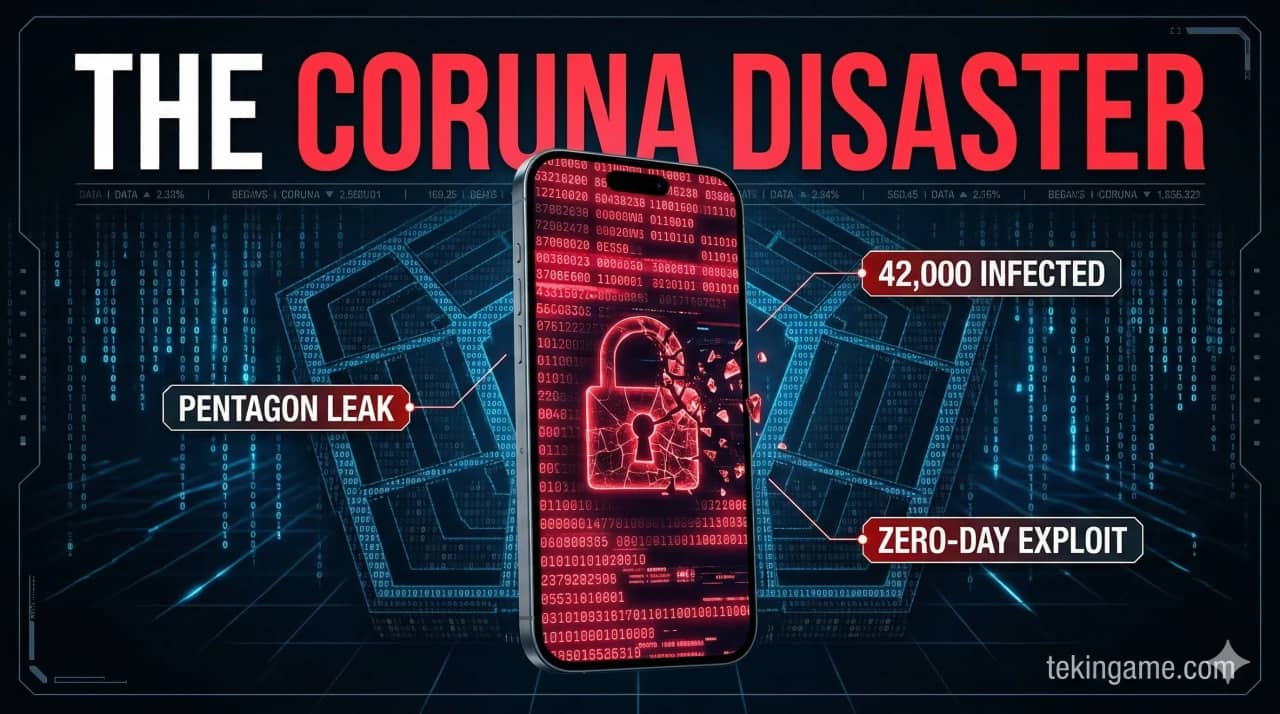
When a US government hacking tool with 23 iPhone vulnerabilities falls into the hands of Russian spies and Chinese hackers, the result is a catastrophe called Coruna. 42,000 iPhones worldwide have been compromised, personal data of millions stolen, and for the first time in history, an American military tool has been used against its own citizens.
March 5, 2026 was the day the cybersecurity world changed forever. Google Threat Intelligence published a report that exploded like a bomb in the tech industry: an advanced hacking toolkit called "Coruna," originally built for the US military, is now in the hands of Russian and Chinese cybercriminals and has infected 42,000 iPhones worldwide.
But this isn't just another cyberattack. Coruna tells a dark story of how defensive tools become offensive weapons — a story that shows how governments, by hoarding vulnerabilities instead of disclosing them, put all of our security at risk.
What is Coruna and How Does It Work?
[IMAGE_PLACEHOLDER_2]Coruna is an advanced "exploit kit" containing 23 zero-day vulnerabilities in the iOS operating system. This toolkit, originally built by a US defense contractor for military forces, has the capability to penetrate various iPhones running iOS 13 through 17.2.
What makes Coruna truly dangerous is the diversity of its attack methods. This tool has 5 different ways to infect iPhones:
- Malicious Websites: Just by visiting an infected link
- Phishing SMS: Clicking suspicious links in text messages
- Fake Emails: Opening infected email attachments
- Fake Applications: Installing infected apps from the App Store
- Physical Access: USB connections and direct attacks
⚠️ Security Alert
If your iPhone doesn't have iOS 17.3 or higher, update immediately. Also install the iVerify app to check if your device has been compromised.
The Leak Path: From Pentagon to Criminals
[IMAGE_PLACEHOLDER_3]The Coruna story reads like a spy thriller, but it's unfortunately completely real. This tool has traveled a complex path from its American creators to criminals:
Stage One: Development in America (2024)
In 2024, a US defense contractor (whose name has not yet been disclosed) developed Coruna for use by American military and intelligence forces. The primary goal was to penetrate suspicious devices and gather intelligence from foreign targets.
Stage Two: Leak to Russia (Late 2025)
In late 2025, somehow not yet fully clear, Coruna fell into the hands of Russian intelligence services. Likely through an insider at the contractor company or a cyberattack on their servers.
Stage Three: Sale to Chinese (January 2026)
In January 2026, Chinese cybercriminal groups purchased Coruna from the Russians and began using it extensively. This was when the attack transformed from a limited intelligence operation into a global security catastrophe.
The Victims: 42,000 Stories of Privacy Violation
[IMAGE_PLACEHOLDER_4]Official Google Threat Intelligence statistics show that 42,000 iPhones worldwide have been infected by Coruna. But behind every number is a real person with a life and personal secrets.
Interestingly, the most victims are in the United States itself — the country that built this tool. This shows how military tools can be used against the citizens of the same country.
What Data Was Stolen?
Coruna is a complete espionage tool with the capability to access all parts of an iPhone:
- Messages and Calls: All SMS, iMessage, and call history
- Photos and Videos: Complete access to gallery and personal files
- Location Data: Continuous tracking of user location
- Contacts: Complete list of numbers and contact information
- Applications: Internal app data including passwords
- Microphone and Camera: Secret recording of audio and video
Apple's Response: Too Little, Too Late?
[IMAGE_PLACEHOLDER_5]When Google published the Coruna report on March 5, Apple initially tried to downplay the importance of the issue. But public and media pressure was so intense that they were forced to act quickly.
iOS 17.3: Emergency Update
On March 9, 2026, Apple released iOS 17.3 with unprecedented speed, patching all 23 Coruna vulnerabilities. This was the fastest security update in iOS history — just 4 days after the public threat announcement.
Tim Cook's Statement
Tim Cook said in an official statement: "The security of our users is our top priority. iOS 17.3 addresses all known Coruna vulnerabilities and we are working with law enforcement on attribution."
But critics argue that Apple should have discovered these vulnerabilities earlier. How is it possible that 23 security holes remained undetected for months?
📊 Summary: Apple's Response
iOS 17.3 released in 4 days, 23 vulnerabilities patched, but many questions remain about why these issues weren't discovered earlier.
Google's Discovery: The Digital Detectives
[IMAGE_PLACEHOLDER_6]If it weren't for Google Threat Intelligence, we probably still wouldn't know about Coruna's existence. This team, composed of the world's best cybersecurity researchers, how did they manage to discover this complex threat?
The Discovery Process
It all started with a suspicious pattern in network traffic. Google researchers noticed that a large number of iPhones in different regions of the world were showing unusual behavior — sending encrypted data to unknown servers at specific times.
After months of research and analysis, they were able to discover the entire attack chain and trace its origin to Coruna. Collaboration with iVerify — a mobile security company — helped reveal more technical details.
Collaboration with iVerify
iVerify, which provides an app for detecting iPhone intrusions, played a key role in discovering Coruna. They were able to identify the digital signature of this malware and provide a tool for detecting infection.
The Dual-Use Problem: When Defense Becomes Attack
[IMAGE_PLACEHOLDER_7]The Coruna catastrophe is a perfect example of the "dual-use technology" problem — technologies that can be used for both defensive and offensive purposes. This issue is a hot debate in the cybersecurity world.
Vulnerability Stockpiling
Governments, especially the US, have been stockpiling software vulnerabilities for years instead of disclosing and fixing them, to use in espionage operations. But Coruna showed how dangerous this strategy is.
When governments keep security holes secret, they not only put their own citizens at risk, but also increase the likelihood of these tools leaking to bad actors.
NSA's Role
The US National Security Agency (NSA) has been criticized for years for stockpiling vulnerabilities. The WannaCry attack in 2017, which used an NSA tool called EternalBlue, was a previous example of this same problem. Now Coruna shows that this issue hasn't been resolved.
📊 Summary: Dual-Use Problem
Government vulnerability stockpiling, military tool leaks to criminals, and lack of transparency in cyber tool development.
Technical Analysis: How Coruna Works
[IMAGE_PLACEHOLDER_8]To fully understand the Coruna threat, we need to look at its technical details. This toolkit includes several complex stages, each designed to overcome one of iOS's security layers.
Exploit Chain
Coruna uses a complex "exploit chain" that includes these stages:
- Initial Penetration: Using WebKit vulnerability to execute code
- Sandbox Escape: Overcoming Safari security restrictions
- Privilege Escalation: Gaining higher system access
- Kernel Exploit: Penetrating the operating system kernel
- Persistence: Remaining in the system even after restart
Persistence Mechanisms
One of Coruna's most dangerous features is its ability to persist in the system. This malware uses 3 different methods to ensure its survival:
- LaunchDaemon Hijacking: Abusing system services
- Configuration Profile: Installing fake management profiles
- Kernel Extension: Installing system kernel modules
Broader Impact: Trust in Digital Security

The Coruna catastrophe goes beyond a simple cyberattack. This incident has severely shaken public trust in digital security and raised serious questions about governments' role in cybersecurity.
Consumer Trust
One of Coruna's biggest damages is the blow to user trust in iPhone security. For years Apple advertised with the slogan "Privacy. That's iPhone," but now users are asking: if 23 vulnerabilities remained hidden for months, what guarantee is there that other problems don't exist?
Government Accountability
The US Congress has announced that extensive investigations into how Coruna leaked will begin. The main questions are:
- Why was this tool built in the first place?
- What controls existed to prevent leaks?
- Are other similar tools also at risk of leaking?
- What measures will be taken to compensate victims?
Protection and Prevention: What Users Can Do
[IMAGE_PLACEHOLDER_10]Although Coruna is a serious threat, users can take effective measures to protect themselves. The most important thing is not to panic, but to act intelligently.

Immediate Actions
✅ Immediate Security Checklist
- Immediately update to iOS 17.3 (or newer)
- Install the iVerify app and perform a complete scan
- Review app permissions and revoke unnecessary ones
- Enable Advanced Data Protection in iCloud
- Use strong, unique passwords with 2FA
Long-term Security
For long-term protection, follow these principles:
- Regular Updates: Always install the latest iOS version
- Careful Clicking: Avoid suspicious links and files
- App Store Only: Never install apps from unofficial sources
- Use VPN: For sensitive communications
- Regular Backups: And verify their integrity
Detecting Infection
If you think your iPhone might be infected, check for these signs:
- Sudden decrease in battery life
- Unusual device heating
- Excessive data usage
- Strange app behavior
- Messages or calls you didn't send
Conclusion: Lessons from the Coruna Catastrophe
The Coruna catastrophe showed that in the digital age, the line between defense and attack, between security and surveillance, and between protection and threat is very thin. When governments build powerful cyber tools, there's always the risk that these tools will fall into the wrong hands.
The 42,000 Coruna victims are a bitter reminder that cybersecurity is a shared responsibility for all of us — from tech companies to governments to users themselves. Apple should have better detection systems, governments should act more transparently, and we should use technology more intelligently.
But most importantly, Coruna showed that real security is only achieved when all players — from technology makers to end users — take their responsibility for protecting privacy and digital security seriously. The future of cybersecurity depends on cooperation and transparency, not secret stockpiling of dangerous tools.
Final Note: This article is based on official reports from Google Threat Intelligence, iVerify, and Apple statements. Information is current as of March 10, 2026. For the latest security information, visit Apple's official website.
🌐 Stay Connected With Us 🎮✨
For the latest tech, gaming, and gadget news, follow us on our official social media channels: