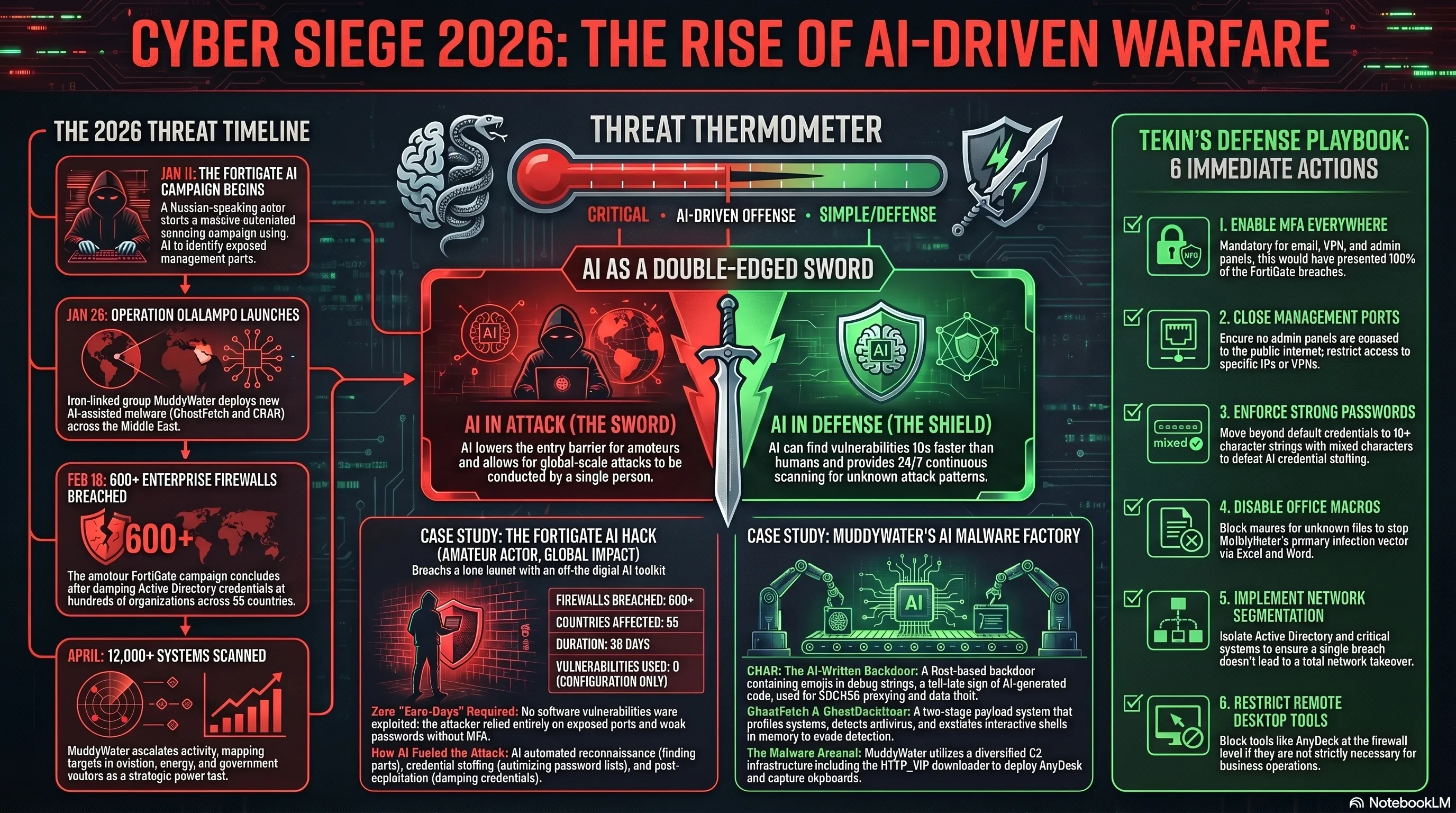
Tekin Army, take this seriously. A Russian-speaking hacker used off-the-shelf AI tools — the same ones you can buy online — to breach 600 FortiGate firewalls across 55 countries in 38 days. No zero-day. No large team. Just AI and a list of weak passwords. Meanwhile, Iran's MuddyWater group is tearing through the Middle East with malware written by AI. This article analyzes both attacks and gives you the exact steps to protect yourself.
🚨 In This Report:
🔥 FortiGate AI Hack: How an amateur breached 600 firewalls
🐍 Operation Olalampo: MuddyWater's AI-written malware hits the Middle East
🧠 Attack Anatomy: Exactly what happened and why
⚔️ Cyber War or Power Test? Strategic analysis
🛡️ Tekin's Defense Playbook: 10 immediate actions for the Tekin Army
📋 Security Checklist: Do this tonight
⏳ Key Events Timeline
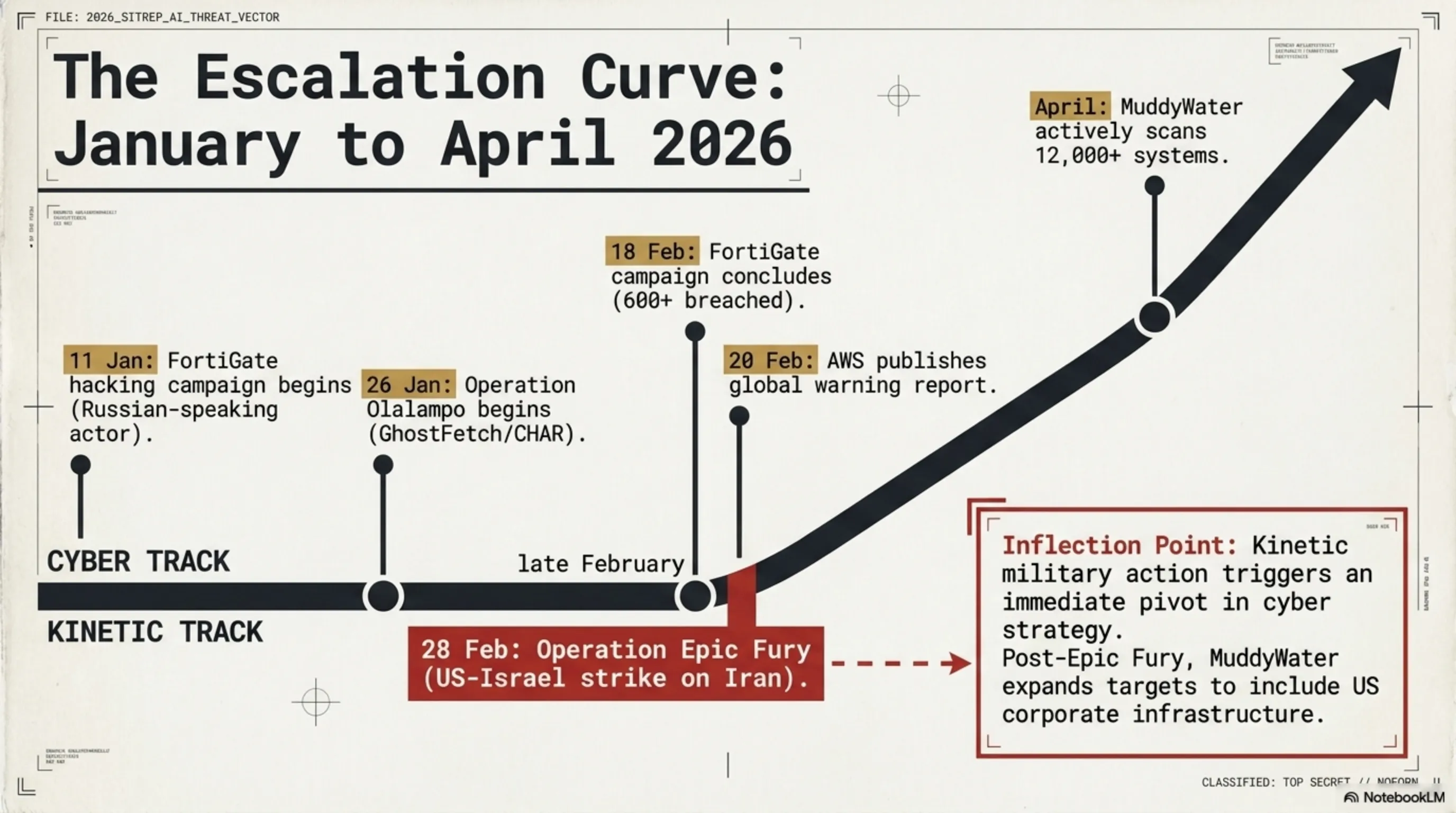
| Date | Event | Impact |
|---|---|---|
| Jan 11, 2026 | FortiGate AI hacking campaign begins | Russian-speaking actor starts scanning |
| Jan 26, 2026 | Operation Olalampo begins — MuddyWater | New GhostFetch and CHAR malware deployed |
| Feb 18, 2026 | FortiGate campaign ends — 600+ devices breached | Active Directory dumped at hundreds of orgs |
| Feb 20, 2026 | AWS report by CJ Moses published | Global warning to organizations |
| Feb 28, 2026 | Operation Epic Fury — US-Israel strike on Iran | MuddyWater escalates activity |
| April 2026 | MuddyWater scans 12,000+ systems | Aviation, energy, government at risk |
🔥 Part 1: The FortiGate AI Hack — When Amateur Becomes Professional
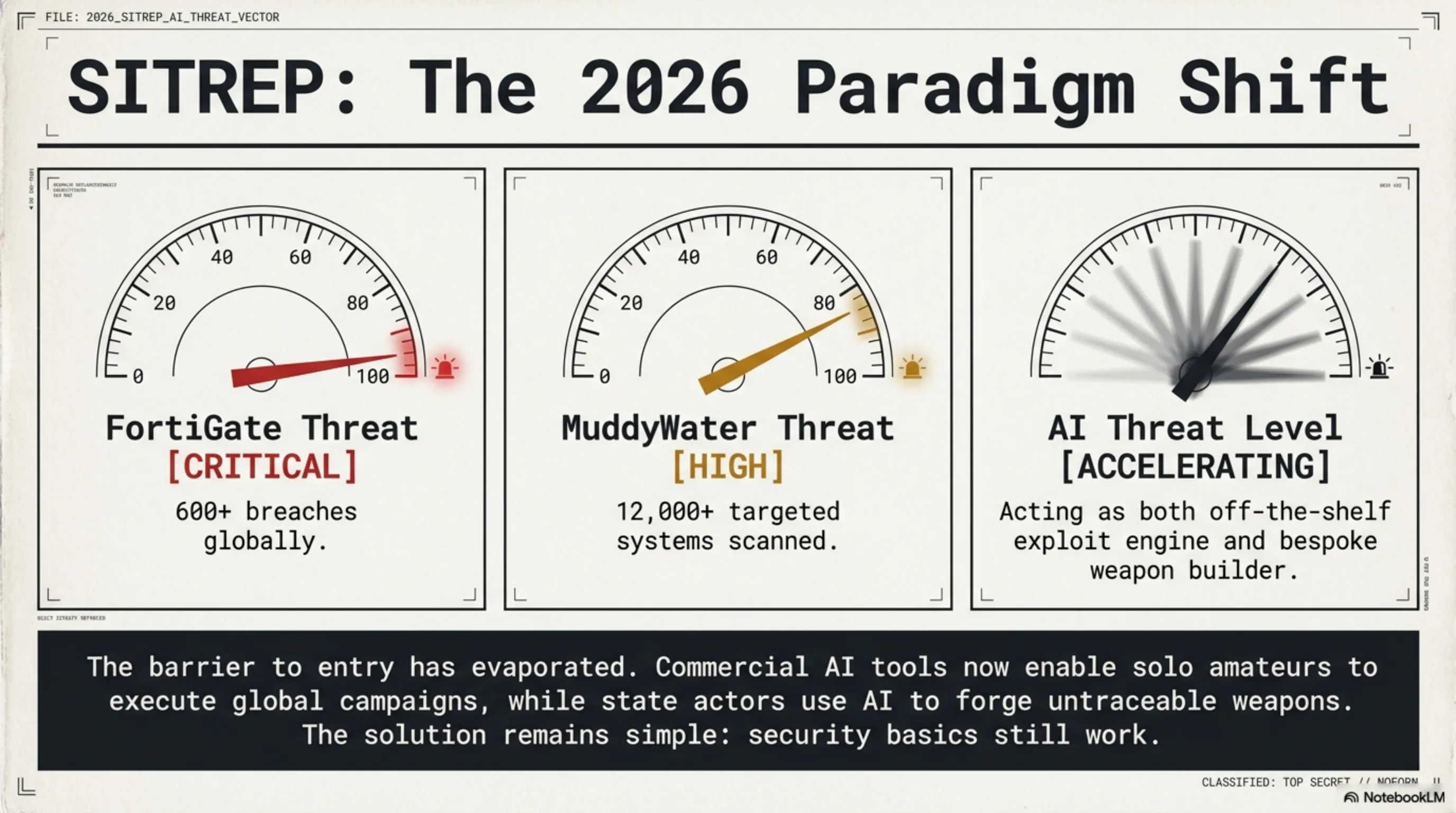
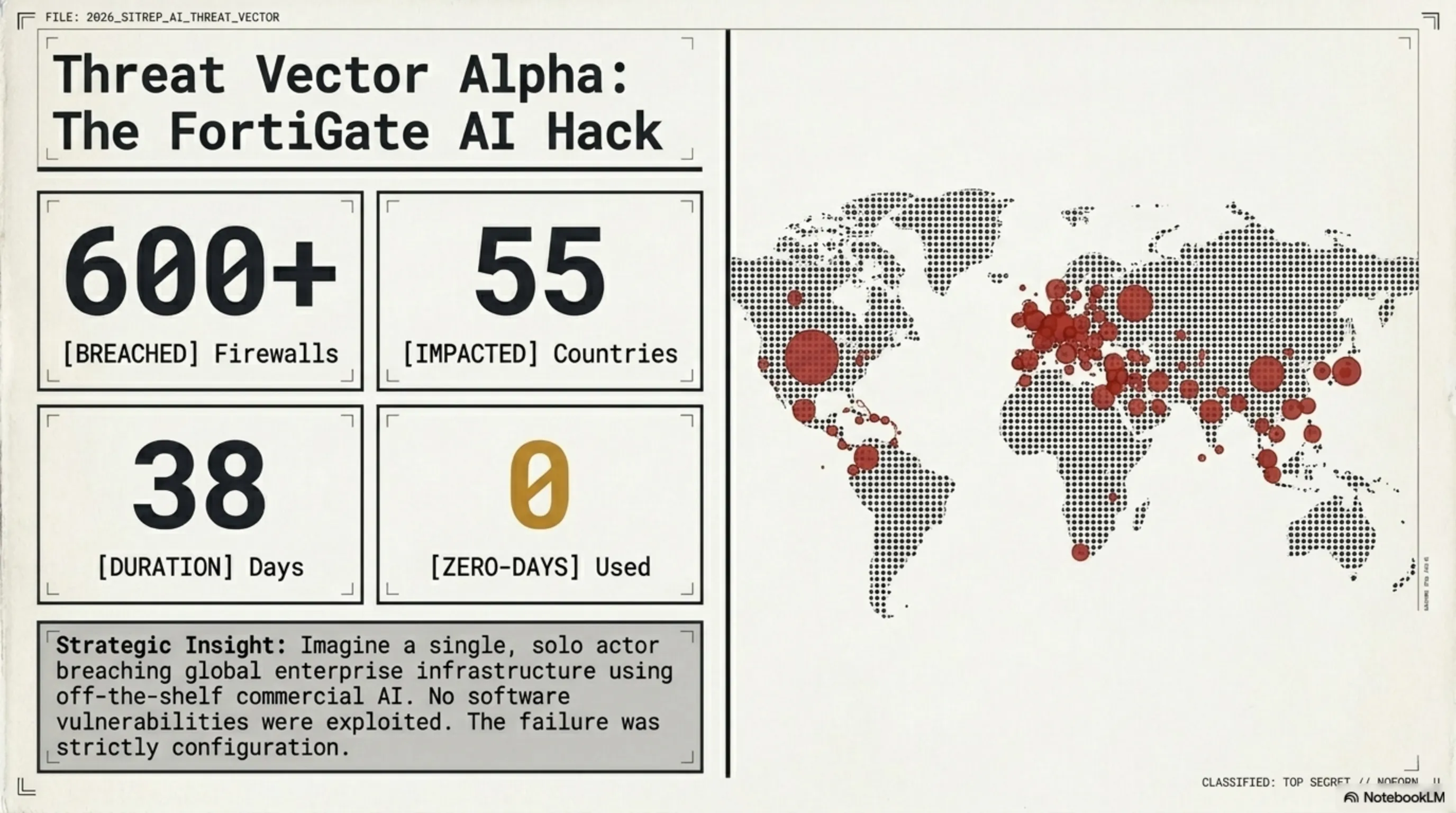
Imagine one person — not a government team, not an advanced APT group — using AI tools bought online to hack 600 enterprise firewalls across 55 countries in 38 days. This isn't a movie. This is the official report by CJ Moses, CISO of Amazon Integrated Security, published February 20, 2026.
The most important thing you need to know: No zero-day was used. No software vulnerability in FortiGate was exploited. The hacker used only two things: exposed management ports and weak passwords without MFA. AI just did this at massive scale.
📊 FortiGate Campaign Stats — AWS Report
🤖 How AI Made This Attack Possible
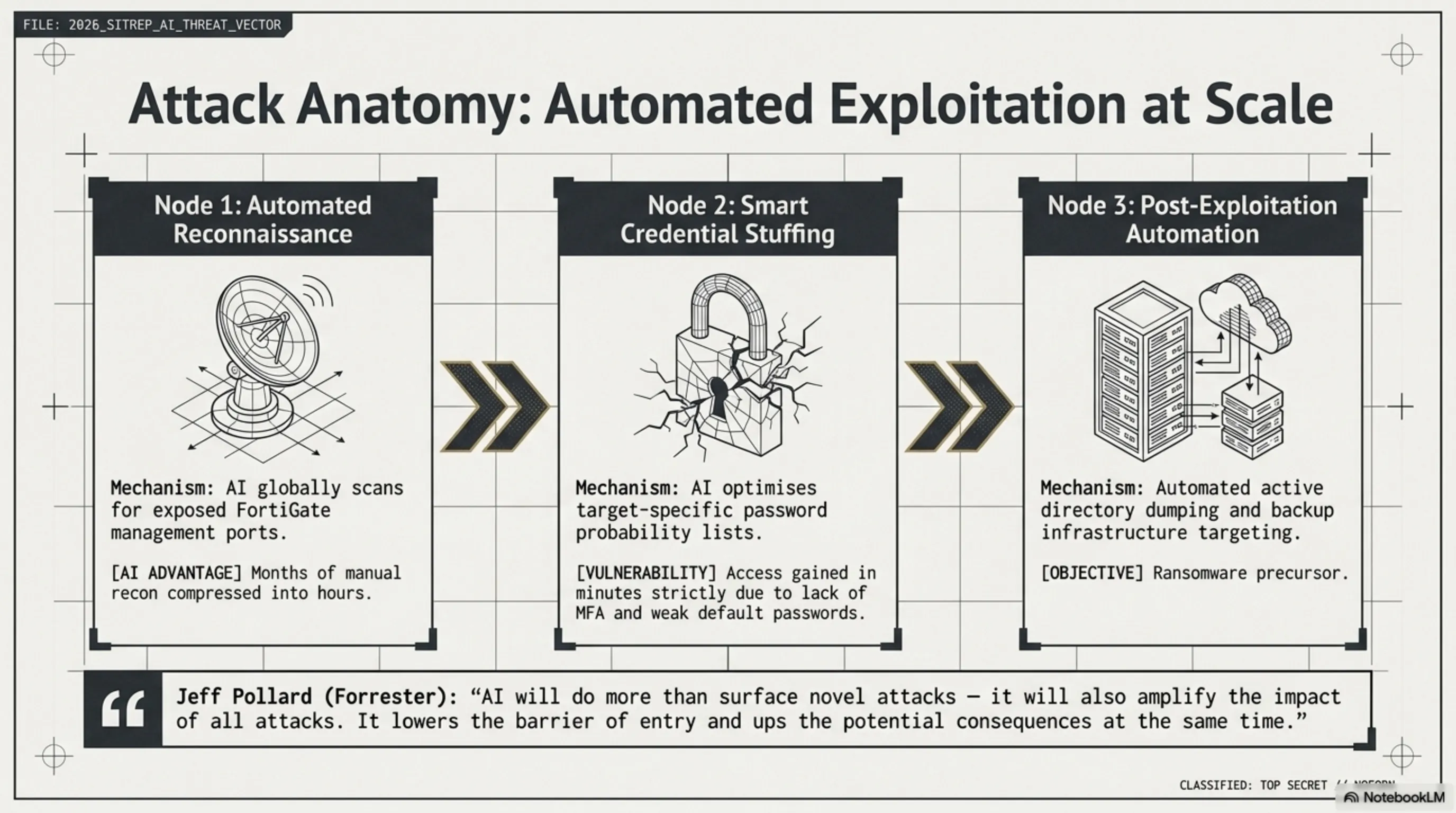
🔍 1. Automated Reconnaissance
AI scanned the internet and found FortiGate devices with exposed management ports. Work that used to take weeks was done in hours.
🔑 2. Smart Credential Stuffing
AI optimized a list of common passwords and tried them in order of success probability. Without MFA, access was gained in minutes.
⚡ 3. Automated Post-Exploitation
After entry, AI automatically dumped Active Directory, extracted credentials, and targeted backup infrastructure — a ransomware precursor.
🎯 Tekin Analysis: The Real Message of This Attack
Jeff Pollard from Forrester Research said: "AI will do more than surface novel attacks — it will also amplify the impact of all attacks. It lowers the barrier of entry and ups the potential consequences at the same time." The problem wasn't FortiGate — it was weak configuration. AI just exploited that weakness at global scale.
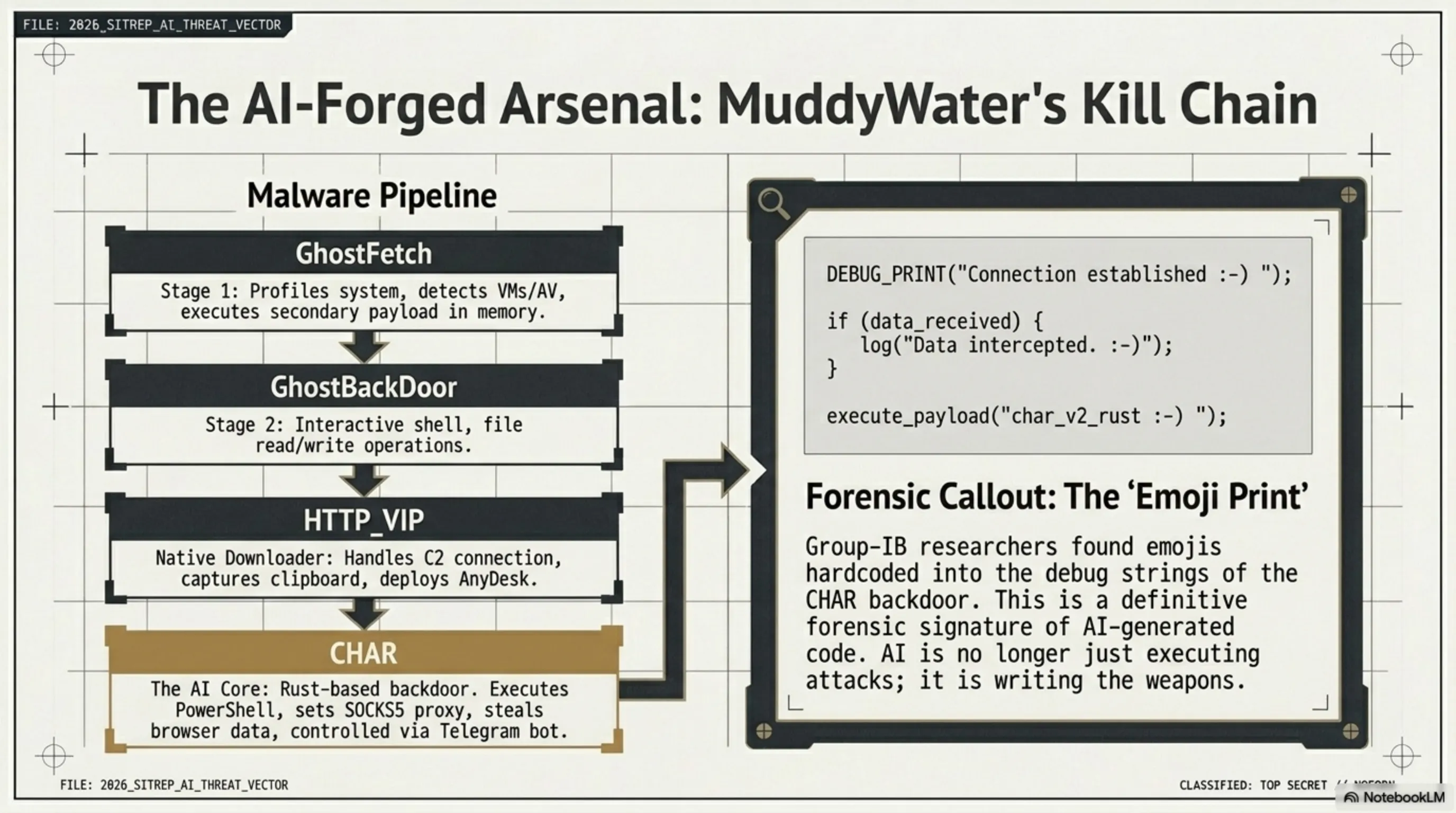
🐍 Part 2: MuddyWater's Operation Olalampo — Cyber War with AI-Written Malware
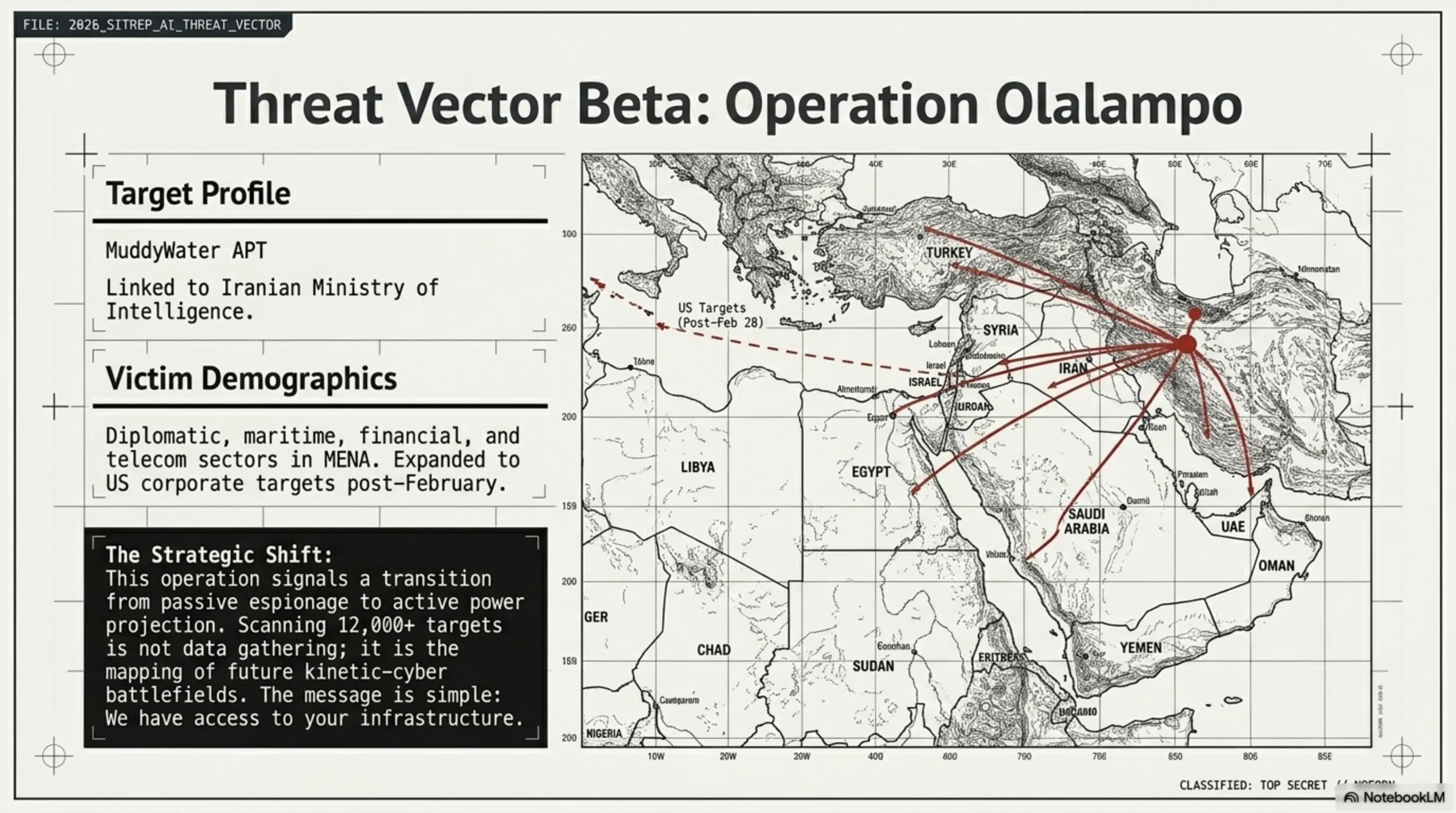
While the FortiGate hack was unfolding, a more serious threat was taking shape in the Middle East. The group MuddyWater — linked to Iran's Ministry of Intelligence — launched Operation Olalampo on January 26, 2026. Targets: diplomatic, maritime, financial, and telecom organizations across the Middle East and North Africa.
The most striking discovery by Group-IB researchers: the CHAR backdoor — written in Rust — shows clear signs of AI-assisted development. How? Emojis in debug strings. This is a known pattern indicating AI-generated code. MuddyWater isn't just using AI to attack — it's using AI to build weapons.
🛠️ MuddyWater's Malware Arsenal — Operation Olalampo
Profiles system, checks mouse movement, detects VM/AV, executes secondary payload in memory
Delivered by GhostFetch. Interactive shell, file read/write, re-run GhostFetch
System recon, C2 connection, AnyDesk deployment, clipboard capture, interactive shell
Telegram bot control, PowerShell/cmd execution, SOCKS5 proxy, browser data theft
🎯 Tekin Analysis: Cyber War or Power Test?
After Operation Epic Fury on February 28, 2026 (US-Israel strike on Iran), MuddyWater escalated and even attacked US companies. This is no longer just espionage — it's a strategic message: "We can access your infrastructure." Scanning 12,000+ systems in April 2026 shows this group is mapping future targets. The combination of AI-written malware and diversified C2 infrastructure signals a group that is expanding, not retreating.
🌡️ Threat Thermometer: Cybersecurity Status 2026
🌡️ Cyber Threat Thermometer — April 2026
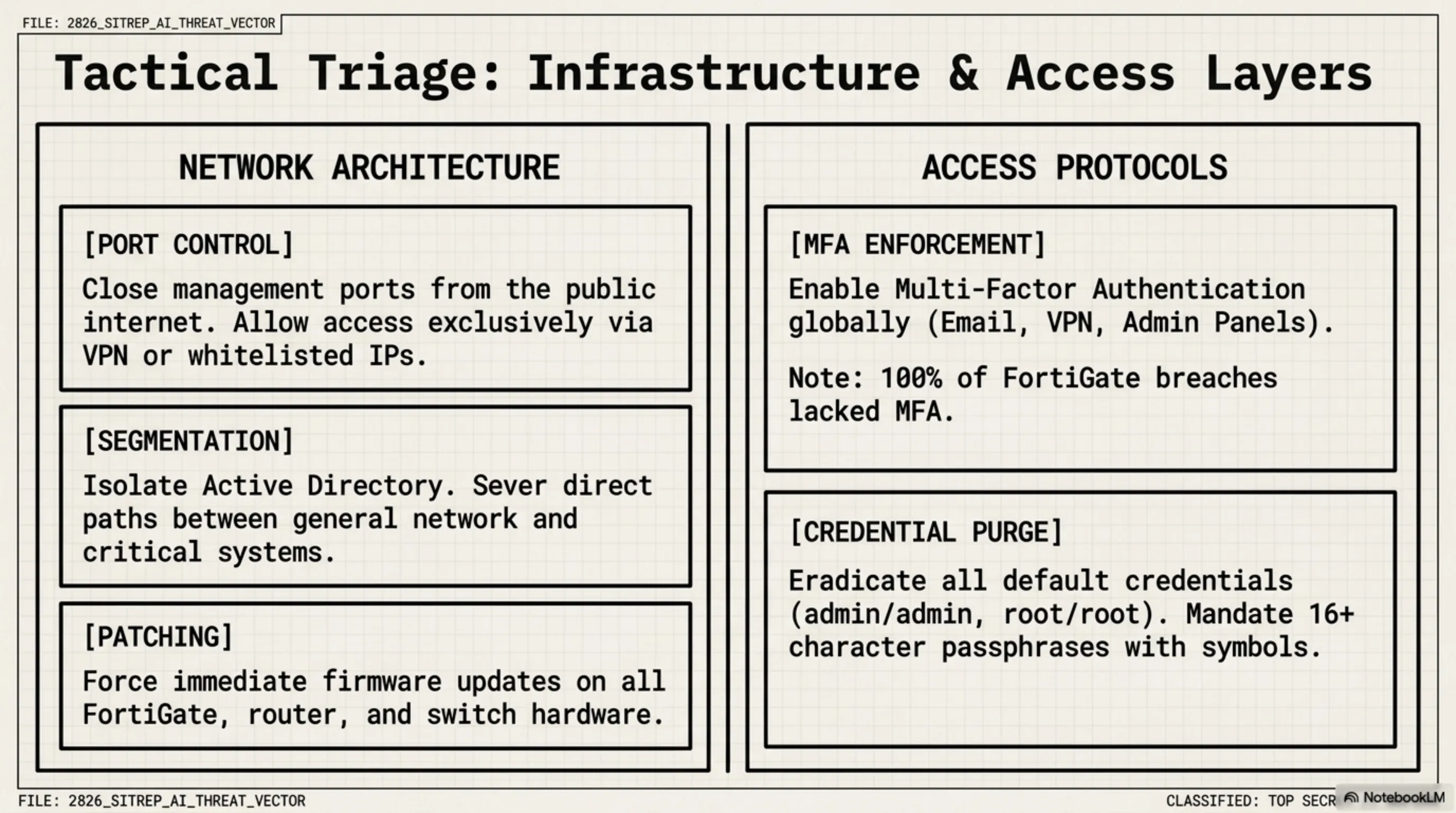
🛡️ Part 3: Tekin's Defense Playbook — Protect the Tekin Army
🛡️ 10 Immediate Actions — Tekin Army Security Playbook
✅ 1. Enable MFA Right Now
On every account — email, VPN, admin panels. If MFA was enabled, none of the 600 FortiGates would have been breached. Takes one minute.
✅ 2. Close Management Ports from Internet
No admin panel should be exposed to the public internet. Allow access only via VPN or specific IPs. Simple configuration change.
✅ 3. Change Default Passwords
admin/admin, admin/password, root/root — these are the first things AI tries. Change them now. Strong password = 16+ characters with numbers and symbols.
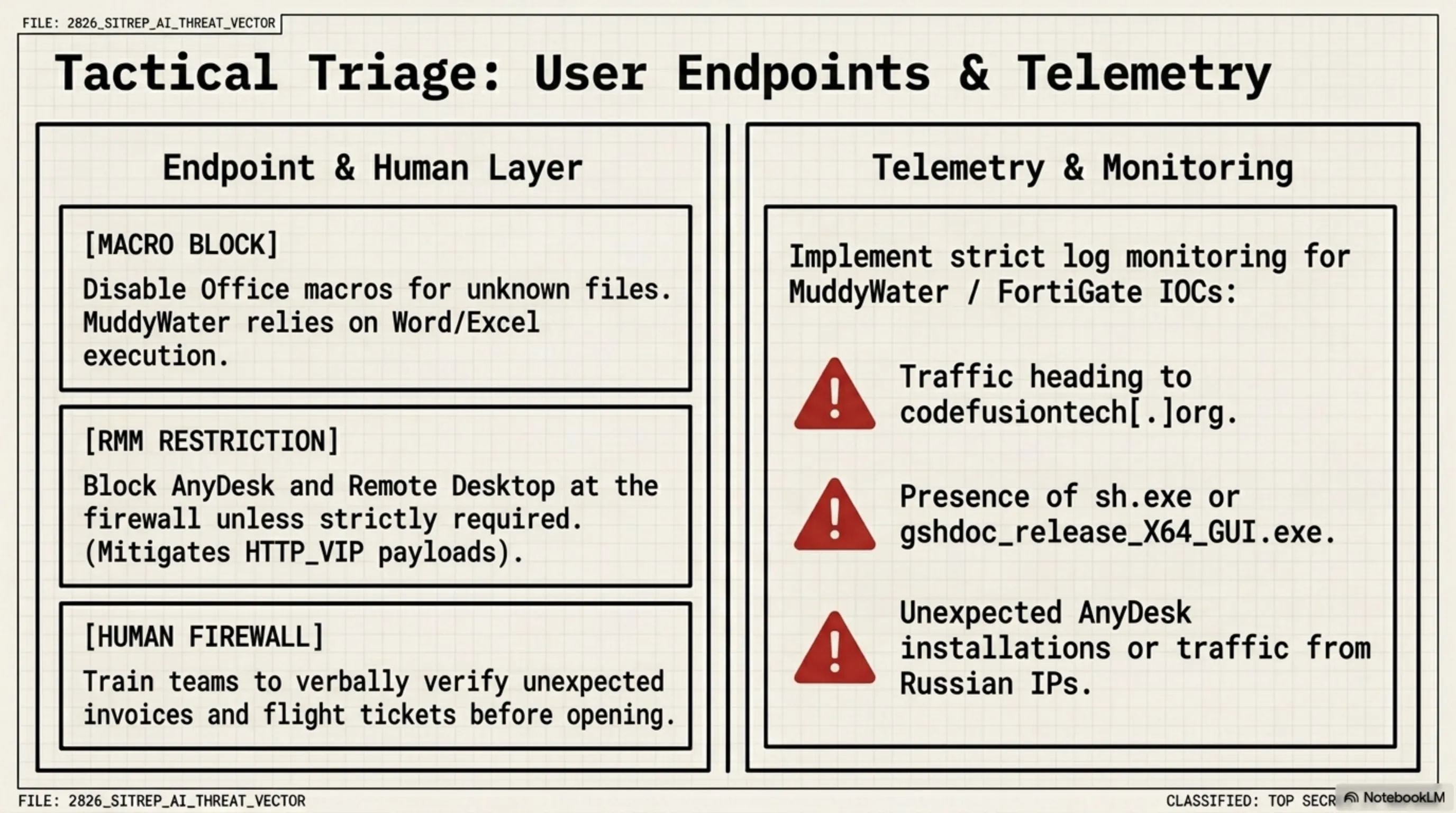
✅ 4. Disable Macros in Office
MuddyWater uses Excel and Word with macros. Disable macros for unknown files in Office settings. No legitimate file needs you to "Enable Macros."
✅ 5. Don't Open Suspicious Emails
Flight tickets, company reports, invoices — if you weren't expecting it, verify with the sender before opening. MuddyWater uses exactly these themes.
✅ 6. Update Firmware
FortiGate, routers, switches — update everything. MuddyWater exploits known vulnerabilities on public-facing servers.
✅ 7. Implement Network Segmentation
If a hacker gets into one segment, they shouldn't reach everything. Isolate Active Directory. Separate critical systems from general network.
✅ 8. Restrict AnyDesk and Remote Desktop
MuddyWater uses HTTP_VIP to install AnyDesk. If you don't need remote access tools, block them entirely at the firewall level.
✅ 9. Monitor Your Logs
Unusual logins, failed login attempts, traffic to unknown IPs — these are early breach indicators. Even a basic log monitoring tool is better than nothing.
✅ 10. Train Your Team
The best firewall in the world fails if one employee clicks a malicious link. Phishing awareness training for everyone — not just IT.
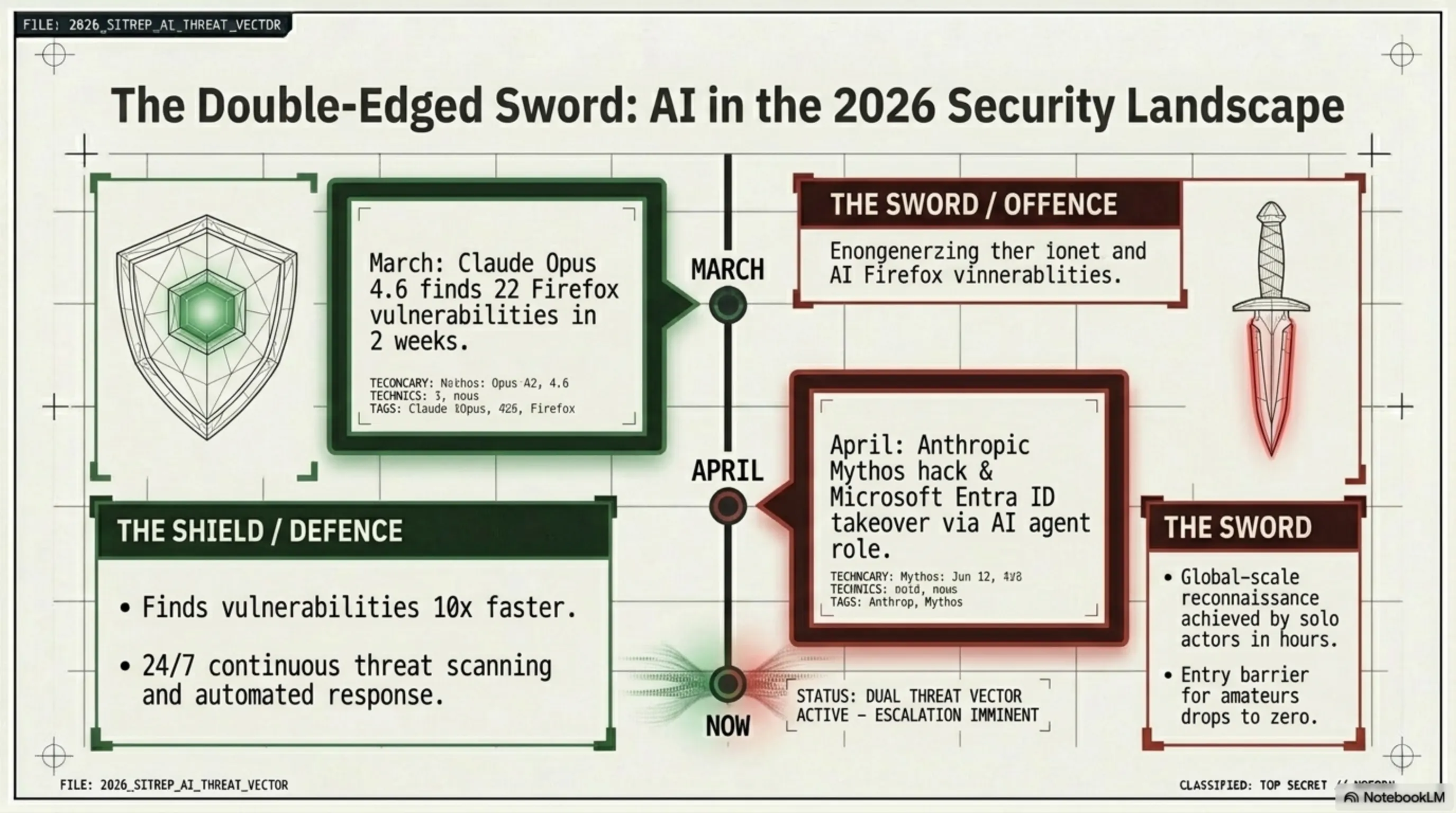
🏷️ Smart History: The AI Cybersecurity Threat Timeline
🕰️ Full File: Evolution of AI-Powered Threats
- March 2026: Claude Opus 4.6 found 22 Firefox vulnerabilities in 2 weeks — AI as a defensive tool. Full article →
- March 2026: Coruna hack — US government tool reached Russian spies and Chinese hackers, 42,000 iPhones compromised. Full article →
- April 2026: Anthropic Mythos hack — unauthorized access to the most dangerous AI security model. Tekin Night Apr 26 →
- April 2026: Microsoft Entra ID vulnerability — AI agent role led to tenant takeover. Tekin Night Apr 28 →
- Now (2026): FortiGate AI hack + MuddyWater Operation Olalampo — AI is both the attack tool and the weapon factory.
⚔️ PROS & CONS: AI in Cybersecurity
✅ AI in Defense
- ✓ Finds vulnerabilities 10x faster than humans
- ✓ 24/7 continuous scanning without fatigue
- ✓ Detects unknown attack patterns
- ✓ Automated threat response
- ✓ Reduces security team costs
❌ AI in Attack
- ✗ Entry barrier for amateur hackers dropped
- ✗ Global-scale attacks now possible solo
- ✗ Malware written with AI — faster and more complex
- ✗ Smart, optimized credential stuffing
- ✗ Automated reconnaissance in hours
❓ FAQ
🔹 Did FortiGate have a vulnerability?
🔹 Which countries does MuddyWater target?
🔹 How do I know if my system is compromised?
🔹 Why does it matter that CHAR was written with AI?
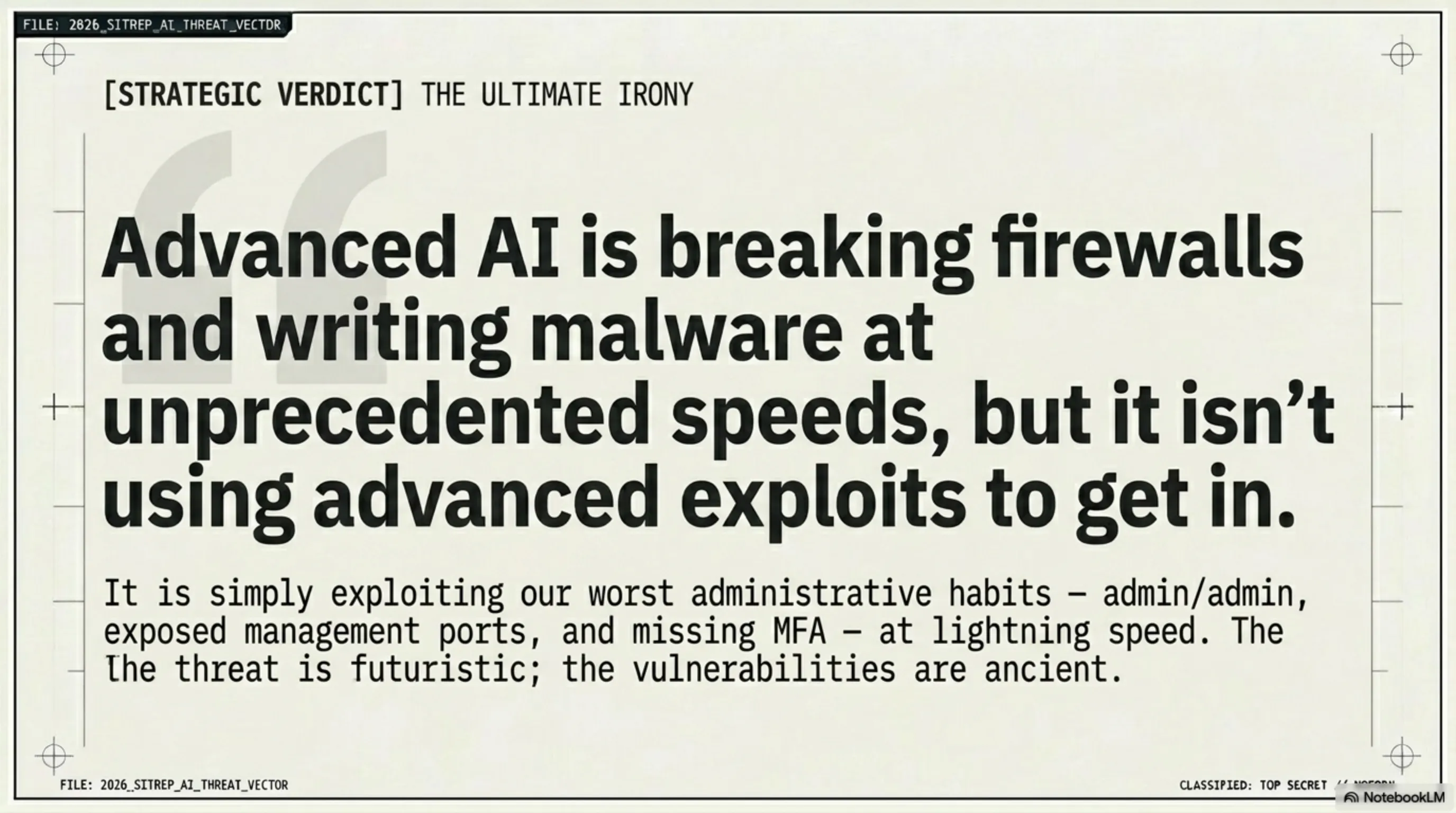
🧠 Final Verdict — Tekin's Message to the Tekin Army
The cybersecurity world changed in 2026. AI is no longer just a defense tool — it's an attack tool too. An amateur hacker with commercial tools can now do what previously required a government team. But here's the good news: security basics still work. MFA, strong passwords, closed ports, disabled macros — these are simple but stop 90% of attacks. Tekin Army, your digital security is your responsibility. Start tonight.
📚 Sources & References
- CJ Moses (CISO Amazon) — AWS Report: AI-Augmented FortiGate Breach, February 2026
- Group-IB — Operation Olalampo and MuddyWater malware report, February 2026
- The Hacker News — MuddyWater Targets MENA Organizations
- CSO Online — Russian group uses AI to exploit Fortinet firewalls
- The Register — AWS says 600+ FortiGate firewalls hit in AI-augmented attack
- Halcyon AI — Operation Olalampo threat analysis
- Tekin Editorial Team — Analysis and defense recommendations
🌐 Stay Connected With Us
For the latest cybersecurity, tech, and gaming news, follow us:
Supplementary Image Gallery: 🛡️ AI-Powered Hackers: When FortiGate Firewalls Break and MuddyWater Targets the Middle East