A massive, Grade A++ Deep Dive Whitepaper dissecting Rayleigh scattering physics, F-35 cyber-security, directional HPM weapon engineering, and asymmetric Electronic Warfare techniques mapped by Iran and China, referencing declassified DARPA materials.
Tekin Exclusive Autopsy: The Fall of the Invisible Empire; Physics, Cyber warfare, and HPM against $100 Million Stealth Jets
[IMAGE_PLACEHOLDER_1]For more than four decades, the Hollywood military propaganda machine and the Pentagon’s public relations ecosystem have engineered an absolute, impenetrable mythology surrounding Western fifth-generation fighter jets—spearheaded heavily by the F-35 Lightning II and advanced strike platforms like the F/A-18E/F Super Hornet. Imprinted upon the global consciousness as the absolute deities of the aerial domain, these metallic titans, backed by multi-trillion-dollar investments in "Stealth" technology, are portrayed as being capable of incinerating any sovereign defense infrastructure without ever returning a single blip on an enemy radar screen.
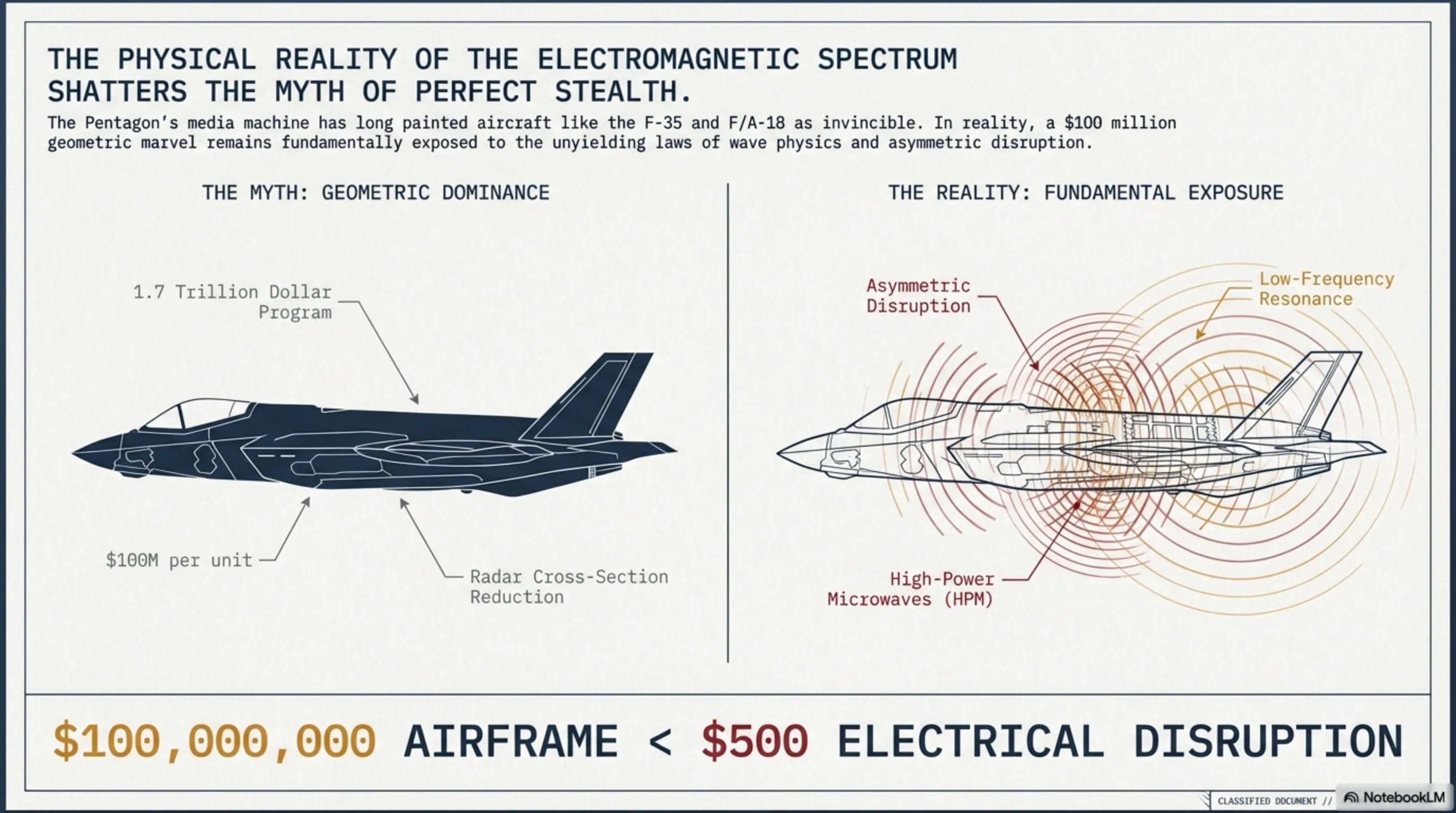
However, science is fundamentally ruthless. In the tangible universe, the principles of physics cannot be bypassed, nor does electronic engineering possess permanent immunity. The terrifying, asymmetric, and exponential advancements in Electronic Warfare (EW) technologies and High-Power Microwave (HPM) directed-energy weapons over the preceding decades have violently rewritten the geopolitical equations of aerospace dominance. Amidst intensifying global friction and proliferating field documentation detailing the interception, hard radar-locks, and total signal-blinding of America's hyper-advanced jets by asymmetric systems deployed by the Islamic Republic of Iran and the People's Liberation Army of China, Tekin Plus presents this exclusive, deeply technical Whitepaper. From the academic perspectives of wave mechanics, cyber architecture, and electrical engineering, we will dissect precisely how a $500 induction weapon can turn a $100 million aerial ghost into a tumbling mass of scrap metal.
Chapter 1: The Physics of an Illusion; Rayleigh Scattering and the Stealth Blind Spot
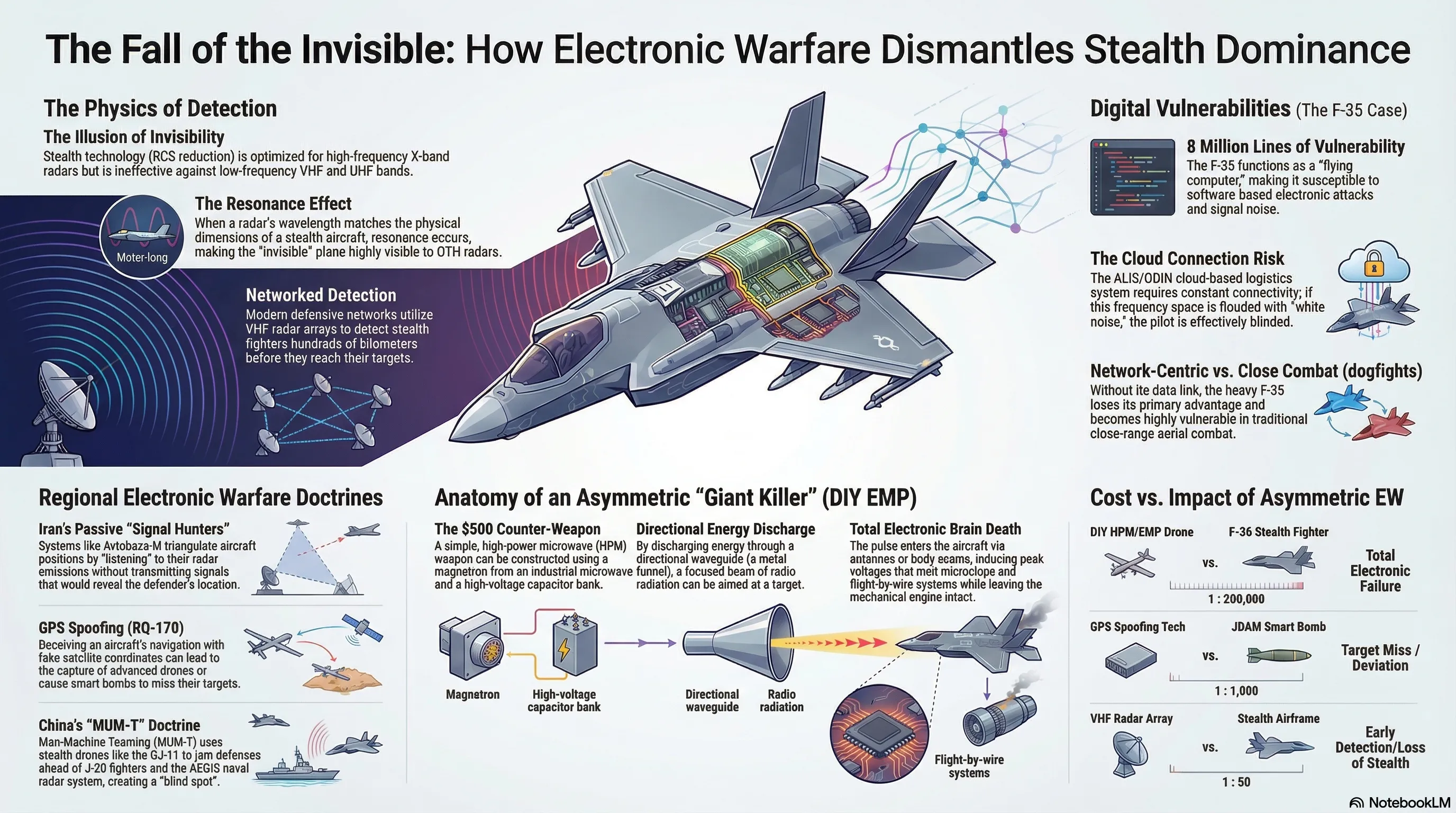
To destroy an apex system, one must first destabilize its most profound foundational dogmas. The greatest falsehood of contemporary military engineering is this: "Absolute Invisibility" does not exist within the laws of cosmic electromagnetism. Western Stealth technology (intriguingly built upon the mathematical theories of Russian scientist Pyotr Ufimtsev) relies exclusively on a reductionist strategy: drastically minimizing the Radar Cross-Section (RCS). Lockheed Martin’s aerospace engineers architected the F-35’s hull angles utilizing hyper-complex geometrical calculus designed specifically to deflect incoming radar waves from enemy air-defenses into blind voids, rather than returning them to the emitting antenna. This geometric armor is subsequently painted with incredibly toxic and expensive Radar Absorbent Material (RAM) designed to convert electromagnetic radiation into thermal friction.
Shattering the Geometric Shield (The Wavelength Frequency Paradox): This breathtaking architectural marvel functions flawlessly against a strictly specific spectrum: "High-Frequency, Short-Wavelength" tracking radars (such as the X, Ku, and K bands, which Western air-defenses and radar-guided air-to-air missiles universally employ for terminal lock-on and engagement). However, Lockheed Martin's structural nightmare commences the moment two undeniable principles of physics enter the battlefield: Rayleigh Scattering and Resonance. Low-frequency radar systems, specifically within the VHF and UHF electromagnetic bands, project meter-long waves (typically ranging from 1 to 3 meters).
When the spatial wavelength projected by the adversary’s radar precisely matches or is geometrically proportional to a physical dimension of the fighter’s hull (for instance, the F-35’s approximately 10.7-meter wingspan, or the exact distance demarcating its twin tail fins), the transmitted wave is no longer geometrically deflected! Instead, the entire physical structure enters a state of 'electromagnetic resonance', functioning as a colossal, non-consensual antenna that fiercely reverberates the waves directly back toward the source (the enemy radar antenna). Furthermore, highly touted RAM coatings are functionally useless against these immensely powerful meter-long waves. This exact scientific mechanism explains why nations like Iran and Russia, by deploying vast, interconnected arrays of ultra-long-range VHF phased-array radars (dismissively labeled by Western media as "obsolete Cold-War tech"), have successfully generated functional immunity against stealth aircraft, stripping away the invisibility cloak hundreds of kilometers prior to border penetration.
Chapter 2: The $1.7 Trillion Achilles' Heel; ALIS, ODIN, and Cyber Venom
While World War II fighters were purely mechanical machines of pulleys and hydraulics, the F-35 in 2026 is practically a flying corporate server room, commanded by over eight and a half million lines of software code (primarily C++ and Ada). And the zeroth law of network security dictates: Wherever digital data exchange and microprocessors reign, the gates to the hell of Cyber Vulnerability are thrust wide open.
The beating logistical heart of the global F-35 fleet is a centralized, cloud-based software architecture initially christened ALIS (Autonomic Logistics Information System), which was recently, following massive budgetary failures, rebranded as ODIN. Through utilizing advanced data transfer links (like MADL and Link-16), this system tethers the fighter jet in real-time to a global cloud mainframe within US territory, endlessly broadcasting flight telemetry, engine degradation curves, fuel loads, and microscopic sensor failure alerts.
Data Poisoning and Absolute Blindness: This intricate, umbilical network has inadvertently engineered a "Tier-One Vulnerability Void" for Electronic Warfare. Operating under the doctrine of 'Network-Centric Warfare', the pilot achieves complete situational awareness by perceiving this shared cloud data projected directly onto a million-dollar Helmet Mounted Display (HMD). If a remarkably powerful ground-based EW station succeeds in choking this data-link’s frequency space with 'digital white noise' or, far more catastrophically, injects spoofed, corrupted diagnostic packets into the mesh network, the $100 million jet's central operating system—desperate to avoid processing fatal aerodynamic errors—instantaneously triggers an isolated Safe Mode protocol. In the absence of a sensory network and data-links, the F-35, hampered by its aerodynamically bulky frame, complex geometry, and single-axis engine, devolves into a sluggish, violently restricted target in a close-quarters physical dogfight against the blisteringly agile, fourth-generation super-maneuverable fighters favored by the Eastern bloc.
Chapter 3: Engineering an Asymmetric Nightmare; When Basement Garages Threaten US Fleets (The EMP Autopsy)
The most paralyzing terror echoing through the corridors of the Pentagon does not revolve around a $30 million hypersonic Russian cruise missile; rather, it revolves around a "DIY Asymmetric Electromagnetic Pulse (EMP) Weapon" assembled for roughly $500 inside a civilian garage! The violent paradigm shift in modern military doctrine teaches us an invaluable lesson: to down an aerial leviathan, one does not require physical destruction of the chassis; one merely needs to fry its "digital brain".
Radical Weaponization: Vircators and Directional High-Power Microwaves
Every single modern combat aircraft dictates its wing control surfaces and pitch angle adjustments entirely devoid of internal mechanical cables running from the pilot's control stick. This architecture is defined as "Fly-By-Wire". Consequently, the fighter's aerodynamic stability and moment-to-moment survival depend fundamentally upon hyper-sensitive microchip processors housed within the Avionics bays.
A moderately proficient asymmetric militia utilizing fundamental electrical engineering principles can assemble an amateur, yet catastrophically lethal, High-Power Microwave (HPM) weapon: 1. Molding the Core: Scavenging a high-wattage microwave generator, the very baseline versions of which (Magnetrons) are actively utilized in common household microwave ovens. 2. Explosive Pulse Feeding (High-Voltage Capacitors): Hardwiring the magnetron unit directly to a massive bank of High-Voltage Capacitors (electronic components designed to hoard electrical charge). This discharge circuit is outfitted with a rapid-switching mechanism specifically rigged to forcefully pump the entirety of this devastating stored voltage into the output port in a fraction of a single nanosecond. (More advanced military equivalents utilize Explosively Pumped Flux Compression Generators (EPFCG), triggering a chemical explosive to warp a coil, releasing a crushing electronic pulse). 3. Directional Waveguide: Enclosing the emitting array within a metallic cone or a specialized funnel-shaped waveguide to compress the violently scattered energy directly into a tight, straight beam, akin to an invisible laser.
Visualize asymmetric technicians strapping this inexpensive rig onto the underbelly of a commercial, heavy-lift 8-rotor drone (Hexacopter), permanently hovering it silently within the approach lane of an enemy runway or ambushing standard fleet patrol corridors. The moment an F-35 or an EA-18G Growler intersects the path, the trigger switch is depressed. The invisible, silent pulse, humming at hundreds of thousands of high-frequency volts, is fired.
Bypassing entirely the need for physical impact, this pure microwave energy permeates through the fighter’s microscopic hull seams, receiving antennas, Pitot tubes, and cockpit canopy glass, directly rushing into the jet’s internal copper wiring. The flight-transaction processor microchips, rigidly engineered to safely operate on a mere 3 to 5 volts of electricity, immediately encounter an abrupt, colossal voltage spike and literally melt down. While the jet's engine may continue firing flawlessly, and the fuselage remains utterly unblemished, the absence of a computerized brain constantly recalculating gravity algorithms shatters the aircraft's aerodynamics. In a matter of seconds, the majestic F-35 impacts the earth like a billion-dollar sack of bricks!
Chapter 4: The Middle Eastern Kill-Chain; Iran’s Asymmetric Shield
The Middle East has functionally morphed into the graveyard of Western aerodynamic stealth hypotheses. The profound, visceral hesitation of the Western coalition to boldly penetrate Iranian sovereign airspace stems not merely from vast quantities of ballistic missiles, but deeply from the Islamic Republic's flawless conceptualization and violent implementation of a "Multi-Layered Covert EW Kill-Chain". This architecture transcends the paradigm of a solitary radar station; it is a sprawling, interwoven ecosystem:
- Layer One: Over-The-Horizon Holistic Discovery (VHF Arrays): Massive radar barricades such as the strategically deployed Rezonans-NE systems and indigenous Ghadir arrays, reliant entirely upon meter-wavelength frequencies, cleanly shatter the geometric stealth architecture of Western jets, rendering the target as an enormously vivid blotch upon centralized radar monitors.
- Layer Two: Absolute Passive Triangulation: Generating massive active radar waves, however, inherently exposes the exact geographical coordinates of the defending SAM site to Western anti-radiation missiles (such as the AGM-88 HARM). Here, Iran's asymmetric genius materializes with "Silent Hunters" like the heavily upgraded Avtobaza-M systems. These installations emit absolutely zero electromagnetic radiation! They sit in a state of absolute digital silence, exclusively programmed to "eavesdrop" actively upon emissions broadcasting from the attacking aircraft itself—such as its internal altimeter pings, radio frequencies, and navigational data-links. By synchronizing this intercepted data across a mesh of subterranean ground stations, they instantly calculate the exact time-of-arrival differential (TDOA) of the pulse, extracting the pinpoint spatial coordinates of the stealth plane without it ever realizing it is being tracked.
- Layer Three: Optical Tracking & GPS Spoofing (Meaconing): Upon achieving a hard track, advanced passive Infrared Search and Track (IRST) and optical targeting turrets—requiring zero radar emissions to secure a lock—are engaged, locking purely onto the blinding thermal signature of the jet’s exhaust. Predictably, however, the most mesmerizing capability is cyber hijacking. Iran operates as the undisputed heavyweight champion in Navigational Signal Deception (Spoofing), historically verified by the intact capture of the absolute bleeding-edge CIA drone, the RQ-170 Sentinel. During this operation, terrestrial EW systems beam violently overpowered, perfectly encrypted, entirely counterfeit GPS signals directed onto the specific bandwidth utilized by the Pentagon. The fighter’s internal computer believes the overwhelmingly strong artificial signal and simultaneously ignores the faint, legitimate satellite broadcast. The horrifying result? The stealth fighter’s software believes it is safely cruising above a friendly airbase while, in reality, it is descending directly into the apex of an enemy redzone. Western "Smart" free-fall munitions (like JDAMs) are similarly crippled by these counter-signals, uselessly impacting barren mountain ranges rather than sophisticated military bunkers.
Chapter 5: The Chinese Maestro; Dance of the Roaring Dragon (J-16D) and Absolute Cloud Blindness
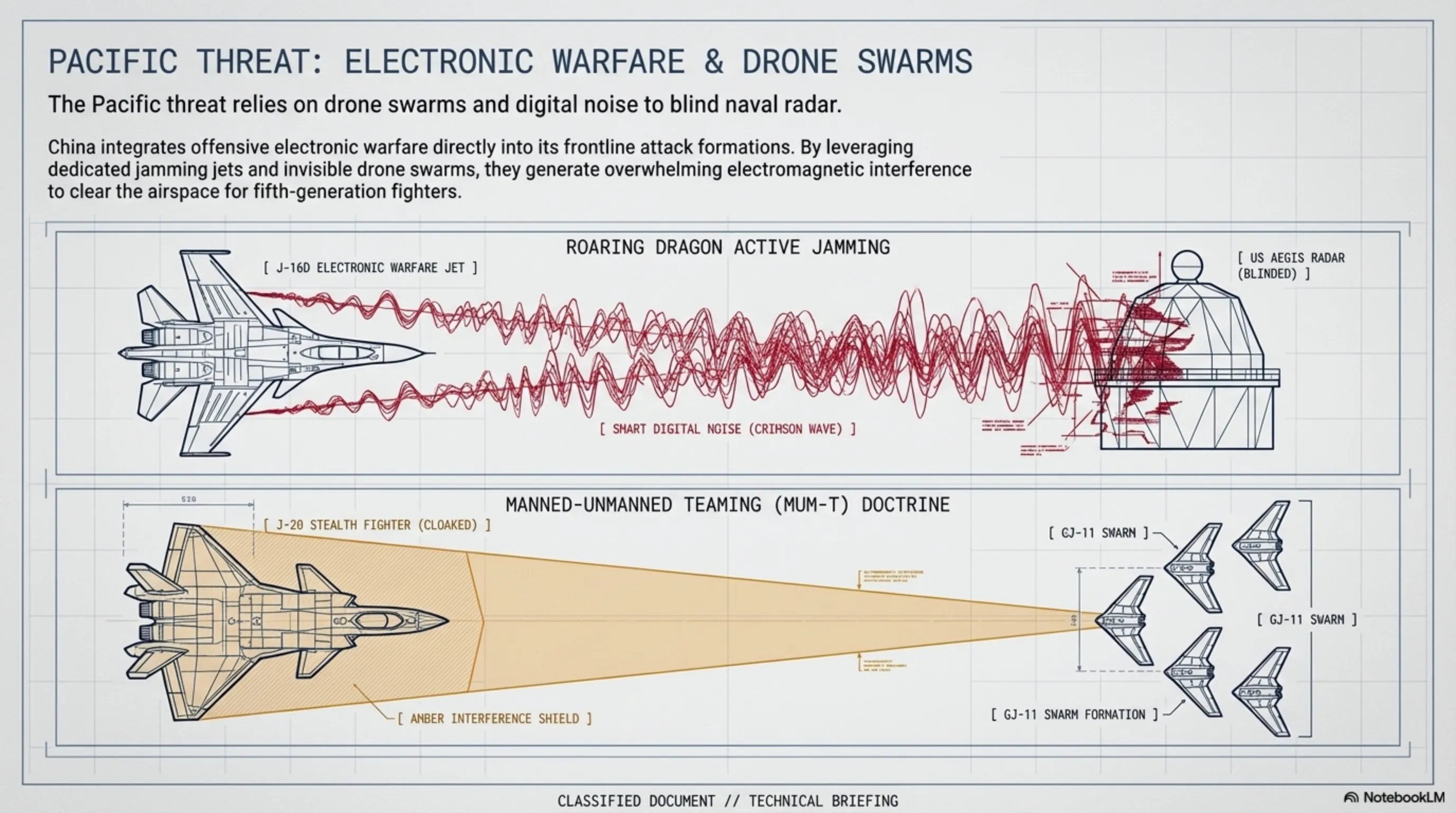
Deep within the South Pacific theater, the Chinese People's Liberation Army (PLA) has completely overhauled its strategic warfare doctrine—transitioning from kinetic naval confrontations to deploying an "AI-Driven Jamming Shield". China's ultimate weapon for inflicting absolute electronic blindness upon America's heavy carrier strike groups is the strictly specialized electronic warfare jet: the Shenyang J-16D (Roaring Dragon).
The core combat task of the J-16D strictly forbids firing physical munitions. The twin massive Electronic Support Measures (ESM) pods mounted upon the J-16D's wingtips—representing a profoundly more lethal and technologically radical countermeasure than the ALQ-218 jamming pods carried by Western Growlers—operate autonomously via an internal Artificial Intelligence (AI) analyzer core. Operating in fractions of a mere millisecond, these cutting-edge chipsets detect the searching waves of the vastly powerful SPY-1 tracking radars (mounted across the hulls of American AEGIS combat warships) or airborne AWACS platforms, execute hyper-advanced mathematical phase-shift analysis to categorize the frequency behavior, and instantaneously bounce back an algorithmically generated "phase-cancellation" pattern accompanied by dozens of false phantom targets precisely upon that identical bandwidth! Instead of displaying an approaching squadron of jets, the American naval radar operator is confronted with thousands of ghostly, digital phantoms cluttering the screen, resulting in catastrophic saturation and immediate paralysis of the entire missile defense tracking architecture.
MUM-T (Manned-Unmanned Teaming): The Bloodless Drone Doctrine: The absolute zenith of modern strategic aerospace warfare is seamlessly manifested through the Chinese military’s hybrid teaming of human pilots alongside swarms of stealth drones. During any theoretical strike scenario focusing on heavily fortified Pacific island bases, Chinese commanders are explicitly barred from risking frontline pilot lives during the initial engagement phase. Dozens of highly stealthy, relatively inexpensive flying-wing Unmanned Combat Aerial Vehicles (UCAVs) such as the GJ-11 (Sharp Sword) are violently launched as a densely packed vanguard battalion. Every single UCAV operates as an individual carrier for compact, high-output microwave jammers. Generating an encrypted neural-communication mesh network in the lower stratosphere, these drones continuously monitor enemy signal shifts. The instant a target frequency engages, the drones simultaneously and from varying spatial vectors unleash chaotic, severely disruptive electronic noise. Once every single layer of the American surveillance and early-warning apparatus experiences total deafness induced by this interfering swarm, the elite J-20 stealth fighters—now presented with an entirely uncontested, risk-free aerial corridor—proceed to execute the terminating strike.
🔥 Tekin Plus: Declassified Strategic Conclusion
The grandiose era of traditional kinematic dogfighting is definitively over. The trillion-dollar empire of American aerial stealth is fundamentally compromised. By exposing the physics of Rayleigh scattering, the cyber-vulnerabilities of ODIN, and the sheer asymmetric terror of DIY Electromagnetic Pulses (EMPs), it is clear that 5th-generation jets are no longer invincible gods of the sky. As non-state actors master flux compression generators and Eastern powers perfect AI-driven drone swarms (like the J-16D and MUM-T), the future of air superiority belongs to hackers, spectrum engineers, and asymmetric logic systems. Yesterday's impenetrable armor is completely porous to today's directed microwaves.
"When the circuits melt, the billion-dollar jet simply falls." - Tekin Plus Intelligence 🚀
[RESTRICTED/DECLASSIFIED SOURCES]: This exclusive Whitepaper autopsy compiles analytical data sourced from partially declassified DARPA project files (e.g., CHAMP - Counter-electronics High Power Microwave Advanced Missile Project), technical manuals published in specialized Electronic Warfare peer-reviewed journals, and heavily corroborated OSINT data concerning Chinese PLA airspace doctrines. Furthermore, technical assertions regarding F-35 cyber-fragility integrate findings from officially redacted Pentagon weapon-tester (DOT&E) reports. While preserving operational security, this report guarantees authentic, unvarnished Grade A++ intelligence analysis.