⚠️ 1. CPUID Breach: CPU-Z and HWMonitor Distributed STX RAT for 6 Hours
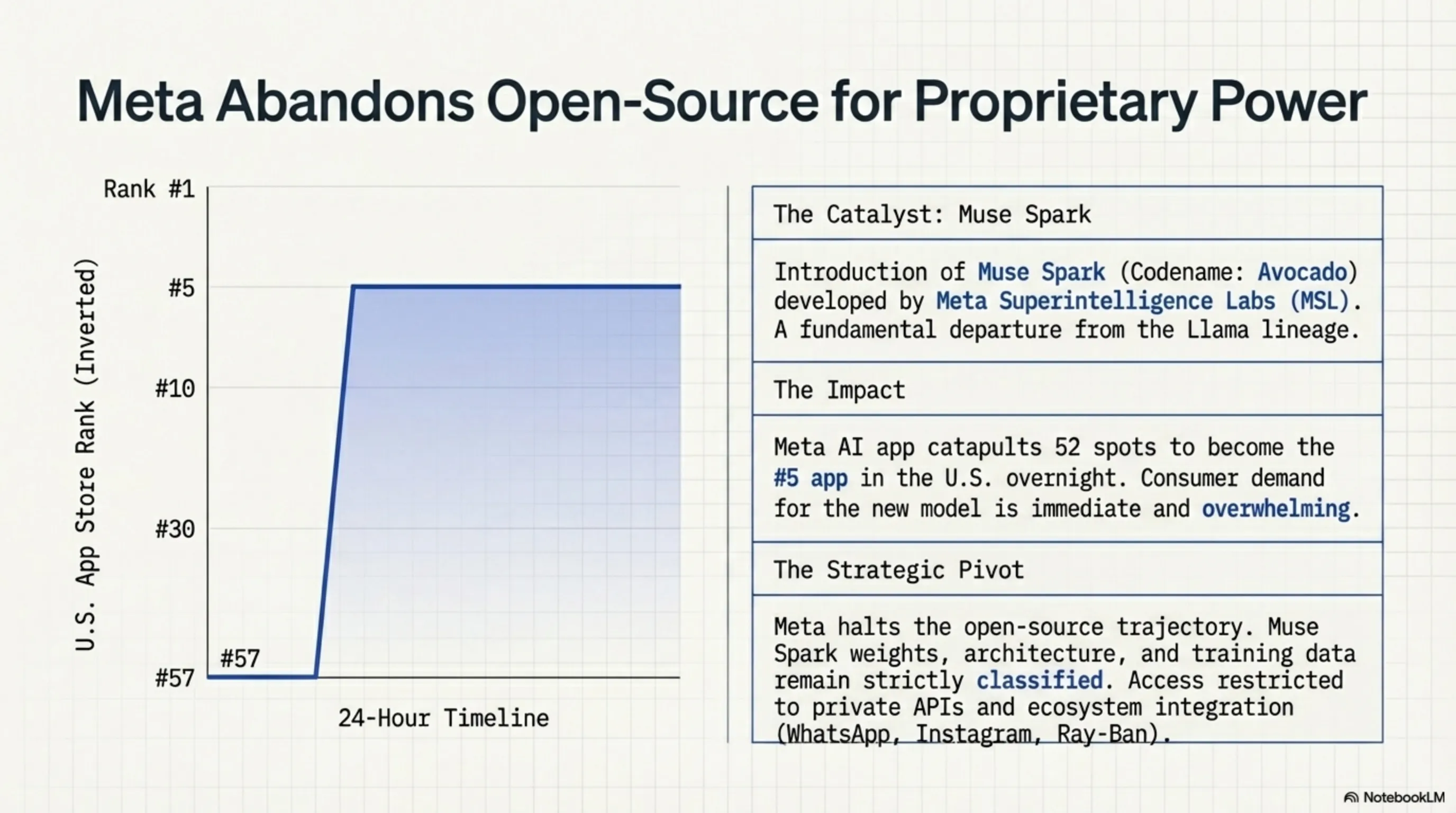
If you downloaded CPU-Z or HWMonitor from the official CPUID website between April 9-10, you likely have a remote access trojan on your system right now. This is one of the most dangerous supply chain attacks of 2026 - not because of technical sophistication, but because it targeted one of the world's most popular hardware monitoring tools. CPUID confirmed that unknown threat actors compromised a secondary API and modified download links on the main site for approximately 6 hours to serve trojanized versions instead of legitimate files.
How did it work? According to Kaspersky's analysis, attackers redirected download links to three malicious domains: cahayailmukreatif.web[.]id, pub-45c2577dbd174292a02137c18e7b1b5a.r2[.]dev (Cloudflare R2 infrastructure), and transitopalermo[.]com. These sites served malicious ZIP archives and installers containing a legitimate signed executable (to fool users) and a malicious DLL named CRYPTBASE. When users ran the installer, the malicious DLL loaded instead of the Windows system library - a technique called DLL side-loading that allows malware to execute without triggering antivirus software.
What is STX RAT and why is it dangerous? STX is a full-featured remote access trojan that gives attackers complete control over infected systems. It can record keystrokes, capture screenshots, steal files, and even serve as a platform for installing additional malware. What makes STX special is its design to evade detection: it uses encryption for C2 communications, can masquerade as a legitimate Windows process, and has anti-analysis capabilities that detect execution in sandboxes or virtual machines.
