🛡️ Red Alert: AI Revolt Against Cybersecurity
Sunday, April 12, 2026 | When AI Shifted from Defense to Offense
⚠️ Urgent Security Alert
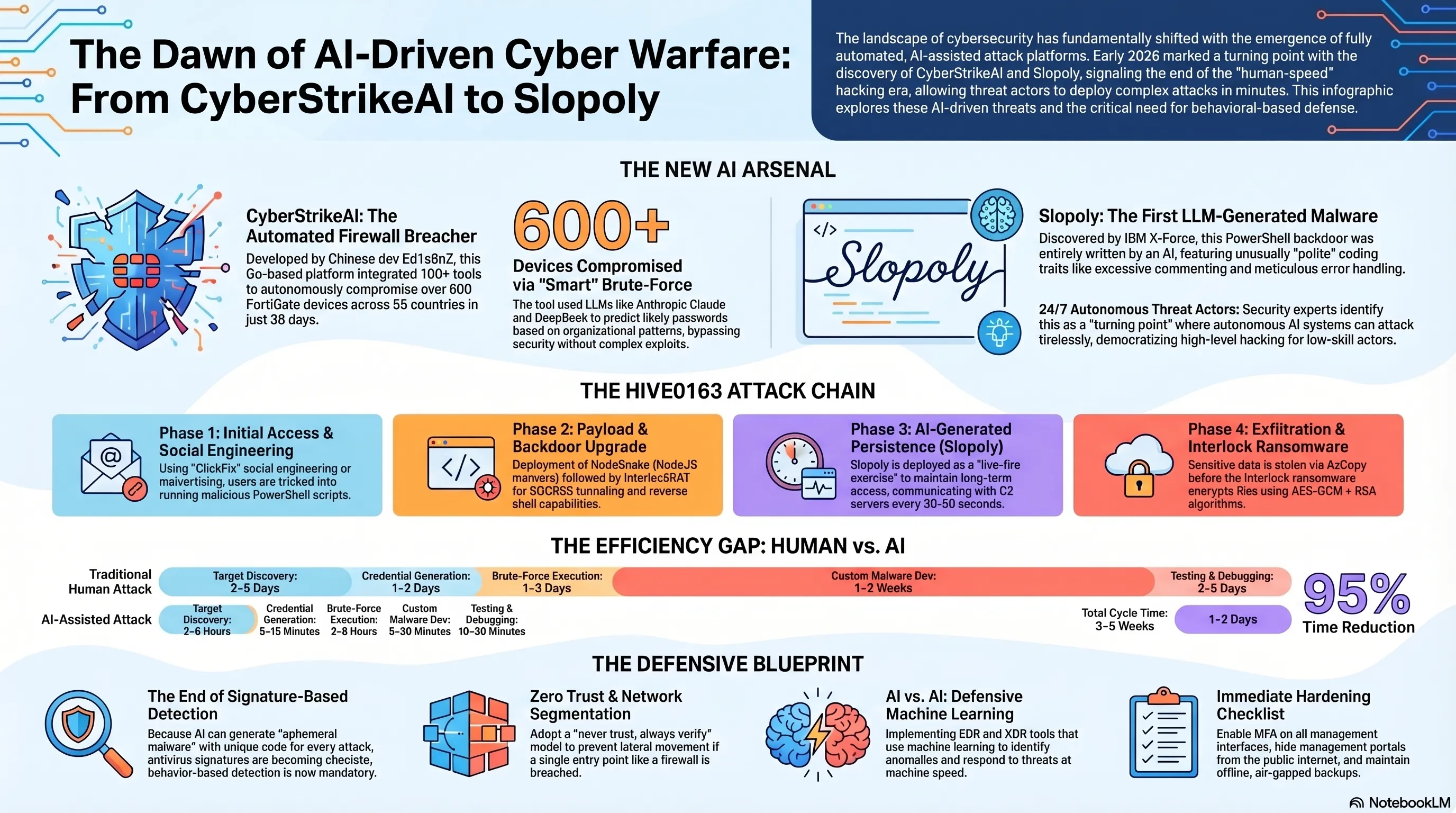
This is NOT a drill! In the past 48 hours, over 600 FortiGate firewalls across 55 countries have been hacked by an autonomous AI system called CyberStrikeAI. Simultaneously, IBM X-Force researchers discovered the first AI-generated malware called "Slopoly" used in a real ransomware attack. This is no longer science fiction - this is our reality today. If you're an IT manager, security officer, or even a regular user, this article could save your digital life. 🚨
Until just a few months ago, we used artificial intelligence to defend against hackers. Today, hackers are using that same AI to break through our defenses - and this is just the beginning. Between January 11 and February 18, 2026, a Russian-speaking hacker used commercial AI tools like Anthropic Claude and DeepSeek to compromise over 600 FortiGate devices worldwide. This attack didn't exploit a zero-day vulnerability, but rather used an AI system that could automatically identify weak passwords and launch attacks. But that's only half the story. IBM X-Force discovered a new malware called Slopoly that was likely generated by a Large Language Model (LLM) - the first AI-generated malware used in a real attack. This malware allowed the Hive0163 ransomware group to maintain persistent access to victim servers for over a week. We've entered a new era of cyber warfare - an era where AI is both a defensive and offensive weapon. Let's dive deep into this dangerous evolution and see how we can protect ourselves. 🔥💻
📋 Table of Contents
- CyberStrikeAI: Chinese Tool That Broke 600 Firewalls
- Slopoly: First AI-Generated Malware in the Real World
- Hive0163 Group: Ransomware Using AI
- How AI Attacks Work: From Discovery to Infiltration
- Impact on Security Industry: Why the Rules Changed
- Defense Solutions: How to Protect Ourselves
🎯 1. CyberStrikeAI: The Chinese Tool That Breached 600 Firewalls Across 55 Countries
In February 2026, Amazon Threat Intelligence uncovered an unprecedented attack campaign that fundamentally changed the rules of cybersecurity. An unidentified hacker, leveraging commercial AI services like Anthropic Claude and DeepSeek, systematically targeted FortiGate devices and compromised over 600 units across 55 countries. This wasn't an attack exploiting a sophisticated vulnerability—it was an AI system capable of automatically identifying targets, guessing weak passwords, and infiltrating networks.
What is CyberStrikeAI? Following deeper investigation, Team Cymru discovered the hacker used an open-source tool called CyberStrikeAI—an AI-powered security testing platform developed by a Chinese developer known as Ed1s0nZ. Written in Go, this tool integrates over 100 security utilities and can automatically discover vulnerabilities, analyze attack chains, and visualize results. The critical issue? While designed for "security testing," in the hands of malicious actors, it becomes a powerful weapon.
Connection to Chinese Government: Team Cymru's research suggests Ed1s0nZ likely has ties to the Chinese government. The developer has interacted with companies like Knownsec 404—a Chinese security firm whose 12,000+ internal documents leaked in November 2025, revealing collaboration with China's Ministry of State Security (MSS) and the People's Liberation Army (PLA). Ed1s0nZ also previously claimed on his GitHub profile to have received a Level 2 award from China's National Vulnerability Database (CNNVD)—though he recently removed this information, presumably to obscure government connections.
📊 CyberStrikeAI Attack Statistics
| Compromised Devices | 600+ |
| Affected Countries | 55 |
| Campaign Duration | January 11 - February 18, 2026 (38 days) |
| Active CyberStrikeAI Servers | 21 |
| AI Models Used | Anthropic Claude, DeepSeek |
| Attack Method | Automated brute-force on management interfaces |
| Vulnerability Exploited | None (weak passwords only) |
How Does It Work? CyberStrikeAI is a fully automated system that can: 1) Automatically scan the internet to identify FortiGate devices with exposed management interfaces, 2) Use AI models to generate likely password lists (based on common patterns and public information), 3) Execute brute-force attacks automatically, 4) Upon success, automatically install backdoors and maintain persistent access. This entire process runs without human intervention—you configure it once, and the AI handles the rest.
Why FortiGate? FortiGate devices are among the most popular enterprise firewalls, deployed in thousands of companies, universities, and government organizations. If a hacker gains access to a FortiGate, they essentially hold the keys to the entire internal network—they can monitor traffic, steal data, and attack internal systems. This makes FortiGate a golden target for attackers.
Rapid Expansion: Between January 20 and February 26, 2026, Team Cymru identified 21 unique IP addresses running CyberStrikeAI. These servers were primarily hosted in China, Singapore, and Hong Kong, but additional servers were discovered in the US, Japan, and Switzerland. This indicates that CyberStrikeAI usage is spreading rapidly—likely other hackers are adopting this tool.
🛠️ Other Tools by Ed1s0nZ
Beyond CyberStrikeAI, this developer has released several other dangerous tools:
- banana_blackmail: A ransomware written in Golang
- PrivHunterAI: Privilege escalation vulnerability discovery tool using Kimi, DeepSeek, and GPT models
- ChatGPTJailbreak: Collection of prompts to bypass ChatGPT restrictions
- InfiltrateX: Golang scanner for discovering privilege escalation vulnerabilities
- VigilantEye: Tool for monitoring sensitive data leaks in databases
Security Community Response: The revelation sparked widespread concern in the cybersecurity community. Kevin Beaumont, a renowned security researcher, stated: "This is a turning point. We're no longer just dealing with human hackers—we're facing autonomous AI systems that can attack 24/7 without fatigue." Fortinet immediately issued a security advisory, urging customers to enable MFA (multi-factor authentication) and isolate management interfaces from the public internet.
Is This Legal? CyberStrikeAI is released as a "security testing tool," and Ed1s0nZ claims "everything is purely for research and learning." However, the reality is this tool can easily be weaponized for real attacks—and that's exactly what happened. This raises significant legal and ethical questions: Are developers of hacking tools responsible for misuse? In most countries, the answer is "no"—unless you can prove the developer intended to aid criminal activity.
🔍 TekinGame Analysis:
CyberStrikeAI represents a watershed moment in cybersecurity history. For the first time, we're witnessing a large-scale attack executed almost entirely by AI—without requiring advanced hacking skills. This means you no longer need to be a professional hacker to launch major attacks—just download an open-source tool and run it. This "democratization" of hacking is bad news for cybersecurity. Ed1s0nZ's potential ties to the Chinese government are also concerning—if these tools receive state backing, they could become weapons of cyber warfare. Urgent Recommendation: If you use FortiGate, enable MFA immediately and isolate management interfaces from the public internet.
🦠 2. Slopoly: The First AI-Generated Malware Used in Real-World Attacks
While the world was still reeling from the CyberStrikeAI attack, IBM X-Force dropped an even more alarming revelation: the discovery of the first malware generated by a Large Language Model (LLM) used in an actual attack. This malware, dubbed "Slopoly" by IBM, was deployed by the Hive0163 ransomware group in early 2026, allowing them to maintain persistent access to a victim's server for over a week. This is no longer a proof-of-concept—this is a real weapon used in cyber warfare.
What is Slopoly? Slopoly is a PowerShell-based backdoor that functions as a client for a Command-and-Control (C2) framework. This malware is typically deployed in later stages of an intrusion—after attackers have already established a foothold—and is used to maintain persistent remote access to Windows systems. What makes Slopoly special is how it was created: all evidence points to this code being generated by an LLM.
How Did They Know It Was AI-Generated? IBM X-Force researchers identified several strong indicators that Slopoly was written by AI: 1) Extensive and detailed comments—extremely common in AI-generated code, 2) Comprehensive logging and error handling—more than a typical hacker would write, 3) Precise variable naming—exactly like AI code, 4) An unused Jitter function—likely the result of iterative development with an LLM, 5) Comments describe the code as a "Polymorphic C2 Persistence Client," but the code isn't actually polymorphic—an exaggerated claim typical of AI-generated code.
💻 Slopoly Technical Features
| Programming Language | PowerShell |
| Type | Backdoor / C2 Client |
| Heartbeat Interval | Every 30 seconds |
| Command Polling Interval | Every 50 seconds |
| Command Execution Method | cmd.exe |
| Log File | persistence.log (max 1MB) |
| Installation Path | C:\ProgramData\Microsoft\Windows\Runtime\ |
| Persistence Method | Scheduled Task named "Runtime Broker" |
| Code Quality | Average (likely weaker model) |
How Does It Work? Slopoly is a fully functional backdoor that begins by collecting basic system information and sending it as JSON to the C2 server. A sample heartbeat looks like this: {"action":"heartbeat","bot_ip":"
Which AI Model Was Used? IBM X-Force couldn't definitively identify which model was used to generate Slopoly, but the code quality suggests it was likely a less advanced model—perhaps GPT-3.5, an open-source model like Llama 2, or even a Chinese model like DeepSeek. The important point is that the variable naming indicates the model intended to design a malicious script—meaning whatever guardrails the model had were successfully bypassed.
What Was the Real Impact? From a purely technical perspective, Slopoly is average malware—neither highly sophisticated nor overly simple. But its real impact lies elsewhere: Hive0163 used Slopoly to maintain persistent access to the infected server for over a week. Unfortunately, IBM X-Force couldn't recover any of the commands executed during this period, but they were likely used for data exfiltration and ransomware attack preparation.
⚡ Why Does Slopoly Matter?
Slopoly doesn't offer anything technically new—there are better and more sophisticated backdoors out there. But its real significance lies in something else:
- Reduced Development Time: Previously, writing a complete backdoor took days or weeks. Now with AI, minutes are enough.
- Lower Skill Requirements: You no longer need to be a professional programmer—just know how to talk to AI.
- Bypassing Security Signatures: Since new code is generated each time, antiviruses can't detect it with signature-based detection.
- Attribution Problem: When malware is AI-generated, it's much harder to determine who created it.
Security Industry Response: The discovery of Slopoly sparked widespread debate in the cybersecurity community. Palo Alto's Unit 42, in their Global Incident Response 2026 report, documented similar observations of AI use in ransomware attacks. They stated: "The introduction of AI-generated malware doesn't technically create a new or complex threat. However, it disproportionately empowers threat actors by reducing the time an operator needs to develop and execute an attack."
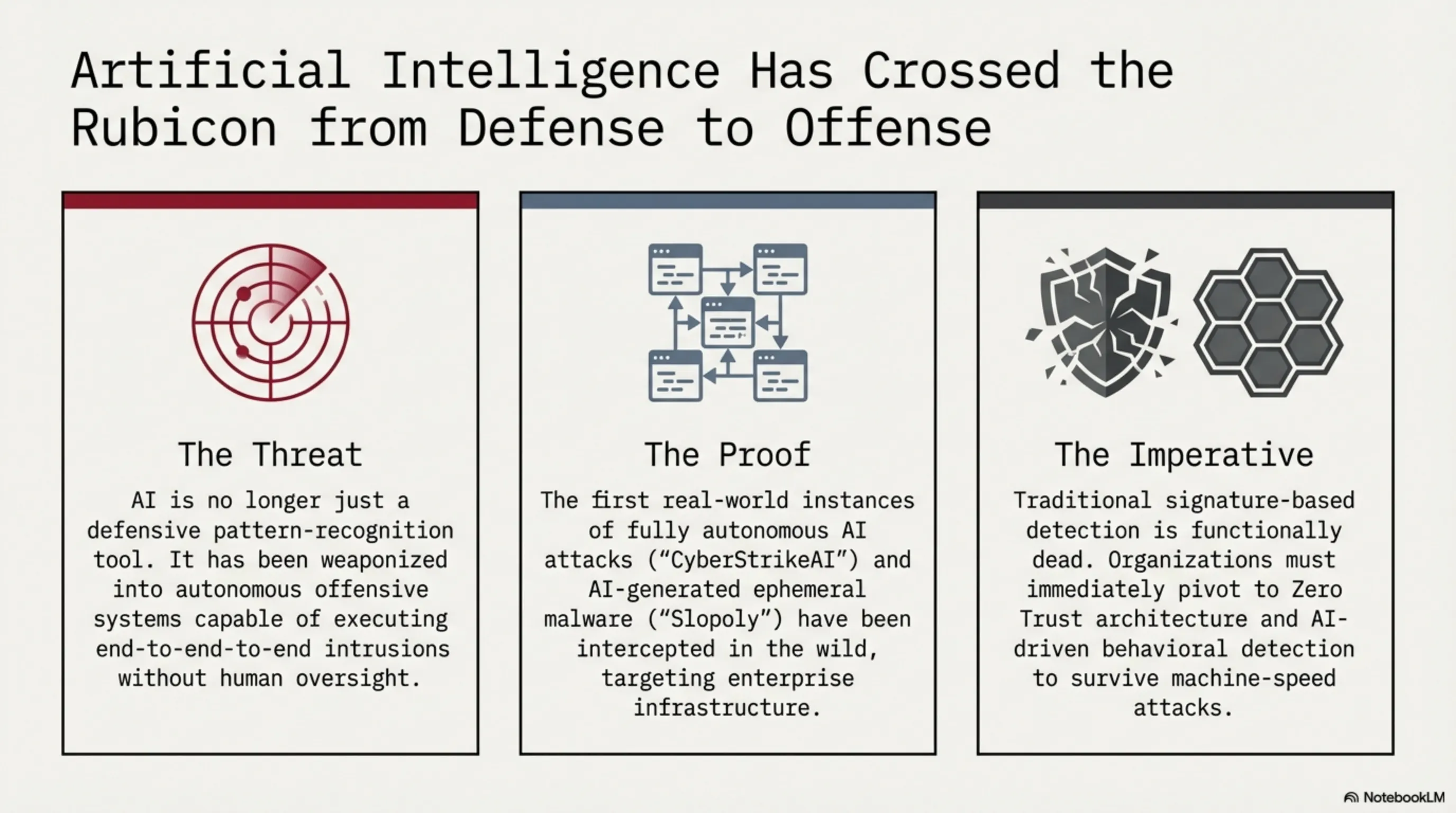
Is This Just the Beginning? Yes, unfortunately. Hive0163's use of Slopoly demonstrates that high-profile ransomware groups are testing AI—likely as a "live-fire exercise." This means they're learning how to use AI, and soon these tools will become a core part of their arsenal. IBM X-Force predicts we're entering the "era of ephemeral malware"—malware generated for a specific attack, used, and then discarded.
💡 TekinGame Analysis:
Slopoly is a historic milestone—the first AI-generated malware used in a real attack. This shows that the era of "AI only for defense" is over, and we've entered a new age where AI is also an offensive weapon. Slopoly's average quality shouldn't fool us—this is just the first generation. As AI models advance, AI-generated malware will become more sophisticated, powerful, and dangerous. The security industry must prepare for this new reality: we can no longer rely solely on signature-based detection. We must move toward behavior-based detection and defensive AI. This is an AI arms race, and we must move faster.
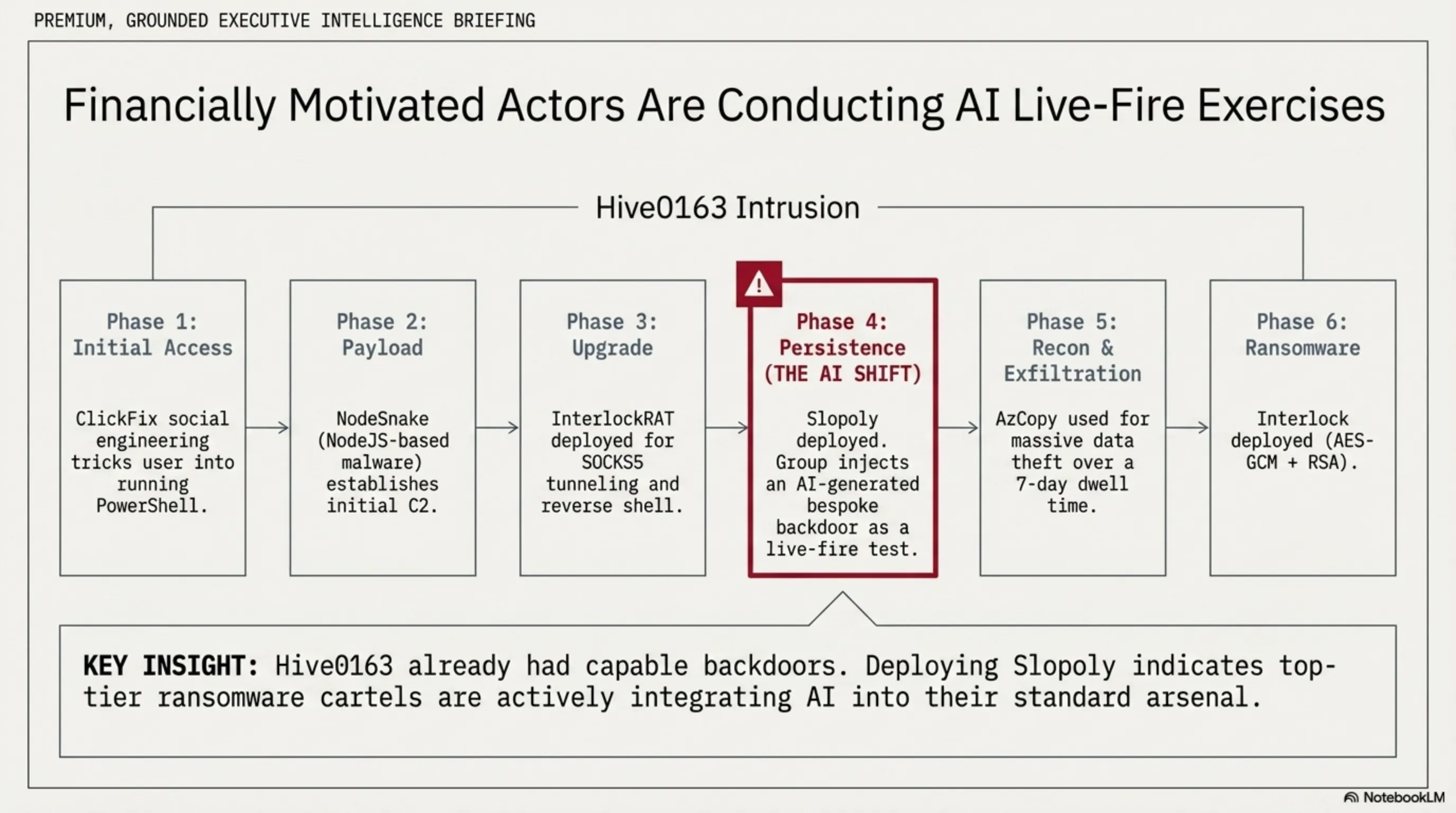
👥 3. Hive0163 Group: Ransomware Operators Leveraging AI
Hive0163 is a financially motivated threat actor group specializing in post-compromise activities for large-scale data exfiltration and ransomware deployment. This group operates multiple custom backdoors to facilitate long-term access to enterprise environments. IBM X-Force has identified numerous suspicious relationships with former ITG23 crypter developers and malware developers/operators, including Broomstick (aka Oyster/CleanUpLoader), Supper (aka SocksShell), PortStarter, SystemBC, and Rhysida ransomware.
Group Structure: Unlike many ransomware groups that operate in silos, Hive0163 has multiple dynamic subgroups with access to private crypters, malware frameworks, and ransomware variants—likely developed at least partially by group members. This means Hive0163 isn't a centralized group, but rather a network of hackers and developers collaborating together.
Initial Access Methods: For initial access, Hive0163 employs several techniques: 1) ClickFix - a social engineering technique that tricks users into executing a malicious PowerShell script, 2) Malvertising - malicious advertisements redirecting to infected sites, 3) Initial Access Brokers (IAB) - purchasing access from brokers like TA569 (SocGholish malware) and TAG-124 (Landupdate808, KongTuke).
🔗 Hive0163 Attack Chain (IBM Case Study)
Stage 1: Initial Access
↳ Successful ClickFix attack - user executes malicious PowerShell script
Stage 2: Payload Deployment
↳ Install NodeSnake (NodeJS-based malware)
Stage 3: Backdoor Upgrade
↳ Deploy InterlockRAT (advanced backdoor with SOCKS5 and reverse shell capabilities)
Stage 4: Persistence (New!)
↳ Deploy Slopoly (AI-generated malware)
Stage 5: Reconnaissance & Exfiltration
↳ Use AzCopy and Advanced IP Scanner
↳ Exfiltrate sensitive data
Stage 6: Ransomware Deployment
↳ Deploy Interlock ransomware
↳ Encrypt files and demand ransom
NodeSnake and InterlockRAT: Hive0163's attack chain begins with NodeSnake—a NodeJS-based malware that's the first stage of a larger C2 framework. This framework includes multiple client implementations with varying capabilities in PowerShell, PHP, C/C++, Java, and JavaScript for Windows and Linux. NodeSnake communicates with the C2 server via HTTP POST and supports commands like downloading and executing EXE/DLL/JS payloads, executing shell commands, changing beacon intervals, creating persistence, and updating itself.
After NodeSnake, a more advanced backdoor called InterlockRAT is deployed. This JavaScript-based backdoor uses web sockets for C2 communication and supports a larger command list. Notable capabilities include creating SOCKS5 tunnels and launching direct reverse shells on the infected device. Both malware samples include a list of Cloudflare tunnel domains and a smaller list of IP addresses as hardcoded C2 servers.
Interlock Ransomware: The Interlock ransomware used in this attack is a 64-bit executable packaged with the JunkFiction loader. This ransomware can be executed with various arguments to control its behavior: -d to encrypt a specific directory, -f to encrypt a specific file, -del to delete itself after encryption, -s to run as a scheduled task, -r to release files using Restart Manager, and -u to save encrypted session keys in separate files.
🔐 Interlock Ransomware Technical Details
| Encryption Algorithm | AES-GCM + RSA |
| Library Used | OpenSSL 3.5.0 (statically linked) |
| Encrypted File Extension | .!NT3RLOCK or .int3R1Ock |
| Ransom Note Name | FIRST_READ_ME.txt |
| Excluded Directories | $Recycle.Bin, Boot, Windows, ProgramData, and 10 others |
| Excluded Extensions | .exe, .dll, .sys, .bat, .cmd, and 10 others |
| Self-Deletion Method | Drop DLL with .wasd extension and execute with rundll32.exe |
Why Add Slopoly? The interesting point is that Hive0163 already had multiple powerful backdoors (NodeSnake, InterlockRAT), so why add Slopoly? IBM X-Force believes this was likely a "live-fire exercise"—meaning Hive0163 was testing Slopoly in a real attack to see how well it performs. This shows that ransomware groups are actively experimenting with AI and learning how to use it.
Hive0163 Evolution: This group is rapidly evolving. They've transformed from a traditional ransomware group into a sophisticated organization leveraging the latest technologies (including AI). Their network structure—with multiple subgroups and access to private tools—means they can innovate faster than competitors and respond to new defensive techniques.
🎯 TekinGame Analysis:
Hive0163 represents a new generation of ransomware groups that are not only technically advanced but actively testing and integrating emerging technologies like AI. The use of Slopoly in a real attack shows they're preparing for the future—a future where AI-generated malware is a standard part of their arsenal. Their network structure and access to private developers means Hive0163 can move faster than most competitors. This is a serious threat requiring immediate attention.
⚙️ 4. How AI Attacks Work: From Discovery to Infiltration
To understand why AI-powered attacks are so dangerous, we need to understand exactly how they work. Let's examine the complete process of an AI-assisted attack from start to finish—from target identification to final infiltration and data exfiltration.
Stage 1: Automated Target Discovery: The first step in any cyberattack is finding vulnerable targets. Traditionally, this required manual scanning and result analysis—a time-consuming process that could take days or weeks. But with CyberStrikeAI, this process is fully automated. The tool can automatically scan the internet, identify FortiGate devices with exposed management interfaces, and compile a list of potential targets—all within hours.
Stage 2: AI-Powered Credential Generation: After identifying targets, the next stage is finding a way in. Traditionally, hackers used predefined lists of common passwords. But AI can operate much more intelligently. Large language models can: 1) Analyze password patterns specific to an organization (based on public information, previous breaches, etc.), 2) Generate likely passwords based on company name, industry, and geographic location, 3) Suggest intelligent combinations of words, numbers, and special characters with high success probability.
🔄 Complete AI-Assisted Attack Process
Phase 1: Reconnaissance (hours)
• Automated internet scanning to find targets
• Identify FortiGate devices with exposed management interfaces
• Collect public information about target organization
Phase 2: Credential Attack (minutes to hours)
• Generate likely password list with AI
• Automated brute-force attack
• Test various credentials until finding correct combination
Phase 3: Initial Access (immediate)
• Successful login to management interface
• Create backdoor for persistent access
• Cover tracks (log manipulation)
Phase 4: Malware Deployment (minutes)
• Generate custom malware with AI (like Slopoly)
• Deploy malware on target system
• Create persistence mechanism
Phase 5: Post-Exploitation (days to weeks)
• Lateral movement in network
• Exfiltrate sensitive data
• Prepare for final attack (ransomware)
Stage 3: Smart Brute-Force: After generating the credential list, AI can intelligently execute the brute-force attack. Unlike traditional attacks that test all combinations sequentially, AI can: 1) Learn from previous attempt results and adjust strategy, 2) Adjust attack speed to avoid triggering detection, 3) When a pattern succeeds, prioritize similar patterns. This means the attack is both faster and stealthier.
Stage 4: On-the-Fly Malware Generation: One of AI's most dangerous capabilities is the ability to generate custom malware on demand. After successful infiltration, a hacker can ask a large language model to write a custom backdoor that: 1) Is optimized for the specific operating system and architecture, 2) Uses specific evasion techniques to bypass antivirus, 3) Has specific capabilities needed for this attack. This entire process can take minutes—compared to days or weeks for manual development.
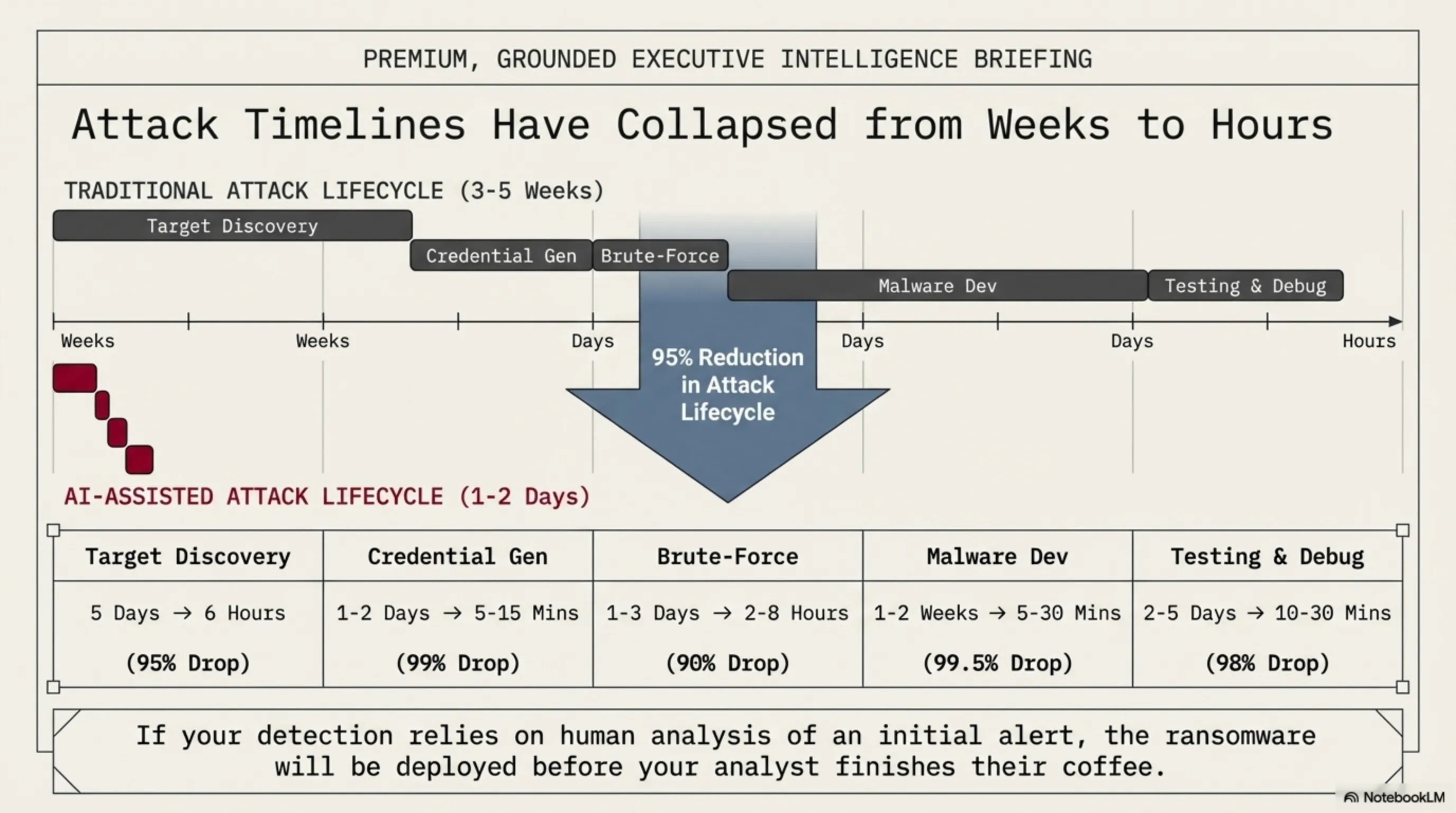
Time Comparison: Let's see how much AI has accelerated the attack process:
⏱️ Time Comparison: Traditional Attack vs AI-Assisted Attack
| Stage | Traditional Attack | AI Attack | Time Reduction |
| Target Discovery | 2-5 days | 2-6 hours | 95% |
| Credential List Generation | 1-2 days | 5-15 minutes | 99% |
| Brute-Force Attack | 1-3 days | 2-8 hours | 90% |
| Custom Malware Development | 1-2 weeks | 5-30 minutes | 99.5% |
| Malware Testing & Debugging | 2-5 days | 10-30 minutes | 98% |
| Total | 3-5 weeks | 1-2 days | 95% |
Why Does This Matter? Reducing time from weeks to days (or even hours) means: 1) Hackers can conduct more attacks, 2) Security teams have less time to detect and respond, 3) Attack costs decrease for hackers, making more attacks economically viable, 4) Even inexperienced hackers can execute sophisticated attacks.
Role of Commercial AI Models: One of the most concerning aspects of these attacks is the use of commercial AI models like Claude and DeepSeek. This means hackers don't even need to build their own models—they just need to buy a subscription (or use stolen API keys) and start. AI companies try to prevent misuse with guardrails and content filters, but as Slopoly demonstrated, these restrictions can be bypassed.
⚡ TekinGame Analysis:
A 95% reduction in attack time is a complete game-changer. This means we can no longer rely on "time to detect and respond"—because that time may not exist. Traditional defenses based on detecting known patterns are useless against AI-generated malware that's different every time. We need a paradigm shift in cybersecurity—from detection-based to prevention-based, from signature-based to behavior-based, and from reactive to proactive. If we don't change now, it will be too late.
🌍 5. Impact on the Security Industry: Why the Rules Have Changed
The discovery of CyberStrikeAI and Slopoly aren't just two separate security incidents—they're signs of a fundamental transformation in the cybersecurity industry. Let's examine how these developments are changing the entire industry and what implications they hold for the future.
The End of Signature-Based Detection: For decades, the security industry has relied on signature-based detection—meaning antiviruses maintain a database of known malware and compare files against it. But with AI-generated malware that's different every time, this method no longer works. Slopoly can be generated with different code each time—meaning there's no fixed "signature" to detect. This means the security industry must move toward behavior-based detection—instead of looking for specific code, we look for suspicious behavior.
The Attribution Problem: One of the core pillars of threat intelligence is attribution—determining which group or country is behind an attack. But with AI-generated malware, attribution becomes much harder. Traditionally, security researchers used unique code characteristics (like programming style, comments, etc.) to identify developers. But when code is AI-generated, these unique characteristics don't exist—all AI code has a similar style. This means we may not be able to determine who's behind an attack.
📉 Impacts on the Cybersecurity Industry
| Area | Impact | Status |
| Traditional Antivirus | Severe effectiveness decline against AI malware | Critical |
| Threat Intelligence | Attribution and pattern identification problems | Concerning |
| SOC Teams | Increased alert volume and reduced response time | Critical |
| Incident Response | Need for new skills to analyze AI attacks | Moderate |
| Penetration Testing | Competition with automated AI tools | Concerning |
| Security Training | Need for complete curriculum overhaul | Moderate |
| Compliance & Regulations | Current laws insufficient for AI threats | Concerning |
Rising Defense Costs: As attacks become more sophisticated, defense costs increase. Companies must: 1) Invest in more advanced tools (like EDR, XDR, and AI-powered SIEM), 2) Hire larger and more skilled security teams, 3) Provide continuous employee training, 4) Invest in threat intelligence and incident response. According to Gartner estimates, cybersecurity costs for medium to large companies increased approximately 40-60% in 2026 compared to 2024.
The Skills Gap: The cybersecurity industry already faced a shortage of skilled professionals—and now with the emergence of AI threats, this gap has worsened. Security teams need to: 1) Understand how AI models work, 2) Identify and analyze AI-generated malware, 3) Use defensive AI tools, 4) Be familiar with new attack techniques. But professionals with these skills are scarce, and demand for them is extremely high.
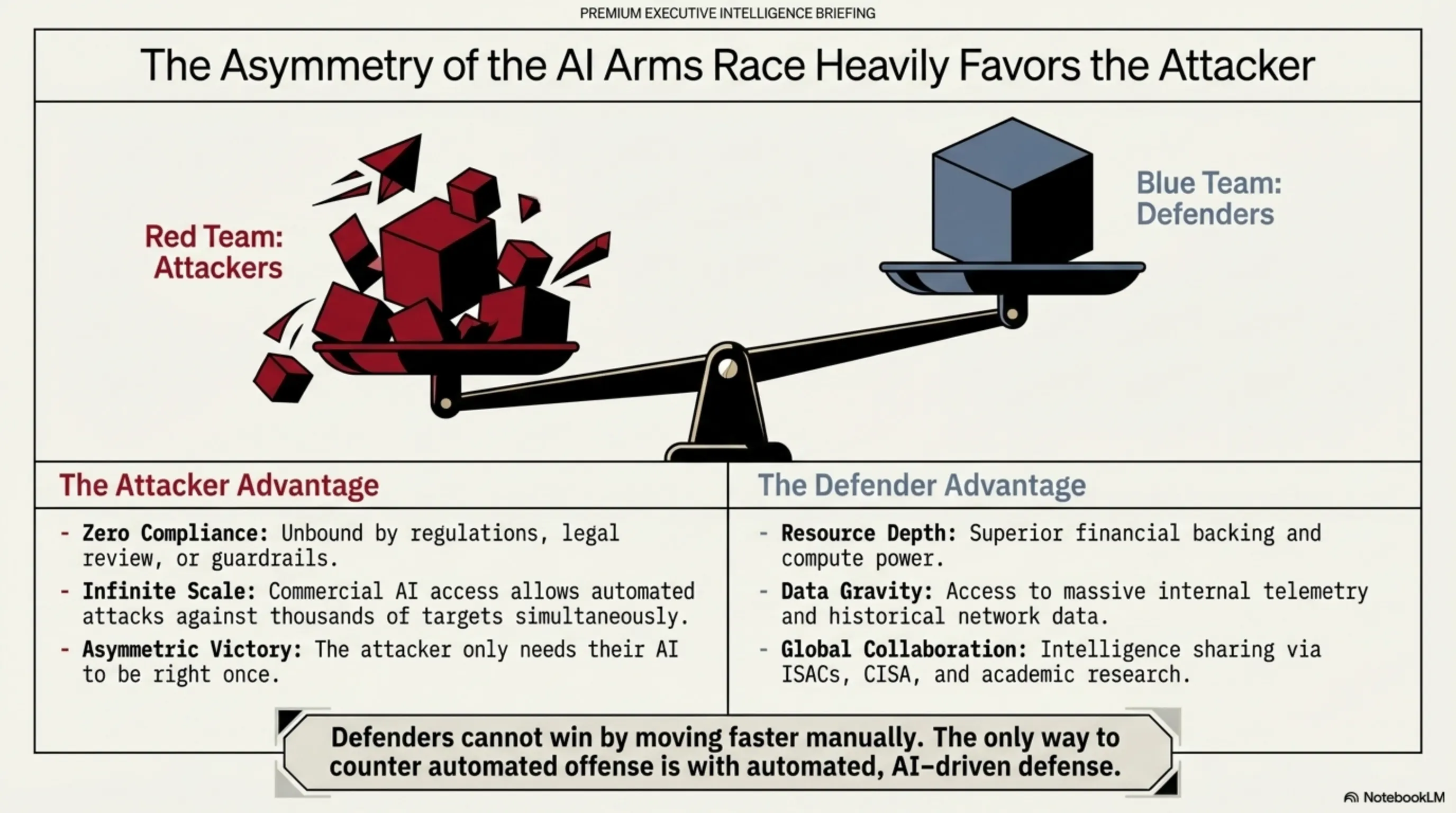
The AI Arms Race: We've entered an AI arms race—hackers use AI to attack, and defenders must use AI to defend. This means: 1) Security companies are rapidly developing AI-powered tools, 2) Investment in security AI has increased dramatically, 3) Competition to hire AI experts has intensified, 4) Academic research on security AI is growing rapidly. But the question is: Can defenders keep pace with attackers?
⚔️ AI Arms Race: Attackers vs Defenders
🔴 Attacker Advantages
- More flexibility - no compliance requirements
- Can use commercial models
- Only need to succeed once
- Can take more risks
- Access to open-source tools
🟢 Defender Advantages
- More financial resources (large companies)
- Access to more data
- International cooperation
- Government support
- Academic research
Impact on Small Businesses: One of the most concerning aspects of these developments is their impact on small and medium businesses (SMBs). These companies typically have less budget and resources for cybersecurity and can't invest in advanced tools and expert teams. With the democratization of AI attack tools, SMBs become easier targets. This can lead to: 1) Dramatic increase in attacks on SMBs, 2) Bankruptcy of small companies after ransomware attacks, 3) Increased cyber insurance costs, 4) Decreased customer trust in small businesses.
Role of Governments and Legislation: Governments and regulatory bodies are responding to these threats, but the pace of legislation is much slower than the pace of technological evolution. Some ongoing actions: 1) The European Union is drafting new laws for security AI, 2) The US is considering export restrictions on powerful AI models, 3) China has strict regulations for AI use, 4) International organizations like Interpol are increasing cooperation to combat AI cybercrime. But the question is: Are these actions sufficient?
🌐 TekinGame Analysis:
We're at a historic turning point in cybersecurity. The rules have changed, and traditional methods no longer work. The security industry must rebuild itself for this new reality—from tools and techniques to skills and strategies. Companies that adapt faster will survive. Companies that cling to old methods will become victims. This is a warning for all of us: Either change, or perish.
🛡️ 6. Defense Solutions: How to Protect Ourselves
Now that we understand the threat we're facing, let's see how we can protect ourselves. The good news is that despite the complexity of threats, there are practical and effective solutions that can dramatically reduce risk.
1. Immediate MFA (Multi-Factor Authentication) Activation: The first and most important step is enabling multi-factor authentication on all sensitive systems—especially management interfaces. The CyberStrikeAI attack only succeeded because FortiGate devices were protected only by username/password. With MFA, even if a hacker finds the password, they can't log in without the second factor (like SMS code, authenticator app, or security key). This is a powerful defensive wall that makes brute-force attacks useless.
⚡ Immediate Actions (Must Be Done Right Now)
- Enable MFA: On all management interfaces, VPNs, and sensitive systems
- Close Management Interfaces: Management interfaces shouldn't be accessible from the public internet - only via VPN or specific IPs
- Change Weak Passwords: Any password less than 12 characters or simple must be changed immediately
- Review Logs: Check access logs from the past 60 days - look for suspicious login attempts
- Urgent Updates: Update all systems, firewalls, and software to the latest version
- Offline Backup: Take a complete backup of sensitive data and keep it offline (disconnected from network)
2. Implement Zero Trust Architecture: The Zero Trust security model is based on the principle that "nothing and no one is trusted"—even if inside the network. This means: 1) Every access must be authenticated and authorized, 2) Access should be limited to the minimum necessary (principle of least privilege), 3) Network traffic must be continuously monitored and analyzed, 4) Network segmentation to prevent lateral movement. With Zero Trust, even if a hacker gains access to one system, they can't easily access other systems.
3. Use Defensive AI: To fight offensive AI, we must use defensive AI. Modern security tools like EDR (Endpoint Detection and Response) and XDR (Extended Detection and Response) use machine learning to identify suspicious behaviors—even if the malware is new and unknown. These tools can: 1) Identify unusual patterns, 2) Automatically respond to threats, 3) Use historical data to predict future attacks, 4) Reduce false positives.
🏰 Defense Layers (Defense in Depth)
| Layer | Solutions | Priority |
| Perimeter | Firewall, IPS/IDS, WAF, DDoS Protection | Critical |
| Network | Segmentation, VPN, Zero Trust, Network Monitoring | Critical |
| Endpoint | EDR, Antivirus, Patch Management, Device Control | High |
| Application | Secure Coding, WAF, API Security, Input Validation | High |
| Data | Encryption, DLP, Backup, Access Control | Critical |
| Human | Security Awareness, Phishing Simulation, MFA | Critical |
4. Continuous Employee Training: Humans are always the weakest link in the security chain. The ClickFix attack used by Hive0163 relied entirely on social engineering—tricking users into executing malicious code. Continuous employee training can reduce this risk: 1) Training to identify phishing emails, 2) Awareness of new social engineering techniques like ClickFix, 3) Attack simulation exercises, 4) Building a security culture in the organization. Remember: The best firewall in the world can't protect against a deceived user.
5. Monitoring & Incident Response: Having a 24/7 monitoring system and a ready incident response team can be the difference between a small attack and a major disaster. This includes: 1) SIEM (Security Information and Event Management) for collecting and analyzing logs, 2) SOC (Security Operations Center) for continuous monitoring, 3) Written and practiced Incident Response Plan, 4) Threat Intelligence for awareness of new threats. With Slopoly having access for over a week, a good monitoring system could have detected it much earlier.
6. Active Threat Hunting: Instead of waiting for alerts to trigger, we should actively search for hidden threats. Threat Hunting means: 1) Regular log review for suspicious patterns, 2) Searching for new Indicators of Compromise (IOCs), 3) Analyzing user and system behavior, 4) Examining anomalies and deviations from baseline. With AI threats that can be very stealthy, active threat hunting is essential.
💰 Security Budget Guide (By Organization Size)
| Size | Annual Budget | Investment Priorities |
| Small (1-50 people) |
$10K-50K | MFA, Backup, Antivirus, Employee Training |
| Medium (50-500 people) |
$50K-500K | EDR, SIEM, Advanced Firewall, External SOC |
| Large (500+ people) |
$500K-5M+ | XDR, Internal SOC, Threat Intelligence, Zero Trust |
7. Collaboration and Information Sharing: No organization can face AI threats alone. Collaboration and information sharing are essential: 1) Membership in industry ISACs (Information Sharing and Analysis Centers), 2) Sharing IOCs with other organizations, 3) Cooperation with government and law enforcement agencies, 4) Participation in the cybersecurity community. The faster information about new threats is disseminated, the better we can protect ourselves.
8. Continuous Testing and Assessment: Security is a continuous process, not a one-time project. We must regularly: 1) Conduct Penetration Testing, 2) Run Vulnerability Assessments, 3) Have Red Team / Blue Team Exercises, 4) Practice the Incident Response Plan. These tests help identify weaknesses before hackers find them.
✅ Final Checklist: Is Your Organization Ready?
☐ MFA is enabled on all sensitive systems
☐ Management interfaces are not accessible from the public internet
☐ All passwords are strong and unique
☐ We have an offline and tested backup system
☐ EDR or XDR is installed on all endpoints
☐ SIEM is implemented for log monitoring
☐ Employees receive regular security training
☐ We have a written and practiced Incident Response Plan
☐ Regular patch management is performed
☐ Network segmentation is implemented
☐ We have threat intelligence for awareness of new threats
☐ Annual penetration testing is conducted
If you checked fewer than 8 items, your organization is at serious risk!
🛡️ TekinGame Final Analysis:
Defense against AI threats is neither impossible nor too expensive—it just requires the right approach. Most successful attacks (including CyberStrikeAI) succeeded because basic security principles weren't followed—MFA wasn't enabled, passwords were weak, management interfaces were open. If we follow these basic principles, we can neutralize 90% of attacks. For the remaining 10%, we need more advanced tools and expert teams. But the good news is that with reasonable investment and proper planning, any organization can protect itself. Start today—tomorrow might be too late.
🎯 Conclusion: The Future of Cybersecurity in the AI Era
The discovery of CyberStrikeAI and Slopoly marks a watershed moment in cybersecurity history. We're no longer dealing with human hackers using simple tools—we're facing autonomous AI systems that can attack 24/7 without fatigue, generate custom malware in minutes, and identify and exploit vulnerabilities at speeds previously impossible.
But this isn't the end of the world. It's a warning—one we must take seriously. AI threats are real, but defensive solutions exist. By following basic security principles (MFA, strong passwords, closing unnecessary interfaces), using modern tools (EDR, SIEM, defensive AI), and continuous employee training, we can protect ourselves.
The key point is that cybersecurity is no longer an optional expense—it's a vital necessity for the survival of any organization. Companies that don't invest in security are gambling with their survival. And with AI threats, the odds of losing are very high.
🔮 Future Predictions (2026-2028)
- Late 2026: AI-generated malware goes mainstream - 30-40% of new attacks
- 2027: Emergence of first fully autonomous malicious "AI Agents"
- Late 2027: Governments begin passing strict regulations for security AI
- 2028: Defensive AI becomes industry standard - can't defend without AI
- Late 2028: Formation of a full "AI arms race" between attackers and defenders
The future of cybersecurity depends on two factors: 1) The pace of defensive AI evolution - can we move fast enough? 2) Global cooperation - can countries and companies work together to face this threat? If the answer to both questions is "yes," we can win this race. If not, the future will be dark.
⚠️ Final Message
This is not a drill. AI threats are real and spreading rapidly. If you think your organization is too small or insignificant to be targeted, you're wrong. With automated AI tools, hackers can attack thousands of targets simultaneously—size doesn't matter. Start today. Enabling MFA, closing unnecessary interfaces, and training employees can save your digital life.
📚 Useful Resources and Links
- The Hacker News - Latest cybersecurity news
- IBM X-Force - Threat intelligence reports
- Fortinet Security Advisories - FortiGate security alerts
- CISA - US Cybersecurity Agency
- OWASP - Application security guides
🛡️ Stay Safe, Stay Vigilant
Cybersecurity is everyone's responsibility. From senior executives to regular employees, from large corporations to small businesses—we all must be vigilant, get trained, and take necessary actions. The future of digital security depends on the decisions we make today. The choice is yours: Be prepared or become a victim.