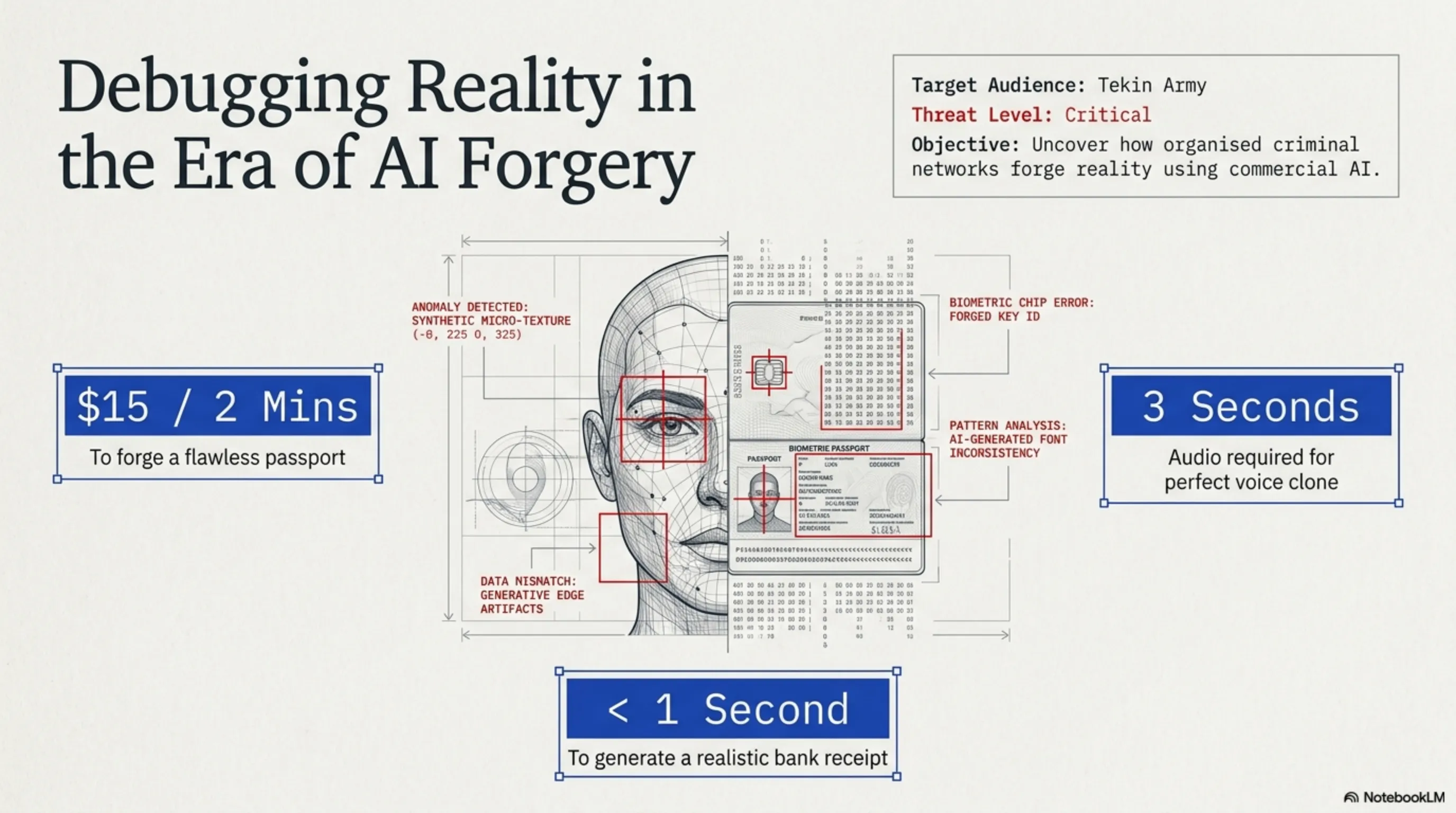
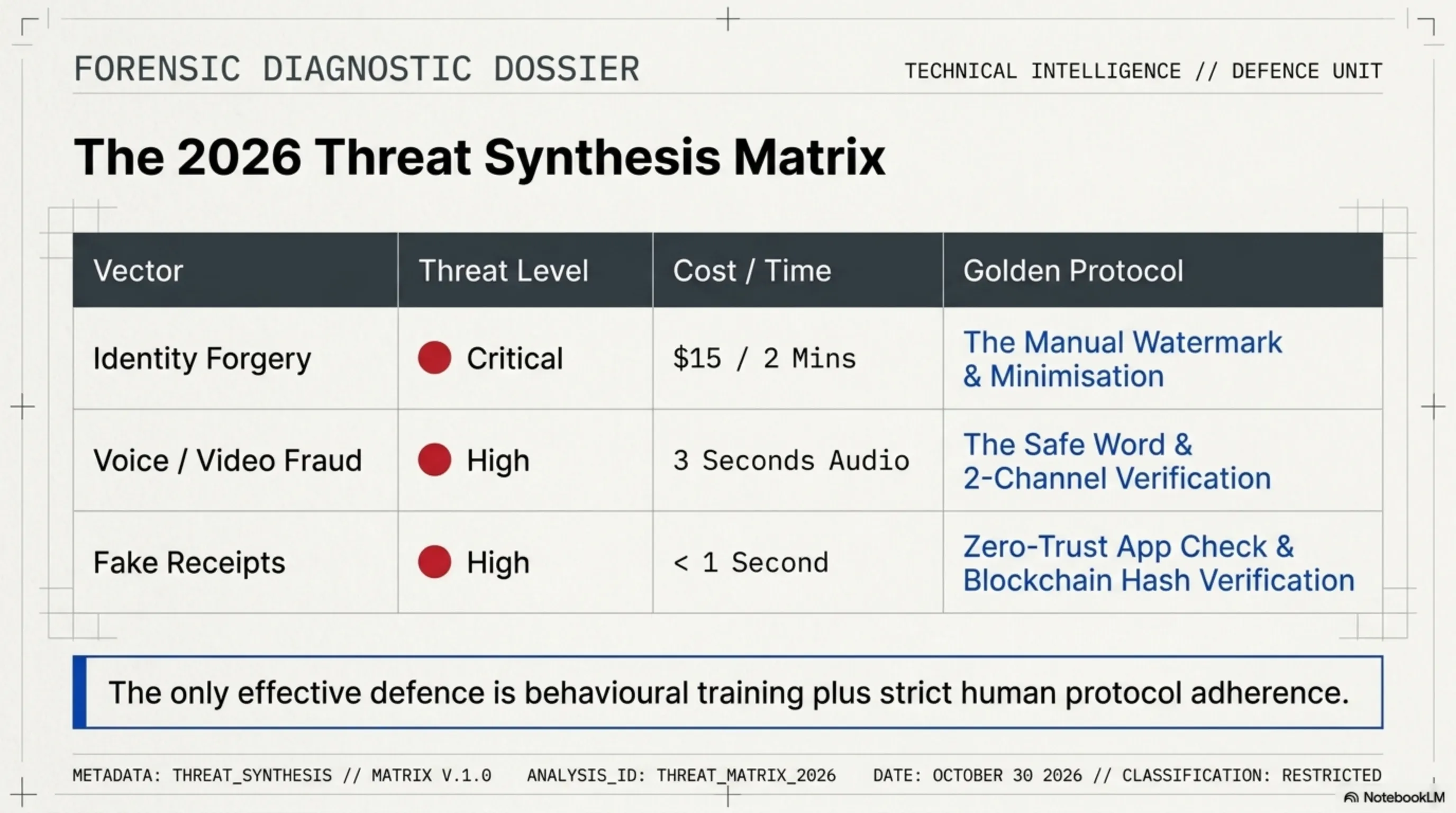
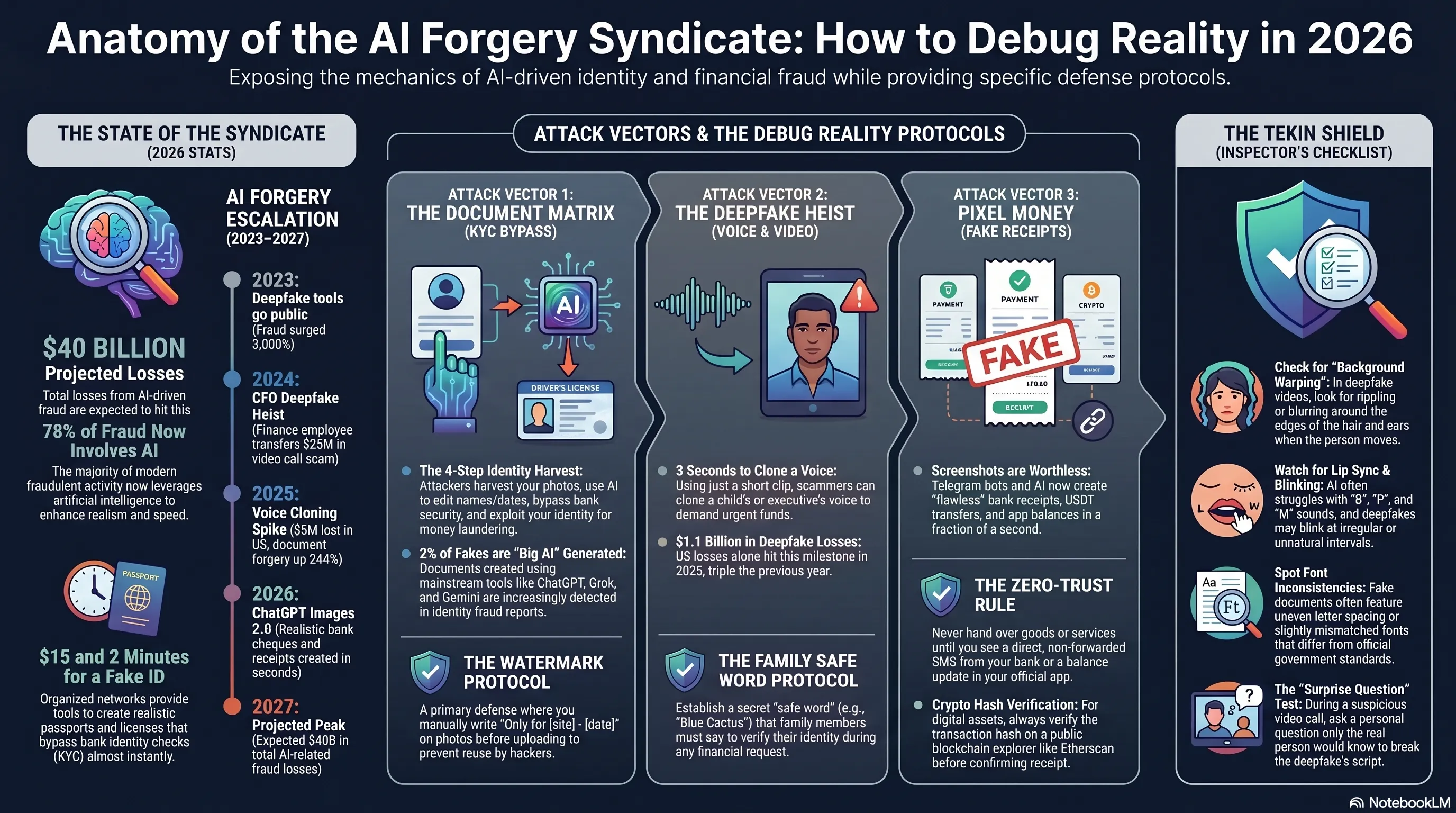
In this highly specialized 5600-word report, we dissect the AI fraud syndicate of 2026. This article analyzes the matrix of forged documents (KYC Bypass), deepfake audio thefts, and fake bank receipts. Finally, it provides the "Tekin Inspector Checklist" featuring 15 definitive signs to debug reality and detect AI forgery.
🕵️ Anatomy of the AI Forgery Syndicate — How to Debug Reality
Tekin Army, read this carefully. In 2026, an organized criminal network using commercial AI tools — the same ones everyone has access to — is forging reality. A fake passport in 2 minutes for $15. Your voice cloned from 3 seconds of audio. A perfectly realistic bank receipt in a fraction of a second. This article dissects how the enemy operates — and how you can protect yourself.
🔍 Autopsy Contents:
📄 Part 1: The Document Matrix — KYC Bypass & Identity Theft
🎭 Part 2: The Deepfake Heist — Voice & Video Fraud
💸 Part 3: Fake Bank Receipts — Pixel Money Illusions
🛡️ Part 4: The Tekin Shield — Inspector's Checklist
⚡ Practical defenses for each section
📊 Alarming Stats — AI Forgery Syndicate 2026
⏳ AI Forgery Evolution Timeline
| Year | Event | Impact |
|---|---|---|
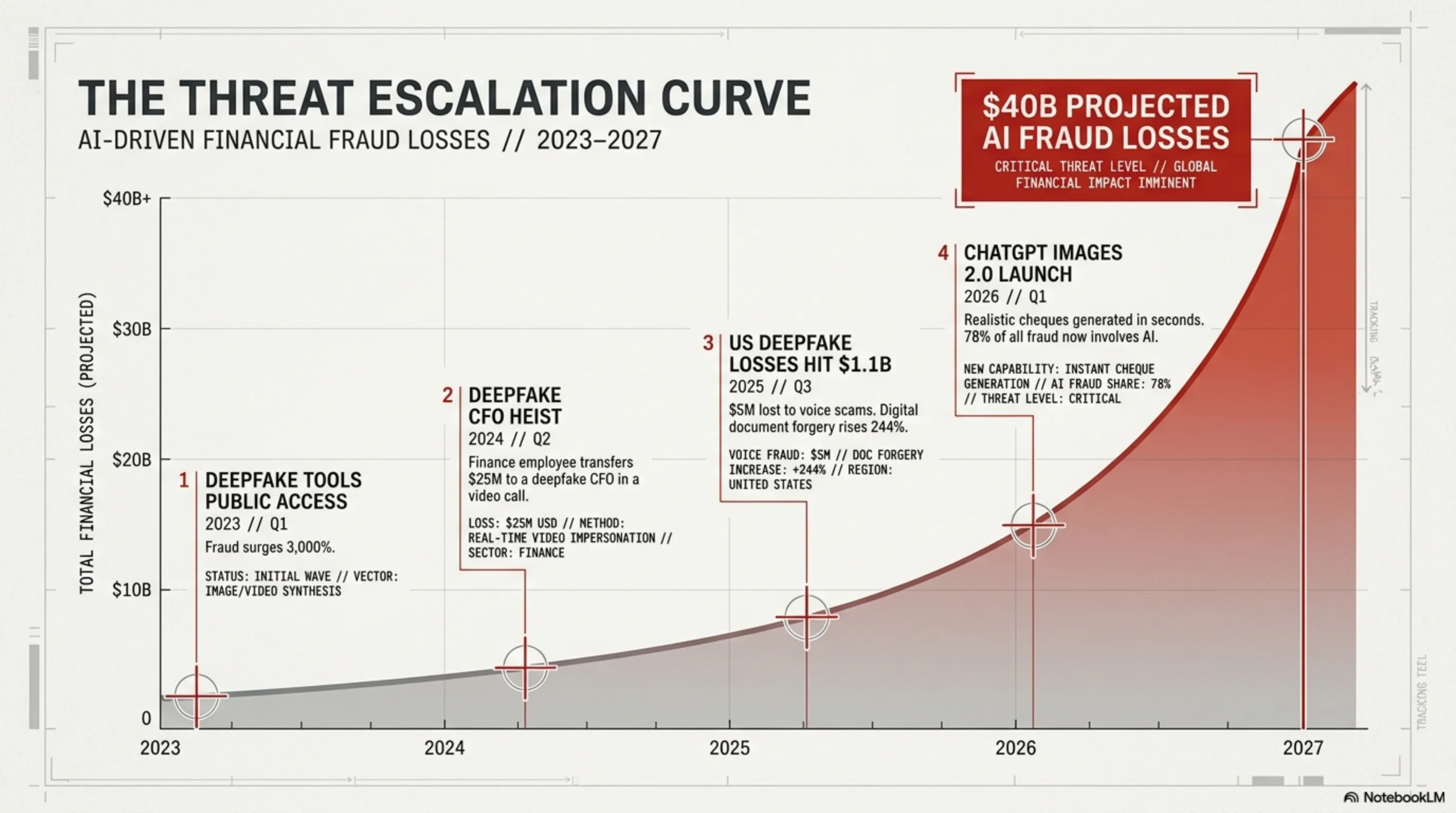
| 2023 | Deepfake tools go public | Fraud surged 3,000% |
| 2024 | Finance employee transfers $25M | Deepfake CFO in video call |
| 2025 | $5M voice cloning losses in US alone | Document forgery up 244% |
| 2026 | ChatGPT Images 2.0 — realistic bank cheque | "We are finished" — experts react |
| 2027 | Projected: $40B AI fraud losses | If we don't act now |
📄 Part 1: The Document Matrix — KYC Bypass
🔴 Attack Anatomy
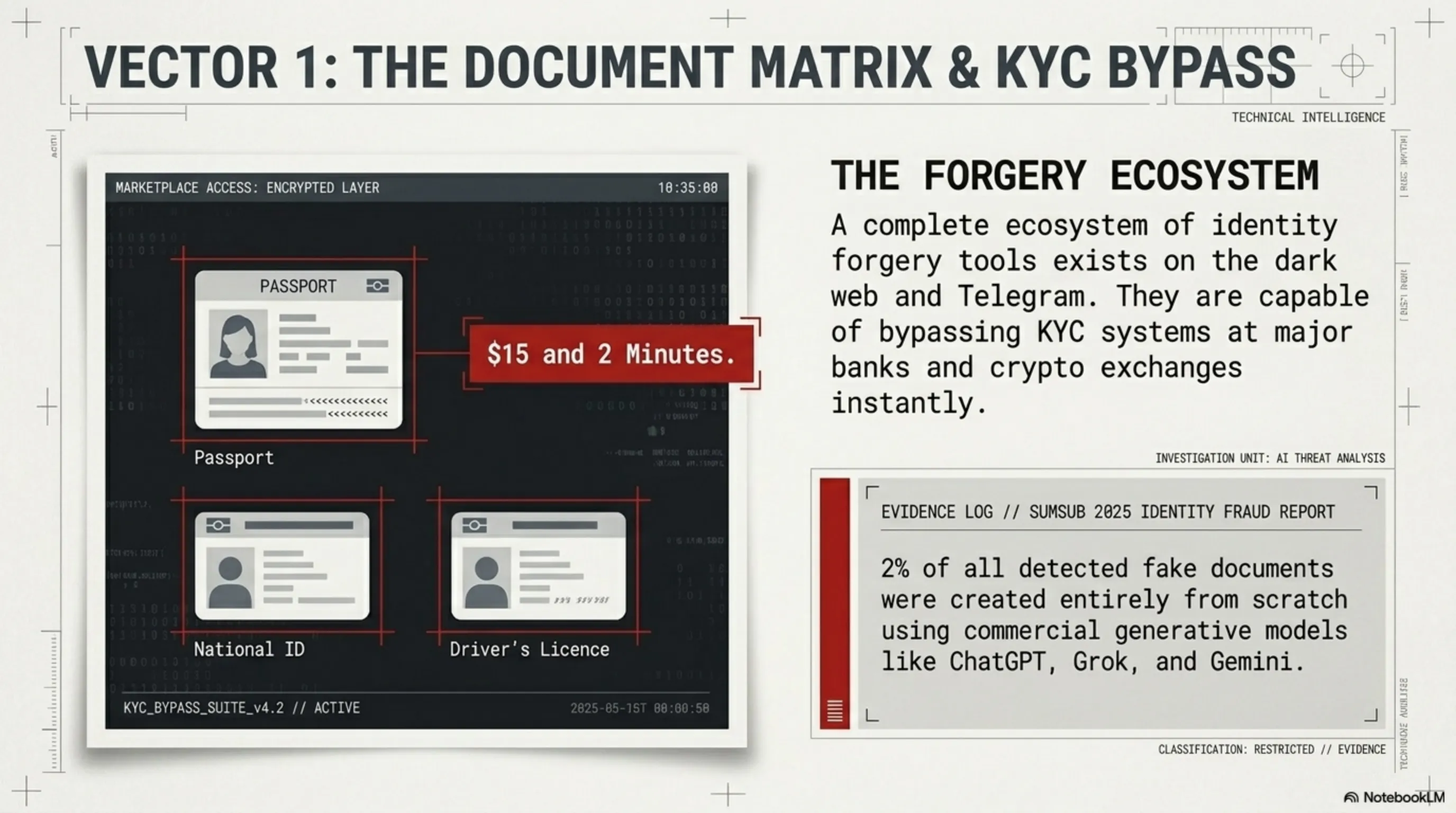
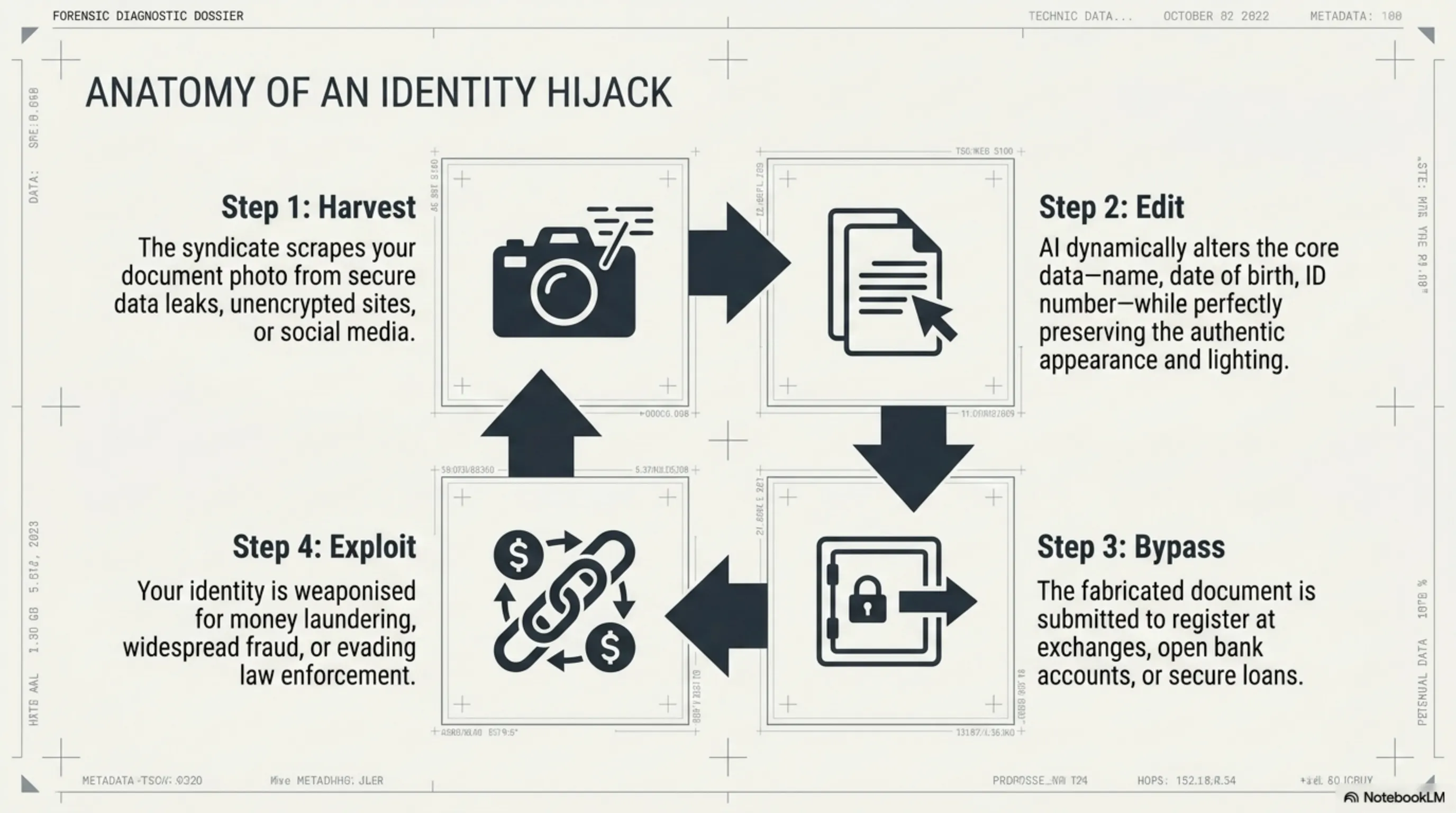
On the dark web and even Telegram, a complete ecosystem of identity forgery tools exists. For $15 and 2 minutes, a hacker can create a flawless passport, driver's license, national ID, or property document that bypasses KYC systems at exchanges and banks. The Sumsub 2025 Identity Fraud Report confirms that 2% of all detected fake documents were created with ChatGPT, Grok, and Gemini.
⚠️ How the Attack Works
🟢 Debug Reality — Defense
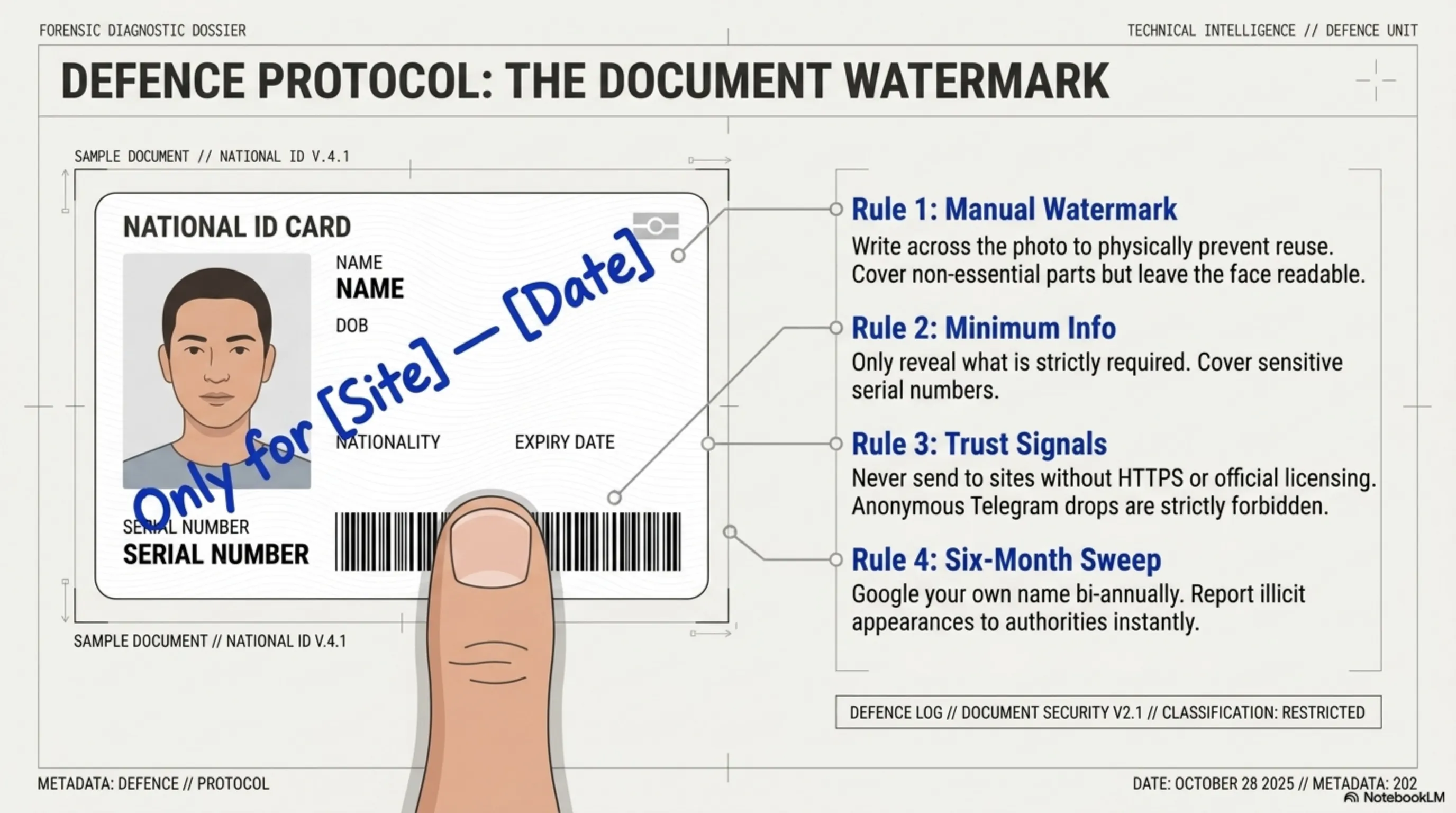
🛡️ The Watermark Protocol — Golden Rule for Documents
✅ Rule 1: Manual Watermark
Before sending any document, write on the photo: "Only for [site name] — [today's date]". That photo can't be reused elsewhere.
✅ Rule 2: Trust Signals
Never send documents to sites without HTTPS, official licensing, or trust seals. Anonymous Telegram chats = forbidden.
✅ Rule 3: Minimum Info
Only show the part of the document that's required. Cover sensitive numbers with your finger before photographing.
✅ Rule 4: Monitor
Every 6 months, Google your own name. If your document appears somewhere it shouldn't, report to authorities immediately.
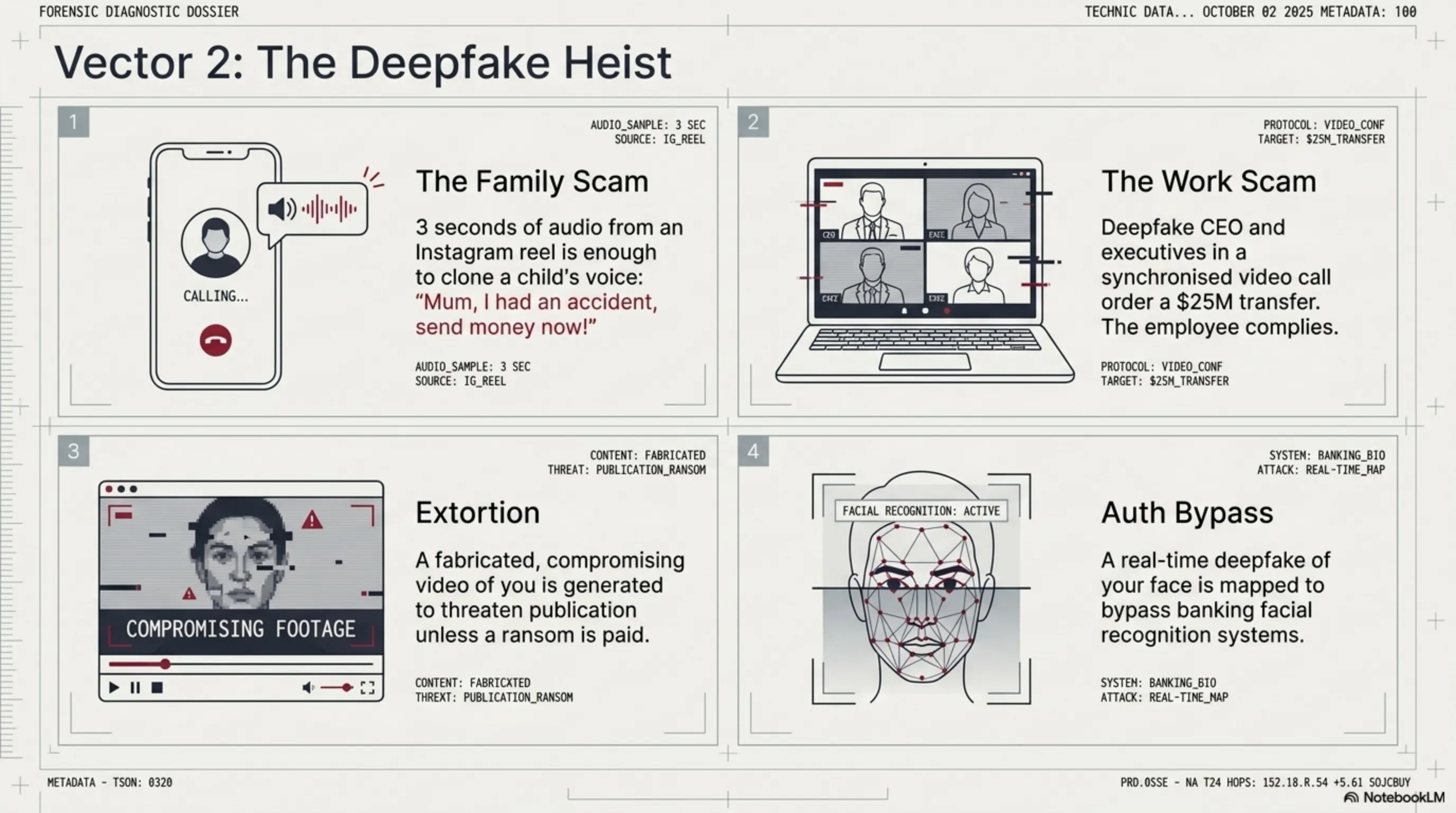
🎭 Part 2: The Deepfake Heist — Voice & Video Fraud
🔴 Attack Anatomy
In 2024, a finance employee at a multinational company transferred $25 million — because in a video call, he saw the CFO and several senior executives giving orders. All deepfakes. In 2025, Americans lost $5 million just from voice cloning scams. Deepfake losses in the US hit $1.1 billion in 2025 — triple 2024. Losses could reach $16 billion by late 2026.
⚠️ Common Attack Scenarios
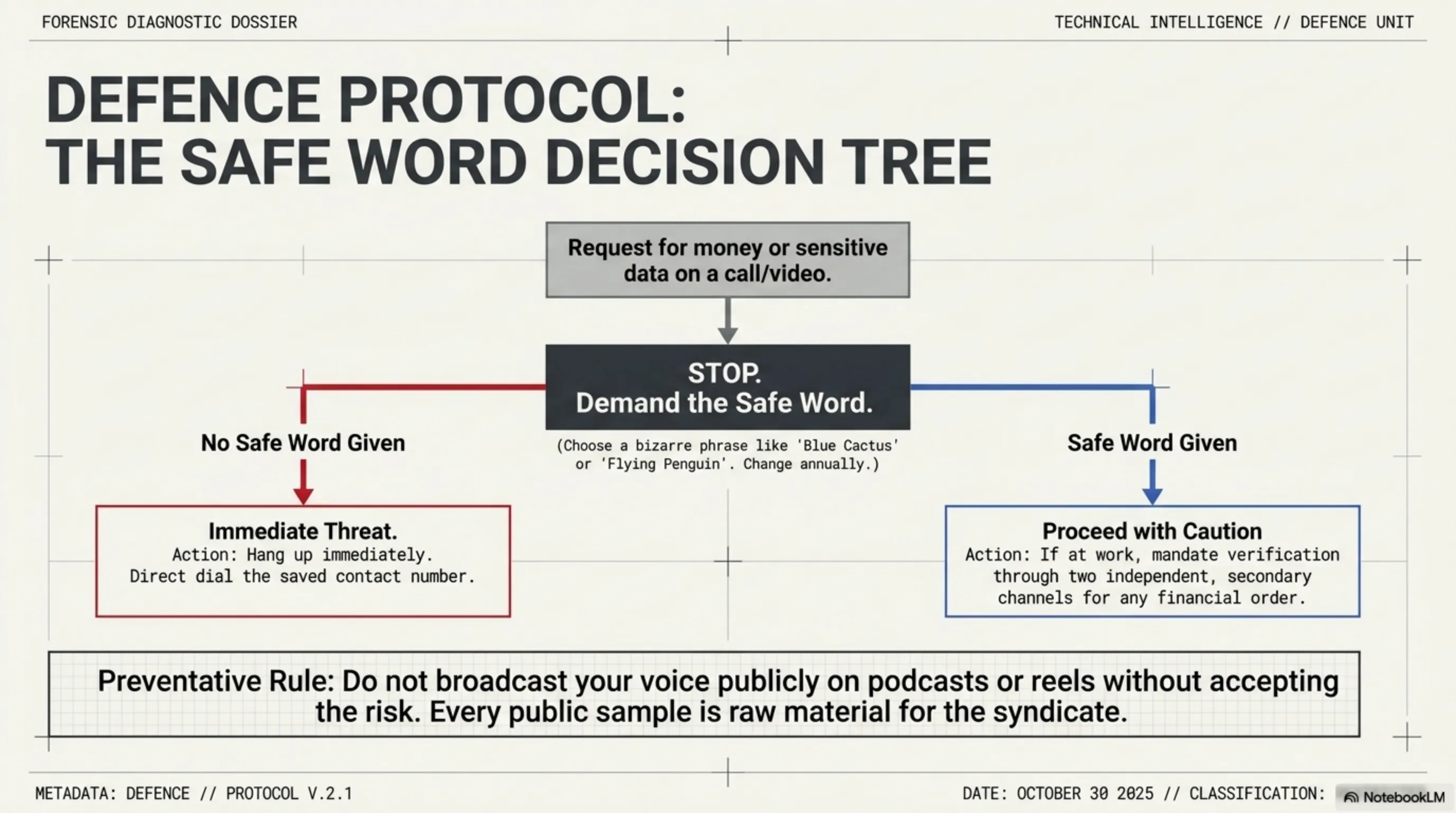
🟢 Debug Reality — The Family Safe Word Protocol
🛡️ Family Safe Word — Tonight's Action
🚨 Rule: If anyone on a call asks for money, they must say the safe word first. If they don't = deepfake. Hang up and call back on the saved number directly.
✅ For Family
A weird word only family knows. Like "blue cactus" or "flying penguin". Change it every year.
✅ For Work
Any financial order above a set amount must be confirmed through two independent channels. Video call alone is not enough.
✅ Social Media
Don't make your voice public in podcasts or reels without a plan. Every public audio sample = raw material for cloning.
💸 Part 3: Fake Receipts & Crypto Illusions
🔴 Attack Anatomy
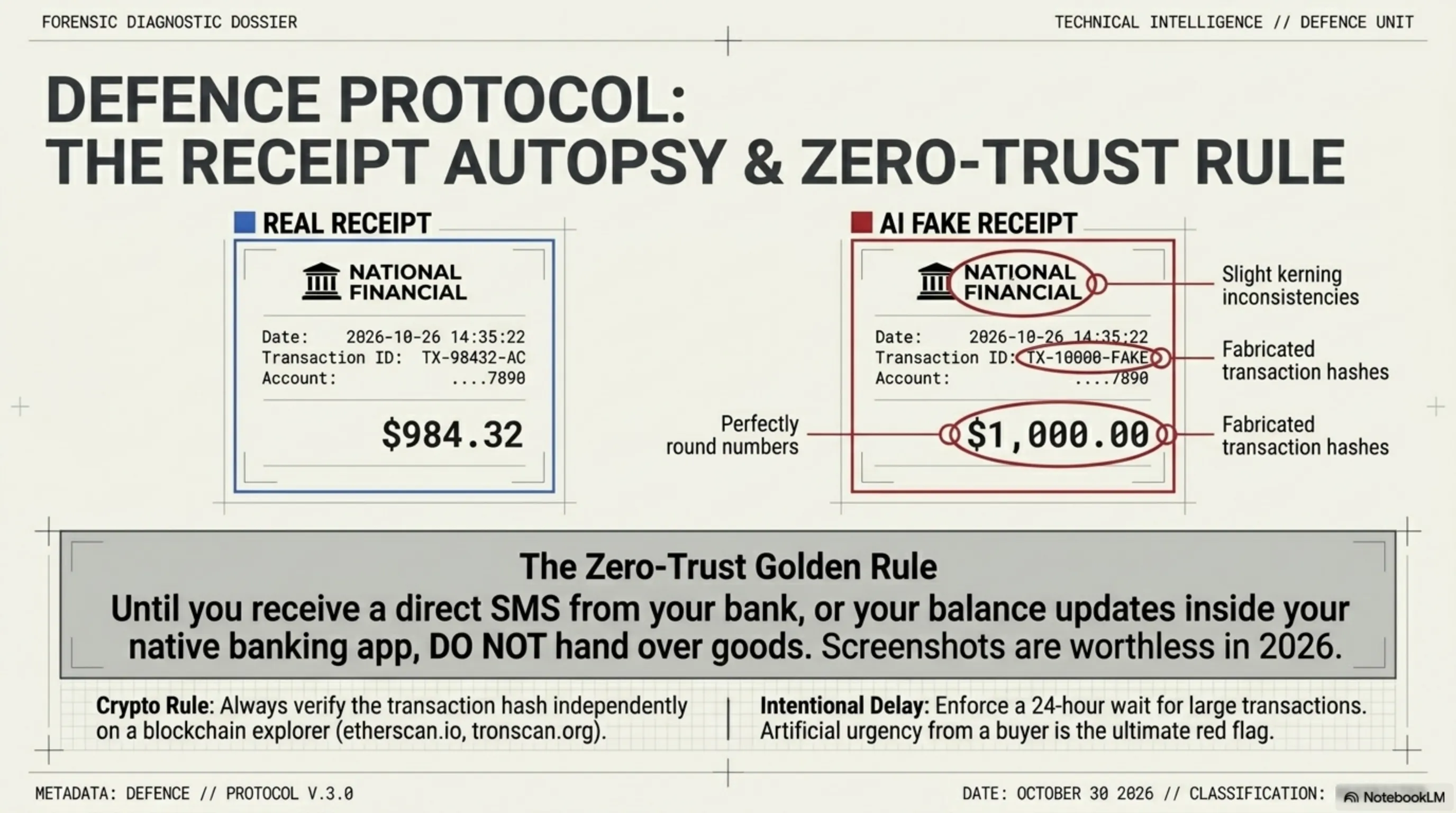
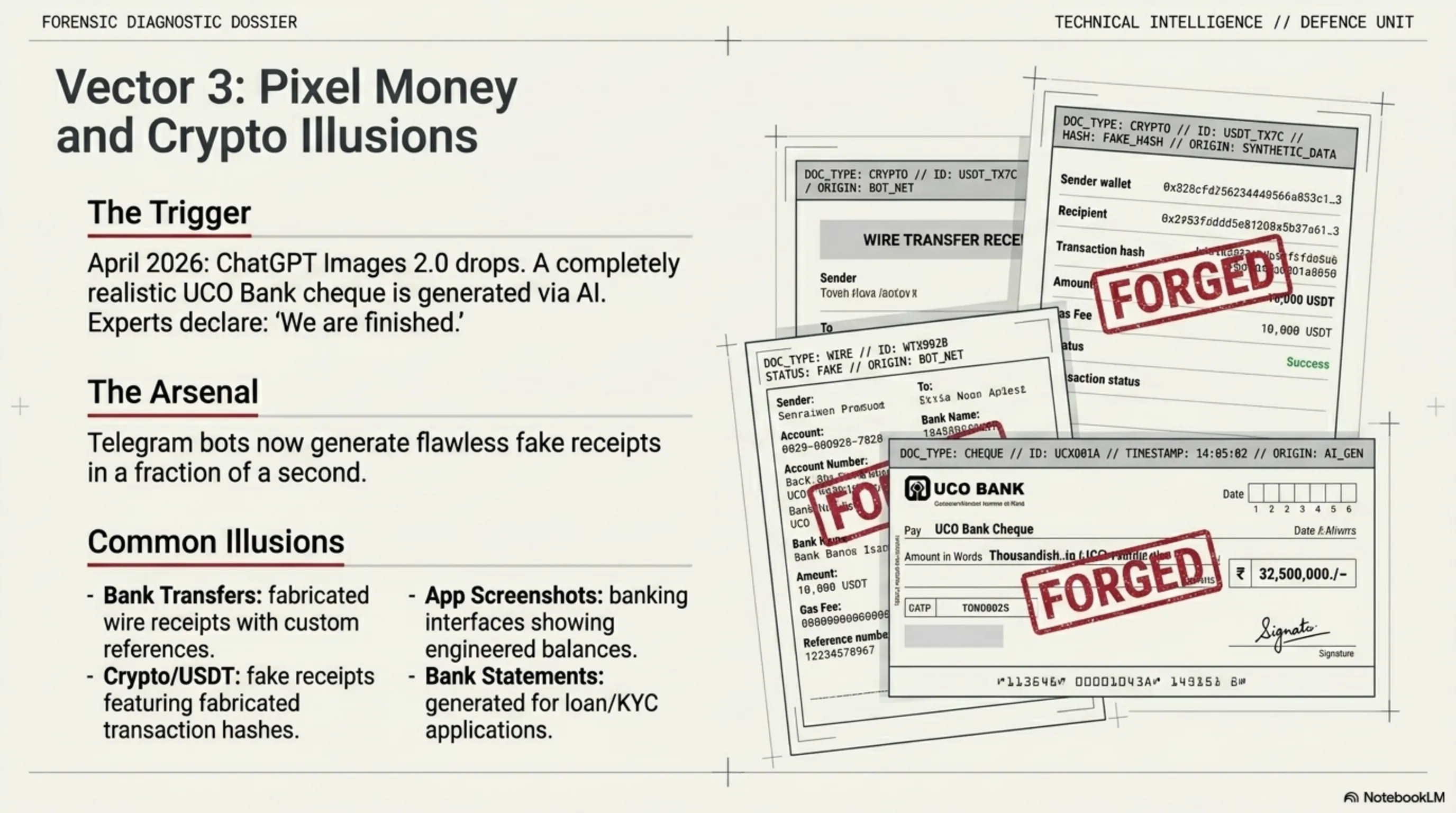
In April 2026, the release of ChatGPT Images 2.0 triggered a new wave of concern. An Indian user created a completely realistic UCO Bank cheque with AI and posted it on social media. Expert reaction: "We are finished." Telegram bots now generate bank transfer receipts, wire transfers, USDT transfers, and PayPal receipts in a fraction of a second.
⚠️ Common Fake Receipt Types
🟢 Debug Reality — The Zero-Trust Rule
🚨 Tekin Garage Golden Rule: Until you receive a direct SMS from your bank or your balance updates in your banking app, do NOT hand over any goods. Screenshots are worthless in 2026!
✅ Direct Confirmation
Only a direct SMS from your bank (not forwarded) or updated balance in your banking app is valid.
✅ Crypto Transactions
Check the transaction hash on a blockchain explorer (etherscan.io, tronscan.org). Until confirmed = money hasn't arrived.
✅ Intentional Delay
For large transactions, wait 24 hours. Scammers always say "urgent" — that itself is a red flag.
🛡️ Part 4: The Tekin Shield — Inspector's Checklist
🔍 Tekin Inspector Checklist — 15 Signs of Forgery
📸 Fake Images & Documents:
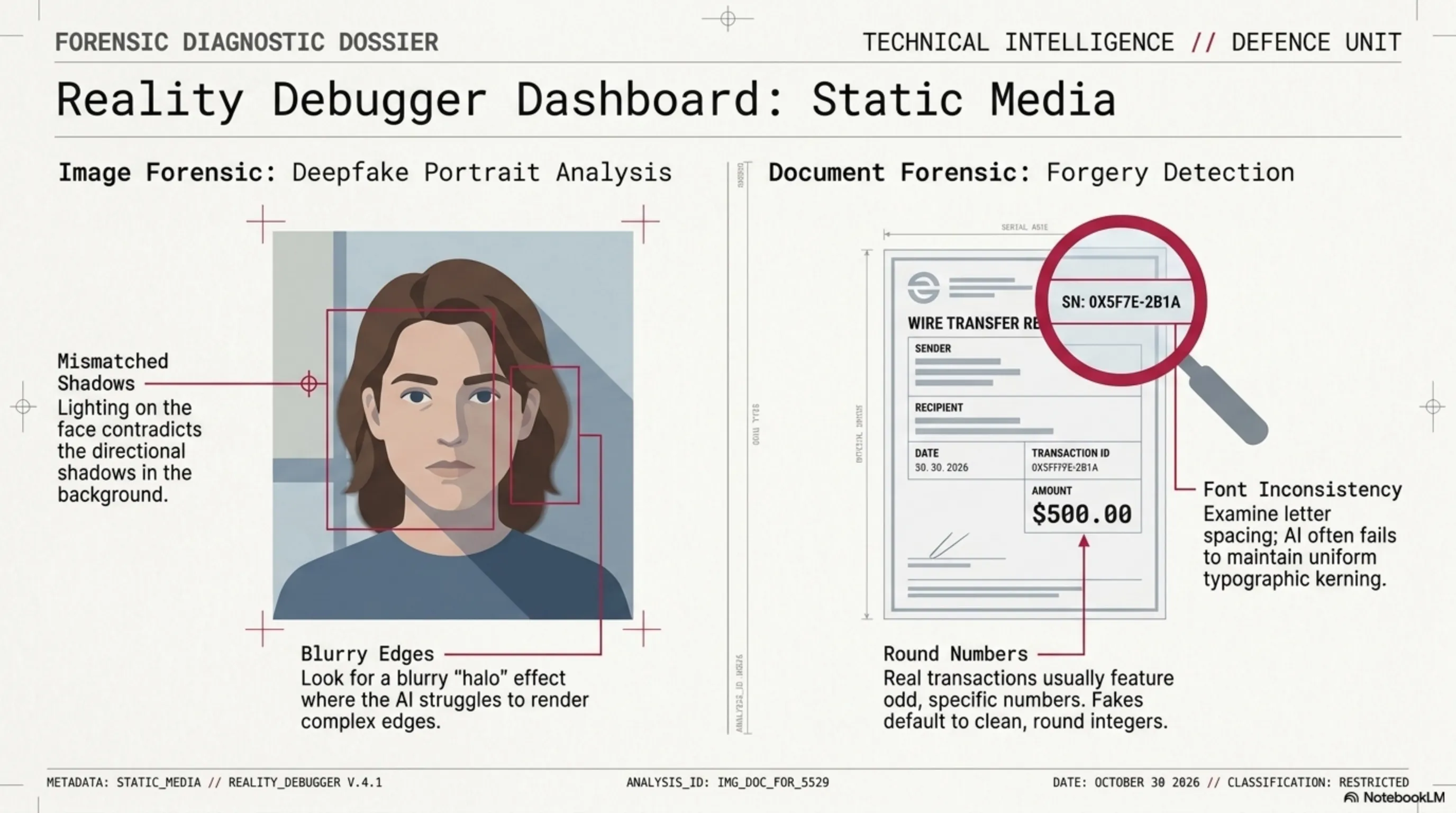
In fake images, shadows come from different directions. Lighting on the face doesn't match the background.
Around hair, ears, and face edges in deepfakes — usually blurry or "halo" effect.
In fake documents, fonts are slightly different. Letter spacing is uneven.
Fake receipts usually have round amounts ($500, $1000). Real receipts have odd numbers.
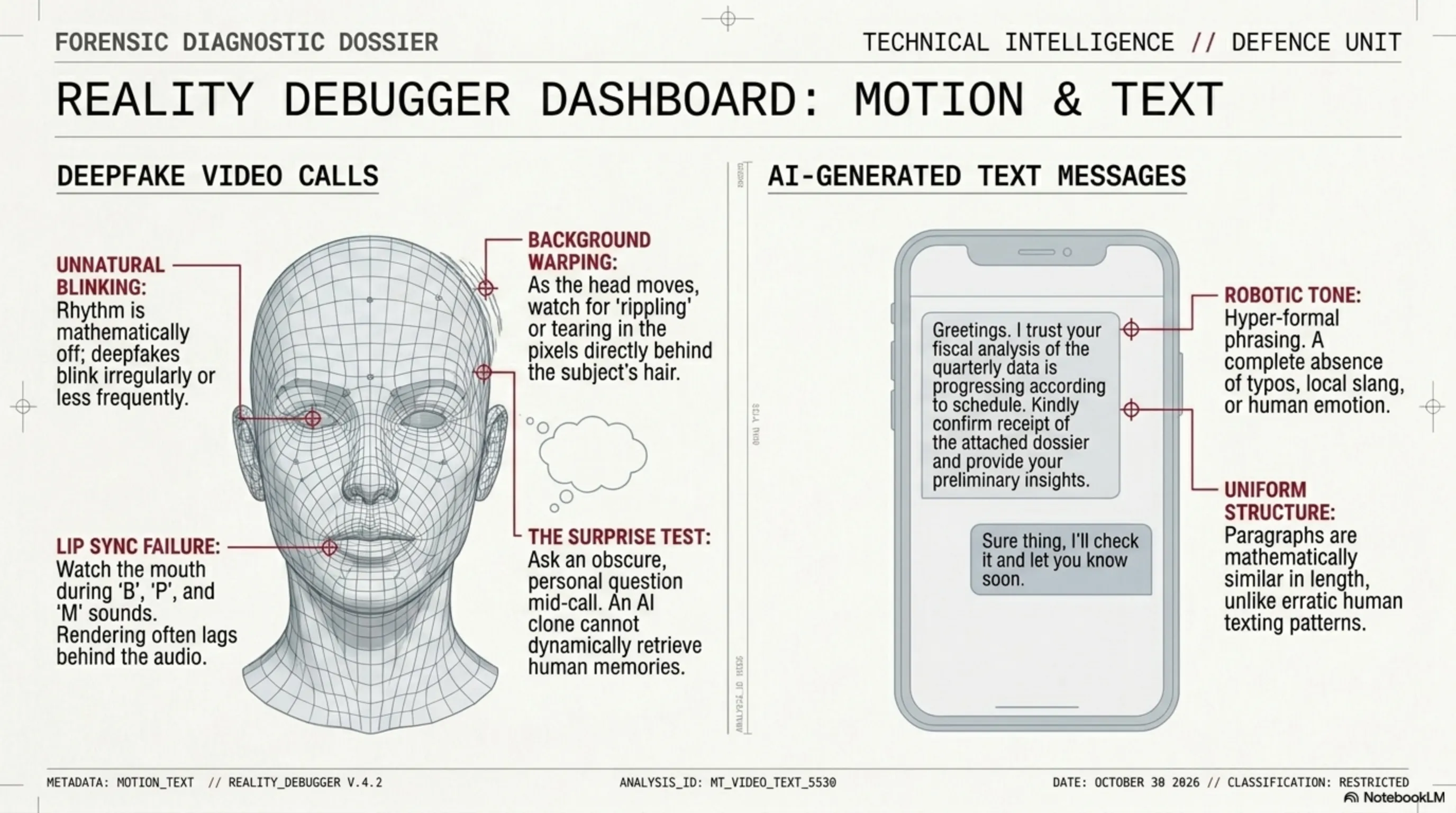
🎥 Deepfake Video Calls:
Deepfakes blink less or at irregular intervals. The rhythm is off.
Lip movement is slightly out of sync with audio. Especially noticeable on "B", "P", "M" sounds.
Around the head and hair in deepfakes, the background sometimes "ripples" when the head moves.
Ask a personal question only that person would know. A deepfake can't answer it.
🤖 AI-Generated Text Messages:
AI messages are very formal, no typos, no local slang, no emotion.
AI messages tend to be similar length with similar structure. Humans send short and long messages.
"Urgent", "right now", "limited time" — scammers want you to not think.
🌡️ Threat Thermometer: AI Forgery Status 2026
🌡️ AI Forgery Threat Thermometer — 2026
🏷️ Smart History: From Photoshop to AI
- 2010: Photoshop — forgery required skill. Only experts could do it.
- 2017: First deepfake videos — required powerful GPU and hours of processing.
- 2023: Deepfake tools go public — anyone can do it. Fraud surged 3,000%.
- 2024: $25M transferred via deepfake CFO. ElevenLabs voice cloning goes public. Tekin Morning Apr 29 →
- 2025: $1.1B deepfake losses in US. Document forgery up 244%.
- 2026: ChatGPT Images 2.0 — realistic bank cheque in seconds. "We are finished" — experts.
⚔️ PROS & CONS: AI in the Forgery World
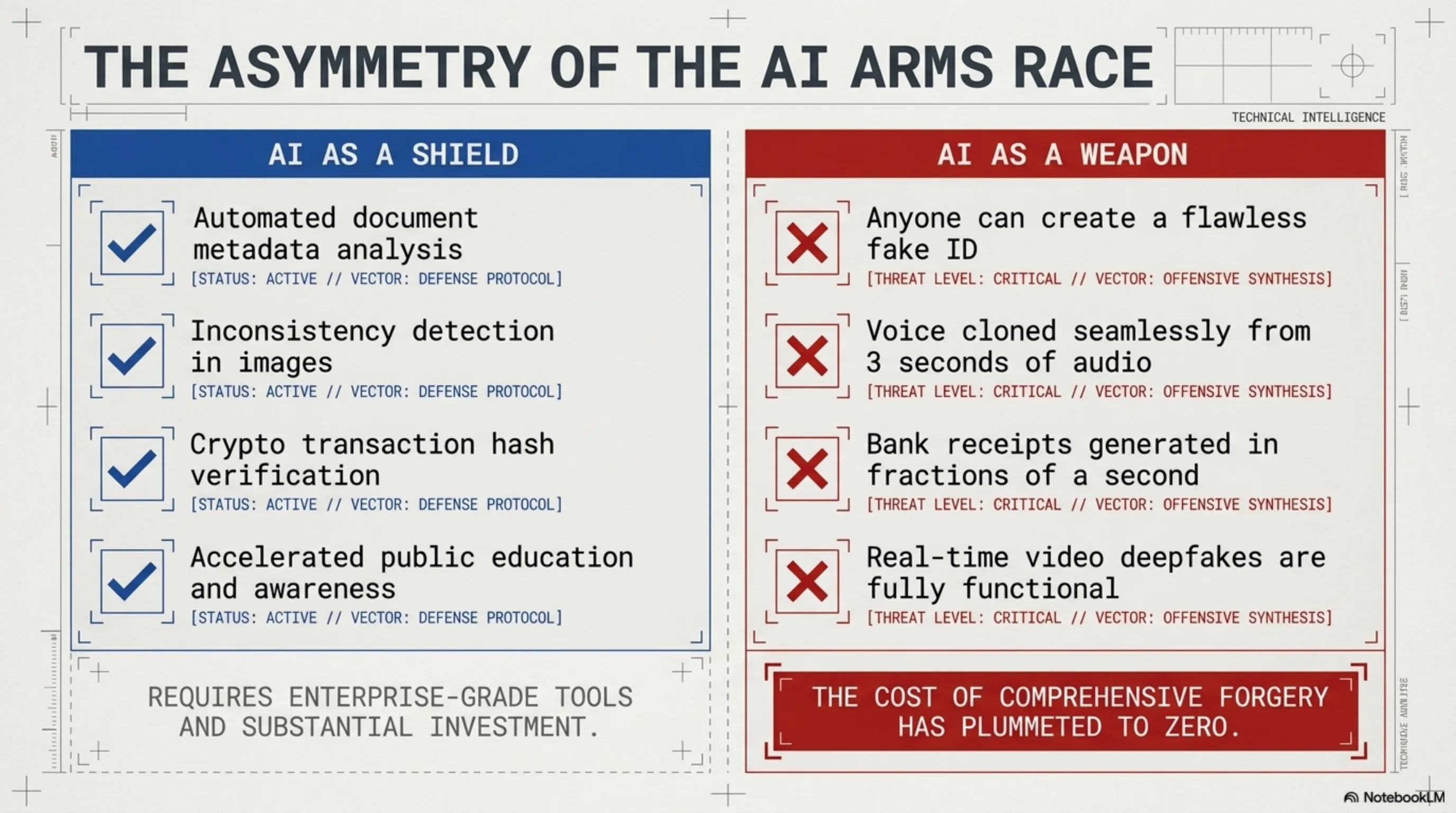
✅ AI in Detection
- ✓ AI tools can detect deepfakes
- ✓ Automated document metadata analysis
- ✓ Inconsistency detection in images
- ✓ Crypto transaction hash verification
- ✓ Public education is faster now
❌ AI in Forgery
- ✗ Anyone can create a fake ID
- ✗ Voice cloned from 3 seconds of audio
- ✗ Bank receipt in a fraction of a second
- ✗ Real-time deepfake video is now possible
- ✗ Cost of forgery has reached zero
❓ FAQ
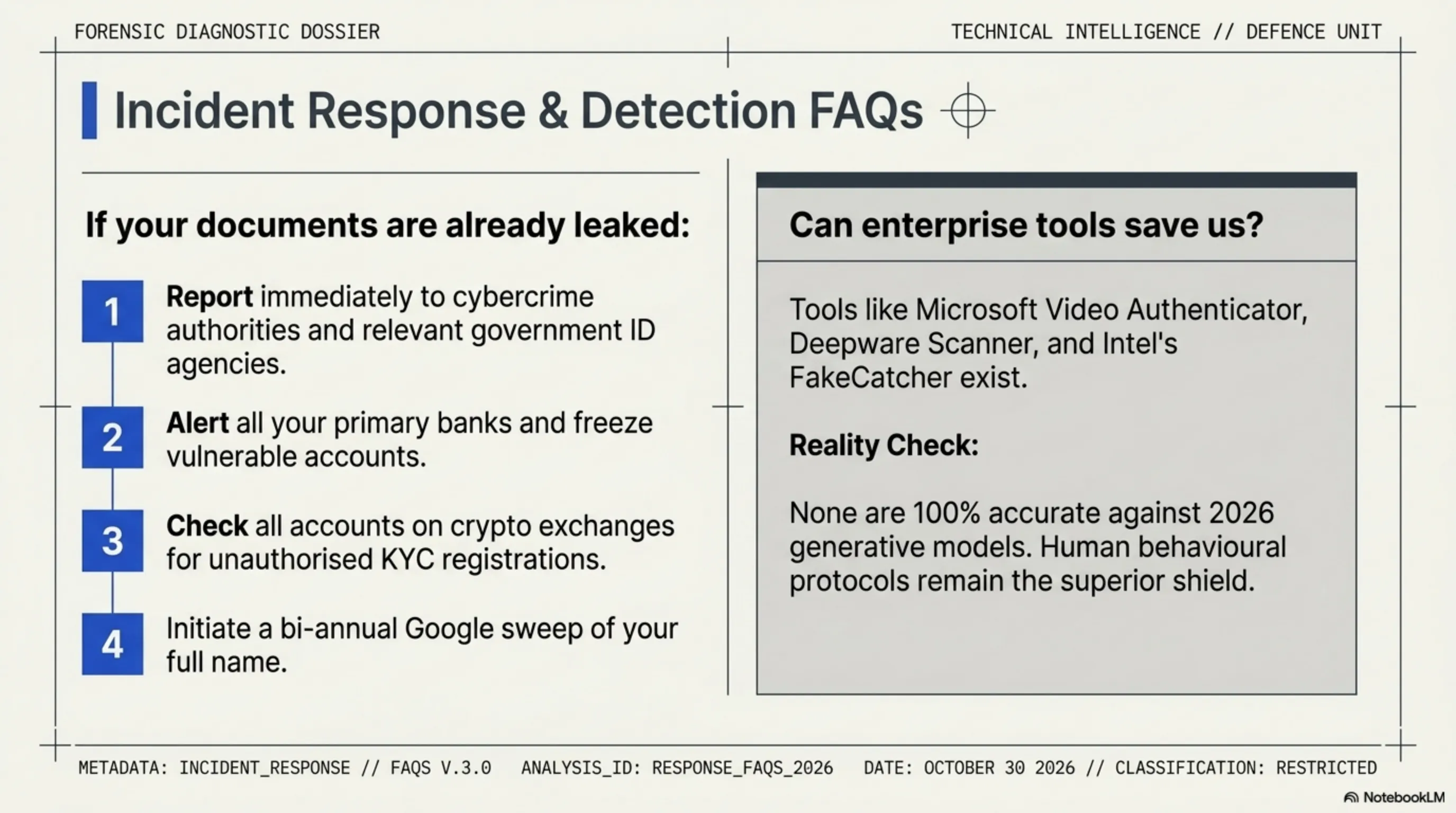
🔹 If my document was already uploaded somewhere, what do I do?
🔹 Are there tools to detect deepfakes?
🔹 How do I know if a bank receipt is real?
🔹 Is my voice in podcasts or videos dangerous?
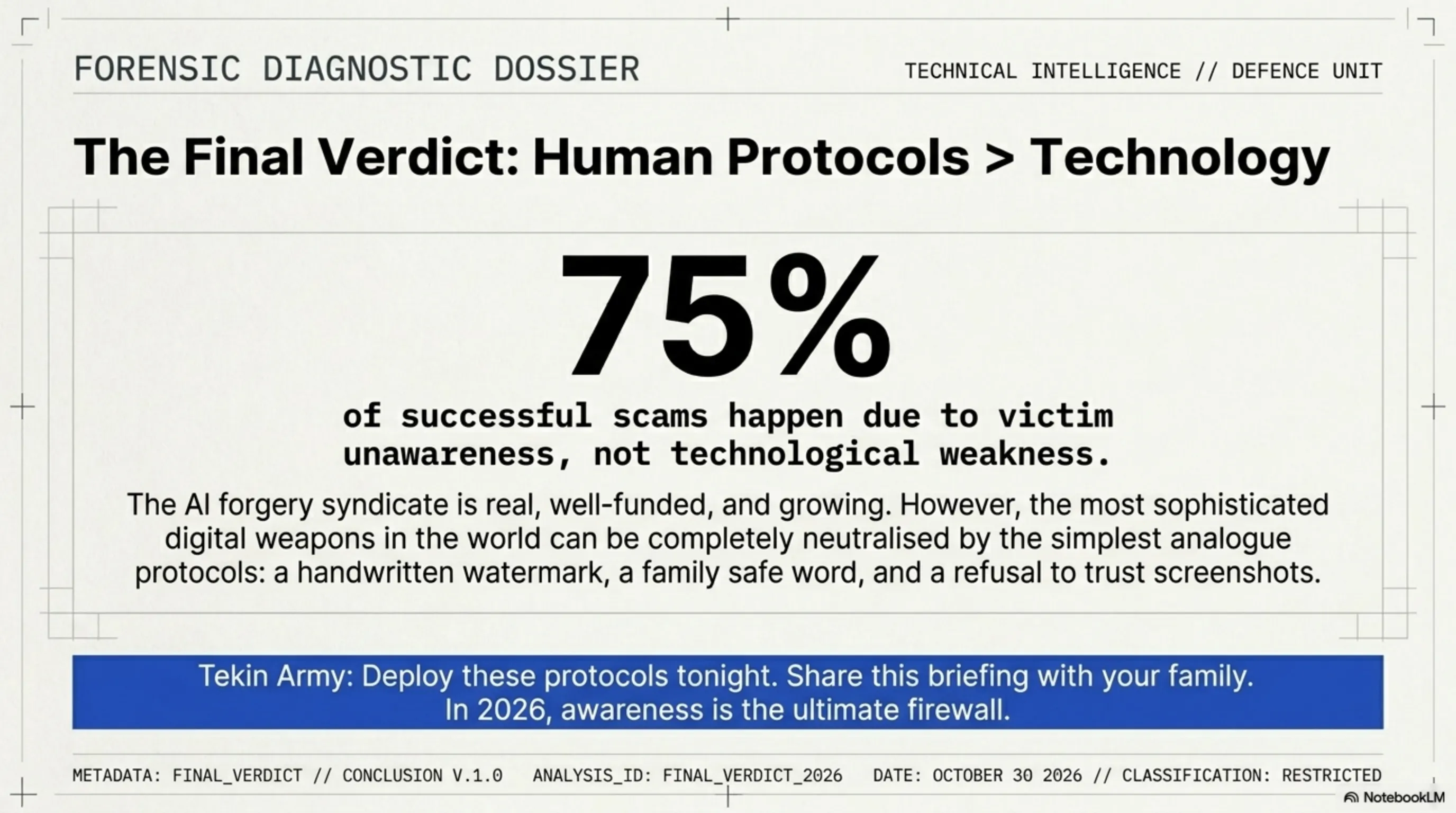
🧠 Final Verdict — Tekin's Message to the Tekin Army
The AI forgery syndicate is real and growing. But the good news: the simplest protocols are the most effective defense. Manual watermarks on documents. Family safe word. Zero-Trust for bank receipts. And education — because 75% of successful scams happen due to victim unawareness, not technology weakness. Tekin Army, share this article with your family. This information could save a life one day.
📚 Sources & References
- Sumsub Identity Fraud Report 2025
- Trend Micro — AI Voice Cloning Scams 2025 ($5M losses)
- Resistant.AI — Global Document Fraud Report 2026
- Deepstrike.io — Deepfake Statistics 2025
- FamilyVest — Deepfake losses $1.1B in 2025
- American Banker — "This is an arms race": Banks cope with AI-faked documents
- Zyphe — AI fake IDs for $15 in 2 minutes
- Tekin Editorial Team — Analysis and defense recommendations
🌐 Stay Connected With Us
For the latest cybersecurity, tech, and gaming news, follow us:
Supplementary Image Gallery: 🕵️ Anatomy of the AI Forgery Syndicate: How to Debug Reality