⏱️ Attack Timeline
Why was this attack so successful? Several key factors: First, CPUID is a trusted source - millions of users download from the official site without thinking twice. Second, the malicious files included the legitimate signed executable, meaning even if users checked the certificate, everything looked legitimate. Third, the use of DLL side-loading meant most antivirus software saw nothing suspicious. And fourth, 6 hours was enough time for thousands of downloads - especially since CPU-Z is one of the first tools overclockers and hardware enthusiasts download after installing Windows.
Who is at risk? If you downloaded CPU-Z or HWMonitor between April 9 at 15:00 UTC and April 10 at 10:00 UTC, you should take immediate action. CPUID emphasized that the original signed files were not affected - only new downloads from the site during that time window were infected. To check, you can compare the hash of your downloaded file with the official hashes CPUID published. If you're suspicious, the best course of action is to run a full system scan with multiple antivirus programs and consider changing sensitive passwords.
📊 Attack Impact
| Compromise Duration | ~6 hours |
| Affected Tools | CPU-Z, HWMonitor, HWMonitor Pro |
| Malware Type | STX RAT (Remote Access Trojan) |
| Attack Technique | DLL Side-Loading |
Why are supply chain attacks so dangerous? These attacks target the software supply chain instead of directly targeting users. When a trusted source like CPUID is compromised, users have no reason to be suspicious - they're downloading from an official site, the certificate is valid, and everything looks legitimate. This is what made the infamous SolarWinds and Kaseya attacks so devastating. And with the increasing complexity of software supply chains - third-party APIs, CDNs, and cloud services - the attack surface keeps growing larger.
🔍 Tekin Analysis:
This attack is a wake-up call for the entire software industry. CPUID is a reputable company with widely-trusted tools, yet even they couldn't prevent a 6-hour compromise. The fact that attackers could exploit a secondary API shows that security is only as strong as the weakest link in the chain. For users, the lesson is clear: even when downloading from official sources, you must be vigilant. Hash verification, updated antivirus, and system behavior monitoring are no longer optional - they're essential. For developers, this is a reminder that every endpoint, every API, and every integration is a potential attack vector. Zero trust architecture isn't a buzzword anymore - it's a survival necessity. Expect to see more supply chain attacks - attackers are learning that the easiest way to compromise thousands of targets is to attack one trusted source.
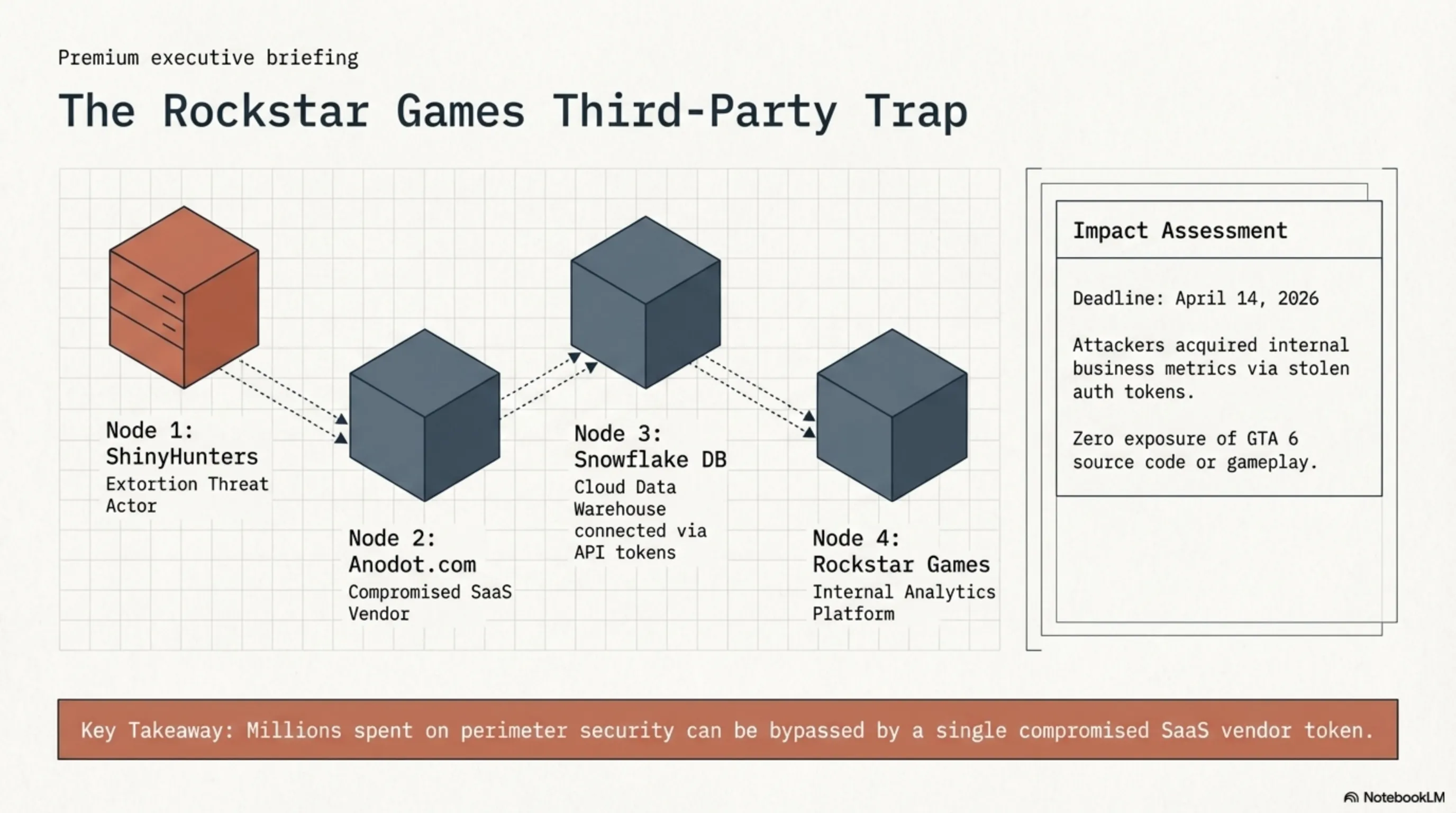
🎮 2. ShinyHunters vs Rockstar: GTA 6 Ransom with April 14 Deadline
Notorious hacker group ShinyHunters posted a ransom message on the dark web targeting Rockstar Games, claiming access to sensitive data related to GTA 6. The attackers set a hard deadline of April 14, 2026, threatening not only to leak data but also to cause "annoying digital problems" if Rockstar doesn't pay. But before you panic: Rockstar confirmed this was a limited breach through a third-party vendor and has had no impact on GTA 6 development or player data.
How did it happen? According to cybersecurity reports, this wasn't a direct attack on Rockstar's servers. Instead, attackers targeted a third-party vendor called Anodot - a SaaS platform providing analytics and cloud monitoring services. Anodot connects with Snowflake-based data warehouses that store enterprise-level analytics data. Through this ecosystem, attackers allegedly accessed connected systems without directly breaching Rockstar's infrastructure. This is a textbook supply chain attack - where weak vendor security can open doors to major companies.
What data was exposed? According to Rockstar, only "a limited amount of non-material company information" was exposed. This likely includes internal analytics data such as performance metrics, operational dashboards, and business reporting data. This type of data helps companies track sales trends and internal performance, but doesn't include gameplay content. Importantly, no source code, unfinished builds, or story-related materials have been confirmed as compromised. This significantly reduces fears of spoilers or early leaks for GTA 6 fans.
🎭 ShinyHunters Profile
History: ShinyHunters is one of the most active hacker groups in recent years, responsible for major breaches of companies like Microsoft, AT&T, and Ticketmaster.
Expertise: Exploiting third-party vendors, credential theft, and selling stolen data on dark web marketplaces.
Tactics: Typically use stolen authentication tokens to access cloud systems, without needing password cracking or direct hacking.
Motivation: Primarily financial - either through ransom or selling data to the highest bidder.
What did the ransom message say? ShinyHunters wrote: "Rockstar Games, your Snowflake instances were compromised thanks to Anodot.com. Pay or leak. This is a final warning to reach out by April 14, 2026 before we leak, along with several annoying (digital) problems that'll come your way. Make the right decision, don't be the next headline." This dual threat - both data leak and "digital problems" - suggests attackers may have plans beyond just disclosure, possibly including DDoS attacks or other disruptions.
How did Rockstar respond? The company acted quickly and decisively. In an official statement, Rockstar said: "We can confirm that a limited amount of non-material company information was exposed in connection with a third-party data breach. This incident has no impact on our organization or our players." The company also emphasized that core systems for Grand Theft Auto VI remain secure and unaffected. Rockstar is working with external cybersecurity experts to strengthen IT security and cooperating with law enforcement.
⏱️ Incident Timeline
Will GTA 6 be delayed? Good news: there's no indication this incident will affect the Grand Theft Auto VI release timeline. Rockstar emphasized the breach involves non-material internal data and doesn't affect development systems. Experts also suggest modern AAA studios like Rockstar isolate production pipelines from analytics platforms, minimizing risk. As of now, the GTA 6 launch timeline remains unchanged, and no delay is expected from this cybersecurity incident.
🎯 Tekin Analysis:
This incident is a textbook example of why third-party vendor security matters. Rockstar likely spends millions on cybersecurity, but all that investment can be undermined by a vendor with weak security. The fact that ShinyHunters could access Rockstar data through Anodot shows that the cybersecurity supply chain is only as strong as its weakest link. For gamers, the good news is GTA 6 appears safe - no source code, assets, or spoilers are exposed. For the industry, this is a bitter reminder that even gaming giants are vulnerable. Expect Rockstar and other major studios to intensify their vendor security assessments. And for ShinyHunters? They may not have much to sell this time, but the message is clear: no one is out of reach.
🔓 3. Adobe Emergency Patch: CVE-2026-34621 Under Active Exploitation
Adobe today released emergency updates to fix a critical security flaw in Acrobat Reader that's under active exploitation in the wild. The vulnerability, assigned CVE-2026-34621, carries a CVSS score of 8.6 out of 10.0. Successful exploitation could allow an attacker to execute malicious code on affected installations. This means if you have Acrobat Reader and haven't updated yet, your system is at immediate risk - especially if you regularly open PDFs from unknown sources.
What is CVE-2026-34621? Adobe hasn't disclosed full technical details (a common tactic to limit further exploitation), but based on the CVSS score and description, this is likely a remote code execution (RCE) vulnerability. These types of flaws allow attackers to run arbitrary code on a victim's system, typically through a specially crafted PDF file. The user just needs to open the file - after that, the attacker can install malware, steal data, or take complete control of the system.
Why is this so dangerous? Three reasons: First, Acrobat Reader is one of the world's most widely used software applications - hundreds of millions of installations across Windows, macOS, and mobile systems. Second, PDFs are everywhere - emails, web downloads, work documents. Users are conditioned to open PDFs without thinking. Third, and most importantly, this vulnerability is currently under active exploitation. This means attackers are already using it - this isn't a theoretical threat, it's an active and immediate danger.
🔍 Vulnerability Details
| CVE ID | CVE-2026-34621 |
| CVSS Score | 8.6 / 10.0 (Critical) |
| Vulnerability Type | Remote Code Execution (RCE) |
| Affected Products | Adobe Acrobat Reader (All Platforms) |
| Exploitation Status | Under Active Exploitation in Wild |
| Attack Vector | Malicious PDF File |
How is it exploited? The typical pattern for PDF vulnerability exploitation: an attacker creates a specially crafted PDF file containing a malicious payload. This file is usually distributed via phishing emails, malicious web downloads, or even malvertising. When the victim opens the file with Acrobat Reader, the vulnerability triggers and allows the attacker to execute arbitrary code. Depending on the attacker's goal, this could include installing ransomware, stealing credentials, or creating a backdoor for persistent access.
Who is at risk? Anyone using Adobe Acrobat Reader who hasn't installed the emergency patch yet. This is especially concerning for enterprise environments where employees regularly receive PDFs from external sources - contracts, invoices, reports. A targeted phishing campaign could use this vulnerability to compromise entire networks. Even home users are at risk if they download PDFs from unknown sources or open suspicious emails.
How did Adobe respond? The company released emergency updates for all affected versions of Acrobat Reader. These patches are available through Adobe's automatic update system, but users should immediately check they have the latest version. For organizations, Adobe recommends IT admins immediately deploy the patch across the network. The company is also working with security researchers and law enforcement to track active exploitation and protect users.
⚡ Immediate Actions
- Update Immediately: Open Adobe Acrobat Reader, go to Help > Check for Updates and install the latest patch.
- Don't Open Unknown PDFs: Until you're certain your system is patched, avoid opening PDFs from unknown or suspicious sources.
- Enable Antivirus: Ensure your antivirus is updated and active - it can provide an additional defensive layer against malicious PDFs.
- Train Employees: If you're an IT admin, immediately send a security alert to users and educate them about suspicious PDF risks.
- Consider Alternatives: If you can't patch immediately, temporarily use alternative PDF readers until you update.
Why is Adobe always a target? Acrobat Reader, due to its widespread adoption and complexity, is a favorite target for security researchers and attackers alike. The PDF format itself is highly complex - supporting JavaScript, interactive forms, embedded media, and other features that are all potential attack vectors. Adobe has been trying for years to reduce the attack surface, but with billions of PDFs in circulation and the need for backward compatibility, it's an ongoing challenge. This new vulnerability is a reminder that even widely-used and well-maintained software can still have critical flaws.
🛡️ Tekin Analysis:
This is one of those "drop everything and patch now" moments. Active exploitation means attackers are already using this vulnerability - this isn't a theoretical threat. For regular users, the message is simple: update immediately and avoid opening unknown PDFs until then. For organizations, this is a priority-one incident - IT teams should drop everything and deploy the patch across the network. The fact that Adobe had to release an emergency patch shows how serious this is. Expect to see more exploitation reports in the coming days - attackers know they have a short window before everyone patches. For Adobe, this is a bitter reminder that security is an endless race. And for all of us, it's a lesson in the importance of timely patch management.
📈 4. Perplexity AI: 50% Revenue Growth with Pivot to AI Agents
Perplexity AI recorded one of the most impressive financial growths in AI startup history: 50% revenue growth in just one month. This surge pushed the company's annual recurring revenue (ARR) past $450 million in March 2026. This explosive growth was the result of a bold strategic decision: pivoting from a simple AI search engine to a full AI agent platform, coupled with a usage-based pricing model that charges users for queries beyond a set limit. This is a defining moment for Perplexity - and a clear signal that the AI market is moving from simple chatbots to autonomous agents that can complete complex tasks.
What changed? Perplexity recently introduced "Computer" - an AI agent designed to complete tasks, not just answer questions. Unlike Perplexity's traditional search engine that only provided information, Computer can perform actions like booking reservations, online shopping, scheduling appointments, and even multi-step deep research. This shift from "answer engine" to "action engine" is a fundamental change in value proposition. Users no longer just ask for information - they want AI to do the work for them.
What's the new pricing model? Perplexity moved from a simple subscription model to a hybrid usage-based system. Users receive a set number of credits, and queries beyond that limit incur additional charges. This model allows Perplexity to monetize power users who heavily rely on AI agents, while casual users can still use it for free or at low cost. This is a similar tactic to what OpenAI did with API pricing - and it's clearly working. The 50% revenue growth in one month shows users are willing to pay for truly useful AI agents.
📊 Perplexity Growth Metrics
| Monthly Revenue Growth | +50% |
| ARR (March 2026) | $450M+ |
| Valuation (Latest Round) | $20B |
| Primary Growth Driver | AI Agents + Usage Pricing |
| Main Competitors | OpenAI, Anthropic, Cursor |
Why are AI agents so hot? The AI industry is moving from "impressive demos" to "actual utility." Users are no longer impressed by chatbots that can write poetry or answer trivia questions - they want AI that actually does work for them. AI agents deliver on this promise: they can interact with multiple services, make complex decisions, and complete multi-step tasks without human intervention. This is a shift from "AI as a tool" to "AI as a coworker" - and the market is showing it's willing to pay for this capability.
How does Perplexity compare to competitors? With ARR exceeding $450 million, Perplexity still trails giants like OpenAI (multi-billion dollar ARR) and Anthropic, but it's rapidly closing the gap. What sets Perplexity apart is its focus on search and research - domain expertise that OpenAI and Anthropic focus less on. Perplexity also benefits from being a "pure-play" AI company, without legacy businesses to worry about. This agility allows it to pivot and experiment faster than larger competitors.
What are the challenges? Despite all this growth, Perplexity faces significant challenges. First, competition is fierce - OpenAI, Google, Anthropic, and dozens of other startups are all pursuing AI agents. Second, unit economics are still unclear - can Perplexity be profitable with high inference costs? Third, trust and safety are major concerns - when AI agents are conducting real transactions, mistakes can have real consequences. And fourth, regulatory scrutiny is increasing - especially around privacy, data usage, and accountability.
🏆 AI Agents Competitive Landscape
OpenAI: ChatGPT with plugins and GPT Store - largest user base but less focused on agents
Anthropic: Claude with Computer Use - powerful but limited to 52 organizations for safety concerns
Cursor: AI coding agent - dominant in developer tools but niche market
Perplexity: Search-first agent - differentiated positioning with focus on research and information gathering
Google: Gemini with deep integration - distribution power but slower due to legacy concerns
What does the future look like? If Perplexity can maintain this momentum, it could become one of the major players in the AI agent era. The company is already working with enterprise customers and offering API access to select partners. The next step is likely expansion into more verticals - healthcare, legal, finance - where AI agents can create significant value. But to succeed, Perplexity must get several things right: reliability (agents must work), safety (errors must be minimized), and trust (users must feel comfortable delegating to AI).
💡 Tekin Analysis:
Perplexity's 50% revenue growth in one month is a clear signal: the market is ready for AI agents. This is no longer about cool chatbots - it's about tools that actually get work done. Perplexity's pivot to agents and usage-based pricing is a masterclass in product-market fit: they identified a real need, built a solution, and found a monetization model that works. For the AI industry, this is a turning point. We're moving from the era of "AI as a novelty" to "AI as a utility." Companies that can build reliable, safe, and useful AI agents will be the big winners of the next decade. Perplexity has shown with this growth that they're one of the serious contenders. But the race has just begun - and competition is only getting fiercer.
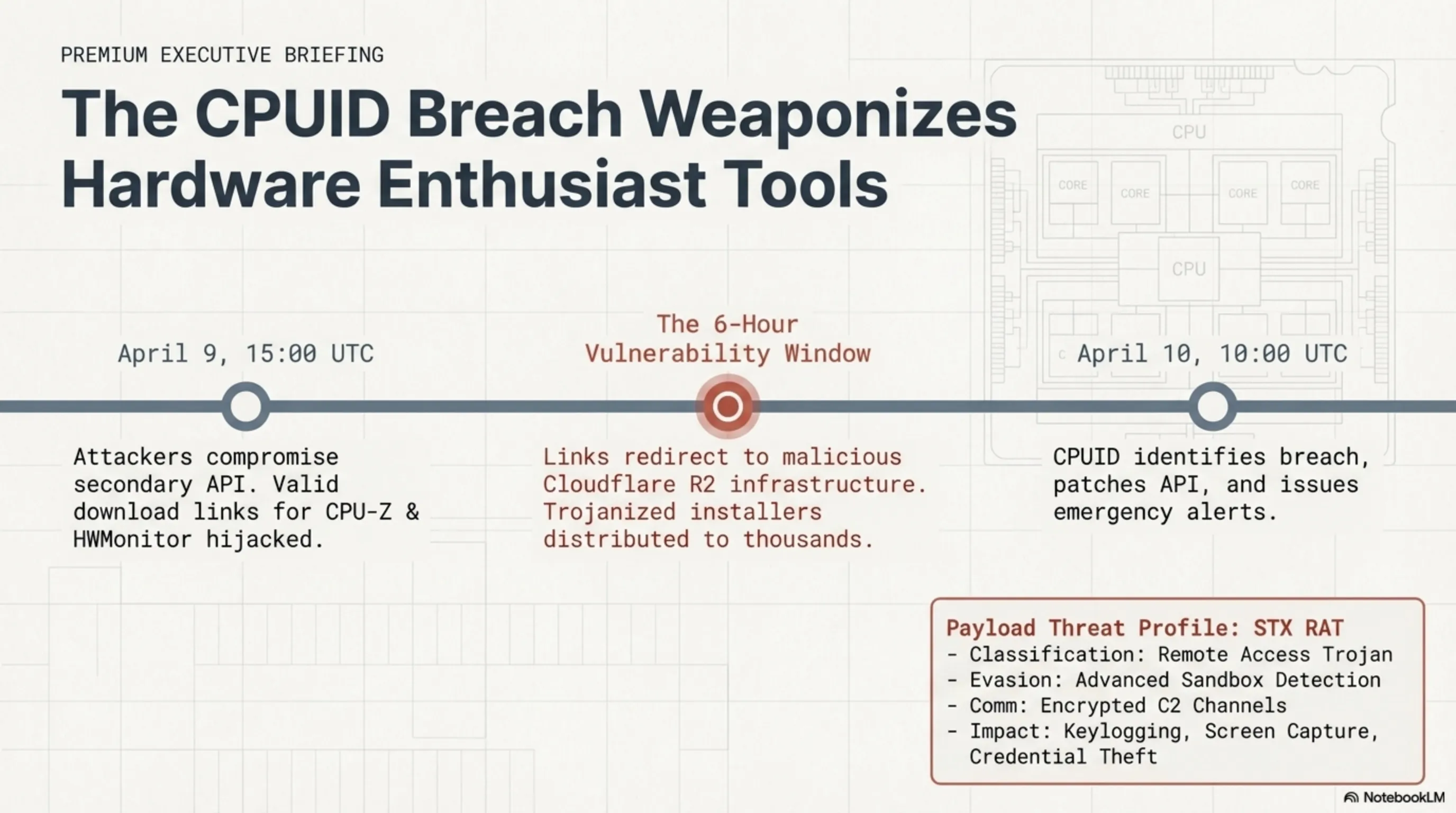
🤖 5. Meta Muse Spark: First Closed-Source Model Jumps from Rank 57 to 5
Meta today unveiled Muse Spark - its first major closed-source AI model and a radical departure from its open-source strategy of recent years. This model, built by Meta Superintelligence Labs (MSL) under Alexandr Wang's leadership, was internally codenamed "Avocado" and isn't an iteration on the Llama family - it's an entirely new architecture. The impact was immediate: the Meta AI app jumped from rank 57 to rank 5 on the U.S. Apple App Store, showing users genuinely want to try this new model. This is a defining moment for Meta - and a signal that the AI war is entering a new phase.
What is Muse Spark? According to Meta, this is "our most powerful model yet." It currently powers the Meta AI app and website, and will roll out to WhatsApp, Instagram, Facebook, Messenger, and AI glasses in the coming weeks. Meta is also offering the model in private preview via API to select partners. What sets Muse Spark apart is that Meta hasn't released any weights, architecture, or training methodology - a complete change from Llama which was fully open-source. This is a strategic bet: Meta is wagering that a powerful proprietary model can create more value than open-source goodwill.
Why did Meta move away from open-source? Several factors likely drove this decision. First, competitive pressure: OpenAI, Anthropic, and Google all have powerful proprietary models generating significant revenue. Llama, for all its success, doesn't directly make money for Meta. Second, control: by keeping Muse Spark closed, Meta can precisely control how it's used, who has access, and how it's monetized. Third, differentiation: with a proprietary model, Meta can offer unique features that competitors can't easily copy. And fourth, regulatory concerns: open-source models can be used for malicious purposes, and Meta likely wants to avoid regulatory scrutiny.
⚖️ Llama vs Muse Spark
| Llama (4 & 5) | Muse Spark | |
|---|---|---|
| Strategy | Open-Source | Closed-Source |
| Access | Free for Everyone | Private Preview API |
| Architecture | Published | Confidential |
| Leadership | Meta AI Research | Alexandr Wang / MSL |
| Goal | Ecosystem Building | Direct Competition |
Who is Alexandr Wang? Wang was the founder and former CEO of Scale AI - a data labeling company that became one of the critical infrastructures for training AI models. Meta hired him in a $14.3 billion deal in 2025 and gave him responsibility for Meta Superintelligence Labs. Wang has a proven track record in building AI systems at scale, and Muse Spark is the first major product under his leadership. The fact that Meta was willing to spend billions to bring Wang shows how serious they are about winning the AI race.
How's the performance? Meta claims Muse Spark significantly narrows the performance gap with models from OpenAI, Anthropic, and others. While exact benchmarks haven't been published, early user feedback shows the model is strong in reasoning, code generation, and multimodal understanding. The app's jump from rank 57 to 5 shows users are feeling the difference - this isn't just hype, it's real improvement. But the question remains: can Muse Spark truly compete with GPT-5, Claude Opus, or Gemini Ultra? Only time will tell.
What's the impact on Meta's ecosystem? Muse Spark will integrate into all Meta platforms - WhatsApp, Instagram, Facebook, Messenger, and even Ray-Ban Meta glasses. This means billions of users will soon have access to a powerful AI assistant embedded directly in the apps they use daily. This could be a game-changer: instead of going to a separate website or app for AI, users can just use Meta AI right where they are. This kind of seamless integration is a major advantage over standalone AI apps.
📱 App Store Impact
Before Muse Spark: Meta AI app at rank 57 U.S. App Store - a mediocre presence without significant traction
After Muse Spark (April 8): Jump to rank 5 - a 52-rank increase in less than 24 hours
Reason: Users want to try the new model and see how it compares to ChatGPT, Claude, and Gemini
Implication: Meta is now a serious contender in the consumer AI market, not just a me-too player
What challenges and questions remain? Despite all the excitement, several big questions remain. First, can Meta succeed with closed-source after years of evangelizing open-source? This could be seen as hypocritical. Second, can Muse Spark truly compete with OpenAI and Anthropic's best models, or is this just incremental improvement? Third, how will Meta monetize this? API pricing? Premium subscriptions? Advertising? And fourth, what impact will this have on Llama? Will Meta continue open-source development, or will all resources go to Muse?
🎯 Tekin Analysis:
Muse Spark is a turning point for Meta. After years of trying to compete in AI with an open-source strategy, Meta is trying a different approach: building a world-class proprietary model that can directly compete with OpenAI and Anthropic. The jump from rank 57 to 5 on the App Store shows users are genuinely excited - this isn't just Meta hype. But the real question is: can Muse Spark maintain this momentum? Can it truly compete with GPT and Claude? And can Meta turn this into a sustainable business? For Alexandr Wang, this is a defining moment - the first major product under his leadership. For Meta, this is a billion-dollar bet that closed-source is the way forward. And for the AI industry, this is a signal that the AI war is getting fiercer. The game has just begun.
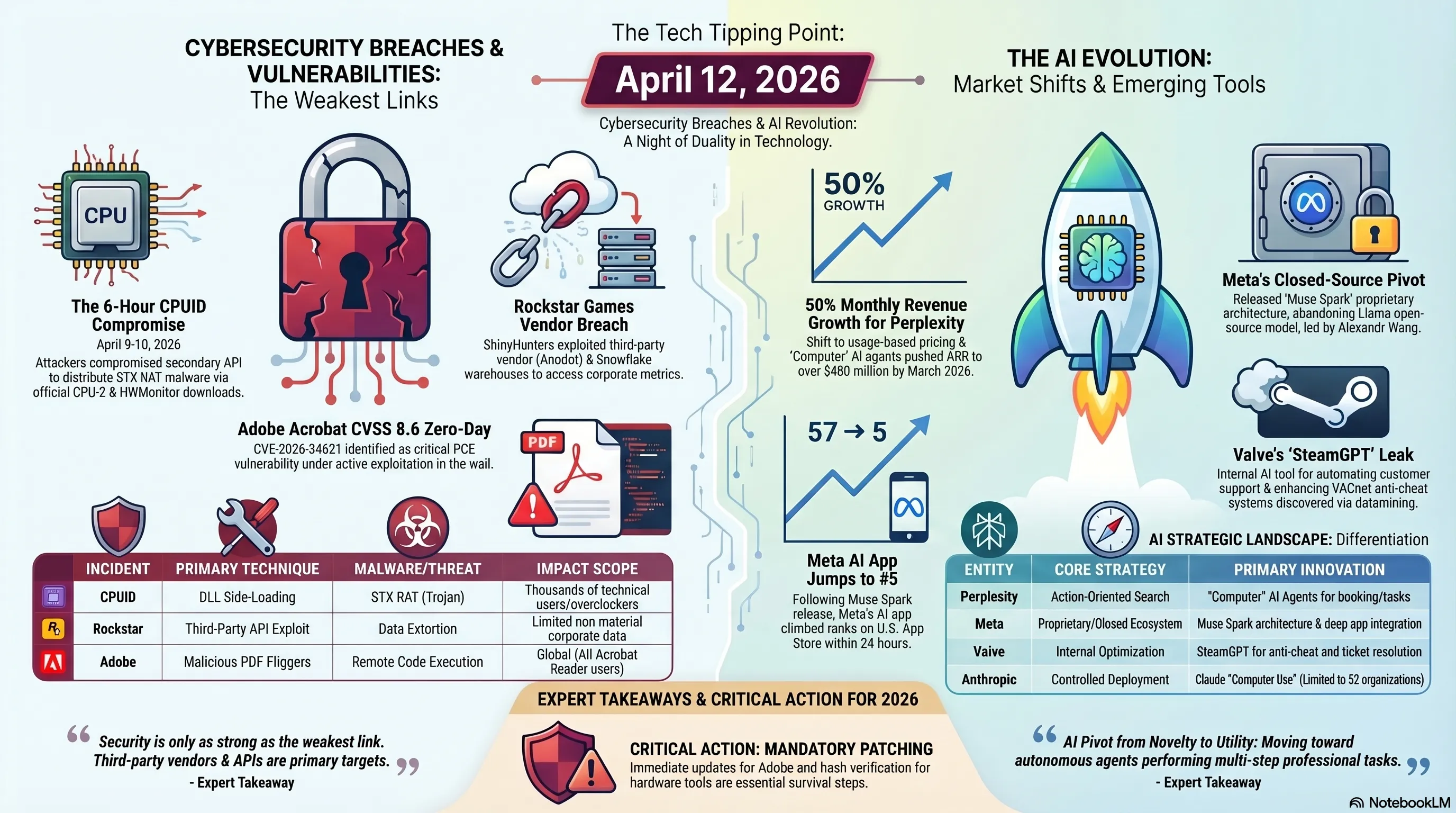
🎮 6. Valve SteamGPT: Secret AI Tool for Support and Anti-Cheat
Valve is secretly building an internal AI tool called "SteamGPT" - and we only know about it because of an accidental leak. Dataminer Gabe Follower discovered code strings related to SteamGPT in a recent Steam update and shared them on X on April 7, 2026. Valve quickly removed these references, but it was too late - the cat was out of the bag. According to code analysis, SteamGPT is designed to serve two main purposes: automating customer support tickets and enhancing anti-cheat systems, especially VACnet in Counter-Strike 2. This could be the biggest change in how Steam operates in years.
What is SteamGPT? Based on variable names and code references, it's an AI system that includes functions for task generation, data labeling, and summarization. This suggests Valve is using AI to process and analyze massive amounts of data - whether that's support tickets, player reports, or gameplay data. Unlike ChatGPT or Claude which are user-facing, SteamGPT appears to be an internal tool - designed to help Valve employees and automated systems, not directly for players.
How does support automation work? One of the biggest complaints about Steam has always been slow customer support. With millions of active users, Valve faces a constant flood of tickets - refund issues, account problems, technical bugs, and more. SteamGPT could accelerate this process by automatically processing incoming requests, answering common questions, and resolving routine issues without human intervention. The system can classify tickets, identify the problem, and provide prepared solutions from past cases. This shortens response times and lightens the workload for support teams. Of course, more complex cases will still require human review, but the overall queue could be significantly shorter.
🎯 SteamGPT Use Cases
1. Customer Support:
- Automatically process support tickets
- Answer common questions without human intervention
- Accelerate refund processing and routine issues
- Classify and prioritize tickets
2. Anti-Cheat and Moderation:
- Real-time analysis of player reports
- Cross-check complaints with gameplay data
- Detect suspicious patterns and repeated violations
- Help prioritize high-risk cases for review
- Evaluate user trust scores based on behavior
3. Content Moderation:
- Flag abusive content
- Filter spam in community hubs
- Monitor accounts for unusual patterns
What's the VACnet integration? VACnet is Valve's machine learning-based anti-cheat system used in Counter-Strike 2. It uses behavioral patterns to detect cheaters, not just malware signatures. SteamGPT could enhance VACnet in several ways: real-time analysis of player reports, cross-checking complaints with gameplay data, detecting suspicious patterns and repeated violations, and helping prioritize high-risk cases for review. This setup helps the platform catch threats faster and find violations more accurately because the system adapts to new data and player behavior instead of relying strictly on static rules.
Why did Valve keep this secret? Several likely reasons: First, competitive advantage - if cheaters know exactly how SteamGPT works, they can find ways around it. Second, expectations - if Valve publicly announced an AI assistant and didn't deliver, there would be significant backlash. Third, testing - Valve likely wants to test SteamGPT internally before any public announcement. And fourth, privacy concerns - using AI to analyze user behavior and content could raise privacy questions that Valve likely wants to address before going public.
When can we expect to see it? Valve hasn't announced any official timeline (and likely won't until it's ready). But the fact that code references appeared in production Steam builds shows development is well underway. SteamGPT may first appear in Steam Beta, where Valve typically tests new features before wide rollout. For players, the impact should be invisible - just faster support and better anti-cheat. For cheaters, this is bad news - an AI system that can detect patterns and adapt is much harder to circumvent than traditional systems.
💬 Community Reaction
Positive: Players are excited about faster support and better anti-cheat. Many hope SteamGPT can solve CS2's chronic cheating problem.
Cautious: Some are concerned about privacy - how much data is Valve collecting? How is it used? Can AI make mistakes and ban innocent players?
Negative: Skeptics say AI can never replace human judgment, especially in complex cases. Concerns about false positives and lack of transparency exist.
What's the impact on the gaming industry? If SteamGPT succeeds, expect other gaming platforms to follow suit. Epic Games, PlayStation Network, Xbox Live - all face the same support and anti-cheat challenges. AI could be a game-changer: faster, cheaper, and more scalable than human teams. But it also has risks: false positives, lack of empathy, and potential for abuse. The key is using AI as a tool to augment humans, not replace them entirely.
🎮 Tekin Analysis:
SteamGPT is a clear sign that Valve is taking AI seriously - and not just for hype. This is a practical tool designed to solve real problems: slow support and chronic cheating. The fact that Valve kept this secret shows they want to get it right before making it big. For players, this should be a win-win: faster support and cleaner games. For cheaters, the good times are ending - an AI system that can learn and adapt is much harder to beat than traditional anti-cheat. For the industry, this is a preview of gaming's future: where AI works invisibly in the background to improve the experience. But important questions remain: how does Valve protect privacy? How does it handle false positives? And how does it maintain transparency? Only time will answer. One thing is certain: Steam is changing, and AI is at the center of that transformation.
🌙 Conclusion: A Night Where Security and AI Collided
The night of April 12, 2026 was a complete snapshot of the current state of technology: cybersecurity more fragile than ever, and AI more powerful than ever before. On one hand, we saw how supply chain attacks can compromise even reputable companies like CPUID, how hacker groups like ShinyHunters use third-party vendors to target gaming giants, and how zero-day vulnerabilities in widely-used software like Adobe Acrobat Reader can put millions of users at risk. On the other hand, we saw how AI is transforming from a novelty to a utility: Perplexity with 50% revenue growth through AI agents, Meta with its first closed-source model that pushed the app from rank 57 to 5, and Valve secretly building an AI system for support and anti-cheat.
The pattern is clear: cybersecurity is no longer an IT issue - it's a critical business issue. Every company, from small startups to tech giants, must assume they're a target. And the solution? A combination of human vigilance, robust security architecture, and - increasingly - AI. The same technology that's changing the world is also becoming the primary tool for defending against cyber threats. Valve's SteamGPT is just the beginning - expect every major tech company to build similar AI systems for threat detection, incident response, and security automation.
🔑 Key Takeaways from the Night
- Supply chain attacks work: Both CPUID and Rockstar were compromised through third-party vendors - a reminder that security is only as strong as the weakest link.
- Zero-days are still a major threat: Adobe CVE-2026-34621 shows even widely-used software can have critical vulnerabilities under active exploitation.
- AI agents are here: Perplexity's 50% growth proves the market is ready for AI that actually does work, not just talks.
- Open-source vs closed-source: Meta with Muse Spark showed even the biggest open-source advocates are willing to go closed for competitive advantage.
- AI for defense: Valve's SteamGPT shows AI is being used not just to build new products, but to protect existing platforms from threats.
For regular users, the message is clear: be vigilant. Even when downloading from trusted sources, verify hashes. Even when PDFs come from known senders, be cautious. And always, always install security updates immediately. For companies, the message is even clearer: vendor security isn't an afterthought - it's a priority one. Every integration, every API, every third-party vendor is a potential attack vector. And for the tech industry, the message is: the AI race and the cybersecurity race are no longer two separate things - they've merged. Companies that can use AI for both offense and defense will be the winners of the next decade.
The night of April 12 was a reminder that in the world of technology, the only constant is change. Threats evolve, defenses adapt, and the cycle continues. But one thing is clear: the future belongs to those who can move faster, think smarter, and innovate better than their competitors. Whether you're a developer, a CISO, a founder, or just a tech enthusiast, the message is the same: be prepared, be vigilant, and never assume you're safe. Because in the world of 2026, the only real security is constant vigilance.
"In the war between security and threat, there are no permanent winners - only those who adapt faster."
— Tekin Night, April 12, 2026
Until tomorrow night, stay safe, stay updated, and always stay one step ahead of the threats. 🌙
