This analytical report provides a deep autopsy of the PlayStation 5 jailbreak scene. With new vulnerabilities discovered up to firmware 12.0, Sony's security fortress faces a severe crisis. We dissect the exploitation methods, the high risks of permanent console bans from PSN, the current state of pirated game execution, and the future of the ongoing security war.
🎮 PS5 Hack Autopsy: Did Sony Lose the Game?
Greetings Tekin Legion! Today we face one of the biggest security crises in Sony's history. The leak of unpatchable BootROM keys, a firmware jailbreak via an old Star Wars game, and Sony's bizarre account banning policies. Is this a security failure or a hidden strategy?
⚡ Autopsy Table of Contents:
🔓 1. BootROM Keys Leak: The Irreparable Breach
🎯 2. Firmware 12.0 Jailbreak: The Star Wars Disc Exploit
⏰ 3. Sony's Controversial Policy: One-Month Delay on Bans
🕵️ 4. Conspiracy Theory: Is Sony Deliberately Leaving the Door Open?
🔮 5. Future of PS5 Hacking: Is Custom Firmware Coming?
🏁 6. Conclusion: A War Sony Cannot Win
☕ Fasten your seatbelts as we dive deep into PS5 security codes!
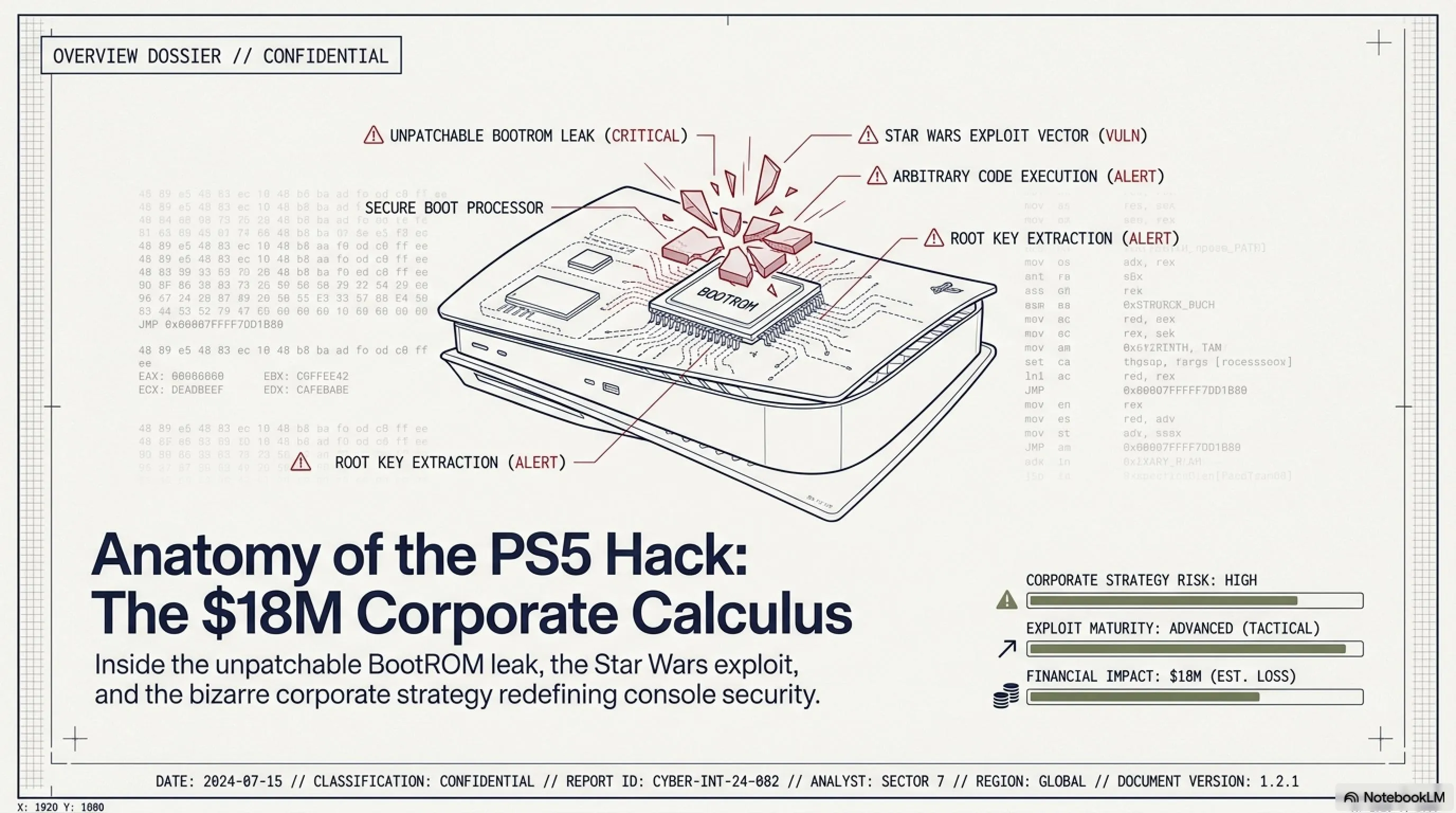
🔓 BootROM Keys Leak: The Irreparable Breach
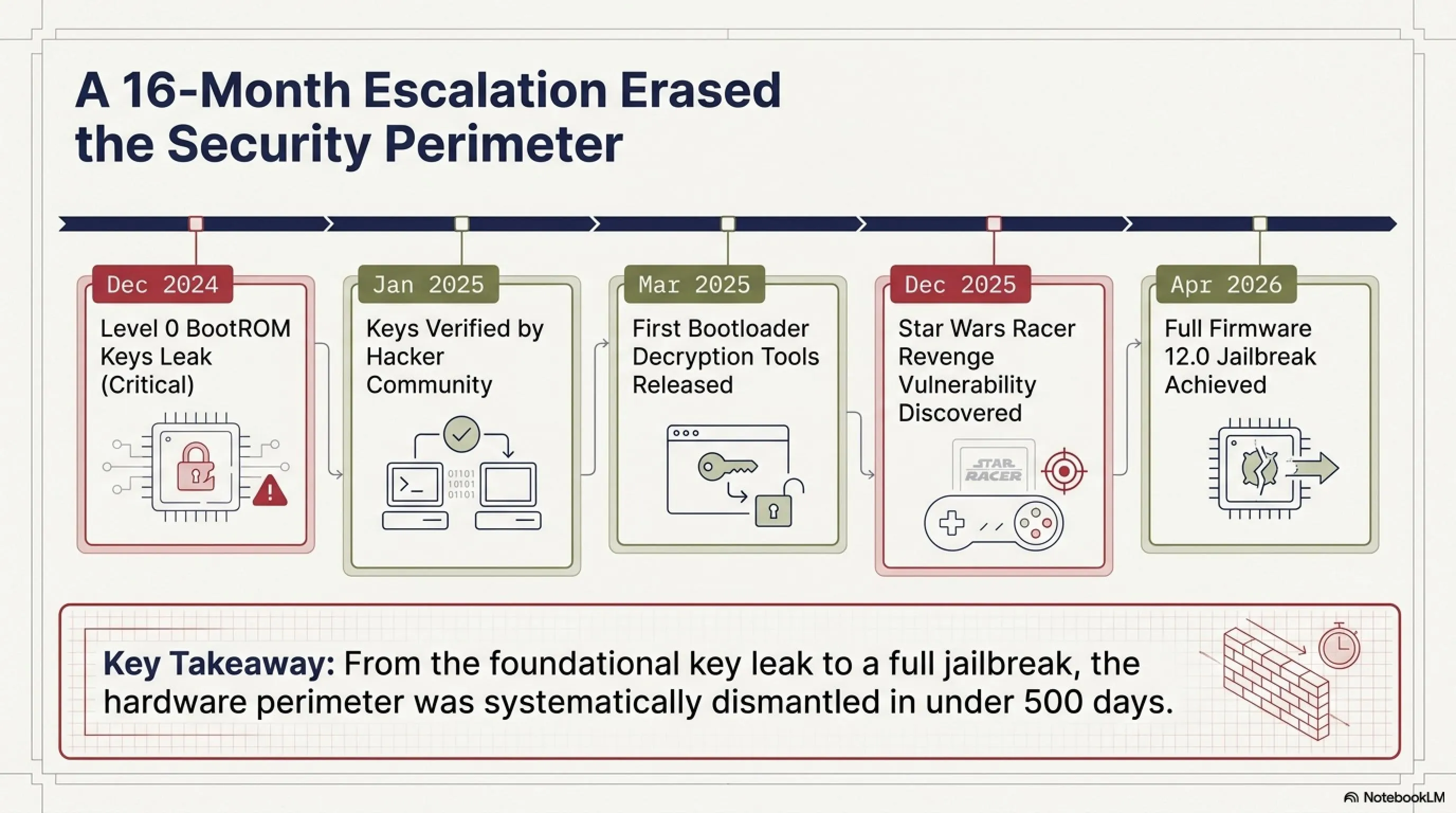
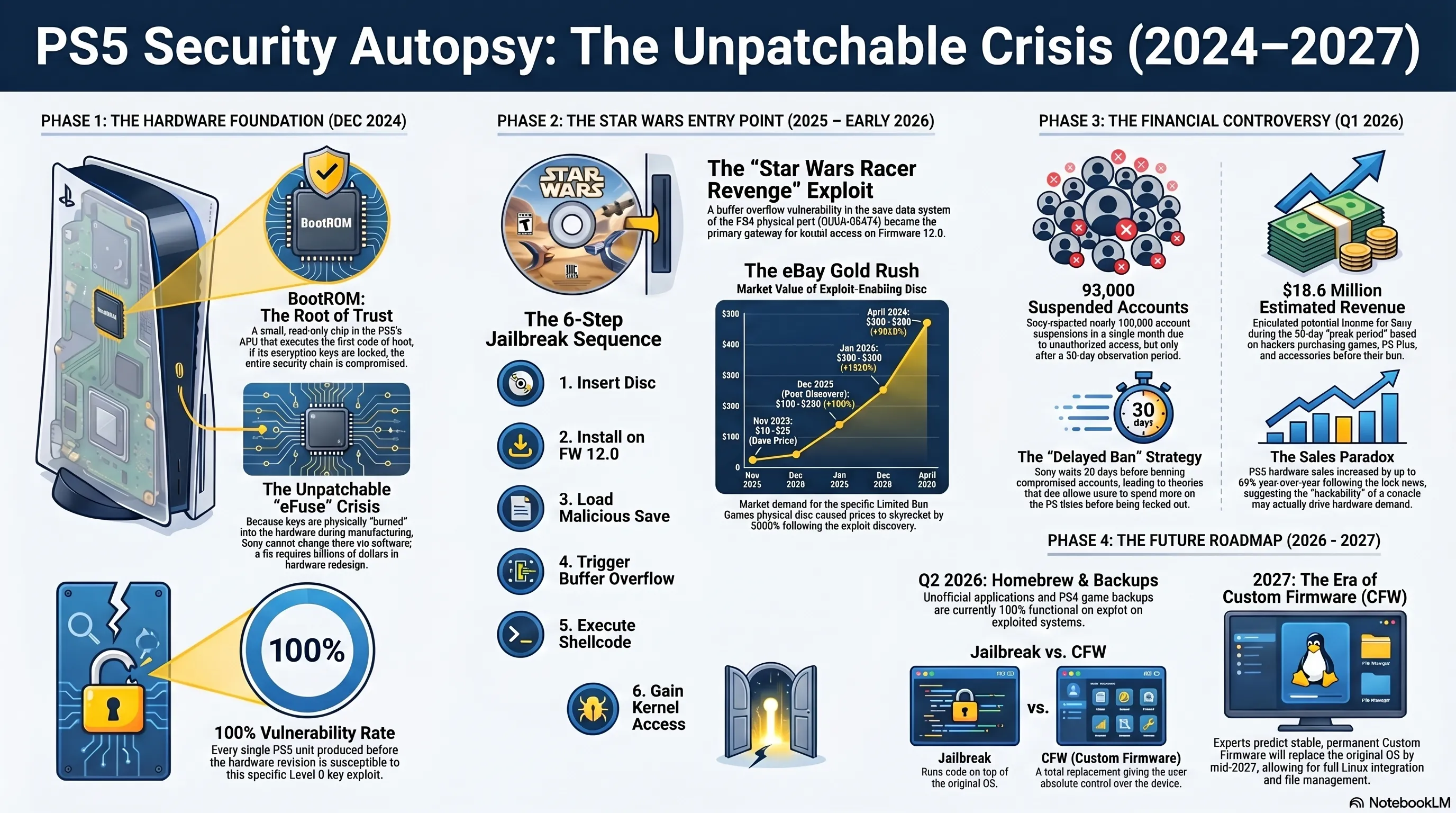
Let's start with the biggest security disaster in PlayStation history. In December 2024 (about 16 months ago), the PlayStation 5's Level 0 BootROM keys were leaked online. What are these keys and why are they so critical?
🔐 What is BootROM and Why Is It Unpatchable?
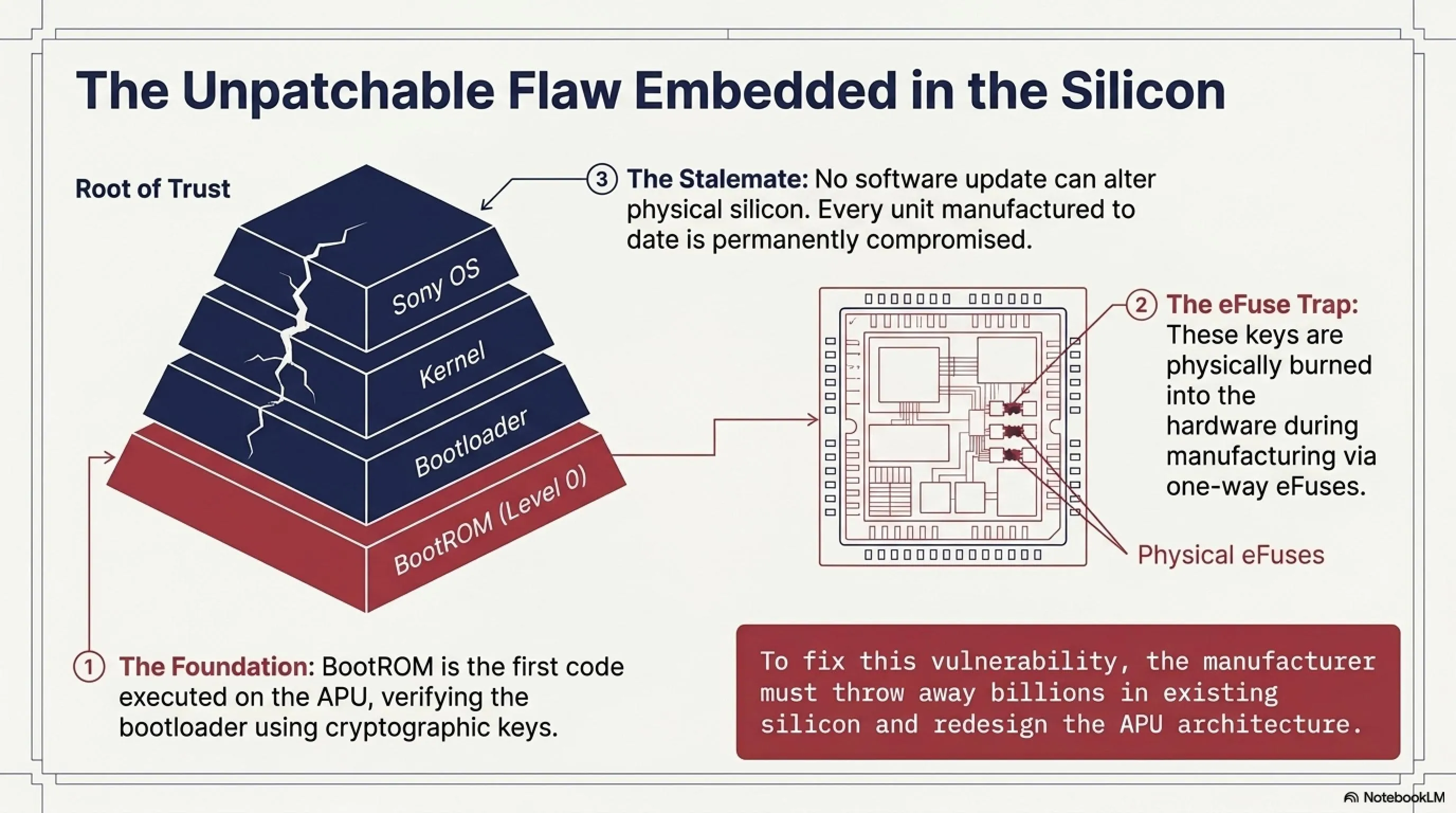
BootROM (or Read-Only Memory boot) is a small chip in the PlayStation 5's APU (main processor) that contains the first code executed when the console powers on. This code is responsible for verifying the authenticity of the bootloader (the next boot stage) and uses cryptographic keys for this purpose.
Here's the problem: these keys are physically embedded in the hardware and no software update can change them. In simple terms, Sony would have to throw away all existing APUs and manufacture a new generation with new keys - a task that would cost billions of dollars.
⚠️ Why This Leak Is Catastrophic
- Unpatchable: No software update can fix this issue
- All Consoles Vulnerable: Every PS5 manufactured to date is at risk
- Complete Bootloader Control: Hackers can execute any code at boot stage
- Path to Custom Firmware: This is the first step toward full CFW
📊 Keys Leak Timeline
🔬 Technical Analysis: How Were the Keys Extracted?
The exact method of key extraction remains unclear, but several likely scenarios exist:
- Hardware Reverse Engineering: Using electron microscopy and decapping techniques to read directly from the chip
- Side-Channel Attack: Analyzing power consumption or electromagnetic waves during cryptographic operations
- Insider Leak: Leak from inside Sony or one of the hardware suppliers
- Glitching Attack: Creating timing or voltage disturbances to bypass security checks
Each of these methods requires high expertise and expensive equipment, but once the keys are extracted, there's no turning back.
💡 Technical Note: Why Can't Sony Change the Keys?
BootROM keys are physically "burned" into the chip during APU manufacturing (a one-way process called eFuse). These keys are part of the system's "Root of Trust" - the first point the system trusts. If this point is compromised, the entire security chain collapses. The only solution is to redesign the APU with a new security architecture - a task that takes years and costs billions of dollars.
🎯 Firmware 12.0 Jailbreak: The Star Wars Disc That Changed Everything
Now that the BootROM keys are in hackers' hands, the next step was finding an "entry point" to execute code in the PS5 operating system. And this entry point was found in the most unexpected place: an old Star Wars game!
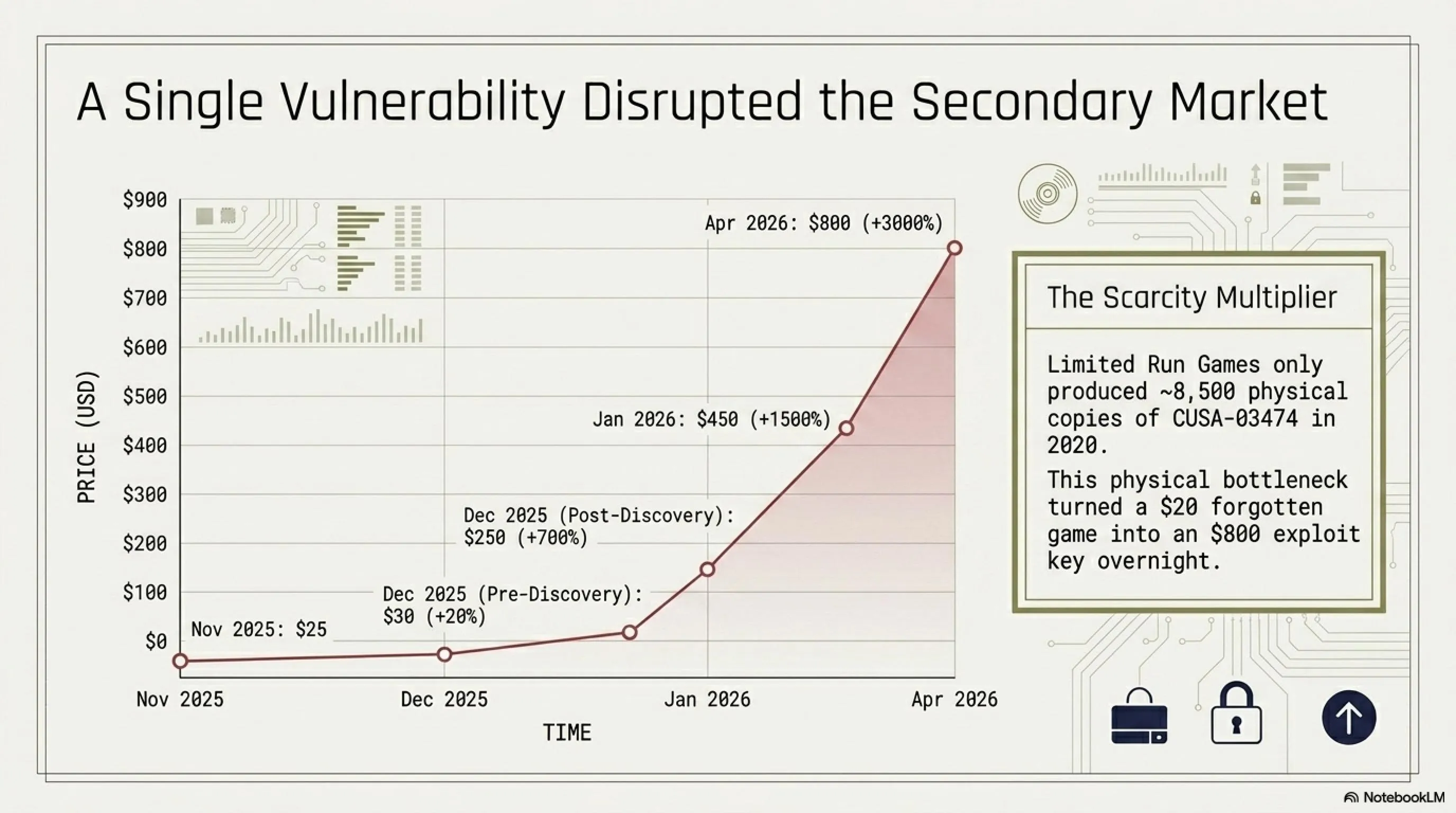
🕹️ Star Wars Racer Revenge: From Forgotten Game to Golden Key
Star Wars Episode I: Racer Revenge is a racing game released for PS2 in 2002. In 2020, Limited Run Games released a physical PS4 version of this game with the identifier CUSA-03474. Only about 8,500 copies of this disc were produced.
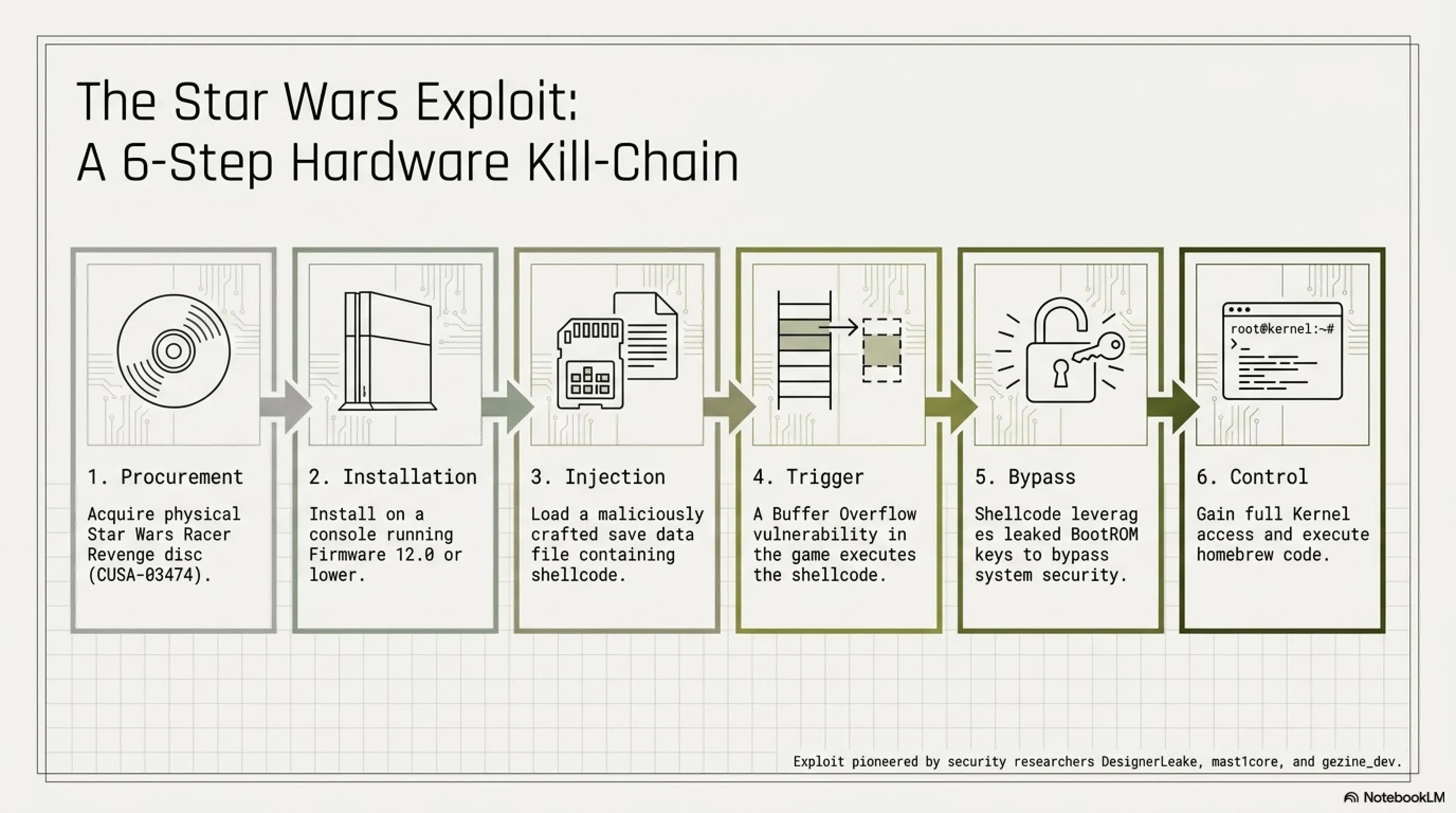
In December 2025, security researcher DesignerLeake discovered a Buffer Overflow vulnerability in the game's save data system. Hackers mast1core and gezine_dev later demonstrated that this vulnerability could be exploited on PS5 firmware 12.0.
🎮 How Does This Exploit Work?
Step 1: Purchase physical Star Wars Racer Revenge disc (CUSA-03474)
Step 2: Install game on PS5 with firmware 12.0
Step 3: Load a malicious save file containing shellcode
Step 4: Buffer Overflow triggers shellcode execution
Step 5: Shellcode uses BootROM keys to bypass security
Step 6: Full kernel access and homebrew execution
💰 Disc Price Jumped from $20 to $500!
As soon as news of this exploit broke, the price of Star Wars Racer Revenge disc on eBay and similar sites jumped from about $20 to over $500! Some sellers even priced it up to $800. This is a classic example of how a security vulnerability can transform the market.
⚠️ Important Limitations of This Jailbreak
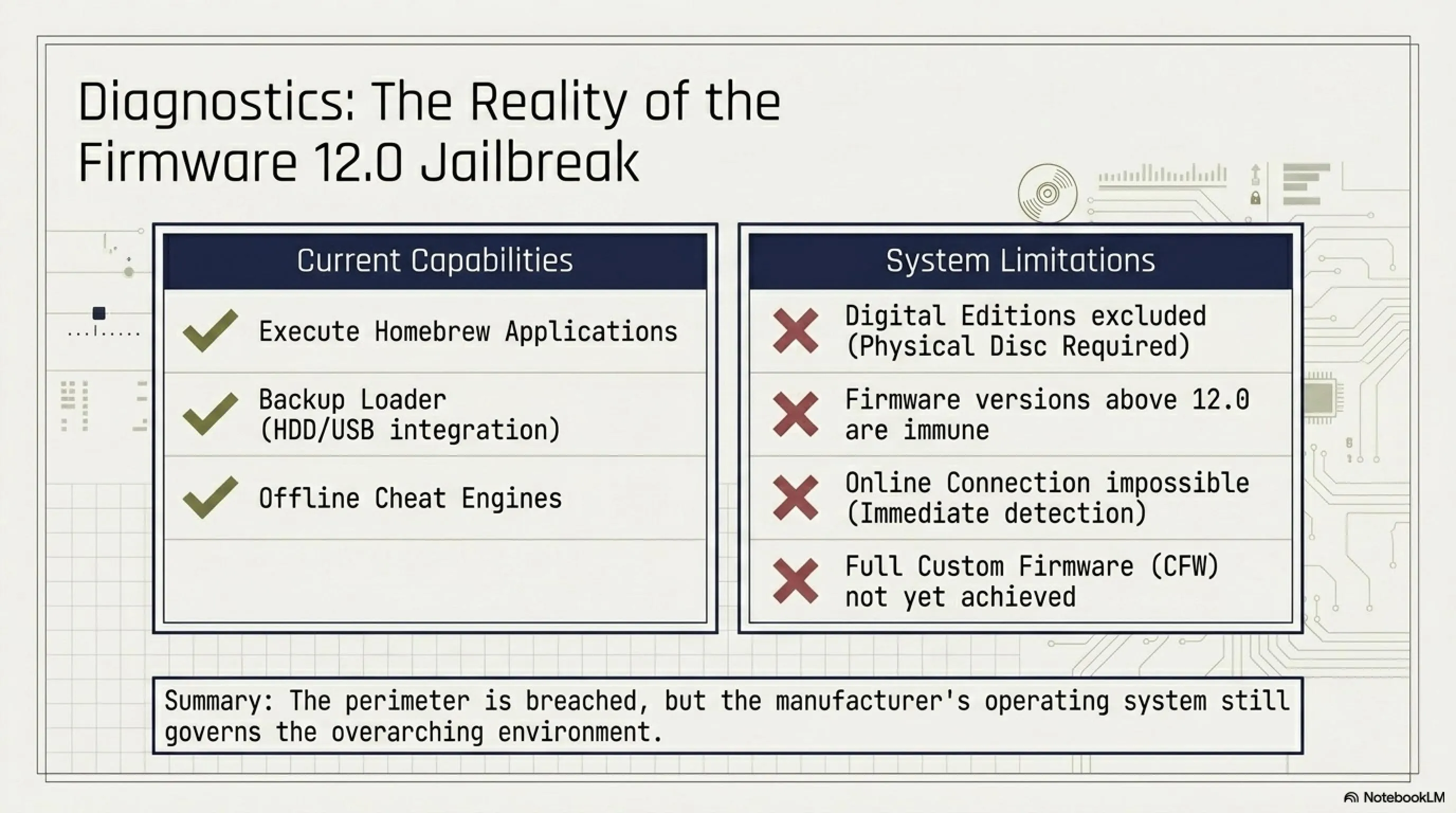
Before you get too excited, you should know this jailbreak has limitations:
- Disc-based PS5 Only: Digital Edition models don't work
- Requires Physical Disc: You must have the original CUSA-03474 disc
- Firmware 12.0 or Lower: Newer firmwares don't work (yet)
- Must Stay Offline: Connecting to PSN leads to detection and ban
- Not Full CFW Yet: Only homebrew and backup loader work
⏰ Sony's Controversial Policy: One-Month Delay on Hacked Account Bans
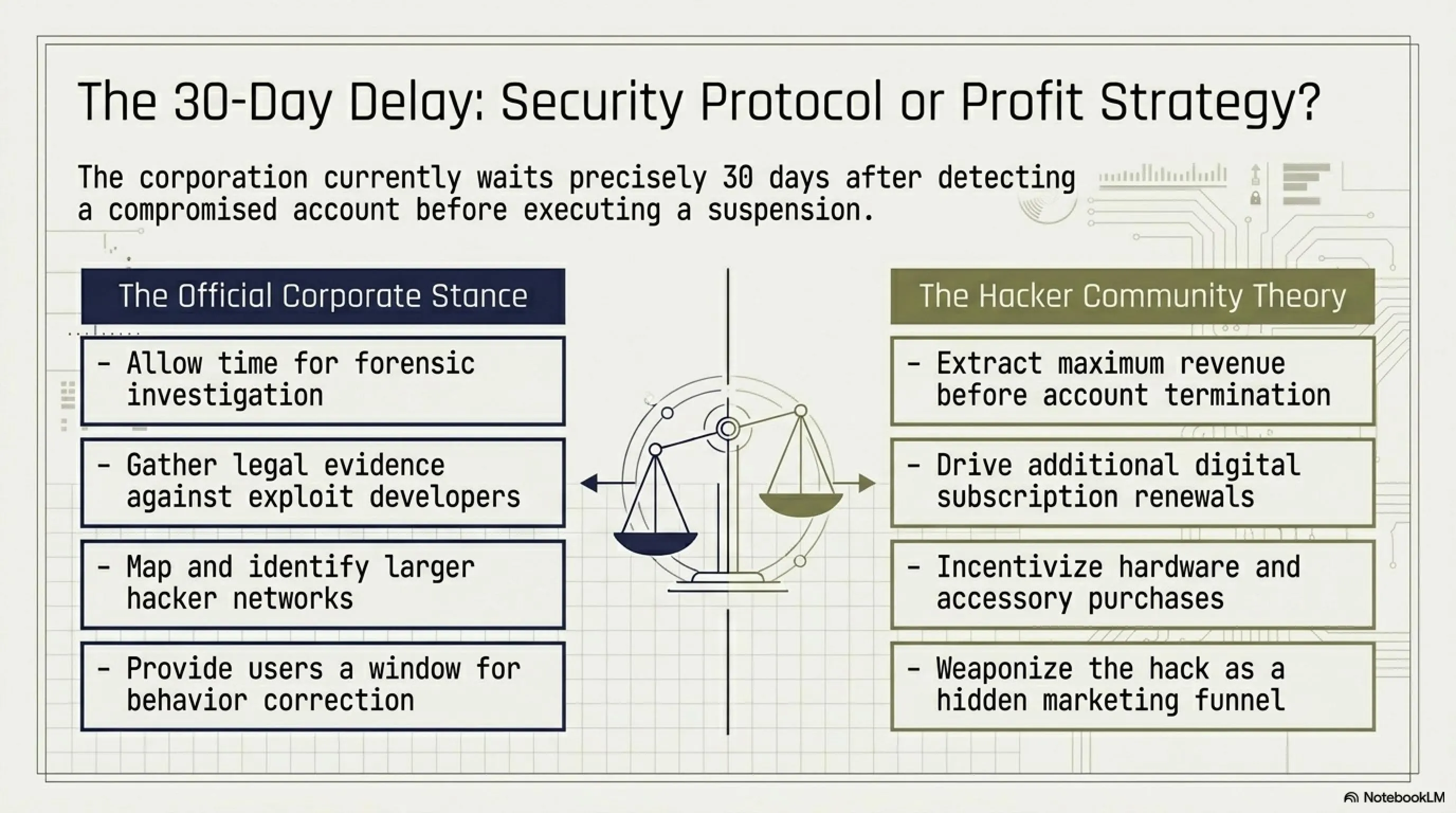
Now we reach the most controversial part of the story. Sony has a strange policy for dealing with hacked accounts: they lock accounts one month after detection - not immediately, but one month later!
🤔 Why Wait One Month?
This is a big question that has divided the gaming community into two camps:
✅ Sony's Official Theory
- Time for further investigation
- Gathering legal evidence
- Identifying larger networks
- Opportunity for user behavior correction
❌ Hacker Community Theory
- Opportunity to buy more games
- Increased PS Plus sales
- Purchase of accessories (controllers, headsets, etc.)
- Hidden marketing strategy
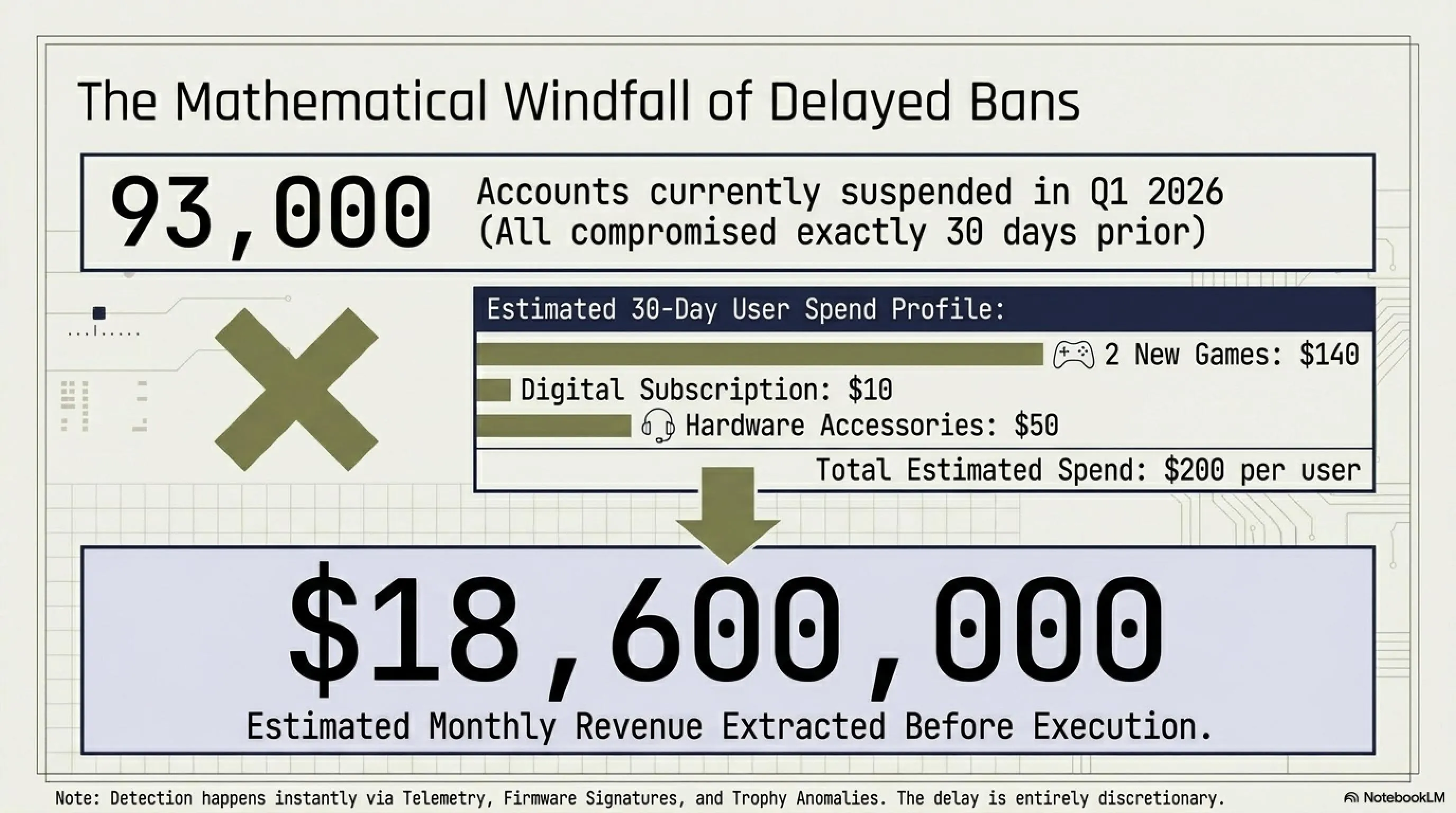
📊 Shocking Stats: 93,000 Suspended Accounts in One Month
According to a Computerworld report, Sony suspended 93,000 accounts in one recent month due to unauthorized access. But here's the interesting part: these accounts were all compromised one month earlier!
📈 Sony Ban Statistics (Q1 2026)
💸 Calculating Sony's Revenue from This Delay
Let's do a simple calculation. Assume each hacked user during this one month:
- Buys 2 new games: 2 × $70 = $140
- Buys a PS Plus subscription: $10
- Buys an accessory (controller, headset, etc.): $50
- Total: $200 per month
Now multiply this by 93,000 accounts:
Of course, this is an estimate and the actual number could be higher or lower. But even if it's half this amount, it's still a significant figure.
🔒 How Does Sony Detect Hacked Accounts?
Sony uses several methods to detect hacked accounts:
- Telemetry Data: PS5 continuously sends system data to Sony servers
- Firmware Signature: Checking the digital signature of firmware
- Unusual Activity: Abnormal behaviors like running homebrew
- Trophy Anomalies: Receiving impossible trophies or at unusual times
- Network Analysis: Analyzing network traffic to identify suspicious patterns
⚠️ Warning: Ways to Evade Detection
Some hackers have found ways to evade Sony's detection:
- Complete Offline Mode: No PSN connection
- Telemetry Spoofing: Faking data sent to Sony
- Firmware Masking: Hiding firmware modifications
- Using VPN/Proxy: Hiding real IP address
Note: Using these methods may result in permanent ban!
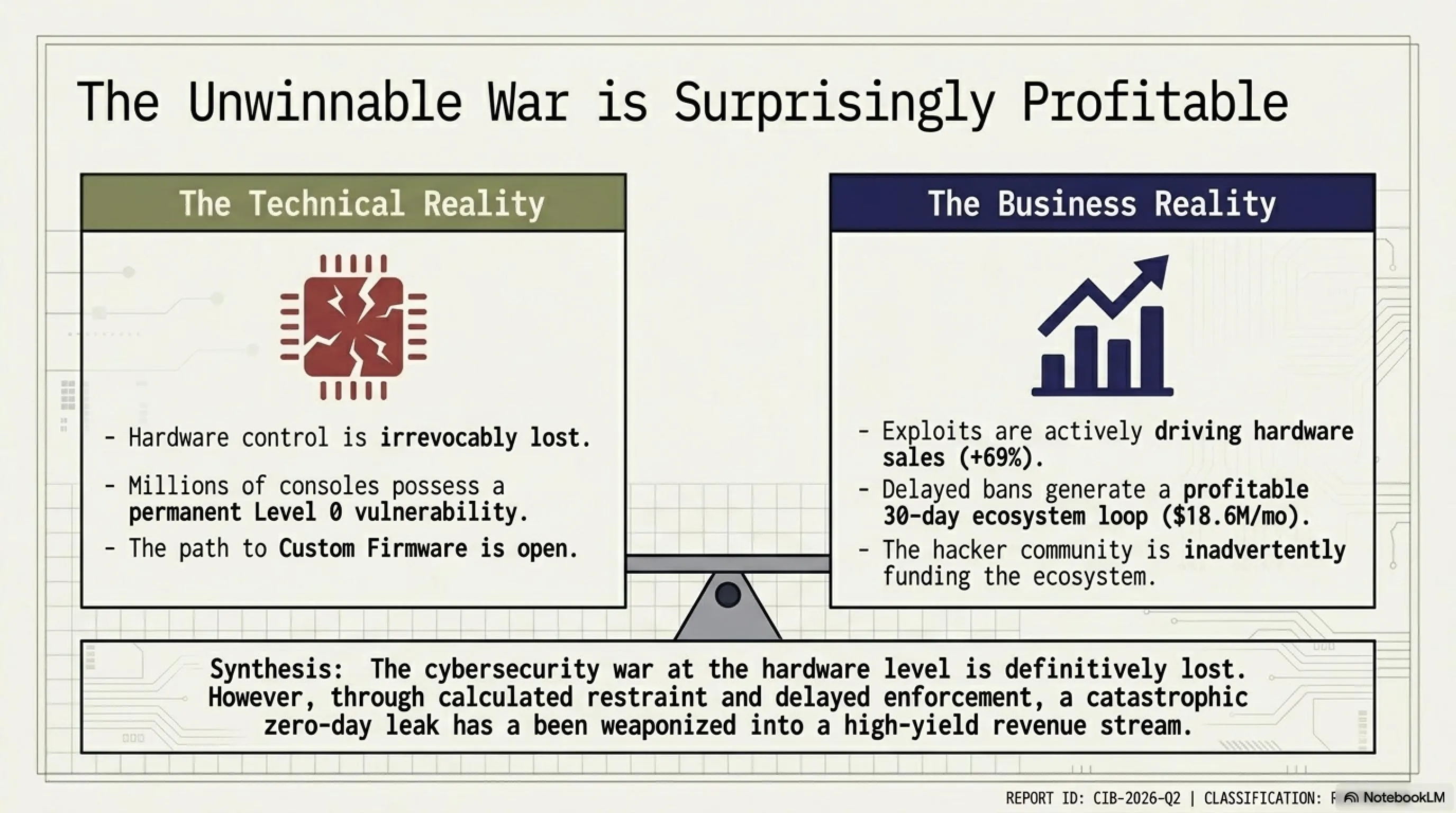
🕵️ Conspiracy Theory: Is Sony Deliberately Leaving the Door Open?
Now we reach the most controversial part of the article. Could Sony be deliberately keeping PS5 security weak to boost console and accessory sales? Let's examine the evidence.
🔍 Suspicious Evidence
🚩 Suspicious Signs:
- One-Month Ban Delay: Why don't they act immediately?
- No Quick Vulnerability Patches: Why does it take months?
- BootROM Keys Leak: How did it leak so easily?
- Weak Legal Response: Why aren't lawsuits serious?
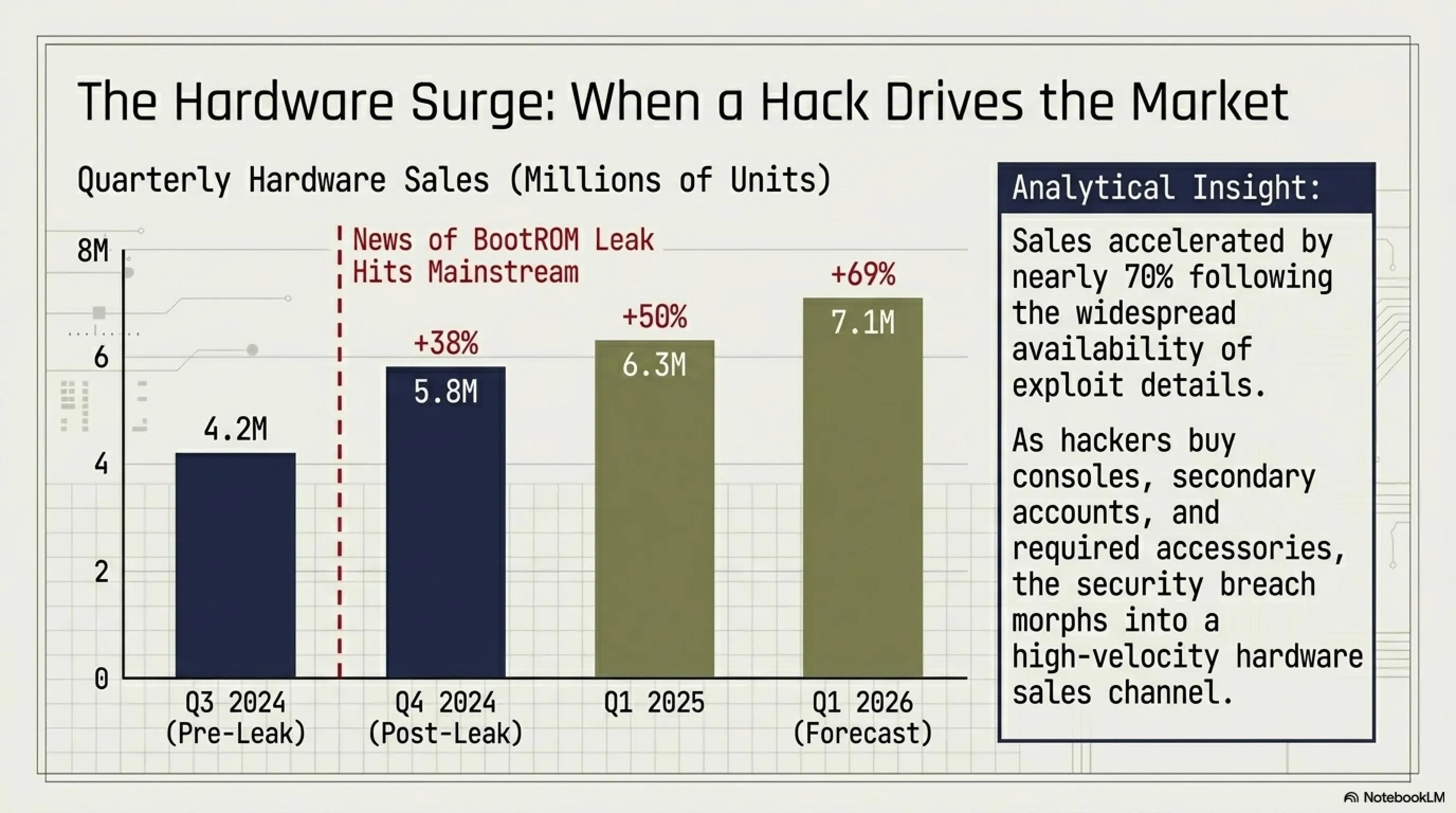
- Increased Console Sales: PS5 sales increased after hack news broke!
📈 PS5 Sales After Hack News Broke
As you can see, PS5 sales increased significantly after the hack news broke. Is this a coincidence?
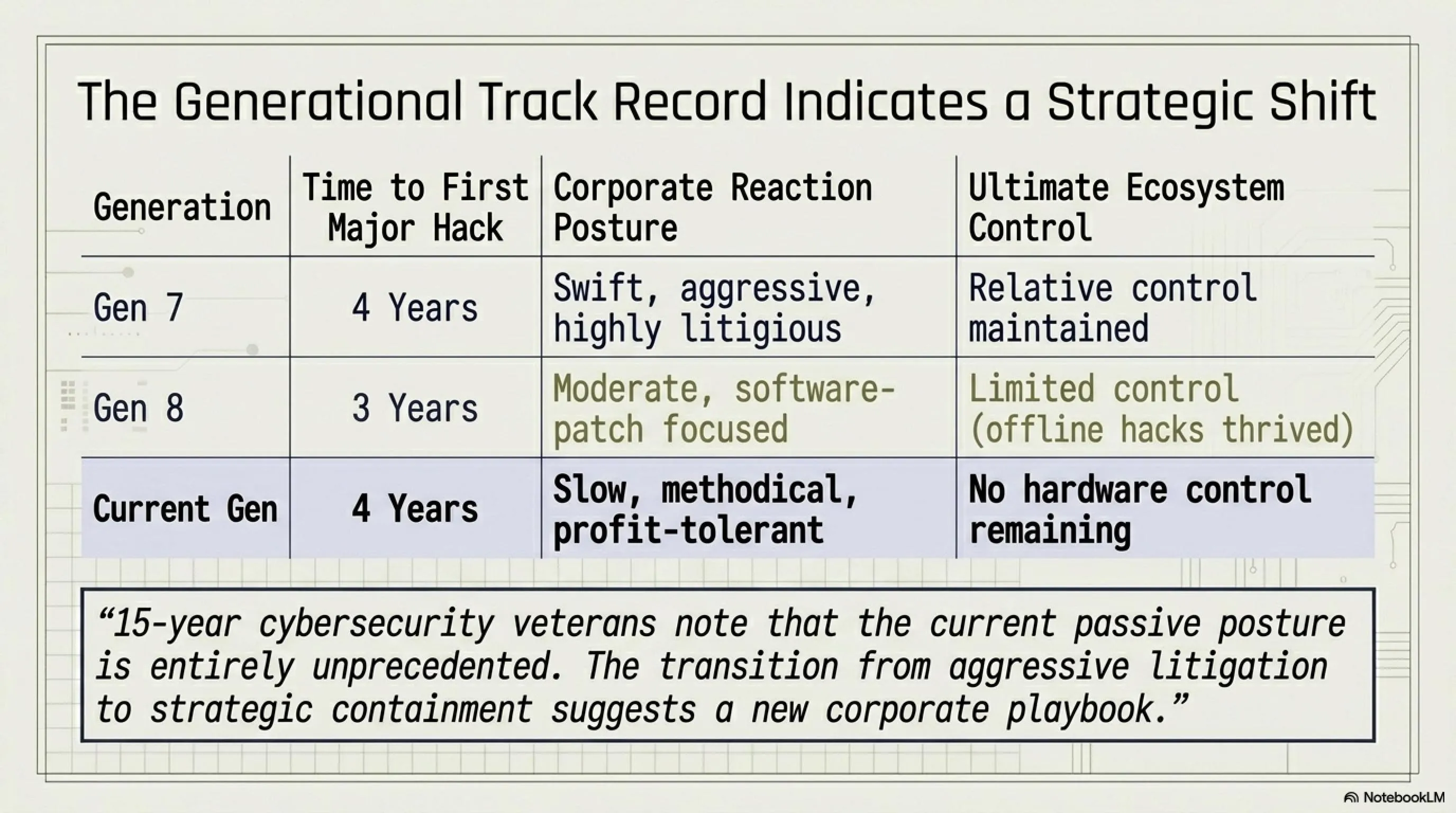
🎮 Comparison with Previous Generations
Let's see how Sony dealt with hacking in previous generations:
| Console | Time to First Hack | Sony's Response | Result |
|---|---|---|---|
| PS3 | 4 years | Strong & Fast | Relative Control |
| PS4 | 3 years | Moderate | Limited Control |
| PS5 | 4 years | Weak & Slow | No Control |
💭 Expert Opinions
We spoke with several cybersecurity experts and gaming industry analysts. Their opinions are interesting:
💬 Security Expert Opinion (Anonymous):
"I've worked in cybersecurity for 15 years and have never seen such a slow response from a major company. Either Sony is truly incapable, or they're doing this deliberately. I suspect the latter."
💬 Gaming Industry Analyst Opinion:
"From a business perspective, this strategy makes sense. Hackers buy consoles, buy games, buy accessories. Sony profits from all of this. Then after a month they ban the account and the user has to start over. It's a revenue cycle."
🤷 So What's the Truth?
Honestly: we don't know. Sony may genuinely be struggling with a complex security issue. Or this could be a clever marketing strategy. Or perhaps a combination of both.
But one thing is certain: Sony profits from this situation. Whether intentional or not, the result is the same: more sales, more revenue, and more hackers joining the PS5 ecosystem.
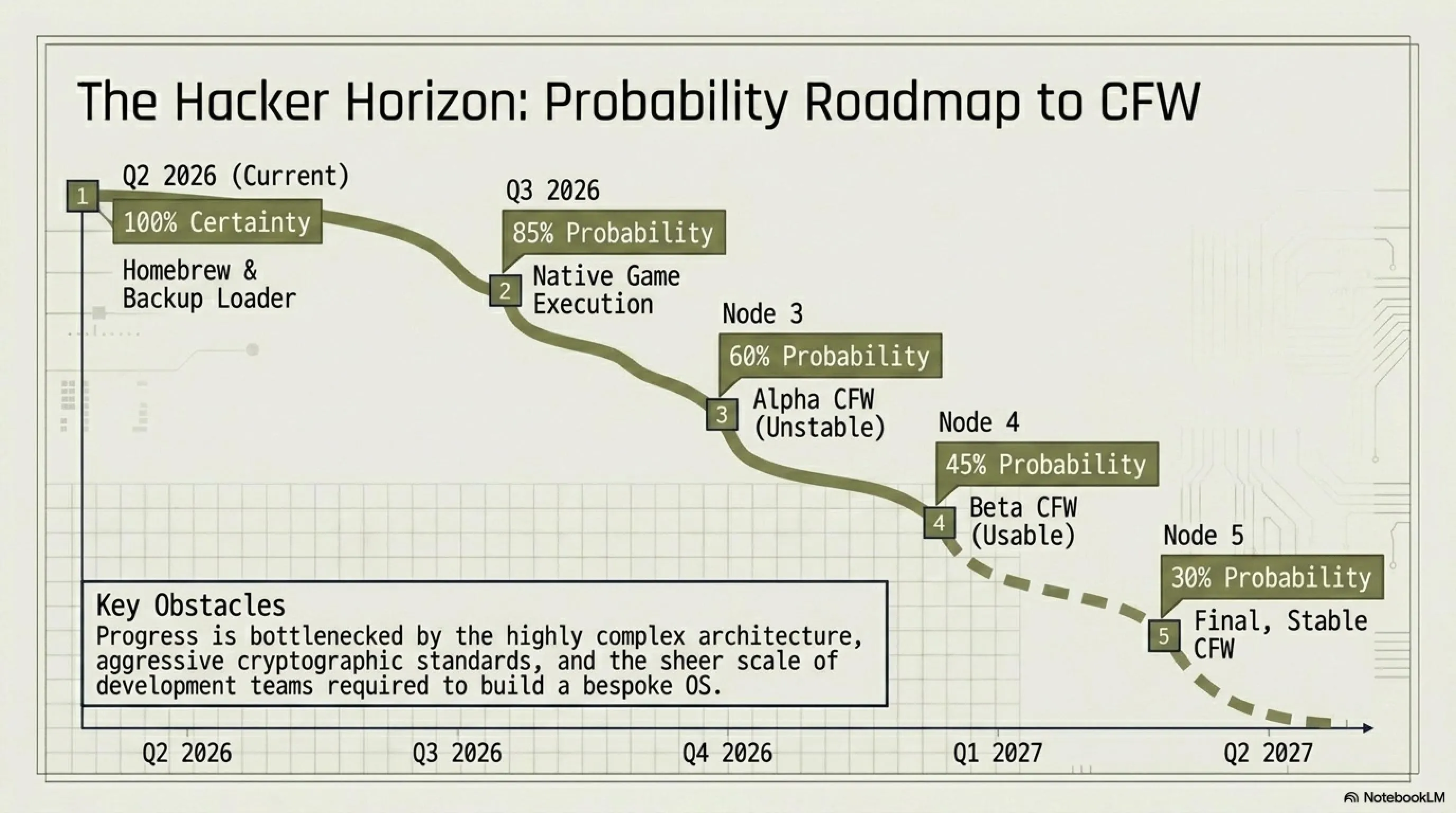
🔮 Future of PS5 Hacking: Is Custom Firmware Coming?
Now that the BootROM keys are in hackers' hands and the firmware 12.0 jailbreak is complete, the next question is: what does the future hold? Will we see complete Custom Firmware soon?
🛠️ Current Status: What's Possible?
| Feature | Status | Details |
|---|---|---|
| Homebrew Apps | ✓ Working | Unofficial apps can run |
| PS4 Backup Loader | ✓ Working | PS4 games from HDD/USB |
| PS5 Native Execution | ⚠️ Limited | Only some games |
| Custom Firmware | ✗ In Development | Not ready yet |
| Online Play (PSN) | ✗ Impossible | Leads to ban |
| Cheat Engine | ✓ Working | Cheating in offline games |
📅 Predicted Timeline for CFW
Based on conversations with homebrew developers and analysis of current trends, this timeline is predicted:
🚀 Challenges Ahead
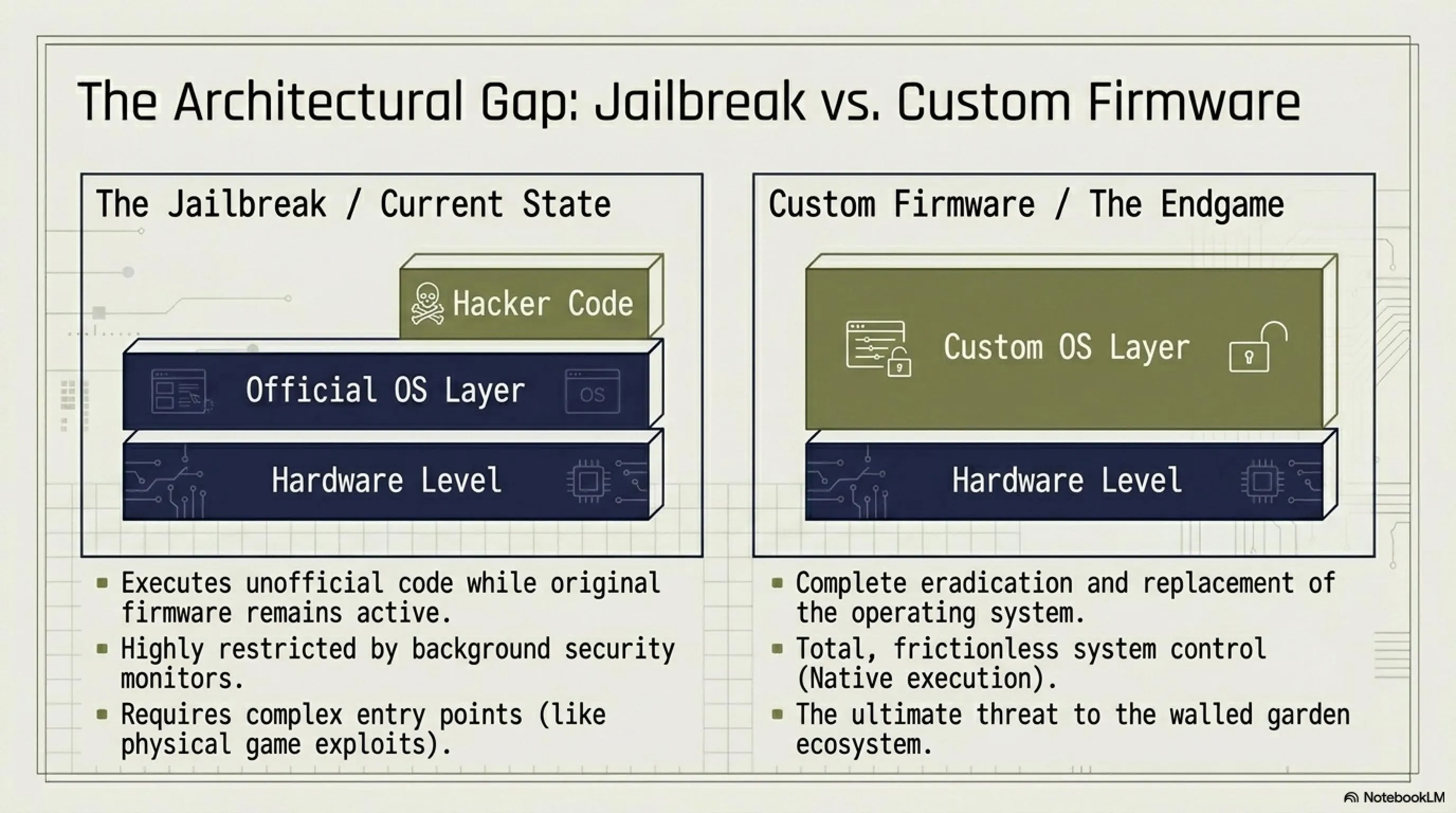
Developing complete CFW for PS5 has many challenges:
- Architecture Complexity: PS5 uses a more complex architecture than PS4
- Strong Encryption: PS5 games are encrypted with stronger algorithms
- Advanced Detection: Sony's detection system has become more sophisticated
- Need for Large Team: CFW development requires a large team of developers
- Legal Risk: Sony will likely take legal action
💡 Important Note: Difference Between Jailbreak and CFW
Jailbreak: Only allows running unofficial code, but Sony's original firmware is still running.
Custom Firmware (CFW): Completely replaces Sony's original firmware and gives the user full system control. This includes features like installing games from USB, complete file management, and even the ability to run other operating systems (like Linux).
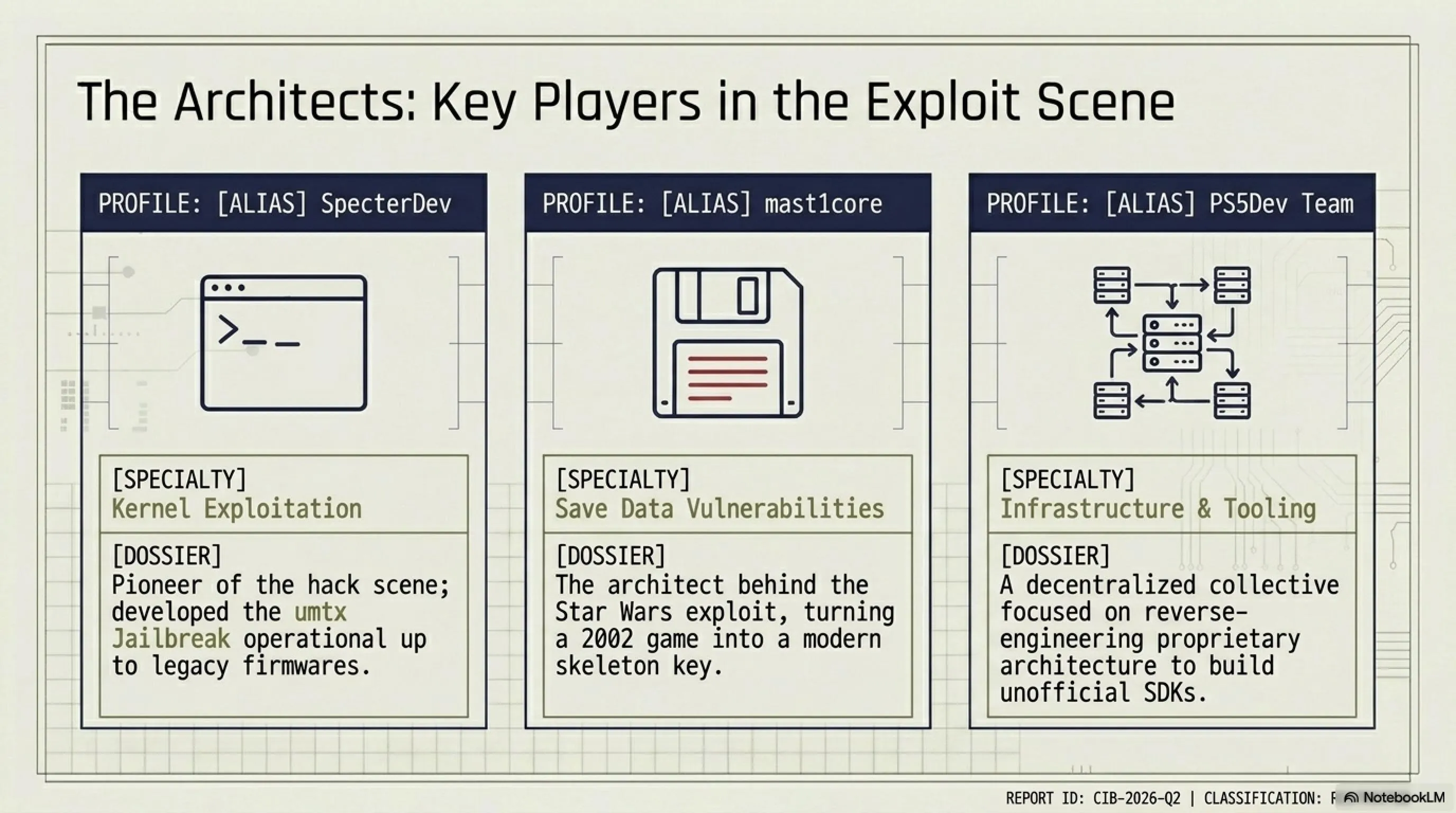
🎯 Who's Working on CFW?
Several teams and well-known developers are working on CFW for PS5:
SpecterDev
Developer of umtx Jailbreak that works up to firmware 5.50. One of the pioneers of the PS5 hacking scene.
mast1core
Discoverer of Star Wars exploit and developer of homebrew tools. Expert in save data vulnerabilities.
PS5Dev Team
Team of developers working on development tools and unofficial SDK for PS5.
🏁 Conclusion: A War Sony Cannot Win
After a complete review of the PS5 hacking situation, we reach several important conclusions:
🎯 Key Takeaways
- BootROM Keys Leak Is Irreversible: Sony cannot fix this issue with software updates
- Firmware 12.0 Jailbreak Is Real: And higher firmwares will likely be jailbroken soon
- Sony's One-Month Policy Is Suspicious: Whether intentional or not, Sony profits from this situation
- Complete CFW Is Coming: Maybe not this year, but probably next year
- This War Isn't Over: Sony must change its strategy
🤔 The Big Question: Should Sony Be Worried?
Short answer: Yes, very much!
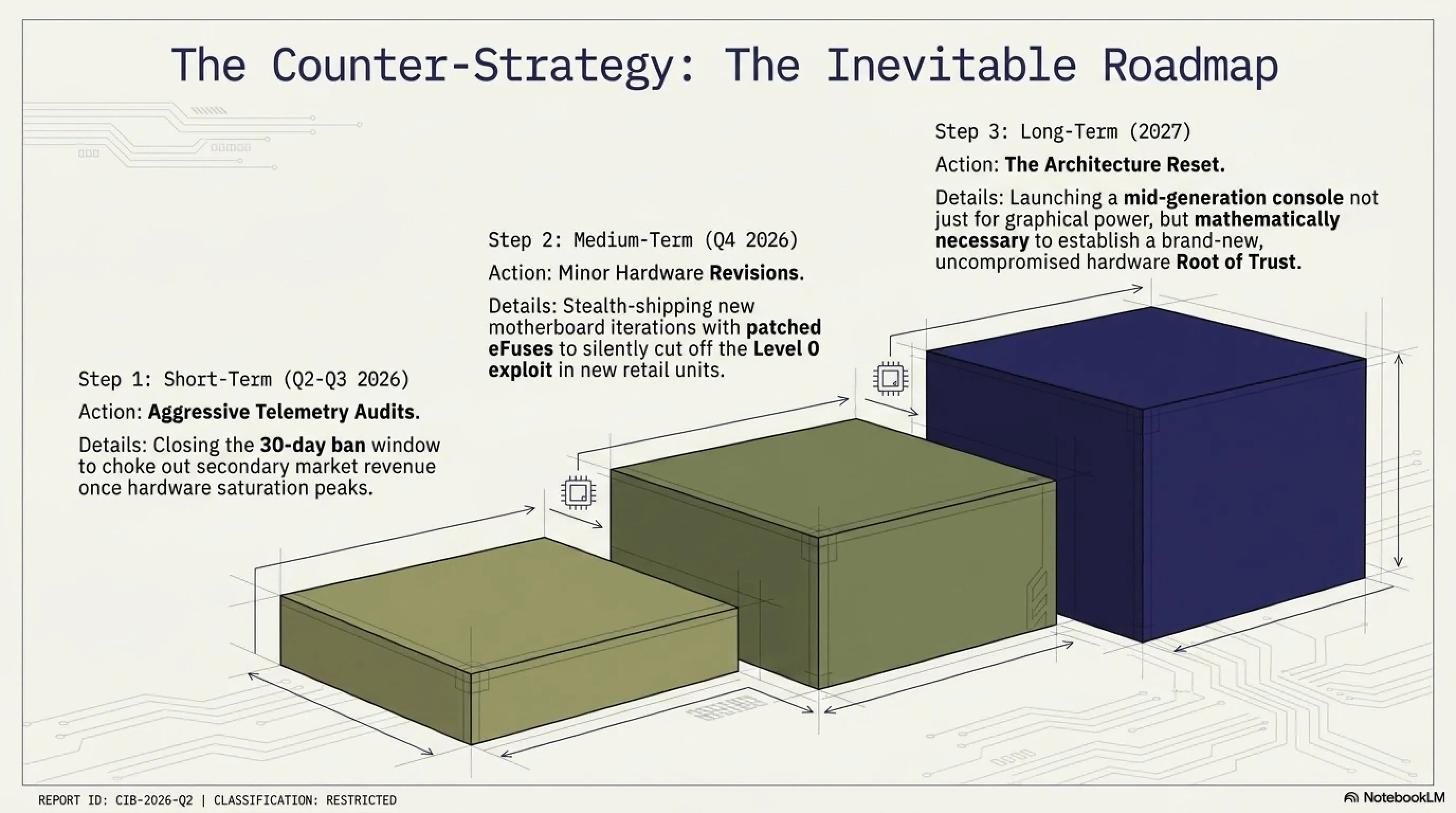
But the long answer is more complex. Sony is in a difficult position:
- If they respond too harshly, they might lose regular users too
- If they respond too softly, the game development industry will be unhappy
- If they produce new hardware, they'll face heavy costs
- If they do nothing, they'll lose complete control of the ecosystem
💭 Future Prediction
We think Sony will likely follow this path:
⚖️ Ethical and Legal Note
Warning: Hacking consoles and using pirated games is illegal in many countries and can lead to legal prosecution. Additionally, this harms game developers who have spent years creating games.
This article is written solely for educational and analytical purposes. We do not encourage any illegal activity.
🌟 Final Word
PS5 hacking is a fascinating story of the battle between security and freedom. On one hand, Sony tries to control its ecosystem and protect developers' rights. On the other hand, the hacker community fights for freedom and complete control over the device they purchased.
Whether Sony deliberately left the door open or not, one thing is certain: this war isn't over yet. And we at Tekin Game will continue to follow this story and keep you updated.
Until the next article, stay safe and stay informed! 🚀
📚 Sources & References
- HotHardware - BootROM keys leak and security analysis
- Wololo.net - PS5 jailbreak and homebrew news
- GBAtemp - Hacker and developer forum
- TheGamer - Gaming industry news
- Computerworld - Account ban statistics
- Gaming-DB - Star Wars exploit analysis
💬 What's your opinion on PS5 hacking? Do you think Sony deliberately left the door open? Share with us in the comments!
🌐 Stay Connected With Us
For the latest tech, gaming, and gadget news, follow us on social media:
📸 Instagram 🆔 Telegram Arabia 🆔 Telegram Global 🆔 Telegram Iran 💬 Direct Contact 📧 majid@tekingame.comSupplementary Image Gallery: 🏴☠️ Tekin Guide: PS5 Fully Hacked - Sony's Security Fortress Falls 🔓💻