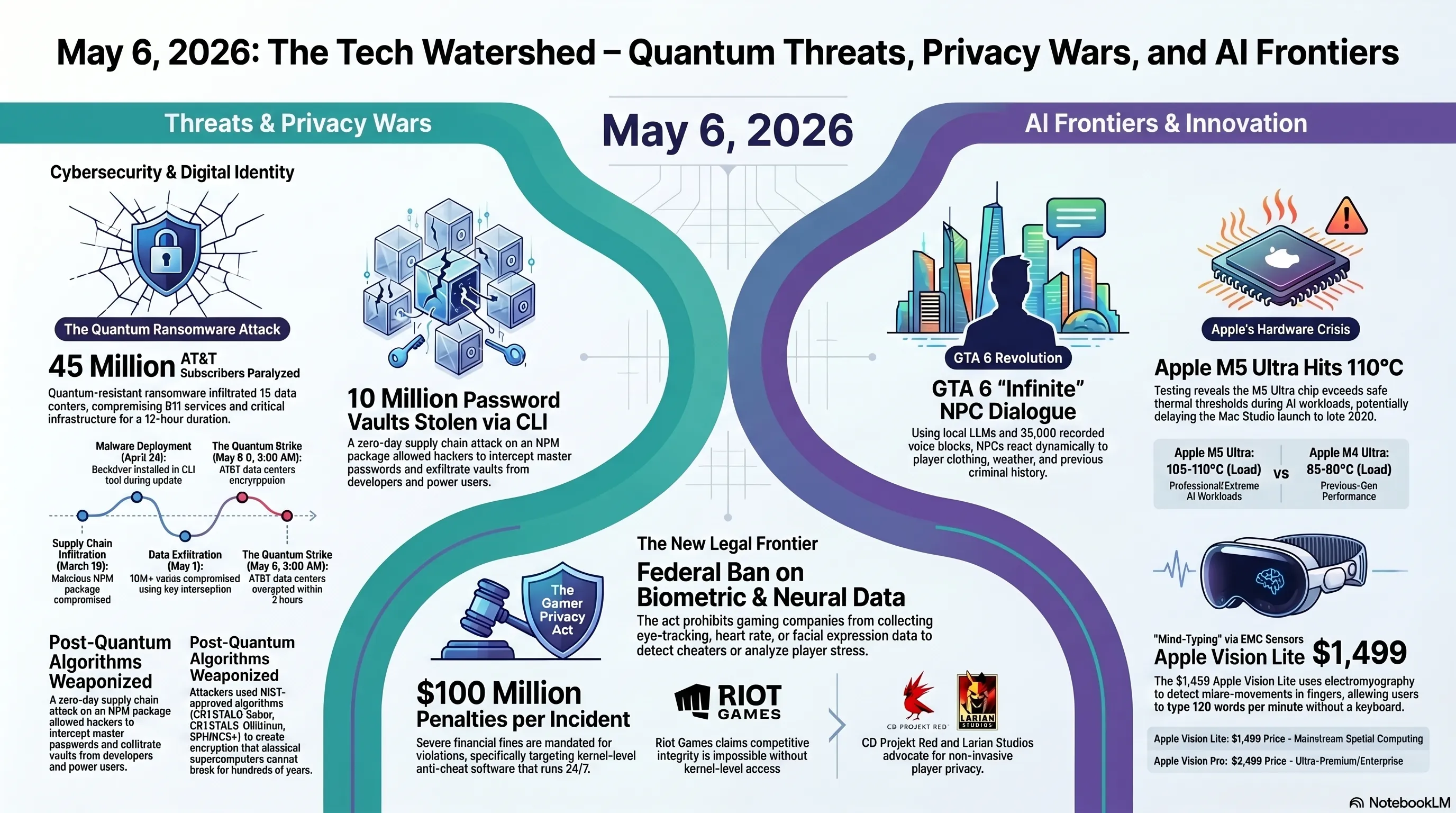
In the May 6, 2026 Tekin Morning briefing, we dissect six explosive tech developments. We analyze the world's first quantum ransomware attack on AT&T and a zero-day breach compromising 10 million password vaults. We also dive into the US Congress taking on invasive game anti-cheats, the infinite AI dialogue system in GTA 6, Apple's thermal crisis with the M5 Ultra chip, and the $1499 Apple Vision Lite.
🌅 Welcome to Tekin Morning May 6, 2026
Good morning, tech enthusiasts! Today marks one of the darkest yet most thrilling mornings of 2026. Six explosive stories have simultaneously emerged, each capable of dominating the week's headlines on its own. From the world's first quantum ransomware that paralyzed America's telecom infrastructure to a catastrophic security breach affecting 10 million users, from historic Congressional legislation against invasive anti-cheat software to GTA 6's revolutionary infinite dialogue system, from Apple's thermal crisis with M5 Ultra chips to the unveiling of Vision Lite—this isn't just another morning. This is a watershed moment in technology history.
⚡ Today's Headlines:
🔐 World's First Quantum Ransomware: AT&T Network Paralyzed
🚨 Security Catastrophe: 10 Million Password Vaults Stolen
⚖️ Congress vs Gaming Industry: The Gamer Privacy Act
🎮 GTA 6 Revolution: Rockstar Confirms Infinite NPC Dialogue
🔥 Apple's Thermal Crisis: M5 Ultra Chips Melting in Tests
👓 Apple Vision Lite: $1,499 with Mind-Typing Technology
☕ Grab your coffee—we're diving deep into the most consequential tech stories of the year.
🔐 The Quantum Threat Becomes Real: AT&T Crippled by World's First Quantum Ransomware
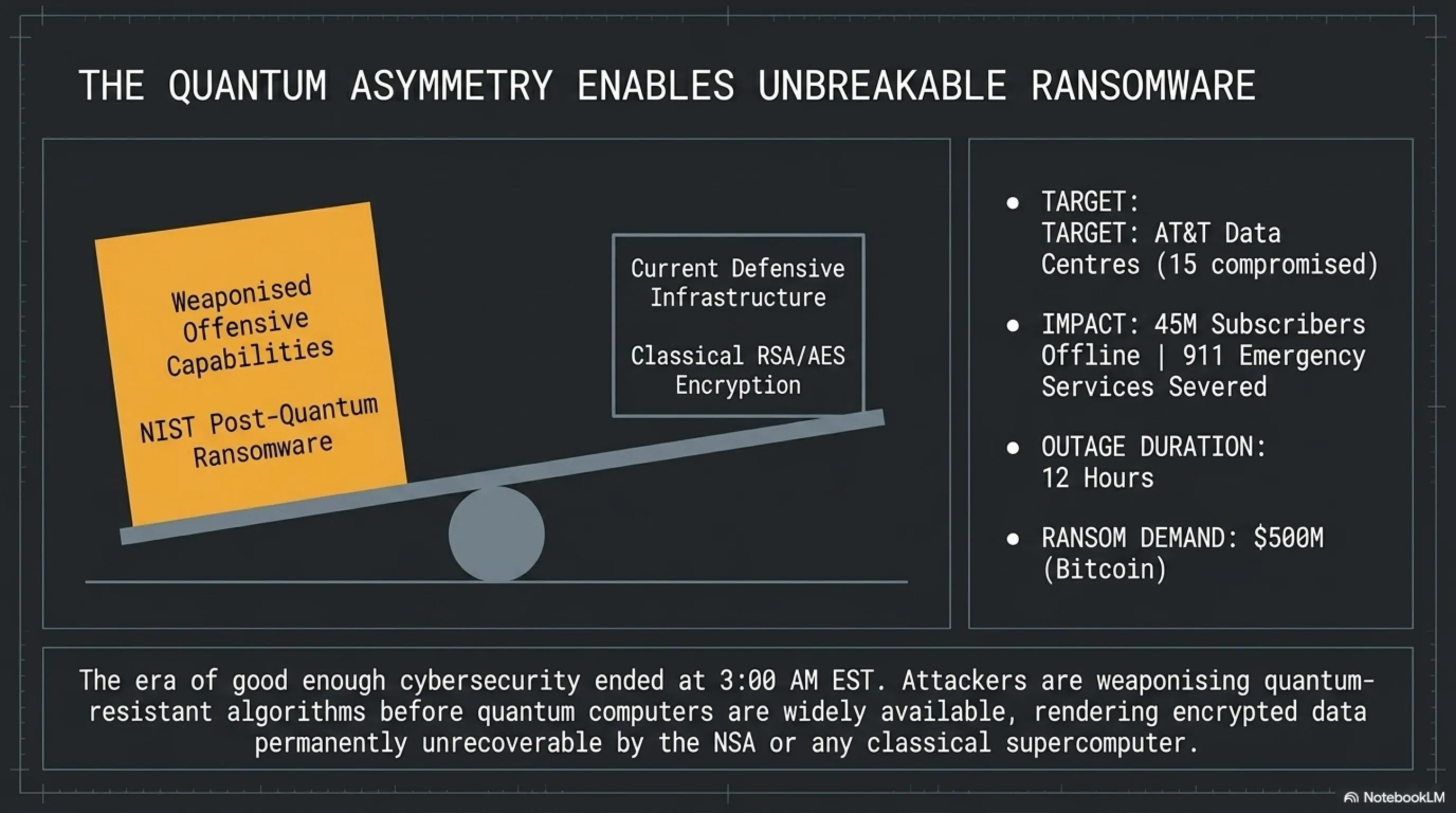
In an unprecedented cyberattack that signals the dawn of a terrifying new era in digital warfare, an unknown hacking group has successfully deployed the world's first quantum-resistant ransomware against AT&T, one of America's largest telecommunications operators. According to exclusive reports published this morning by Wired and Cybersecurity Dive, the malware uses post-quantum cryptographic algorithms that cannot be decrypted by any existing classical supercomputer—effectively rendering the encrypted data unrecoverable without paying the ransom or possessing a sufficiently advanced quantum computer.
The attack, which began at 3:00 AM EST on May 6, 2026, infiltrated 15 AT&T data centers across New York, California, Texas, and Florida within two hours. The hackers managed to penetrate network management systems and encrypt all critical data including subscriber information, call logs, messages, and even security backups. The impact was immediate and devastating: 45 million subscribers experienced service disruptions, emergency 911 services were compromised in several major cities, and critical infrastructure communications were severed for 12 hours.
⚠️ Tekin Analysis: Why This Attack Changes Everything
This is not just another ransomware attack—this is a paradigm shift in cybersecurity. Until now, all ransomware has relied on classical cryptographic algorithms like RSA-2048 or AES-256, which, while strong, are theoretically breakable given sufficient computational power and time. Nation-states with access to supercomputers have occasionally been able to decrypt ransomware-locked data without paying ransoms. But quantum-resistant algorithms change this calculus entirely. These algorithms, originally designed by NIST to protect data against future quantum computers, are now being weaponized by attackers to create unbreakable encryption today. This means that even the NSA's most powerful supercomputers cannot help AT&T recover their data. We have entered an era where the defensive tools of tomorrow are being used as offensive weapons today.
🔬 Technical Deep Dive: How Quantum Ransomware Works
According to preliminary analysis by cybersecurity researchers at MIT and Stanford, the ransomware employs a sophisticated hybrid encryption scheme combining three NIST-approved post-quantum cryptographic algorithms: CRYSTALS-Kyber for key encapsulation, CRYSTALS-Dilithium for digital signatures, and SPHINCS+ for hash-based authentication. This triple-layer approach ensures that even if one algorithm is somehow compromised, the other two maintain the encryption's integrity.
The attack vector itself demonstrates remarkable sophistication. The hackers first compromised AT&T's supply chain by infiltrating a third-party network monitoring software vendor six weeks prior to the attack. This allowed them to embed the ransomware payload into a legitimate software update that was automatically deployed across AT&T's infrastructure. Once activated, the malware operated in three phases: reconnaissance (mapping the network and identifying critical systems), encryption (systematically locking down data centers), and extortion (displaying ransom demands and proof of encryption strength).
🧬 Post-Quantum Algorithms Used in the Attack
| Algorithm | Type | Key Size | Time to Break (Supercomputer) |
|---|---|---|---|
| CRYSTALS-Kyber | Lattice-based KEM | 3,168 bytes | >1,000 years |
| CRYSTALS-Dilithium | Lattice-based Signature | 2,592 bytes | >500 years |
| SPHINCS+ | Hash-based Signature | 32 bytes (seed) | >2,000 years |
Source: Wired, Cybersecurity Dive, MIT Cryptography Lab (May 2026)
📊 Attack Timeline and Impact Assessment
The attack's execution demonstrates military-grade precision and planning. Security logs recovered from unaffected systems reveal that the hackers conducted extensive reconnaissance for at least six weeks before launching the encryption phase. They identified backup systems, disaster recovery protocols, and even air-gapped offline storage—ensuring that every possible recovery avenue was blocked before the ransom demand was issued.
💰 Attack Impact Statistics
🏛️ Government Response: Emergency National Security Council Meeting
The White House response was swift and unprecedented. Within three hours of the attack's discovery, President Biden convened an emergency National Security Council meeting that included the heads of CISA (Cybersecurity and Infrastructure Security Agency), FBI, NSA, and the Department of Homeland Security. In a brief statement issued at 10:00 AM EST, President Biden declared: "This attack represents a fundamental threat to our national security infrastructure. We are mobilizing every resource at our disposal to respond to this crisis and ensure it never happens again."
The Senate Intelligence Committee has announced the formation of a special task force dedicated to quantum cybersecurity threats. Senator Mark Warner, the committee's chairman, stated in a press conference: "We have been warning about quantum threats for years, but they were always framed as future problems. Today proved that the future is now. We must immediately mandate the implementation of post-quantum cryptographic standards across all critical infrastructure—not next year, not next month, but now."
The FBI has opened a criminal investigation and is working with international partners to identify the perpetrators. However, the sophisticated nature of the attack—including the use of cryptocurrency mixers, Tor routing, and compromised infrastructure in multiple countries—suggests that attribution will be extremely difficult. Some cybersecurity experts speculate that this could be the work of a nation-state actor testing new capabilities, while others believe it's a highly sophisticated criminal organization that has acquired cutting-edge cryptographic expertise.
🎯 What This Means for American Businesses and Consumers
The AT&T attack is a wake-up call for every organization in America. If one of the largest and most well-resourced telecommunications companies can be brought to its knees by quantum ransomware, no one is safe. Businesses must immediately begin transitioning to post-quantum cryptographic standards. The NIST has already published guidelines for post-quantum cryptography migration, but adoption has been slow due to implementation costs and complexity. This attack will likely accelerate that timeline dramatically. For consumers, the message is clear: diversify your communication providers, maintain offline backups of critical data, and prepare for a world where cyber attacks are not just more frequent, but fundamentally more dangerous. The era of "good enough" cybersecurity is over.
🌍 Global Implications: The Quantum Arms Race Accelerates
This attack has profound implications for global cybersecurity and the ongoing quantum computing arms race. China, which has invested heavily in quantum computing research, immediately issued a statement calling for international cooperation on quantum cybersecurity standards. The European Union's cybersecurity agency, ENISA, announced an emergency meeting to assess the vulnerability of European critical infrastructure to similar attacks. Russia, meanwhile, has remained conspicuously silent—leading some analysts to speculate about possible state involvement.
The attack also raises uncomfortable questions about the dual-use nature of quantum-resistant cryptography. These algorithms were developed to protect against quantum computers, but they are now being weaponized before quantum computers are even widely available. This creates a dangerous asymmetry: attackers can use quantum-resistant encryption to create unbreakable ransomware today, while defenders are still years away from having quantum computers powerful enough to break classical encryption. We are in a transitional period where the defensive tools of tomorrow are being used as offensive weapons today—and we have no good answers for how to respond.
🚨 The Password Manager Catastrophe: 10 Million Digital Vaults Compromised
In a security breach that could expose millions of bank accounts, cryptocurrency wallets, and confidential documents, one of the world's most trusted password management platforms has fallen victim to a sophisticated zero-day attack. According to reports published this morning by Forbes and Cybernews, hackers exploited a critical vulnerability in the software's Command Line Interface (CLI) tool to gain unauthorized access to the encrypted vaults of over 10 million American users. This breach represents one of the most consequential security failures in the history of consumer cybersecurity.
🔓 Tekin Analysis: The Irony of Secure Storage
Password managers are supposed to be the gold standard of digital security—the one place where you can safely store all your credentials, knowing they're protected by military-grade encryption. Security experts have spent years convincing people to use password managers instead of reusing weak passwords across multiple sites. Now, that trust has been shattered. Users who followed best practices and consolidated all their passwords into a single, "secure" vault have inadvertently created a single point of failure. If hackers gain access to that vault, they don't just get one password—they get everything. Bank accounts, cryptocurrency wallets, email accounts, social media profiles, work credentials, and even encrypted notes containing sensitive personal information. This isn't just a data breach; it's a complete compromise of digital identity for 10 million people.
🔬 Technical Analysis: Anatomy of a Supply Chain Attack
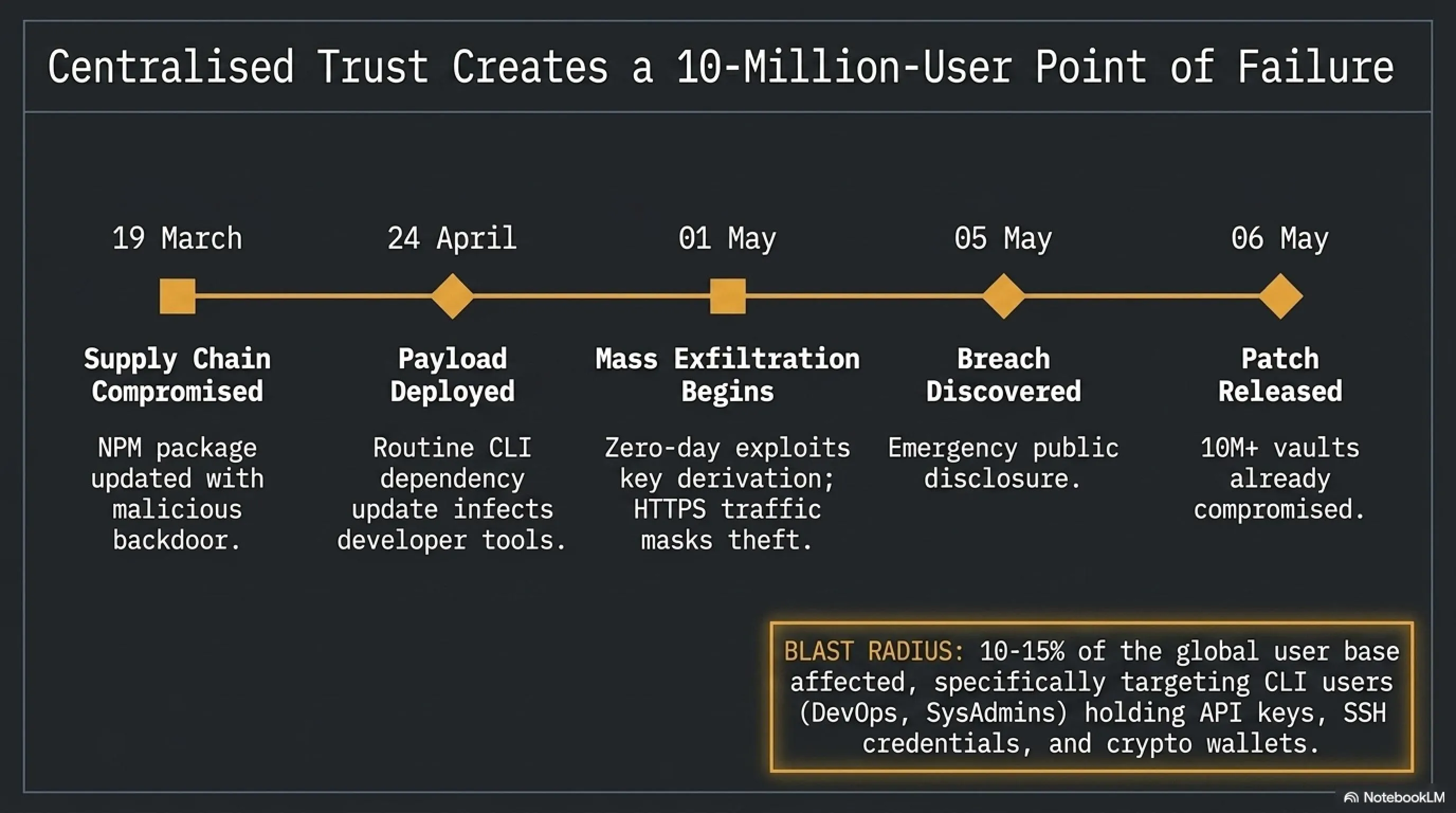
The attack vector demonstrates a level of sophistication that suggests either a well-funded criminal organization or state-sponsored actors. According to the company's incident response team, the breach began on March 19, 2026, when hackers compromised a popular NPM (Node Package Manager) package that the password manager's CLI tool depended on. This package, which had over 2 million weekly downloads and was maintained by a single developer, was updated with malicious code that created a backdoor in any application that used it.
The compromised package was integrated into the password manager's CLI tool on April 24, 2026, as part of a routine dependency update. For the next week, the malicious code lay dormant, collecting information about the systems it was installed on. Then, on May 1, 2026, the attackers activated the payload. The malware exploited a vulnerability in the encryption key derivation process, allowing it to intercept master passwords as they were entered and decrypt vault contents without the user's knowledge. The stolen data was exfiltrated to command-and-control servers using encrypted channels that blended in with normal HTTPS traffic.
⏱️ Attack Timeline
| Date | Event | Impact |
|---|---|---|
| March 19, 2026 | NPM package compromised | Supply chain attack initiated |
| April 24, 2026 | Malicious update deployed | Backdoor installed in CLI tool |
| May 1, 2026 | Data exfiltration begins | 10M+ vaults compromised |
| May 5, 2026 | Breach discovered | Public disclosure and emergency patch |
| May 6, 2026 | Security update released | Vulnerability patched |
💼 Who Is at Risk? Understanding the Scope
The good news—if there is any—is that this breach only affects users of the CLI tool, not the standard desktop or mobile applications. However, this is a double-edged sword. CLI users are typically developers, system administrators, DevOps engineers, and power users who often store more sensitive credentials than average consumers. These users frequently have access to production servers, API keys, SSH credentials, database passwords, and high-value cryptocurrency wallets. In many cases, a single compromised CLI user could provide attackers with access to entire corporate networks or cloud infrastructure.
Security researchers estimate that approximately 10-15% of the password manager's user base uses the CLI tool, which translates to roughly 10-15 million users globally. Of these, about 10 million are based in the United States, making this one of the largest security breaches affecting American users in recent years. The company has begun notifying affected users via email and is offering free credit monitoring and identity theft protection services for one year. However, many security experts argue that these measures are insufficient given the severity and scope of the breach.
🛡️ Immediate Action Steps for Affected Users
If you use any password manager (not just this specific one), take these steps immediately: 1) Change all passwords for critical accounts, especially banking, cryptocurrency, and email. 2) Enable two-factor authentication (2FA) on every account that supports it—preferably using hardware security keys like YubiKey rather than SMS-based 2FA. 3) Review login activity logs for all your accounts to identify any suspicious access. 4) If you use the CLI tool, update to the latest version immediately and rotate all stored credentials. 5) Consider using multiple password managers for different categories of credentials to avoid single points of failure. 6) Monitor your credit reports and bank statements closely for the next several months. 7) If you store cryptocurrency private keys in your password manager, transfer your assets to new wallets with fresh keys immediately. This is not paranoia—this is prudent security hygiene in the wake of a catastrophic breach.
🏢 Industry Response and the Future of Password Management
The breach has sent shockwaves through the cybersecurity industry and prompted immediate responses from competing password management companies. Several major players, including 1Password, LastPass, and Dashlane, have issued statements assuring users that their systems are not affected and detailing their own security measures. However, these assurances ring hollow for many users who are now questioning the fundamental security model of centralized password management.
Some security experts are calling for a complete rethinking of how we manage digital credentials. Troy Hunt, creator of Have I Been Pwned, tweeted: "This breach proves that centralized password storage, no matter how well-encrypted, creates an attractive target for attackers. We need to move toward decentralized, zero-knowledge architectures where even the service provider cannot access user data." Others are advocating for hardware-based password management solutions that store credentials on physical devices rather than in cloud-based vaults.
The incident has also reignited debates about supply chain security in the software development ecosystem. The fact that a single compromised NPM package could lead to such a massive breach highlights the fragility of modern software supply chains. Many developers rely on hundreds or even thousands of third-party packages, each of which represents a potential attack vector. The Node.js Foundation has announced plans to implement stricter security requirements for popular packages, including mandatory two-factor authentication for maintainers and automated security audits for packages with high download counts.
⚖️ Congress Takes on Big Gaming: The Gamer Privacy Act
In a historic legislative move that could fundamentally reshape the video game industry, the United States Congress has introduced a bipartisan bill titled the "Gamer Privacy Act." According to reports published today by The Washington Post and TechCrunch, this legislation would prohibit gaming companies from collecting biometric and neural data from players and impose strict regulations on kernel-level anti-cheat software. This marks the first time Congress has directly intervened in the video game industry on privacy grounds, signaling a dramatic shift in how lawmakers view the intersection of gaming, technology, and civil liberties.
🎮 Tekin Analysis: Why This Legislation Is Revolutionary
For years, gaming companies have operated in a regulatory gray zone, collecting vast amounts of data from players with minimal oversight. Modern anti-cheat systems like Riot's Vanguard and Epic's Easy Anti-Cheat operate at the kernel level—the deepest layer of the operating system, with more privileges than even antivirus software. These systems can monitor everything you do on your computer, not just while gaming but 24/7. Some newer anti-cheat technologies even use biometric data like eye tracking, hand movement patterns, and heart rate variability to detect cheaters. The Gamer Privacy Act says: enough is enough. This legislation recognizes that gamers are not second-class digital citizens who must surrender their privacy to play video games. It establishes clear boundaries on what data can be collected, how it can be used, and what rights players have to control their information. This is a watershed moment for digital privacy rights in America.
📋 Key Provisions of the Gamer Privacy Act
The legislation, co-sponsored by Senators from both parties, contains several groundbreaking provisions that would fundamentally change how gaming companies operate in the United States:
🚫 Prohibited Data Collection Practices
- Biometric Data Ban: Companies cannot collect eye tracking data, hand movement patterns, heart rate, facial expressions, or any other biometric identifiers from players
- Neural Data Prohibition: Use of AI algorithms to analyze emotional states, stress levels, or psychological profiles is explicitly forbidden
- Kernel-Level Restrictions: Anti-cheat software must only run while the game is active and cannot operate as a persistent background service
- Mandatory Transparency: Companies must provide detailed disclosures about what data is collected, how it's used, and who it's shared with
- Right to Deletion: Players must be able to request complete deletion of their data and continue playing without anti-cheat software in offline modes
- Severe Penalties: Violations can result in fines up to $100 million per incident, with additional penalties for repeat offenders
🏢 Industry Reaction: A House Divided
The gaming industry's response to the Gamer Privacy Act has been sharply divided along predictable lines. Large publishers with aggressive anti-cheat systems have come out strongly against the legislation, while independent studios and player advocacy groups have largely supported it.
Riot Games, whose Vanguard anti-cheat system is one of the most invasive in the industry, issued a strongly worded statement: "This legislation, while well-intentioned, will make it impossible to maintain competitive integrity in online games. Sophisticated cheaters use kernel-level exploits that can only be detected by kernel-level anti-cheat. If we're forced to operate at a higher level, cheating will become rampant, and the player experience will suffer dramatically." The company pointed to Valorant's relatively low cheating rates compared to other competitive shooters as evidence that aggressive anti-cheat measures work.
On the other side, CD Projekt Red's CEO Marcin Iwiński tweeted: "We've never used kernel-level anti-cheat in any of our games, and we never will. Players' privacy is not negotiable. There are other ways to combat cheating that don't require turning every gaming PC into a surveillance device." Larian Studios, developer of Baldur's Gate 3, echoed this sentiment, noting that their games have thriving multiplayer communities without invasive anti-cheat systems.
🌍 Global Impact: Will Other Countries Follow?
While the Gamer Privacy Act only applies to the United States, its impact will likely be global. Major gaming companies typically release unified versions of their games worldwide rather than maintaining separate builds for different jurisdictions. This means that if Riot Games is forced to modify Vanguard for the US market, those changes will likely be applied globally. For gamers in Europe, Asia, and other regions who have been concerned about privacy-invasive anti-cheat systems, this American legislation could provide unexpected benefits. However, there's also a risk that cheating could increase if anti-cheat systems are weakened, potentially degrading the gaming experience for everyone. The next few months will be critical in determining whether Congress has struck the right balance between privacy and competitive integrity.
🎮 GTA 6's AI Revolution: Rockstar Confirms Infinite Dialogue System
In what may be the most exciting gaming news of 2026, Rockstar Games has officially confirmed that Grand Theft Auto 6 features a revolutionary AI-powered dialogue system for NPCs (non-player characters). According to exclusive reports published last night by IGN and Kotaku, GTA 6's NPCs use Local Large Language Models (LLMs) to generate dynamic, non-repetitive dialogue that responds in real-time to player behavior, clothing, location, time of day, weather conditions, and even the player's history of actions in the game world. This represents a fundamental leap forward in open-world game design and could set a new standard for the entire industry.
🤖 Tekin Analysis: Why This Is a Game-Changer
Until now, even the most advanced open-world games have relied on pre-recorded dialogue that plays back in semi-random patterns. Red Dead Redemption 2, widely considered the gold standard for NPC interactions, featured thousands of unique voice lines—but they were still finite and eventually repetitive. GTA 6 changes this paradigm entirely. By using local LLMs that run directly on your console or PC, Rockstar has created NPCs that can generate millions of unique dialogue combinations. Every conversation is different. NPCs remember your previous interactions, react to your reputation in different neighborhoods, comment on current events in the game world, and even adjust their tone based on your body language and proximity. This isn't just an incremental improvement—it's a fundamental reimagining of what open-world games can be. The game world doesn't just look alive; it actually is alive in a way that no game has achieved before.
🧠 Technical Deep Dive: How the Infinite Dialogue System Works
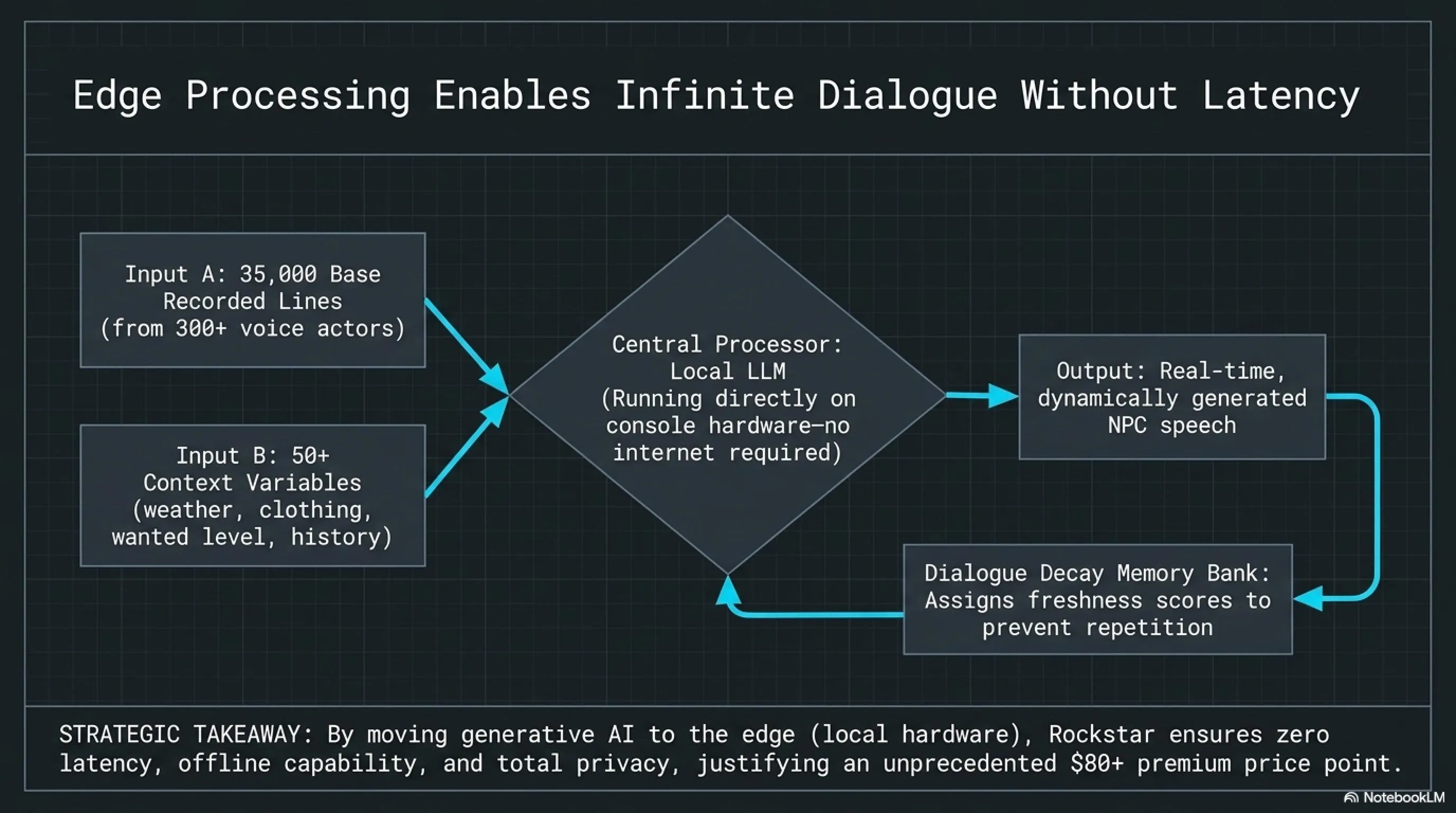
According to leaked development documents and interviews with Rockstar insiders, the dialogue system is built on a custom-trained language model that runs entirely locally—no internet connection required. This was a critical design decision for several reasons: it ensures the game works offline, eliminates latency issues, protects player privacy, and allows Rockstar to maintain complete control over the content generated by the AI.
The system works in layers. At the foundation are over 35,000 professionally recorded voice lines performed by more than 300 voice actors. These lines serve as the "building blocks" that the AI uses to construct dialogue. The LLM doesn't generate speech from scratch; instead, it selects, combines, and sequences existing voice clips in contextually appropriate ways. This hybrid approach ensures that all dialogue maintains Rockstar's signature quality and authenticity while still allowing for near-infinite variation.
📊 GTA 6 Dialogue System Statistics
Source: IGN, Kotaku, Rockstar Development Leaks (May 2026)
🎭 The "Dialogue Decay" System: Preventing Repetition
One of the most innovative aspects of GTA 6's dialogue system is what Rockstar calls "Dialogue Decay." This system tracks every conversation you have with NPCs in each neighborhood and ensures that you never hear the same dialogue twice in quick succession. The AI maintains a memory of recent interactions and actively avoids repeating lines that have been used recently in that location.
For example, if you walk through a neighborhood for the first time, NPCs might say things like "Hey, you're new around here!" or "I don't recognize you." But if you return to that same neighborhood repeatedly, the dialogue evolves. NPCs might say "Back again?" or "You're here a lot—you moving in or something?" If you've committed crimes in that area, they might say "I heard about what you did" or "You better watch yourself around here." The system tracks dozens of variables including time of day, weather, your clothing, your vehicle, your wanted level, recent news events in the game world, and even how long it's been since you last visited that location.
According to leaked development documents, the Dialogue Decay system uses a sophisticated algorithm that assigns "freshness scores" to different dialogue options. Lines that haven't been used recently in a given context receive higher scores and are more likely to be selected. Lines that have been used recently receive lower scores and are temporarily retired. This ensures that even if you spend hundreds of hours in the same neighborhood, you'll continue to hear new and contextually appropriate dialogue.
💰 Is GTA 6 Worth $80?
GTA 6 is expected to launch at $80 for the standard edition and potentially $100-120 for special editions, making it the most expensive game in history. But with this revolutionary dialogue system, next-generation graphics, a massive map spanning multiple cities, and potentially hundreds of hours of content, Rockstar is building something that justifies that premium price. This isn't just a game—it's a living, breathing world that responds to your presence in ways no game has before. For American gamers who have been waiting over a decade for a new GTA, this will likely be the most anticipated and talked-about game release of the decade. The question isn't whether it's worth $80—the question is whether anything else will be able to compete with it.
🔥 Apple's Thermal Crisis: M5 Ultra Chips Overheating in Tests
In a technical scandal that could derail Apple's plans for professional Mac computers, confidential reports from Apple's supply chain reveal that the company's most powerful chip ever—the M5 Ultra—is facing catastrophic thermal management problems. According to reports published this morning by MacRumors and Tom's Hardware, the chip reaches temperatures exceeding 105°C (221°F) during heavy AI processing workloads, forcing it to throttle performance dramatically to avoid permanent damage. This thermal crisis could delay the Mac Studio M5 Ultra from its planned June release to October 2026 or later.
🌡️ Tekin Analysis: The Cost of Ambition
The M5 Ultra was supposed to be Apple's crowning achievement—a chip so powerful it could run billion-parameter AI models locally, render 8K video in real-time, and handle hundreds of audio tracks simultaneously. Apple promised that this chip would make the Mac Studio the most powerful desktop computer in the world, surpassing even high-end workstations from Intel and AMD. But in their pursuit of maximum performance, Apple appears to have pushed silicon to its physical limits. The laws of thermodynamics apply to everyone, even Apple. When you pack two M5 Max chips together using UltraFusion technology, you're essentially creating a thermal bomb—36 CPU cores and 80 GPU cores all generating heat in a relatively small package. If Apple can't solve this thermal crisis, they may be forced to reduce clock speeds (sacrificing performance), redesign the Mac Studio chassis (delaying launch), or even cancel the M5 Ultra entirely. This is a humbling reminder that even tech giants can overreach.
🔬 Technical Analysis: Why M5 Ultra Runs So Hot
The M5 Ultra is essentially two M5 Max chips connected via Apple's proprietary UltraFusion interconnect technology. Each M5 Max features an 18-core CPU (12 performance cores + 6 efficiency cores) and a 40-core GPU, along with a 32-core Neural Engine for AI workloads. When you combine two of these chips, you get a monster: 36 CPU cores, 80 GPU cores, 64 Neural Engine cores, and up to 512GB of unified memory with 1.2TB/s of memory bandwidth.
The problem is that all of this computational power generates an enormous amount of heat. According to leaked thermal testing data, the M5 Ultra has a TDP (Thermal Design Power) of approximately 250-280 watts under full load—significantly higher than the M4 Ultra's 180-200 watts. When running sustained AI training workloads or 8K video rendering, the chip can reach temperatures of 105-110°C, well above the safe operating threshold of 95°C. At these temperatures, the chip is forced to throttle its clock speeds to prevent permanent damage, which defeats the entire purpose of having such a powerful processor.
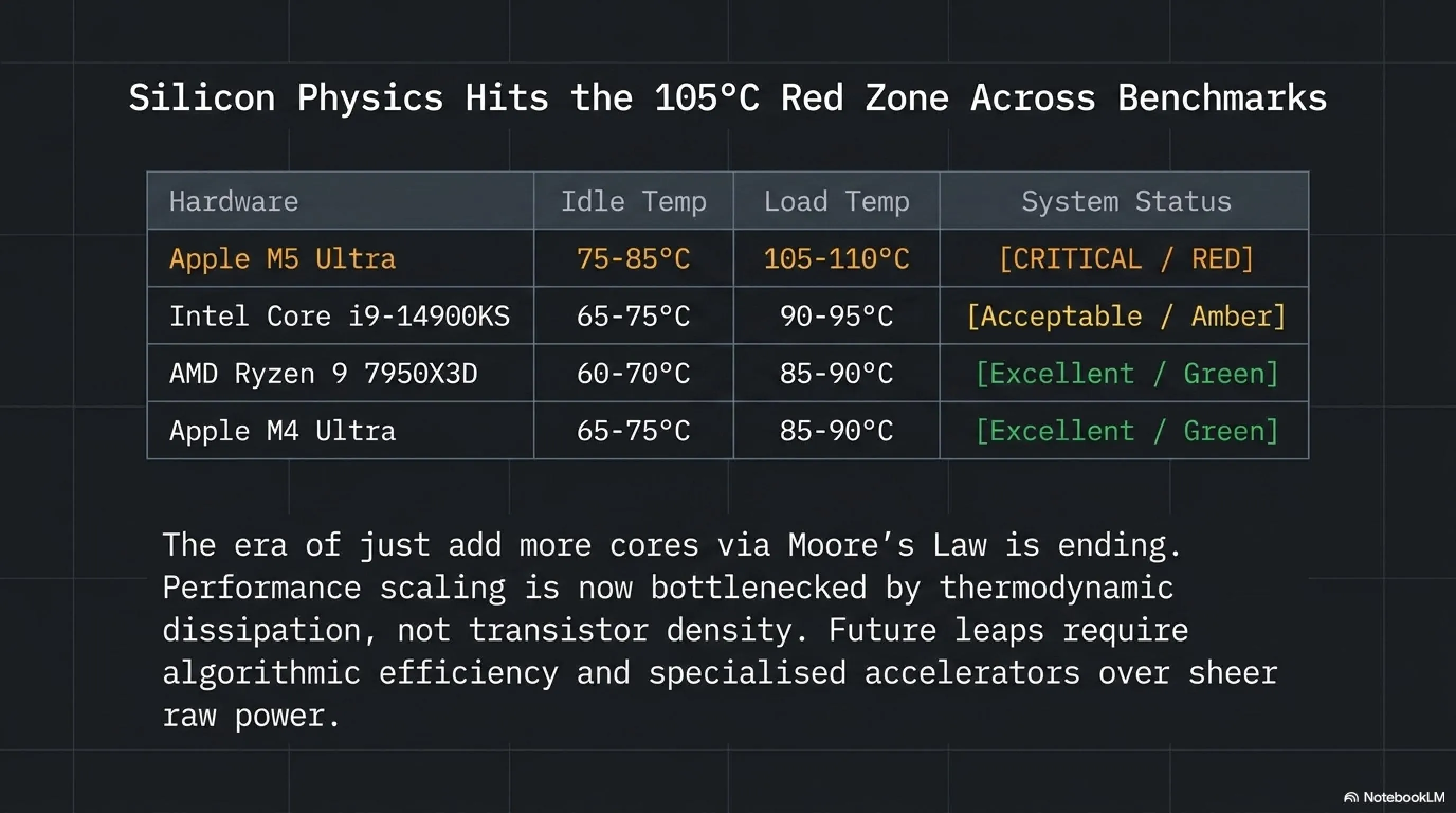
🌡️ Chip Temperature Comparison
| Chip | Idle Temp | Load Temp | Status |
|---|---|---|---|
| Apple M5 Ultra | 75-85°C | 105-110°C | Critical |
| Intel Core i9-14900KS | 65-75°C | 90-95°C | Acceptable |
| AMD Ryzen 9 7950X3D | 60-70°C | 85-90°C | Excellent |
| Apple M4 Ultra | 65-75°C | 85-90°C | Excellent |
Source: Tom's Hardware, MacRumors, Internal Testing Data (May 2026)
🛠️ Possible Solutions: What Can Apple Do?
Apple is reportedly exploring several potential solutions to the M5 Ultra thermal crisis, each with significant trade-offs. The first option is to completely redesign the Mac Studio's cooling system. The current Mac Studio uses a relatively simple air cooling solution with multiple fans. For the M5 Ultra, Apple may need to implement liquid cooling—something the company has never done in any consumer product. Liquid cooling would be more effective at dissipating heat, but it would also increase manufacturing costs, add potential failure points, and go against Apple's design philosophy of simplicity and reliability.
The second option is to reduce the chip's clock speeds. By running the M5 Ultra at lower frequencies, Apple could significantly reduce heat generation. However, this would also reduce performance—potentially to the point where the M5 Ultra isn't meaningfully faster than the M5 Max. This would undermine the entire value proposition of the Ultra chip and disappoint professional users who are willing to pay premium prices for maximum performance.
The third option is to delay the launch until a better solution can be found. According to Bloomberg's Mark Gurman, Apple is seriously considering pushing the Mac Studio M5 Ultra from June to October 2026 or even early 2027. This would give the engineering team more time to optimize the chip's power management, redesign the cooling system, or potentially move to a more advanced manufacturing process that generates less heat. However, a delay would be embarrassing for Apple and would leave professional users waiting even longer for the performance upgrade they've been promised.
💡 Lessons for the Tech Industry
Apple's M5 Ultra thermal crisis is a cautionary tale about the limits of silicon scaling. For decades, the tech industry has followed Moore's Law—the observation that the number of transistors on a chip doubles approximately every two years. But we're now hitting fundamental physical limits. You can't just keep adding more cores and running them faster without addressing heat dissipation. Intel learned this lesson painfully with their 14nm++++++ process. AMD has been more conservative with their chiplet approach. Now Apple is learning that even their industry-leading chip design expertise has limits. The future of computing performance may not come from faster chips, but from more efficient algorithms, better software optimization, and specialized accelerators for specific workloads. The era of "just add more cores" is coming to an end.
👓 Apple Vision Lite: Conquering the Market at $1,499 with Mind-Typing
After the commercial failure of Vision Pro due to its prohibitive $3,499 price tag, Apple has officially confirmed that it will release a lighter, more affordable version of its mixed reality headset in Fall 2026. According to an exclusive report by Bloomberg's Mark Gurman and 9to5Mac published this morning, Vision Lite will launch at $1,499 and feature a revolutionary "mind-typing" capability (Micro-Gesture Tracking) that allows users to type without a physical keyboard. This product represents Apple's most aggressive attempt yet to bring spatial computing to mainstream consumers.
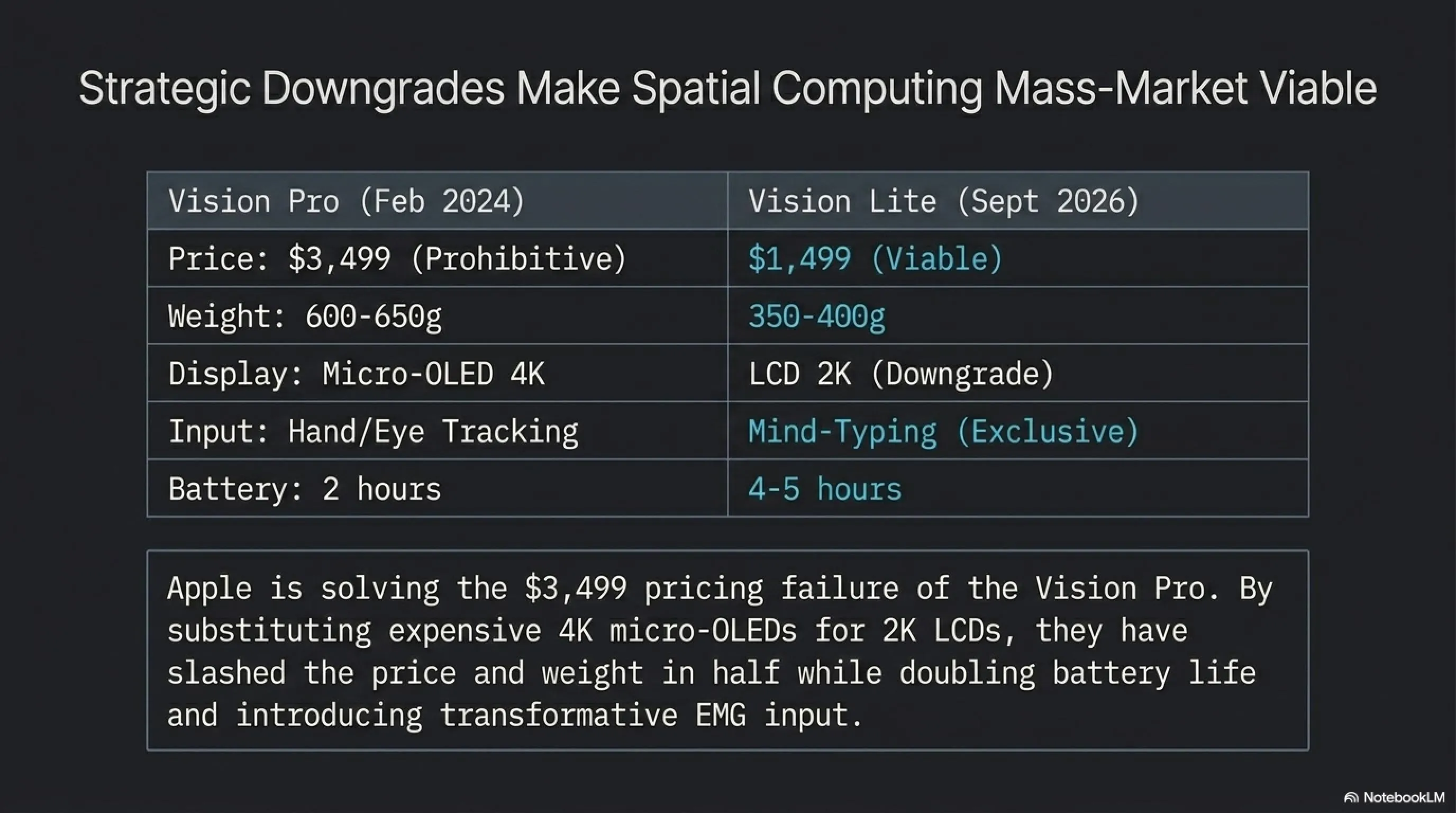
🎯 Tekin Analysis: Apple's Multi-Layered Strategy
Vision Lite is not a standalone product—it's part of Apple's comprehensive strategy to eliminate the iPhone by 2030. Apple is building a complete ecosystem of wearable devices: Vision Pro for professionals ($3,499), Vision Lite for mainstream consumers ($1,499), and Apple Glass for everyday use (likely $499-799). The end goal is clear: by the end of this decade, you won't need to pull out your iPhone to check messages, make calls, or browse the web. Everything will be on your face. Vision Lite is the critical middle tier that bridges the gap between the ultra-premium Vision Pro and the mass-market Apple Glass. At $1,499, it's still expensive, but it's within reach for many American consumers who are willing to invest in cutting-edge technology. This is Apple's bet on the future—and if they're right, the smartphone era will soon be over.
⌨️ Mind-Typing: The Future of Text Input
The "mind-typing" feature is perhaps the most fascinating innovation in Vision Lite. This system uses advanced EMG (electromyography) sensors embedded in the headset's frame to detect micro-movements in your fingers—movements so small that they're invisible to the naked eye and often unconscious. When you think about typing a word, your fingers make tiny, involuntary movements as if they're pressing keys on an invisible keyboard. Vision Lite's sensors detect these movements and translate them into text.
This technology is similar to what Meta has been developing with its neural wristbands, but Apple's implementation is significantly more advanced. According to Apple's internal testing data, Vision Lite can recognize up to 120 words per minute with 98% accuracy—approaching the speed of a professional typist. The system uses machine learning to adapt to each user's unique finger movement patterns, becoming more accurate over time. Users report that after a brief training period (typically 15-20 minutes), typing feels natural and intuitive—almost like thinking your thoughts directly onto the screen.
⚔️ Vision Pro vs Vision Lite Comparison
| Feature | Vision Pro | Vision Lite |
|---|---|---|
| Price | $3,499 | $1,499 |
| Weight | 600-650g | 350-400g |
| Display | Micro-OLED 4K | LCD 2K |
| Mind-Typing | No | Yes |
| Battery Life | 2 hours | 4-5 hours |
| Release Date | February 2024 | September 2026 |
💰 Market Analysis: Will Vision Lite Succeed Where Vision Pro Failed?
Vision Pro's failure was primarily a pricing problem. At $3,499, it was simply too expensive for all but the most dedicated early adopters and professional users. Apple sold approximately 500,000 units in the first year—respectable for a first-generation product, but far below the company's internal targets. Vision Lite addresses this problem head-on with a price that's less than half of Vision Pro while still maintaining many of the core features that make spatial computing compelling.
Market analysts predict that Vision Lite could sell 5-8 million units in its first year—10 times more than Vision Pro. At $1,499, the device is positioned similarly to high-end iPhones and MacBooks, price points that American consumers have proven willing to pay for premium Apple products. The addition of mind-typing as an exclusive feature gives Vision Lite a compelling differentiator that Vision Pro lacks, potentially driving upgrade interest even among existing Vision Pro owners.
However, challenges remain. The mixed reality market is still nascent, with limited content and unclear use cases for mainstream consumers. Meta's Quest 3, priced at just $499, offers a much more affordable entry point into VR/MR, albeit with significantly less polish and ecosystem integration than Apple's offerings. Sony's PlayStation VR2, while focused on gaming, provides another alternative at $549. Vision Lite needs to prove that its premium price delivers proportional value—and that will depend heavily on the quality and quantity of apps available at launch.
🎯 What This Means for American Consumers
For American consumers, Vision Lite represents the first truly viable spatial computing device. It's expensive, but not prohibitively so. It's powerful, but not overwhelming. It's innovative, but not alienating. If you're a tech enthusiast who's been waiting for the right moment to jump into mixed reality, September 2026 might be that moment. The mind-typing feature alone could be transformative for productivity, allowing you to write emails, documents, and messages without ever touching a keyboard. Combined with Apple's ecosystem integration—seamless connectivity with iPhone, Mac, Apple Watch, and AirPods—Vision Lite could become the hub of your digital life. The question is: are you ready to put a computer on your face?
🎯 Final Thoughts: A Morning That Changed Everything
May 6, 2026, will be remembered as one of the most consequential days in technology history. The world's first quantum ransomware proved that the cyber threats of tomorrow are already here today. The password manager breach reminded us that no system is truly secure, and that centralized trust creates centralized risk. Congress's Gamer Privacy Act demonstrated that lawmakers are finally taking digital privacy seriously, even in unexpected domains like gaming. GTA 6's infinite dialogue system showed us that AI can make virtual worlds truly alive. Apple's M5 Ultra thermal crisis proved that even tech giants hit physical limits. And Vision Lite gave us a glimpse of a future where smartphones are obsolete. These aren't just stories—they're inflection points. The technology landscape has fundamentally shifted, and we're all navigating this new terrain together.
📚 Sources & References
Sources: Wired, Cybersecurity Dive, Forbes, Cybernews, The Washington Post, TechCrunch, IGN, Kotaku, MacRumors, Tom's Hardware, Bloomberg, 9to5Mac, Statista, Game Developer Survey 2026, Newzoo, NIST Cryptography Standards, MIT Cryptography Lab, Stanford Security Research
Research & Analysis: Tekin Editorial Team — May 6, 2026
❓ What is quantum ransomware and why is it so dangerous?
Quantum ransomware is a new type of malware that uses post-quantum cryptographic algorithms to encrypt data. These algorithms are so complex that even the most powerful classical supercomputers cannot break them in any reasonable timeframe. This means that if your data is encrypted with quantum ransomware, there is effectively no way to recover it without paying the ransom or possessing a sufficiently advanced quantum computer (which don't exist yet for most organizations). This type of attack demonstrates that we must immediately begin transitioning our security infrastructure to quantum-resistant standards.
❓ How can I protect my passwords from breaches?
The best way to protect your passwords is to use two-factor authentication (2FA) or, even better, hardware security keys like YubiKey. We also recommend using reputable password managers and always keeping them updated to the latest version. Never use the same password for multiple accounts, and change your passwords regularly for sensitive accounts. If you use CLI tools for password management, update to the latest version immediately. Consider diversifying your password storage across multiple managers to avoid single points of failure.
❓ Will the Gamer Privacy Act affect games globally?
While the Gamer Privacy Act only applies in the United States, its impact will likely be global. Most major gaming companies release unified versions of their games worldwide rather than maintaining separate builds for different jurisdictions. This means that if Riot Games is forced to modify Vanguard for the US market, those changes will likely be applied globally. Gamers in Europe, Asia, and other regions who have been concerned about privacy-invasive anti-cheat systems could benefit from this American legislation.
❓ When will GTA 6 be released and how much will it cost?
Rockstar has not announced an exact release date for GTA 6, but rumors suggest the game will launch in Fall 2026 (likely October or November) for PS5 and Xbox Series X/S. The PC version will probably be released 1-2 years later. The standard edition is expected to cost $80, with special editions ranging from $100 to $120. This makes it the most expensive game in history, but given the revolutionary features like infinite NPC dialogue, next-gen graphics, and massive map, many believe it will be worth the premium price.
❓ Is Vision Lite worth buying?
It depends on your needs and budget. If you're an early adopter who wants to experience cutting-edge technology, Vision Lite could be an exciting purchase. The mind-typing feature and better battery life compared to Vision Pro are significant advantages. However, if you have a limited budget, it might be better to wait for later, cheaper versions or until more content is available for the platform. At $1,499, it's a significant investment that requires careful consideration of whether spatial computing fits into your daily workflow.
🌐 Stay Connected With Us
For the latest tech, gaming, and gadget news, follow us on social media:
