☕ Good Morning Tekin Legion - April 21, 2026
Good morning everyone! Today, April 21, 2026, we're kicking off with 6 explosive tech stories. From Tesla launching fully driverless Robotaxis to Mexico's massive government hack using AI, critical vulnerabilities in Adobe and SGLang, Zerion crypto wallet breach, and Nintendo Switch 2's final specs - everything you need to start your day informed and confident.
⚡ Today's Headlines:
🚗 Tesla launches unsupervised Robotaxi in Dallas & Houston
🇲🇽 Hundreds of millions of Mexico government records hacked with Claude Code & GPT-4.1
📄 Adobe Acrobat Reader Zero-Day with 8.6 score actively exploited
💰 Zerion Crypto Wallet hacked - $100K stolen
🐛 SGLang critical vulnerability with 9.8 score discovered
🎮 Nintendo Switch 2 final specs: 12GB RAM and 4K
☕ Grab your coffee and get ready for a comprehensive tech news journey!
1. Tesla Robotaxi: The New Era of Driverless Transportation in Dallas & Houston 🚗🤖
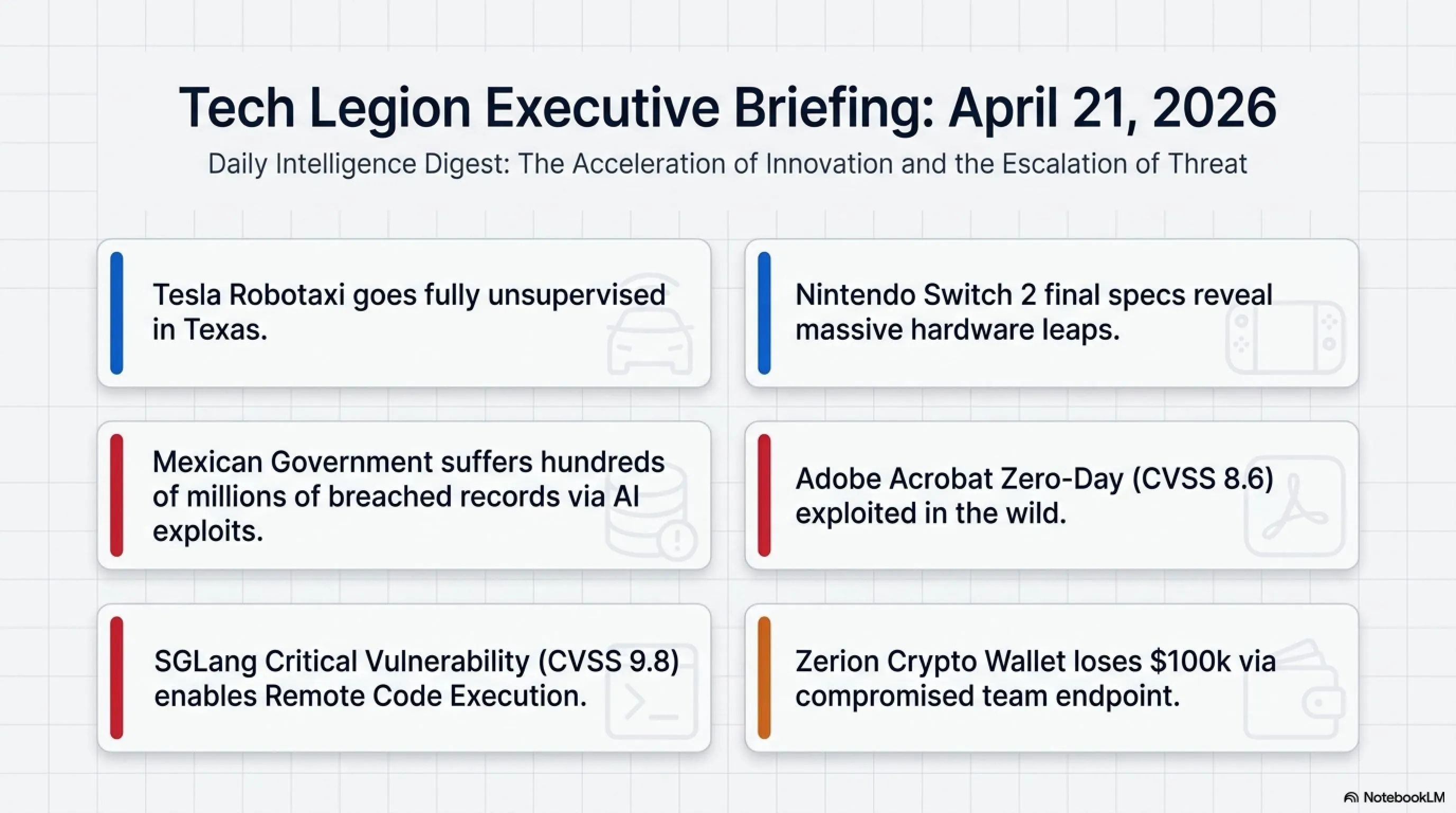
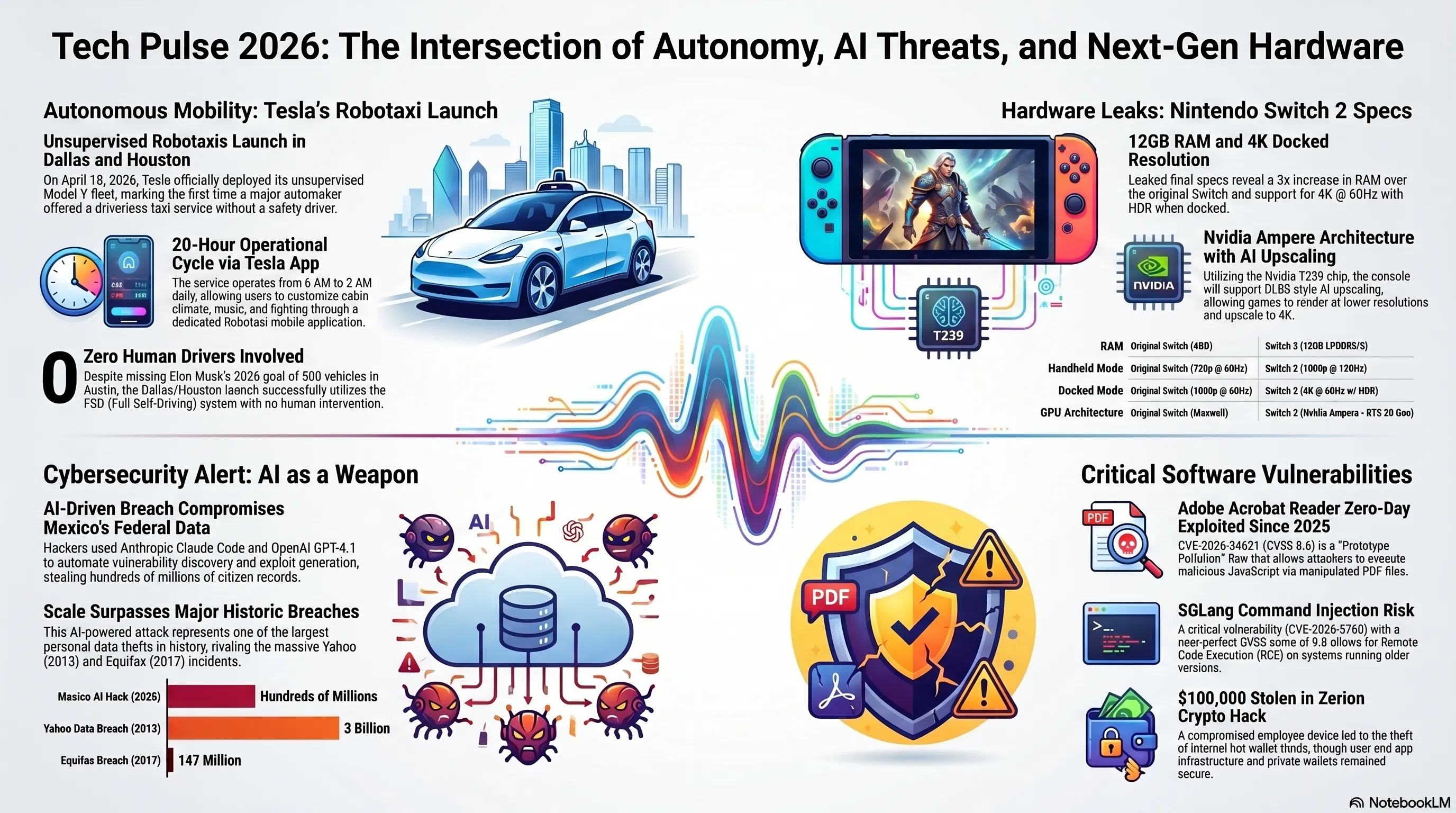
Tesla made history on April 18, 2026, by launching its fully unsupervised Robotaxi service in Dallas and Houston. This marks the first time a major automaker has offered a completely driverless taxi service without a safety driver for the general public. The service represents a watershed moment in the autonomous vehicle industry that has been years in the making.
🔍 Tesla Robotaxi Technical Details
- Vehicle: Tesla Model Y equipped with FSD (Full Self-Driving) system
- Operating Hours: 6 AM to 2 AM (20 hours per day)
- Booking Method: Via dedicated Tesla Robotaxi app
- Cabin Experience: Personalized with temperature, music, and lighting control
- Expansion: Second Model Y added to fleet on April 20
After months of testing in Austin, Texas, the service has now expanded to two major cities. Users can order a fully autonomous Model Y through a dedicated app that will pick them up and deliver them to their destination without any human driver. This technology, which has been in development for years, has finally become a reality.
📊 Key Statistics
Elon Musk had promised in 2025 that by year's end, Tesla would have 500 vehicles in Austin and coverage for half of America's population, but neither goal materialized. However, the launch of unsupervised service in Dallas and Houston demonstrates that Tesla has finally achieved the necessary technology. This is a major step for the autonomous vehicle industry that could transform the future of urban transportation.
⚖️ Robotaxi Security: Pros & Cons
✅ Advantages
- Reduced accidents from human error
- 24/7 availability without driver breaks
- Lower transportation costs for passengers
- Reduced pollution through route optimization
- Increased accessibility for disabled individuals
⚠️ Risks & Concerns
- Vulnerability to cyberattacks
- Potential for remote hacking and control
- System failures in adverse weather
- Privacy concerns and passenger tracking
- Legal liability in case of accidents
2. Massive Mexico Government Hack with AI: Hundreds of Millions of Records Stolen 🇲🇽💥
In one of the largest security breaches in history, hackers used advanced AI tools to infiltrate Mexican government systems and steal hundreds of millions of citizen records. This attack, discovered by cybersecurity firm Gambit Security, demonstrates how artificial intelligence can become a double-edged sword.
⚠️ AI Tools Used in the Attack
- Anthropic Claude Code: For analyzing and writing exploit code
- OpenAI GPT-4.1: For identifying vulnerabilities and automating attacks
- Target: Federal and state government organizations in Mexico
- Stolen Data: Personal information of millions of citizens
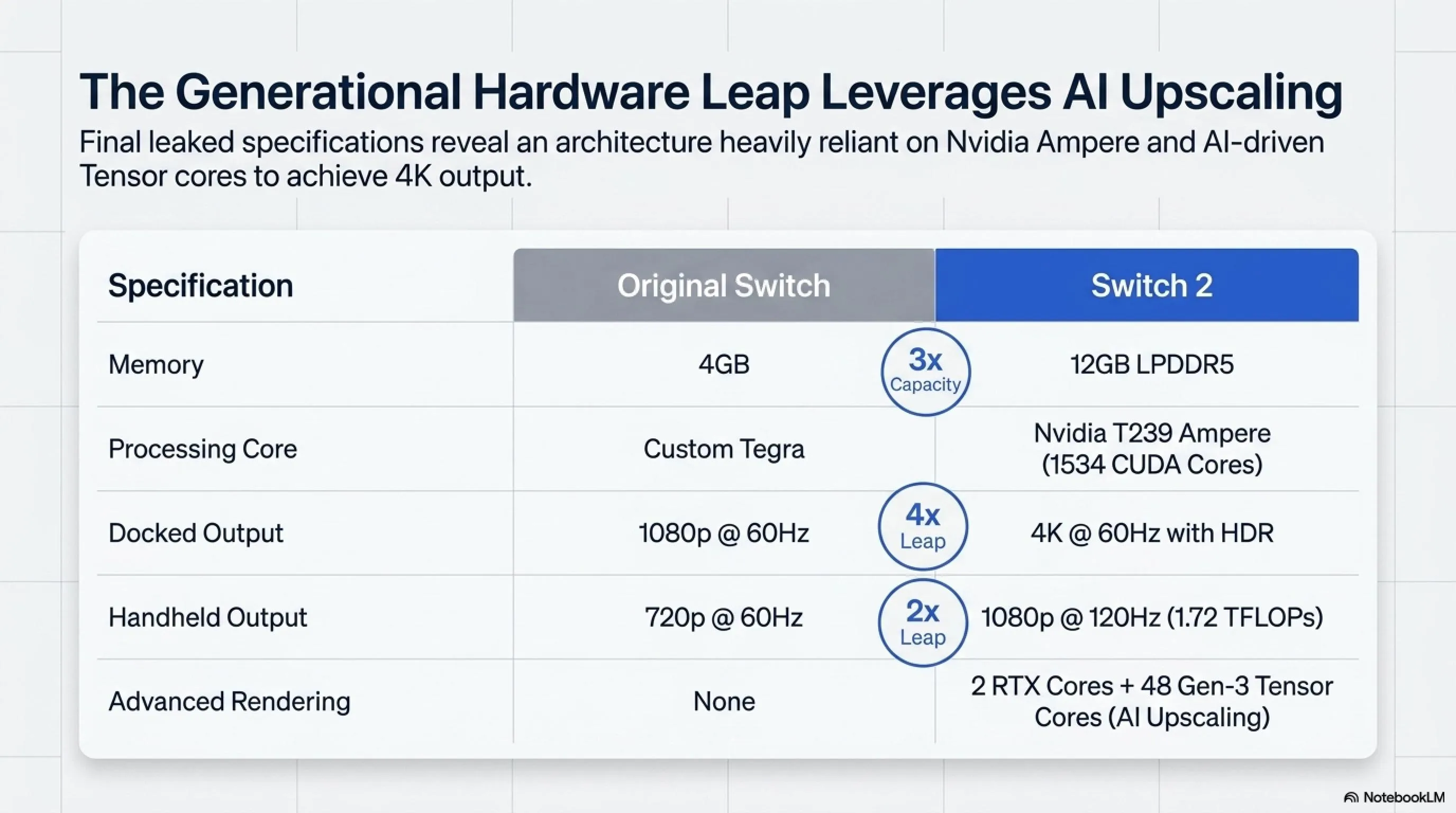
According to Gambit Security's report, a small group of individuals used Claude Code and GPT-4.1 to penetrate federal and state government organizations. These AI tools helped hackers identify vulnerabilities faster, write exploit code, and automate attacks. This type of attack demonstrates that artificial intelligence can dramatically increase the power of cyberattacks.
📈 Comparison with Previous Attacks
| Attack | Records | Year |
|---|---|---|
| Mexico AI Hack | Hundreds of millions | 2026 |
| Yahoo Data Breach | 3 billion | 2013 |
| Equifax Breach | 147 million | 2017 |
This attack is a serious warning for governments and organizations worldwide. With the advancement of AI tools, hackers can execute more sophisticated attacks at greater speed. This makes increased investment in cybersecurity and the development of AI-based defense systems more critical than ever.
3. Adobe Acrobat Reader Zero-Day: 8.6 Vulnerability Being Actively Exploited 📄⚠️
Adobe released an emergency patch in April 2026 to fix a critical vulnerability in Acrobat Reader that has been actively exploited since December 2025. This vulnerability, registered as CVE-2026-34621 with a CVSS score of 8.6 out of 10, allows attackers to execute malicious code through manipulated PDF files.
🔴 CVE-2026-34621 Vulnerability Details
- Vulnerability Type: Prototype Pollution
- CVSS Score: 8.6 out of 10 (Critical)
- Discovery Date: December 2025
- Patch Date: April 2026
- Attack Method: Opening manipulated PDF file
- Result: Execution of malicious JavaScript code
Security researcher Haifei Li from EXPMON disclosed the details of this vulnerability and demonstrated how attackers can execute malicious JavaScript code in Adobe Reader by creating specific PDF files. Evidence shows this vulnerability has been used in real attacks since December 2025, making it a serious threat.
⚡ Attack Timeline
| Date | Event |
|---|---|
| December 2025 | Exploitation begins |
| Early April 2026 | Details disclosed by Haifei Li |
| April 2026 | Adobe emergency patch released |
Adobe Acrobat Reader users should immediately update to the latest version. This vulnerability demonstrates that even widely-used software like Adobe Reader can be targeted by sophisticated attacks. It's recommended to avoid opening PDF files from unknown sources and always keep your software up to date.
4. Zerion Crypto Wallet Hacked: $100K Stolen from Hot Wallets 💰🔓
Crypto wallet service Zerion announced in April 2026 that a team member's device was compromised, resulting in approximately $100,000 stolen from the company's internal hot wallets. Fortunately, user wallets, Zerion applications, and core infrastructure were not affected by this attack.
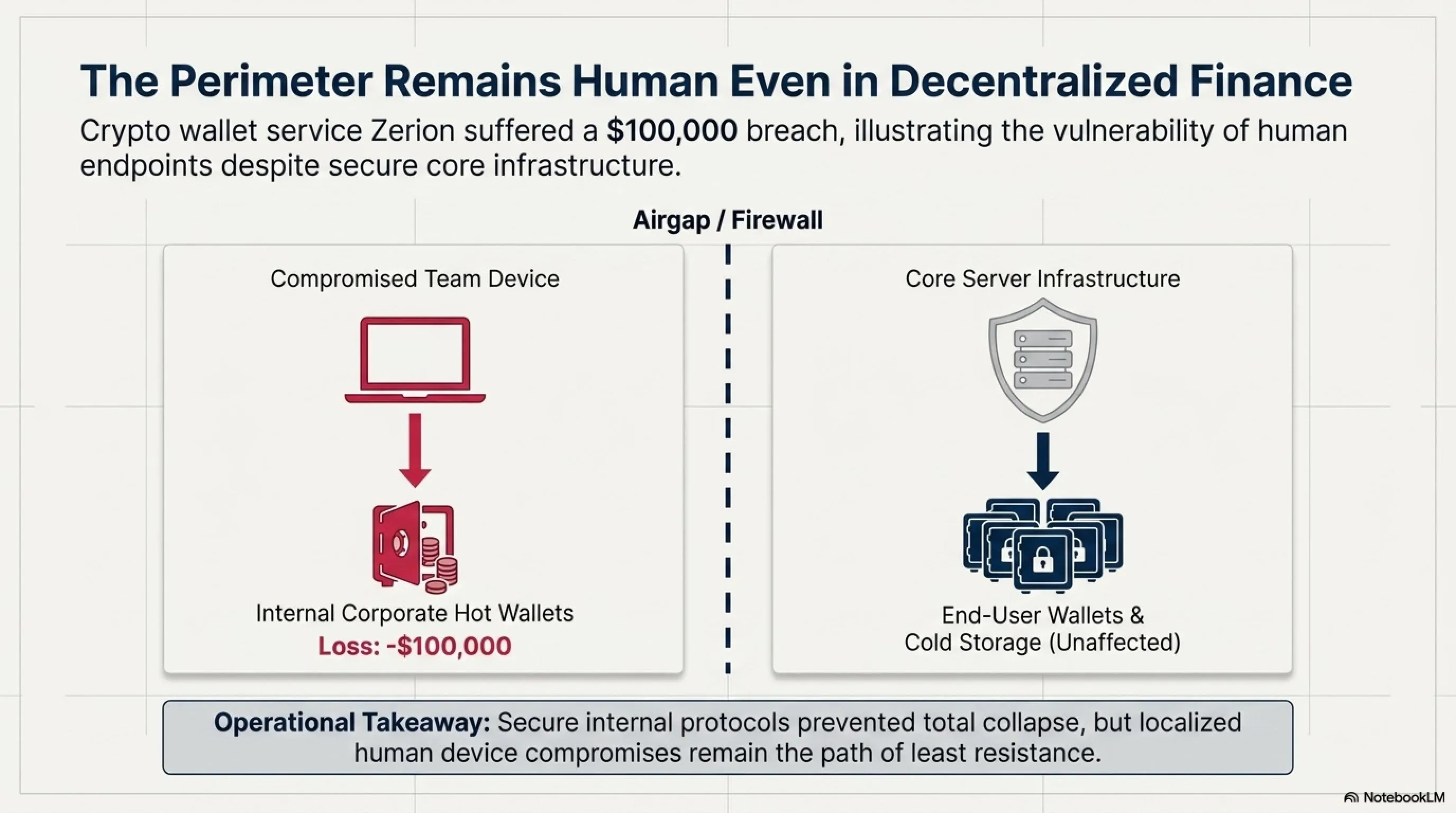
🔍 Zerion Attack Details
- Attack Target: Device of one Zerion team member
- Amount Stolen: Approximately $100,000
- Source of Funds: Company's internal hot wallets
- User Status: User wallets are secure
- Infrastructure: Apps and servers unaffected
Zerion responded quickly and announced that only the company's internal hot wallets were targeted and none of the users' assets are at risk. This attack is an important reminder that even security companies can be targeted and highlights the importance of securing employees' personal devices.
💡 Security Tips for Crypto Users
1. Use Cold Wallets: Store large amounts in cold wallets
2. Two-Factor Authentication: Always enable 2FA
3. Regular Updates: Keep software and devices updated
4. Diversify Storage: Don't keep all assets in one wallet
5. SGLang Critical Vulnerability: 9.8 Score and Remote Code Execution Risk 🐛💻
A critical vulnerability has been discovered in SGLang, registered as CVE-2026-5760 with a CVSS score of 9.8 out of 10. This command injection vulnerability allows attackers to execute arbitrary code remotely on vulnerable systems.
⚠️ CVE-2026-5760: Technical Details
- Identifier: CVE-2026-5760
- CVSS Score: 9.8 out of 10 (Critical)
- Type: Command Injection
- Impact: Remote Code Execution (RCE)
- Vulnerable Systems: Older versions of SGLang
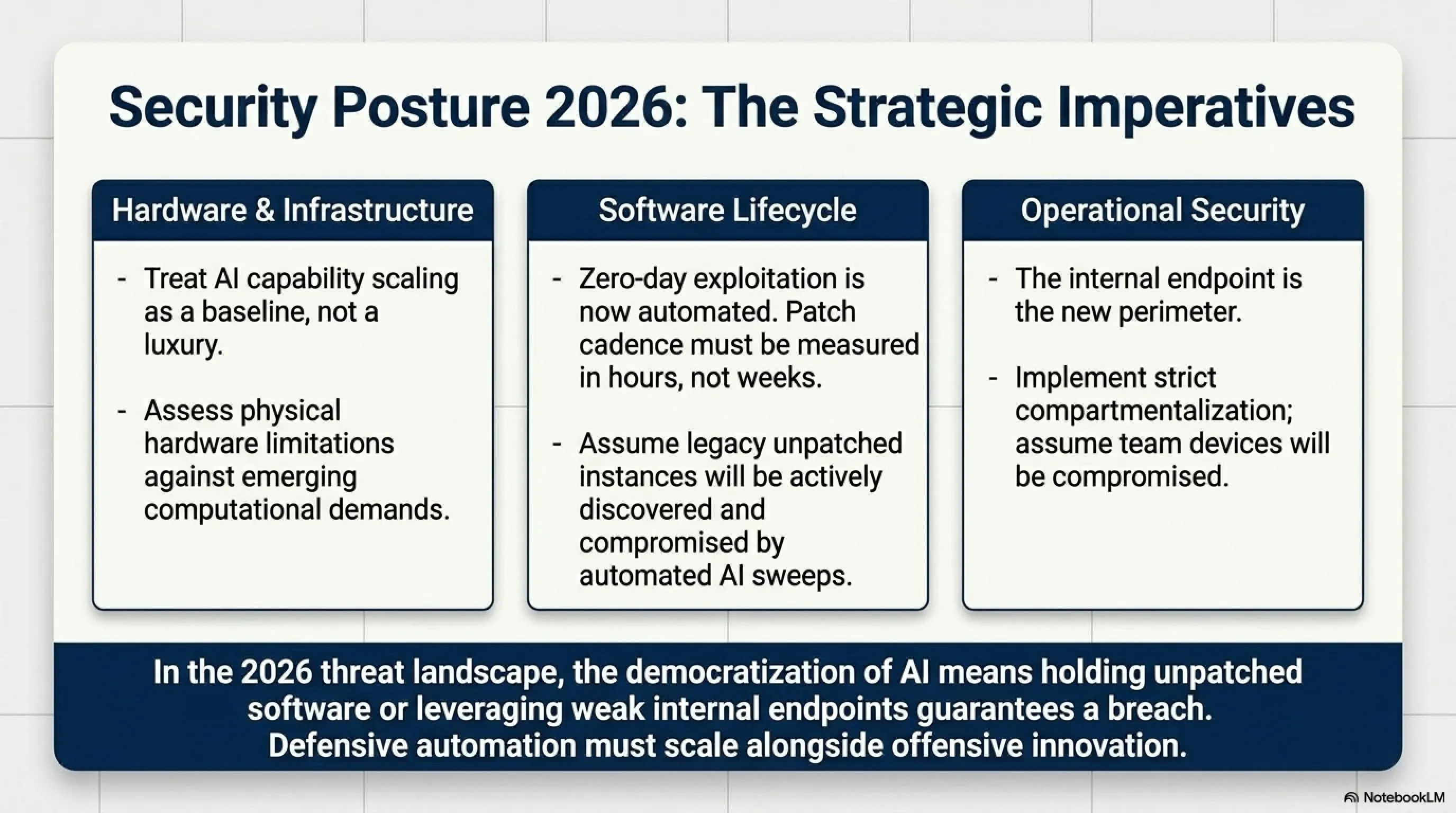
Command Injection is one of the most dangerous types of vulnerabilities because it allows attackers to directly execute operating system commands. In the case of SGLang, this vulnerability could lead to complete system control by the attacker. SGLang users should immediately update to the latest version and ensure their systems are not exposed to this threat.
🛡️ Immediate Protection Measures
1. Immediate Update: Update to the latest SGLang version
2. Check Logs: Review system logs for suspicious activity
3. Restrict Access: Limit access to SGLang services
4. Firewall: Configure firewall rules to protect the system
6. Nintendo Switch 2 Final Specs: 12GB RAM and 4K Support 🎮✨
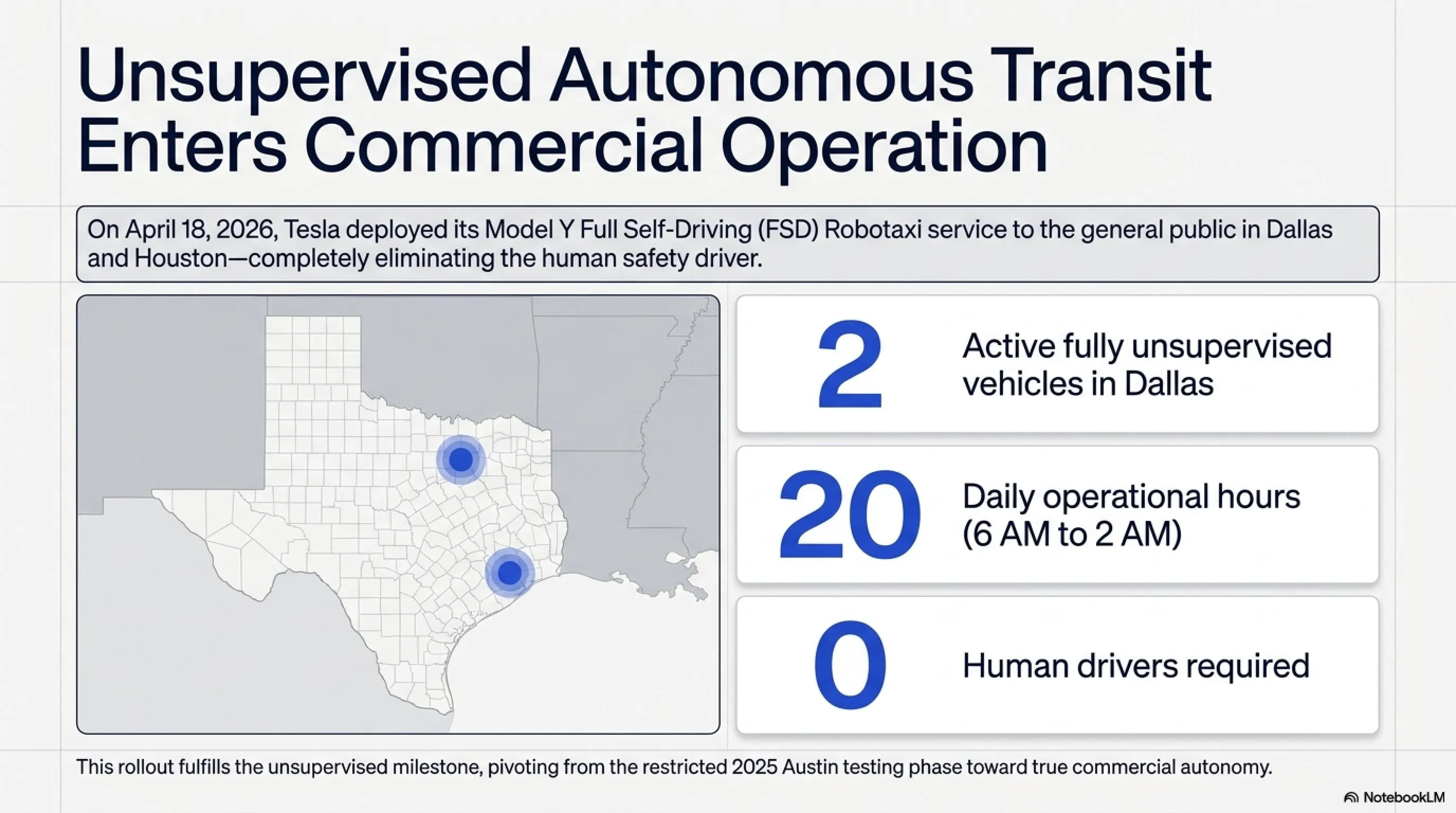
Nintendo Switch 2's final specifications leaked in April 2026, revealing that Nintendo plans to return to the market with a powerful console. Switch 2 with 12GB RAM, 4K support in docked mode, and 1080p @ 120Hz in handheld mode will be a major leap from the previous generation.
🎮 Nintendo Switch 2 Technical Specifications
| CPU | Arm Cortex-A78C (8 cores) |
| GPU | Nvidia T239 Ampere (1534 CUDA cores) |
| RAM | 12GB LPDDR5/LPDDR5X |
| Handheld | 1080p @ 120Hz, 1.72 TFLOPs |
| Docked | 4K @ 60Hz with HDR |
| Ray Tracing | 2 RTX cores (full support) |
Switch 2, using Nvidia Ampere architecture (RTX 20 generation) and 48 third-generation Tensor cores, will also have AI upscaling capabilities. This means games can be rendered at lower resolutions and then upscaled to 4K using AI, providing better performance.
📊 Comparison with Original Switch
| Specification | Original Switch | Switch 2 |
|---|---|---|
| RAM | 4GB | 12GB (3x) |
| Handheld | 720p @ 60Hz | 1080p @ 120Hz |
| Docked | 1080p @ 60Hz | 4K @ 60Hz |
| Performance | 1x | 4x (docked), 2x (handheld) |
Early benchmarks show that Switch 2 will be approximately 4 times more powerful than the original Switch in docked mode and about 2 times more powerful in handheld mode. This power increase means better graphics, higher frame rates, and the ability to run more complex games. Nintendo is expected to announce this console in late 2026 or early 2027.
❓ Frequently Asked Questions (FAQ)
▶️ Is Tesla's Robotaxi truly driverless?
Yes, Tesla's Robotaxi service in Dallas and Houston is completely unsupervised, meaning there is no human driver in the vehicle. This is the first time a major automaker has offered such a service to the general public. The vehicles use Tesla's FSD (Full Self-Driving) system and can navigate, drive, and park completely autonomously.
▶️ How can I protect myself from the Adobe Acrobat Reader vulnerability?
To protect yourself from CVE-2026-34621, immediately update Adobe Acrobat Reader to the latest version. Also avoid opening PDF files from unknown sources and disable JavaScript in Adobe Reader settings. This vulnerability has been exploited since December 2025, so an immediate update is essential.
▶️ Are Zerion user wallets at risk?
No, Zerion user wallets are secure. Only the company's internal hot wallets were targeted, and approximately $100,000 of the company's internal assets were stolen. Zerion applications, infrastructure, and user wallets were not affected by this attack. However, it's always recommended to use two-factor authentication and store large assets in cold wallets.
▶️ When will Nintendo Switch 2 be released?
Nintendo has not yet announced an official release date for Switch 2, but based on recent leaks and Nintendo's previous patterns, the console is expected to be announced in late 2026 or early 2027. The leaked final specifications show the console will feature 12GB RAM, 4K support in docked mode, and 1080p @ 120Hz in handheld mode.
▶️ How was AI used in the Mexico government hack?
Hackers used advanced AI tools such as Anthropic Claude Code and OpenAI GPT-4.1 to identify vulnerabilities, write exploit code, and automate attacks. These tools helped them infiltrate federal and state government organizations in Mexico and steal hundreds of millions of citizen records. This attack demonstrates that AI can dramatically increase the power of cyberattacks.
🎯 Final Conclusion
Today, April 21, 2026, witnessed significant events in the technology world. Tesla took a major step toward the future of transportation by launching fully driverless Robotaxis in Dallas and Houston. Meanwhile, the massive Mexico government hack using artificial intelligence demonstrated that AI can be a double-edged sword.
Critical vulnerabilities in Adobe Acrobat Reader and SGLang remind us of the importance of cybersecurity and regular software updates. The Zerion hack also showed that even security companies can be targeted. Finally, the Nintendo Switch 2 specifications leak promises a powerful console with 4K and 120Hz capabilities.
💡 Key Takeaway: In today's world, staying informed about the latest technology and cybersecurity developments is no longer a choice, but a necessity. Always keep your software updated and get information from reliable sources.
🌐 Stay Connected With Us
For the latest tech, gaming, and gadget news, follow us on social media:
📚 Sources & References
Sources: Tesla Official Announcements, Gambit Security Reports, Adobe Security Bulletins, Zerion Official Blog, CVE Database (NIST), Nintendo Leaks & Rumors, TechCrunch, The Verge, Ars Technica, Wired, Security Research Papers
Research & Analysis: Tekin Editorial Team - April 21, 2026
Note: All information in this article has been collected from reliable sources and carefully reviewed. For more up-to-date information, please refer to the original sources.
🌐 Stay Connected With Us 🎮✨
For the latest tech, gaming, and gadget news, follow us on our official social media channels:
