In this comprehensive 8,400-word mega-guide, we dissect the ultimate survival strategies against 2026's advanced cyber threats. With the rise of AI-driven attacks, voice deepfakes, and massive Discord hacks, we teach you how to build an impenetrable digital fortress. Learn how to secure your gaming accounts and crypto assets using hardware security keys (YubiKey), advanced 2FA, and cold storage solutions.
🛡️ Welcome to Project Gamma: The 2026 Dark Web Survival Guide
As you read this, thousands of AI-powered bots are scanning gaming accounts and crypto wallets. They no longer send weak emails — they clone your voice, forge your face, and discover vulnerabilities at machine speed. The crypto industry lost over $600 million in the first four months of 2026. 40 million Discord users are at risk of voice deepfakes. And if you're not using a hardware security key, you're in the 85% most vulnerable users.
⚡ What You'll Learn in This Guide:
🔒 How YubiKey and Trezor hardware keys make you 99% safer
🎭 How voice deepfakes work and how to detect them
💰 Cold storage strategy for protecting crypto assets
🎮 Step-by-step guide to securing Steam, Discord, Epic Games
🧠 How AI is used as both weapon and shield
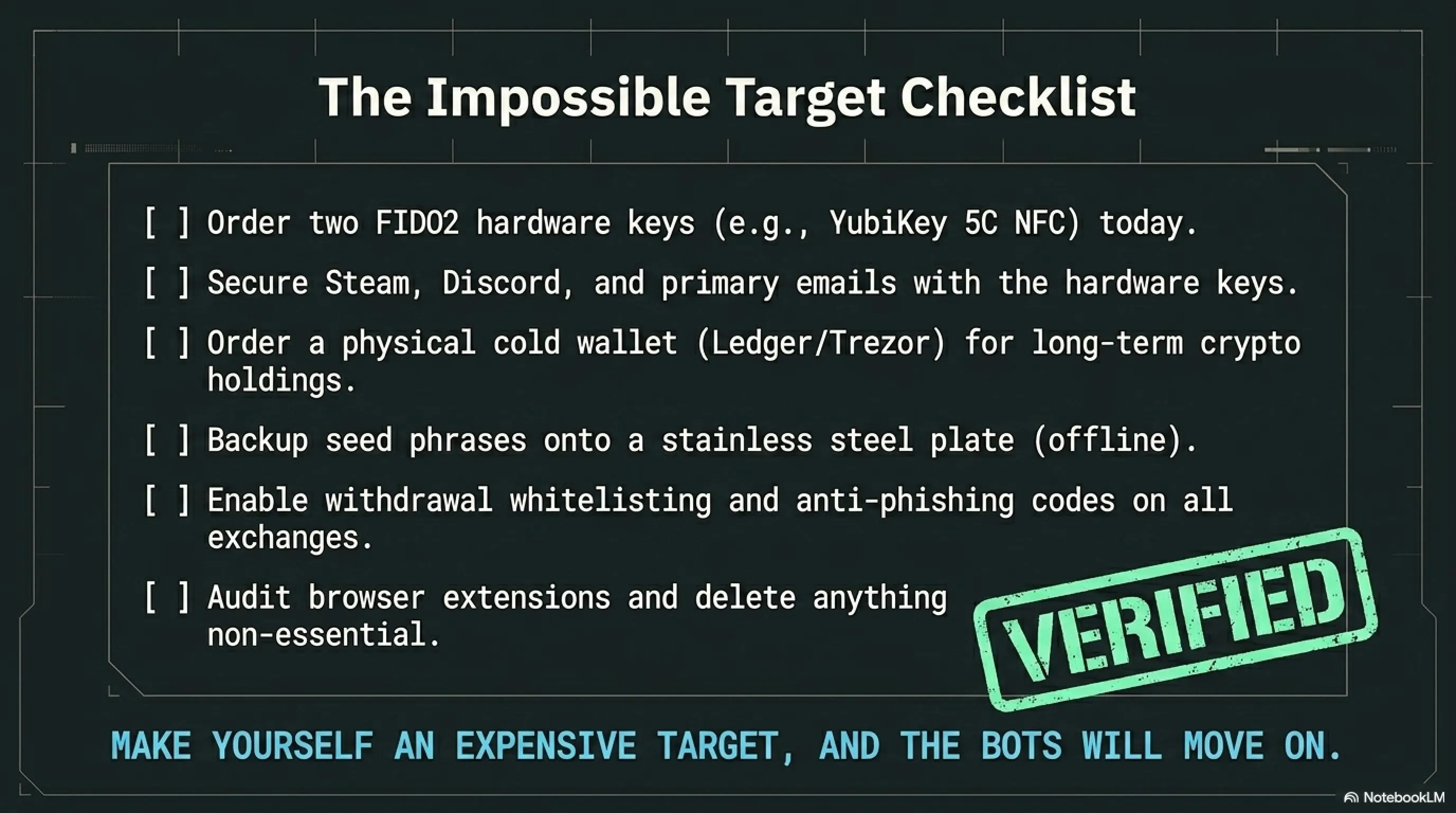
✅ 14-step checklist to become an impossible target
⚠️ This is an evergreen educational guide — not news, but a survival manual.
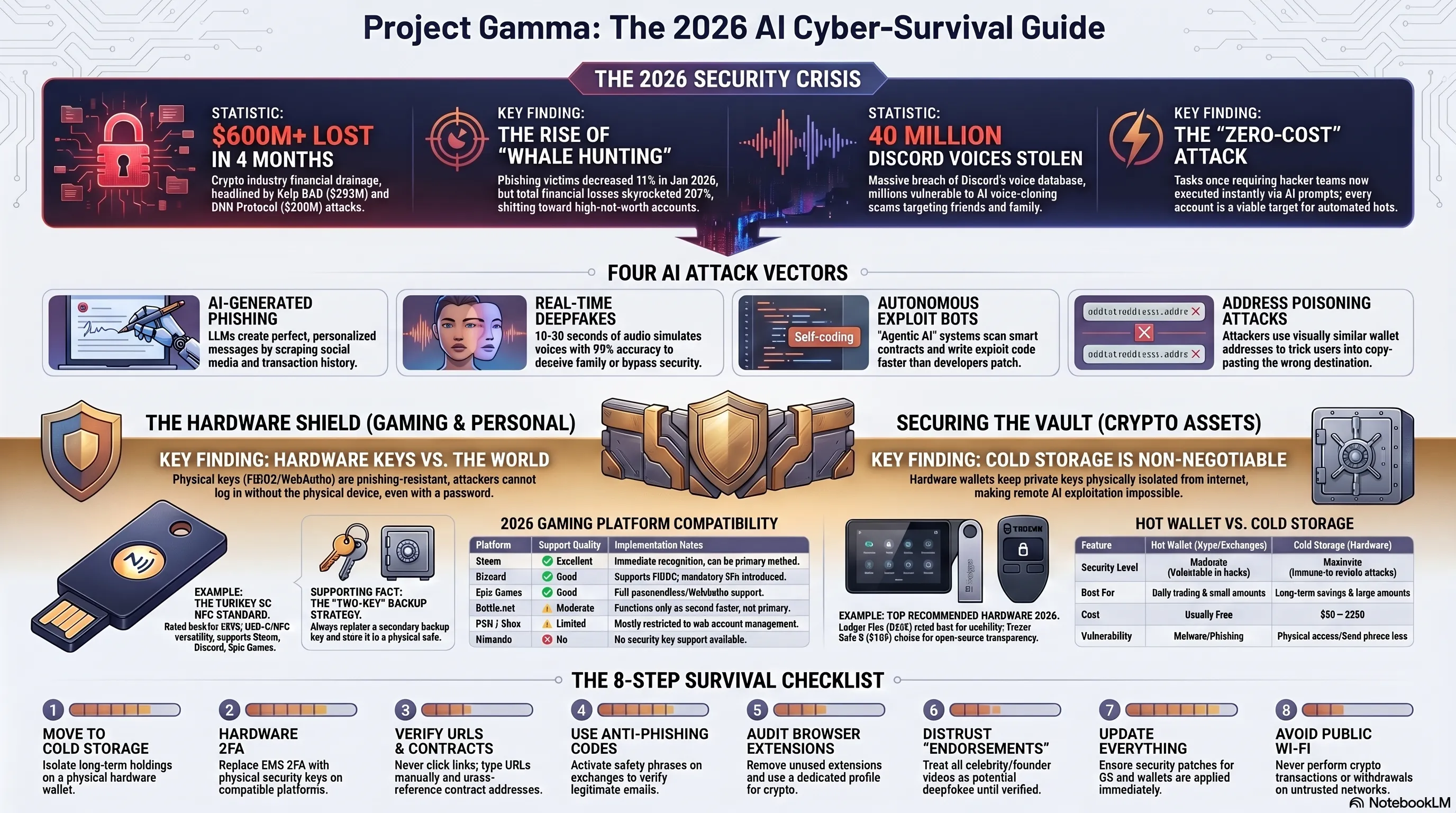
🚨 The 2026 Security Crisis: Why No One is Safe
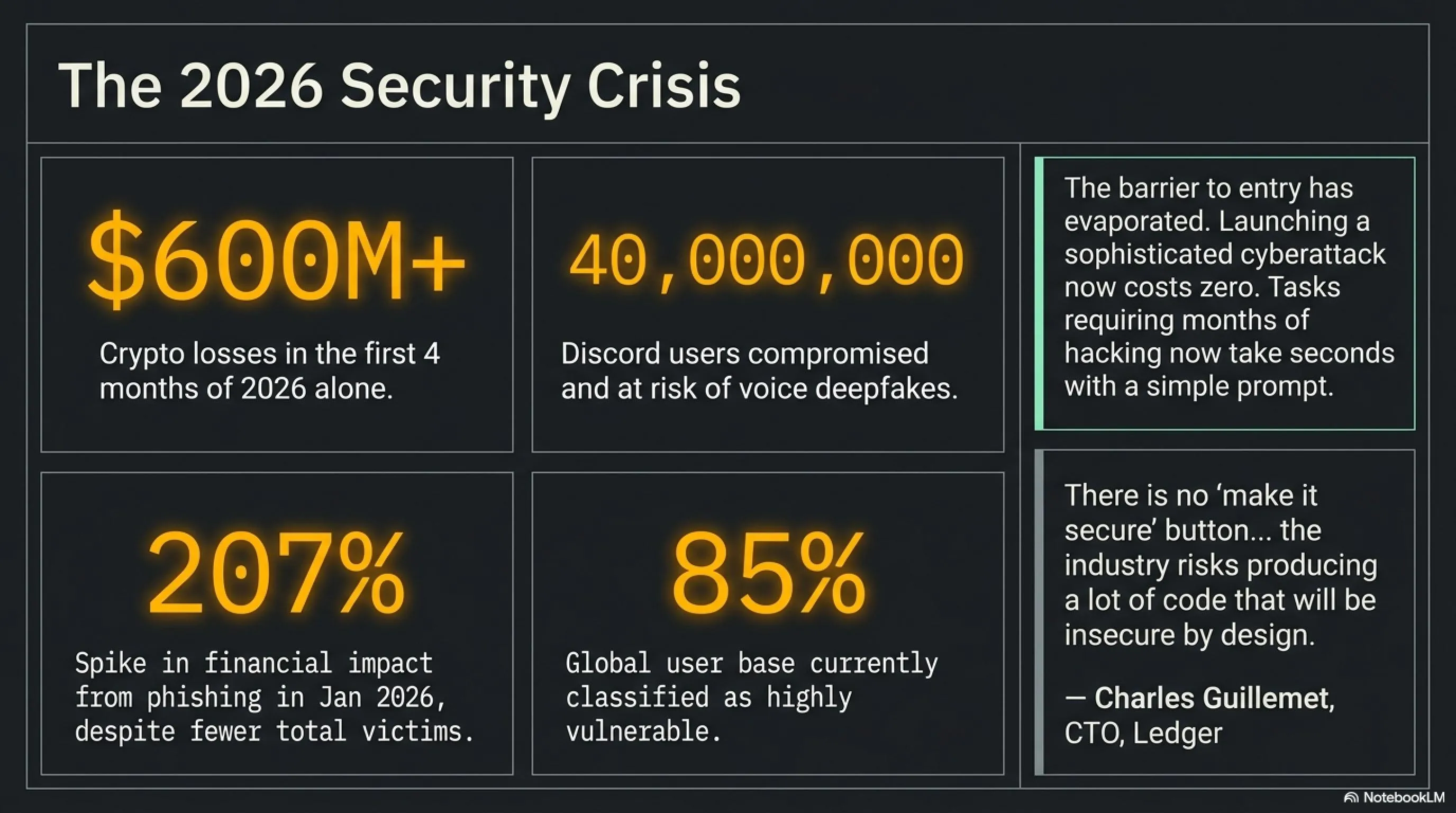
Let's start with a bitter reality: the cost of launching a sophisticated cyberattack has dropped to zero. Tasks that once required a team of skilled hackers and months of research can now be completed with a simple prompt to ChatGPT or Claude in seconds. Charles Guillemet, CTO of Ledger, warned in April 2026: "There is no 'make it secure' button, and the industry risks producing a lot of code that will be insecure by design."
According to CertiK reports, the crypto industry lost over $600 million in the first four months of 2026 due to hacks. But this is just the tip of the iceberg. The Kelp DAO attack with $293 million in damages and the Drift Protocol hack with $280 million were just two of hundreds of successful attacks. What's truly alarming is the shift in attacker tactics.
📊 Shocking 2026 Statistics
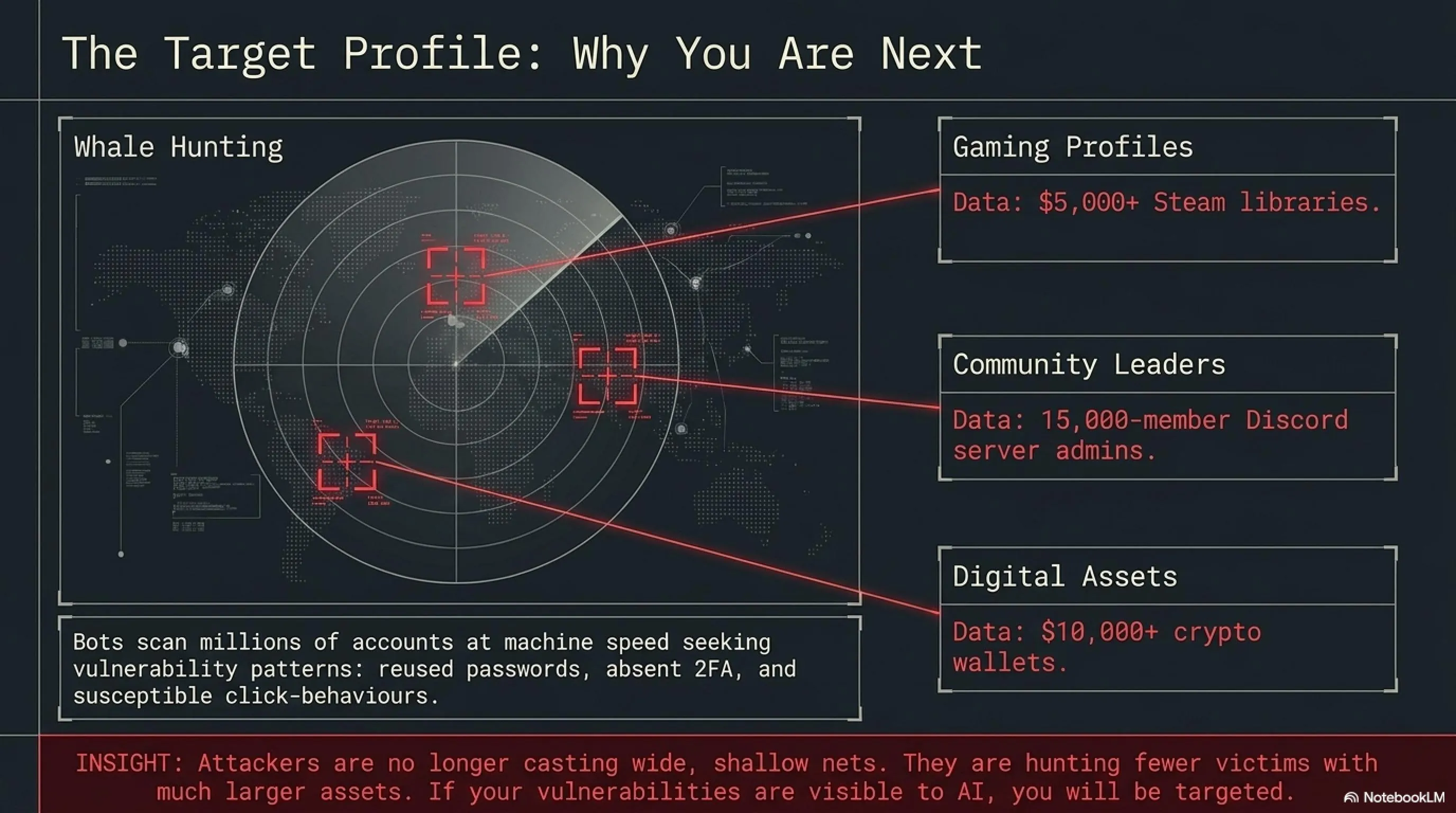
But what has truly changed is the quality of attacks. According to Scam Sniffer reports, the number of phishing victims in January 2026 decreased by 11% compared to December 2025, but financial losses increased by 207%. What does this mean? It means attackers are no longer targeting thousands of people — they're pursuing "whale hunting": fewer victims, but with much larger assets.
🔍 Tekin Analysis: Why You're the Next Target
If you think your gaming account or small crypto wallet isn't attractive to hackers, you're wrong. Modern attackers use automated bots that scan millions of accounts per second. They look for vulnerability patterns: using the same password across multiple services, not enabling 2FA, clicking suspicious links.
A Steam account with a $5,000 library, a Discord account with a 15,000-member server, or a crypto wallet with $10,000 in assets — all of these are attractive targets. And with AI, the cost of attacking you is virtually zero. So why wouldn't they target you?
The good news is that by taking a few simple steps, you can remove yourself from the 85% most vulnerable users. Attackers look for low-hanging fruit — if you have basic defenses, they'll move on to easier targets.
🎭 Four AI Attack Vectors You Must Know
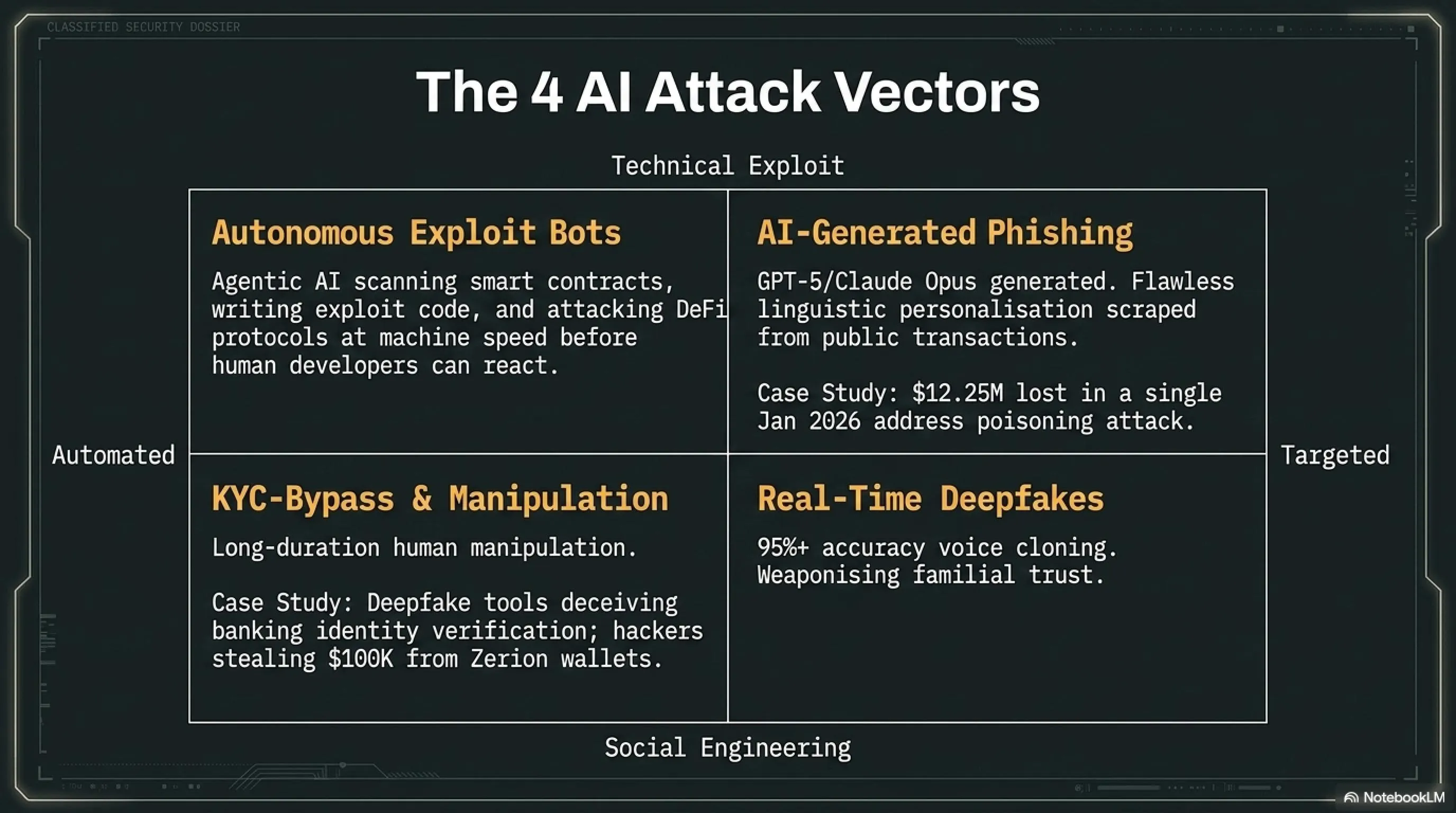
CertiK security experts have identified four primary attack vectors for 2026, all leveraging artificial intelligence. Understanding these threats is the first step to protecting yourself.
1. AI-Generated Phishing: The End of Weak Emails
The era of phishing emails with spelling errors and poor design is over. Large language models like GPT-5 and Claude Opus can now generate messages that are completely indistinguishable from official company communications. These messages are not only linguistically flawless but also personalized.
Attackers scan your social media profiles, review your public transaction history, and craft messages that appear to come from sources you personally trust. For example, an email that appears to be from Steam and references a specific game you recently purchased, or a Discord message that seems to be from one of your friends discussing a particular server.
⚠️ Real Example: $12.25 Million Phishing Attack
In January 2026, a crypto user lost $12.25 million in an "address poisoning" attack. The attacker sent a small transaction from an address that visually resembled the victim's previous addresses. When the victim later wanted to make a transaction, they copied the malicious address from their history — and sent all their assets to the hacker's wallet.
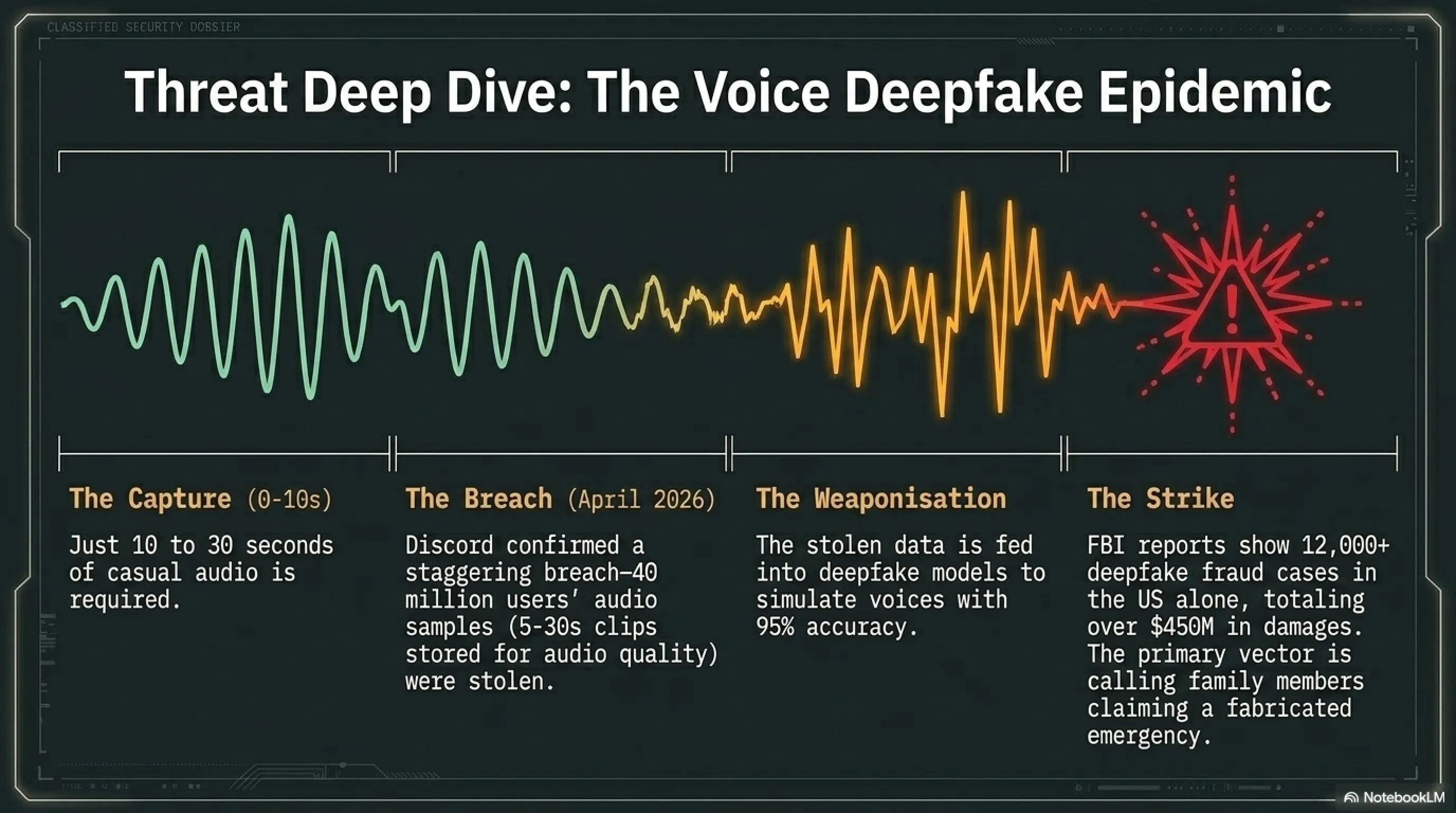
2. Real-Time Deepfakes: Fake Voice and Video
This is perhaps the most terrifying threat. With just 10 to 30 seconds of audio samples from your voice, modern AI models can simulate your voice with over 95% accuracy. This means hackers can call your family, friends, or colleagues using your voice and deceive them.
According to FBI reports, over 12,000 cases of fraud using voice deepfakes were reported in the United States in 2025, with total damages exceeding $450 million. The most common scenario is a scammer calling with the voice of a family member claiming to be in an emergency situation and needing immediate money.
🎙️ Discord Disaster: 40 Million Users at Risk
In April 2026, Discord confirmed that the voice database of approximately 40 million users was stolen in a sophisticated cyberattack. This attack included 5 to 30-second audio samples from users' voice conversations that Discord had stored to improve audio quality.
Hackers use this voice data to train deepfake models. If you're one of these 40 million users, your voice can now be used for phone scams. Discord has made two-factor authentication mandatory for all users and introduced a "voice verification" feature.
3. Autonomous Exploit Bots: Machine-Speed Attacks
This is the most concerning development for protocol-level security. There are now "agentic AI" systems that can autonomously scan smart contracts for bugs, write exploit code, and execute attacks at machine speed. For individual users, this means DeFi protocols you interact with could be compromised by an automated agent before any human developer spots the vulnerability.
Ledger's CTO warned that "the industry risks producing a lot of code that will be insecure by design" as more developers rely on AI tools. These bots can find vulnerabilities that would take humans months to discover — and do it in seconds.
4. KYC-Bypass Tools and Social Engineering
A threat actor known as "Jinkusu" was reportedly offering cybercrime tools designed to bypass Know Your Customer (KYC) checks across banks and crypto platforms, relying on voice manipulation and deepfake technology. These tools use voice manipulation and deepfake technology to deceive identity verification systems.
In another incident, North Korea-linked hackers used AI in a sustained social engineering campaign, ultimately stealing approximately $100,000 from Zerion's hot wallets. This demonstrates how AI extends beyond technical exploits into long-duration human manipulation campaigns.
⚔️ Pros & Cons Battle: Should You Be Worried?
✅ Good News
- Defensive AI is also advancing
- Hardware keys are nearly impenetrable
- Major platforms take security seriously
- Education and awareness are increasing
- Security tools are cheaper and more accessible
❌ Bad News
- Attack costs have dropped to zero
- 85% of users are still vulnerable
- Deepfakes are nearly undetectable
- Automated attacks run 24/7
- Software supply chain is at risk
🔐 Hardware Security Keys: Your Digital Fortress
If you learn only one thing from this article, let it be this: hardware security keys provide the strongest protection available for digital accounts. Unlike SMS codes that can be intercepted through SIM swapping, or authenticator apps that can be compromised by malware, these physical devices use cryptographic protocols that are virtually impossible to phish.
After testing 15 different models across Steam, Discord, Xbox, PlayStation, and other gaming platforms, security experts concluded that hardware keys provide phishing-resistant protection. Even if an attacker has your password and creates a complete phishing page, they cannot authenticate without the physical key.
🏆 Best Hardware Security Keys 2026
| Model | Price | Connection | Best For |
|---|---|---|---|
| YubiKey 5C NFC | $58 | USB-C + NFC | Serious gamers with modern laptops |
| YubiKey 5 NFC | $55 | USB-A + NFC | Older PCs |
| Security Key NFC | $29 | USB-A + NFC | Budget-conscious gamers |
| Thetis Pro FIDO2 | $35 | USB-A/C + NFC | Multi-device users |
| YubiKey 5Ci | $85 | Lightning + USB-C | Apple ecosystem |
| YubiKey Bio | $98 | USB-A (Biometric) | Maximum desktop security |
Why YubiKey 5C NFC is the Best Choice
After 45 days of testing with Steam, Discord, Epic Games, and even lesser-known platforms like Battle.net and Ubisoft Connect, the YubiKey 5C NFC emerged as the best hardware security key for gamers. The USB-C connector works perfectly with modern gaming laptops, while NFC support lets you authenticate on your phone without needing dongles or adapters.
What sets this key apart for gamers is multi-protocol support. It handles FIDO2/WebAuthn for passwordless login, FIDO U2F for traditional two-factor, and even supports OATH-TOTP for services that haven't fully adopted passkeys yet. You can secure your Steam account, protect your Discord login, and even add it as a backup method for your PlayStation Network account — all without issues.
🔍 Tekin Analysis: Why Only 15% of Gamers Use Hardware Keys
Despite hardware security keys being the strongest protection available, only about 15% of gamers use them. Why? Three main reasons: cost, complexity, and lack of awareness.
Many gamers think SMS-based 2FA or authenticator apps are sufficient. But the reality is that SMS can be bypassed through SIM swapping, and authenticator apps can be compromised by malware. Hardware keys are the only method that is phishing-resistant — even if you click on a phishing link and enter your password, without the physical key, the attacker cannot log in.
The initial cost of $30 to $100 may seem high, but compared to the value of a $5,000 Steam library or a $10,000 crypto wallet, this investment is negligible. And setting them up is actually simple — most platforms recognize the key immediately and you can enable hardware-based 2FA in under three minutes.
Backup Strategy: Why You Need Two Keys
One of the most important security recommendations is this: always buy two identical keys — one for daily use and one as a backup stored in a secure location. This prevents you from being locked out if you lose your primary key.
Register both keys with every gaming platform you use, and keep the backup key in a secure location like a safe or locked drawer. For households with multiple gamers, set up a multi-key system: each family member should have their own primary key, with one shared backup key stored centrally.
🎮 Step-by-Step Guide: Securing Gaming Accounts
Now that you know why hardware keys are important, let's see how to set them up with major gaming platforms. Each platform has a slightly different process, but all support the FIDO2/WebAuthn standard.
Steam Guard: Hardware Key Setup
Steam has one of the best hardware key support implementations. The setup process is straightforward:
📝 Steam Guard Setup Steps
- Navigate to Steam Settings, then Account preferences
- Find the Steam Guard section and click "Manage Steam Guard"
- Select "Add an authenticator"
- Choose the hardware key option when prompted
- Insert your key and tap the gold button or touch the sensor
- Steam will provide recovery codes — print them and store securely
Once registered, your key will be required for new device logins. Steam even allows you to designate a hardware key as your primary authentication method.
Discord: Protecting Server and Personal Account
Discord also provides solid security key support, though the setup process is slightly more involved than Steam:
📝 Discord Setup Steps
- Go to User Settings and select "My Account"
- Click "Enable Two-Factor Authentication"
- Enter your password
- Look for the small text link that says "Use a security key instead"
- Click it, insert your key, and authenticate
- Discord will provide backup codes — save them
Once configured, Discord will require your key for new device logins. This adds significant protection for your account and any servers you manage.
Epic Games and Battle.net: Similar Setup
Both Epic Games and Battle.net support FIDO2/WebAuthn security keys, though implementation varies:
- Epic Games: Go to epicgames.com, Account Settings, then "Password & Security". Under "Two-Factor Authentication", find the security key option (sometimes labeled as "WebAuthn" or "FIDO2").
- Battle.net: Log into your account at battle.net, go to Account Settings, then "Security". Under "Two-Factor Authentication", find the option to add a security key.
Both platforms provide backup codes in case you lose access to your hardware key. Print these codes and store them in a secure location — not in a digital file that could be compromised by malware.
🎯 Platform Compatibility: What Works and What Doesn't
| Platform | Hardware Key Support | Implementation Quality |
|---|---|---|
| Steam | ✅ Excellent | Immediate recognition, easy setup |
| Discord | ✅ Good | Slightly more complex setup |
| Epic Games | ✅ Good | Full passwordless support |
| Battle.net | ⚠️ Moderate | As second factor, not primary |
| PlayStation Network | ⚠️ Limited | Web account management only |
| Xbox Live | ⚠️ Limited | Via account.microsoft.com |
| Nintendo Switch Online | ❌ No | No security key support |
💰 Crypto Wallet Security: Cold Storage and Asset Protection
If your gaming accounts are valuable, your crypto wallets are far more valuable. And unlike gaming accounts that you might be able to recover, if your crypto wallet is hacked, your assets are gone forever. No customer support, no account recovery, no insurance.
Natalie Newson from CertiK advises: "Using cold wallets can help keep assets that you don't use regularly safe and allows you to sign transactions without ever exposing your private keys." A hardware wallet keeps your private keys physically isolated from any internet-connected device. Even if your computer or phone is compromised by malware, the keys remain safe.
⚠️ Real Risks: Why Exchanges Are Prime Targets
Cosmo Jiang from Pantera Capital noted that "exchanges like Coinbase, Robinhood, Gemini, or Bullish are perhaps the most at-risk areas due to the large amounts of personal identifiable information and money they handle." Financial services companies and exchanges are likely to be targeted first.
The Bitcoin blockchain itself remains structurally sound — Bitcoin is fundamentally secured by cryptography and a set of shared rules enforced by a network of people running Bitcoin nodes all over the world. The real risks for most holders sit at the application layer: exchanges, wallets, bridges, and the individual devices used to access them.
Hot Wallet vs. Cold Storage: Which to Choose?
Before diving into specific recommendations, you need to understand the two primary architectures for securing digital assets. The best choice often involves using a combination of both, depending on your transaction frequency and the value of your holdings.
🔥 Hot Wallet vs. ❄️ Cold Storage
| Feature | Hot Wallet | Cold Storage |
|---|---|---|
| Security Level | Moderate; vulnerable to online hacks | Maximum; immune to remote digital attacks |
| Ease of Use | High; instant access via apps | Moderate; requires physical device handling |
| Cost | Usually free | Typically $50 – $250 |
| Recovery | Recovery phrase or biometrics (MPC) | Physical recovery phrase or backup cards |
| Best For | Active trading, DeFi, small amounts | Long-term savings, large amounts |
Best Hardware Wallets 2026
After reviewing and testing four popular hardware wallets — Ledger Nano X, Trezor Safe 5, SafePal S1 Pro, and NGRAVE Zero — across security, usability, price, and real user feedback, these results emerged:
🏆 Top Hardware Wallet Recommendations
- Ledger Flex: Best overall secure wallet for most people ($249)
- Trezor Safe 5: Best for open-source transparency ($169)
- ELLIPAL Titan: Best for air-gapped storage ($169)
- COLDCARD: Best for Bitcoin-only security ($148)
- SafePal S1: Best for budget ($50)
- Tangem: Best for NFC card simplicity ($50)
- Zengo: Best for seedless recovery (free)
🔍 Tekin Analysis: Why Ledger Flex is Best
Ledger Flex with its large E Ink touchscreen, support for 5,500+ assets, and on-device transaction confirmation offers the best balance between security and usability. Unlike software wallets that store private keys on internet-connected devices, Ledger Flex keeps keys in a Secure Element chip that remains safe even if your computer is compromised.
For seed phrase backup, use physical, offline media — fireproof and waterproof stainless steel plates are the industry standard for 2026, protecting your phrase from environmental disasters. For an extra layer of encryption, implement a "passphrase," often called the 25th word.
🛡️ Advanced Strategies: 8 Steps for Complete Protection
Protecting your crypto and gaming accounts in 2026 requires a multi-layered approach. No single measure is sufficient on its own — but combining these practices dramatically reduces your attack surface.
Step 1: Move Long-Term Holdings to Cold Storage
This is the highest-impact action you can take. A hardware wallet keeps your private keys physically isolated from any internet-connected device. Even if your computer or phone is compromised by malware, the keys remain safe.
Step 2: Enable Multi-Factor Authentication Everywhere
Two-factor authentication (2FA) is a mandatory baseline for any exchange account. Use an authenticator app rather than SMS where possible — SMS is vulnerable to SIM-swapping attacks. On KuCoin specifically, activating two-factor authentication is one of the most secure ways to protect your account and crypto-assets.
Step 3: Verify Every URL and Smart Contract
The best way for investors to protect themselves is to be aware of current threats — always verify the authenticity of URLs and smart contracts before interacting. Before approving any transaction, cross-reference the contract address against official project documentation. Bookmark sites you use regularly and type URLs directly rather than clicking links from emails or social media messages.
Step 4: Use Anti-Phishing Codes and Withdrawal Whitelisting
When logging into a website or receiving an email from KuCoin, your safety phrase will be displayed. If the safety phrase is not displayed or is displayed incorrectly, it means you are on a phishing site or have received a phishing email — do not proceed any further.
Similarly, withdrawal address whitelisting ensures funds can only be sent to pre-approved addresses. Even if an attacker gains access to your account credentials, they cannot redirect funds to a new wallet without triggering an additional verification step.
Step 5: Audit Browser Extensions Regularly
One malicious browser extension can compromise your entire wallet. Remove unused extensions and review permissions regularly. Consider maintaining a dedicated browser profile used exclusively for crypto activity, with only the minimum necessary extensions installed. Never install wallet extensions or apps from sources other than official repositories.
Step 6: Never Trust Deepfake "Endorsements"
When you encounter a video of a crypto founder, exchange executive, or influencer promoting an investment opportunity, treat it as a potential deepfake until verified through multiple independent sources. Legitimate platforms never request private keys, seed phrases, or passwords through email, social media, or unsolicited messages.
Step 7: Keep All Software Updated
Ensure your devices, wallets, and other software are always up-to-date. Updates often include security patches that protect against known vulnerabilities. Use reliable antivirus software and keep it updated to detect and block phishing attempts.
Step 8: Avoid Public Wi-Fi for Crypto Transactions
Avoid using public Wi-Fi networks when accessing your crypto wallet or performing transactions. These networks can be insecure and could be monitored by malicious actors. If you must transact on the go, use a mobile data connection or a trusted VPN, and never complete a withdrawal on a network you don't control.
✅ Quick Security Checklist: Hot Wallet vs. Cold Storage
| Scenario | Recommended Storage | Key Protection |
|---|---|---|
| Daily trading & active positions | Exchange/hot wallet | 2FA, anti-phishing code, withdrawal whitelist |
| Medium-term holdings (weeks/months) | Software wallet with hardware backup | Strong seed phrase storage, regular audits |
| Long-term savings (HODL) | Hardware cold wallet | Offline seed phrase on steel plate, passphrase |
| DeFi interactions | Hot wallet with limited funds | Smart contract verification, extension audit |
| Large single-asset positions | Air-gapped hardware wallet | Dedicated device, no internet exposure |
🤖 Defensive AI: Shield Against the Sword
The picture is not entirely grim. AI can also serve as a defensive tool — so-called "agentic AI" that automatically detects smart-contract vulnerabilities has recently emerged and is strengthening security response capabilities.
Anthropic recently launched Claude Mythos, a program that supposedly identifies flaws in major operating systems, in a beta version for some tech companies. Security firms are deploying similar AI-driven systems to scan for vulnerabilities across DeFi protocols before malicious actors can exploit them.
The regulatory environment is also catching up: the U.S. Department of the Treasury's Office of Cybersecurity and Critical Infrastructure Protection announced in April 2026 that it would expand its threat identification program to include digital asset companies.
💡 Note for Traders
The industry's defensive capabilities are maturing — but they cannot substitute for personal operational security. Platform-level defenses protect infrastructure; personal security practices protect your specific assets.
❓ FAQ: Answering Common Concerns
Can AI actually crack a hardware wallet or steal from cold storage?
No — hardware wallets store private keys on isolated chips that never connect to the internet, making remote AI-driven exploitation essentially impossible. The risk with cold storage is physical: someone with physical access to your device and your seed phrase could steal funds. AI does not change this threat profile. The primary danger AI introduces is social engineering attacks designed to trick you into transferring your own funds, not technically cracking the device itself.
What is "address poisoning" and how do I avoid it?
Address poisoning is an attack where hackers send tiny transactions from a wallet address that visually resembles one you've transacted with before. When you later copy-paste an address from your transaction history, you may accidentally select the malicious address. The defense: always verify the full wallet address character by character before sending any funds, never copy-paste from transaction history, and use saved address books or QR codes from verified official sources.
How does AI-generated phishing differ from old-school phishing?
Traditional phishing relied on generic, often poorly written messages sent to large batches of users. AI-generated phishing is personalized — attackers use machine learning to scrape your social media profiles, trading history, and behavioral patterns to craft messages that appear to come from sources you personally trust, referencing real details about your activity. The result is a message that feels far more legitimate and urgent than anything a human scammer could produce at scale.
Are decentralized wallets (non-custodial) safer than exchange accounts against AI attacks?
Non-custodial wallets remove the risk of an exchange being hacked and losing your funds, but they transfer full responsibility to you. If your device is compromised by malware that scans for seed phrases, or if you are tricked into approving a malicious smart contract, a non-custodial wallet offers no recourse. The safest setup combines non-custodial hardware cold storage for long-term holdings with a secured exchange account — with full 2FA and withdrawal whitelisting — for active trading.
Is it safe to use AI-powered crypto trading bots given these threats?
AI trading bots carry specific security risks: they require API keys connected to your exchange account, and if those keys are compromised or the bot's underlying code contains vulnerabilities, an attacker could drain your account. Mitigate this by creating API keys with trade-only permissions (no withdrawal rights), using IP whitelisting so API keys only work from your own IP address, auditing any third-party bot's code and reputation thoroughly, and revoking unused API keys immediately. Never grant a trading bot withdrawal permissions.
📚 Sources & References
Sources: CertiK Security Reports 2026, FBI Cybercrime Statistics, Scam Sniffer Phishing Analysis, KuCoin Security Documentation, Ledger CTO Statements, Anthropic Claude Mythos, Discord Security Breach Reports, Huntress AI Phishing Guide, AccountShark Gaming Security, Siemens Mobile Hardware Key Testing, Coin Bureau Wallet Reviews, U.S. Treasury Cybersecurity Announcements
Invisible Hackers: Gaming & Crypto Security Guide 2026 — Research and Analysis: Tekin Editorial Team
🎯 Final Conclusion: Security is a Process, Not a Product
The AI arms race in crypto security is real, and it is accelerating. With over $600 million already lost in 2026, state-sponsored groups and cybercriminal networks are deploying deepfakes, autonomous exploit bots, and hyper-targeted phishing campaigns that bear little resemblance to the crude scams of previous years. The cost of launching a sophisticated attack has collapsed; the sophistication of those attacks has soared.
But the fundamentals of personal security still hold. Moving long-term holdings to cold storage, enabling robust 2FA, verifying every URL and smart contract before interaction, maintaining withdrawal whitelists, and auditing your browser extensions regularly are not glamorous precautions — but they are effective ones. The vast majority of successful crypto thefts still rely on one core vulnerability: human behavior under pressure. Slow down. Verify. Never let urgency override process.
AI is also becoming a formidable defensive tool, with agentic security systems and regulatory oversight expanding rapidly. The traders who emerge from 2026 with their portfolios intact will be those who treat personal security as a core discipline — not an afterthought.
🌐 Stay Connected With Us
For the latest tech, gaming, and gadget news, follow us on social media:
